Description
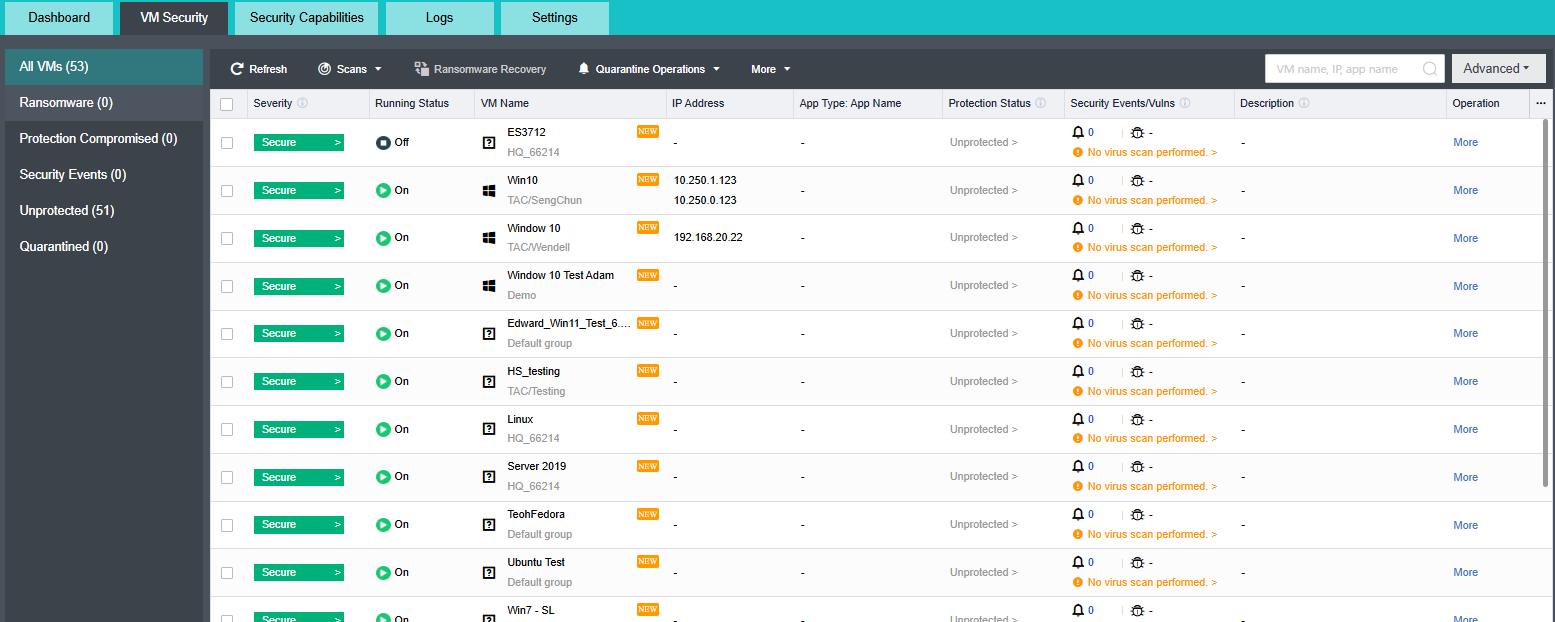
The asset management feature automatically obtains the basic and security information of VMs, including risk level, running status, VM name, IP address, operating system, application, VM protection status, and security events.
Prerequisites
None.
Precautions
- There are time intervals for asset information reporting. The basic information reporting interval is 1 minute, the security information reporting interval is 5 minutes, and the application information reporting interval is 4 hours.
- The virtual machine list is sorted by security status by default. The sorting policy is Protection Compromised > High > Medium > Low > Protection Off > Unprotected > Protected. When the security status is the same, it will sort by application information Database > Web > Unidentified Application.
Steps
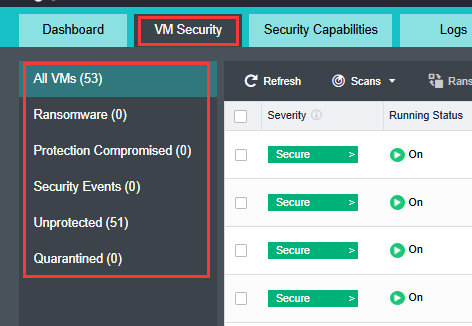
- Go to aSecurity > VM Security and manage platform assets by category.
• Ransomware Detected: Displays the list of VMs with pending suspected ransomware events.
• Protection Compromised: Displays the list of compromised VMs. When the security component of a VM is compromised, the security status of the VM is displayed as Protection Compromised.
• Security Events Detected: Displays the list of VMs with pending security events.
• Unprotected: Displays the list of unprotected VMs.
• Quarantined: View the list of quarantined VMs.
- Go to aSecurity > VM Security > VMs to view the running status and information of all HCI VMs.
• Risk levels include Protection Compromised, High, Medium, Low, and Protected.
Protection Compromised: Indicate that ransomware exists or the VM has been compromised. Immediate fixing is required.
High: Indicate that a high-threat virus or a critical, high-severity attack event exists. Immediate fixing is required.
Medium: Indicate that a medium-threat virus, a low or medium-severity attack event, a brute-force attack, or a high-risk vulnerability exists. Related fixing is recommended.
Low: Indicate that a low-threat virus or a low or medium-severity vulnerability exists. Fixing based on actual situations is recommended.
Protected: Indicate that no security risks exist.
• Running status includes On, Suspended, and Off.
• Security risk events include security events and vulnerabilities.
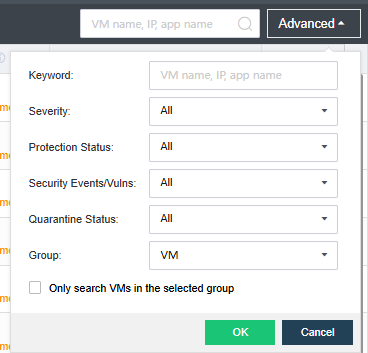
- Click Advanced to filter VMs by category.
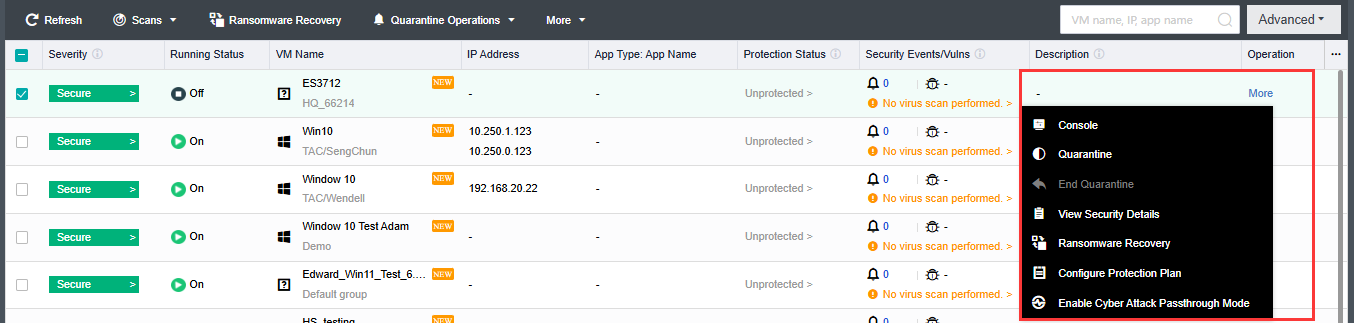
- Click More in the Operation column of a VM to go to the console, quarantine the VM, cancel quarantine, view security details, perform ransomware recovery, configure the protection solution, and enable passthrough mode for the VM.