In the monitoring mode, proxy SSO is implemented by monitoring login data. It is applicable in two scenarios.
Scenario 1: Proxy server deployed out of the intranet. See the following figure.

The data flow is as follows:
- Users can access the Internet through a proxy server, and the device monitors the interaction between PCs and the proxy server.
- When the proxy server authenticates the PCs, they are also authenticated by the device. The configuration procedure is as follows:
Step 1.Set the authentication policy. Navigate to Access Mgt > Authentication > Web Authentication > Authentication Policy and click Add to set the authentication policy according to the IP or MAC addresses of the users who require SSO.
The proxy server is not located on the intranet of the device. Before user authentication, access to the domain server must be allowed. Choose Authentication Policy > Action > Advanced > Before authentication, added to group, set the group to be used before authentication, and configure the Internet access policy to allow this group to access the proxy server.
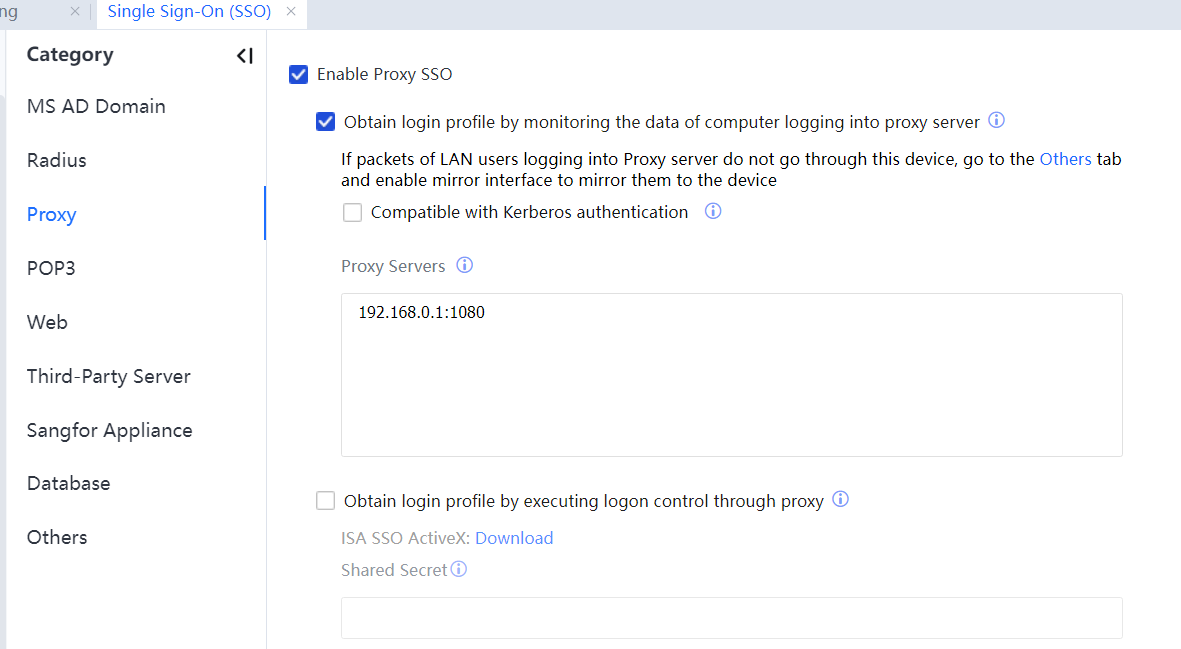
Step 2.Navigate to Access Mgt > Authentication > Web Authentication > Single Sign-On(SSO) > Proxy and tick Enable Proxy SSO. Select Proxy Enable Proxy SSO. Select Proxy, and obtain login profile by monitoring the data of computing logging into the proxy server.
In Proxy Server List, enter the proxy server's IP address and listening port. If multiple proxy servers exist, enter one IP address and port number in each row. Set the port numbers to those for proxy authentication. See the following figure.
Step 3.Log in to the proxy server on a computer. If the login is successful, you can access the Internet.
If the proxy server is an ISA server that adopts IWA, the Compatible with Kerberos option needs to be selected for implementing SSO. This option applies only when login packets pass through the IAG and are inapplicable to the mirroring and bypass modes.
In this scenario, if Show Terms of Use is selected at Authentication Policy > Action > Advanced, redirection must be implemented at the DMZ port. Otherwise, users cannot be authenticated and access the Internet.
Scenario 2: Proxy server deployed in the intranet. See the following figure.
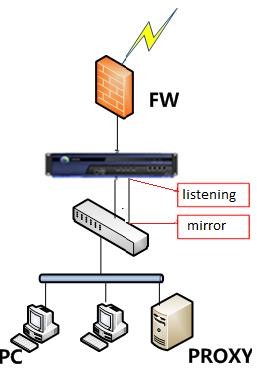
The data flow is as follows:
- Users can access the Internet through a proxy server; the IAG does not forward the authentication data.
- A mirroring port is configured on the switch to mirror the data sent from PCs to the proxy server to the IAG.
- When the proxy server authenticates the PCs, they are also authenticated by the device. The configuration procedure is as follows:
Step 1.Set the authentication policy. Navigate to Access Mgt > Authentication > Web Authentication > Authentication Policy and click Add. Set the authentication policy according to the IP or MAC addresses of the users who require SSO.
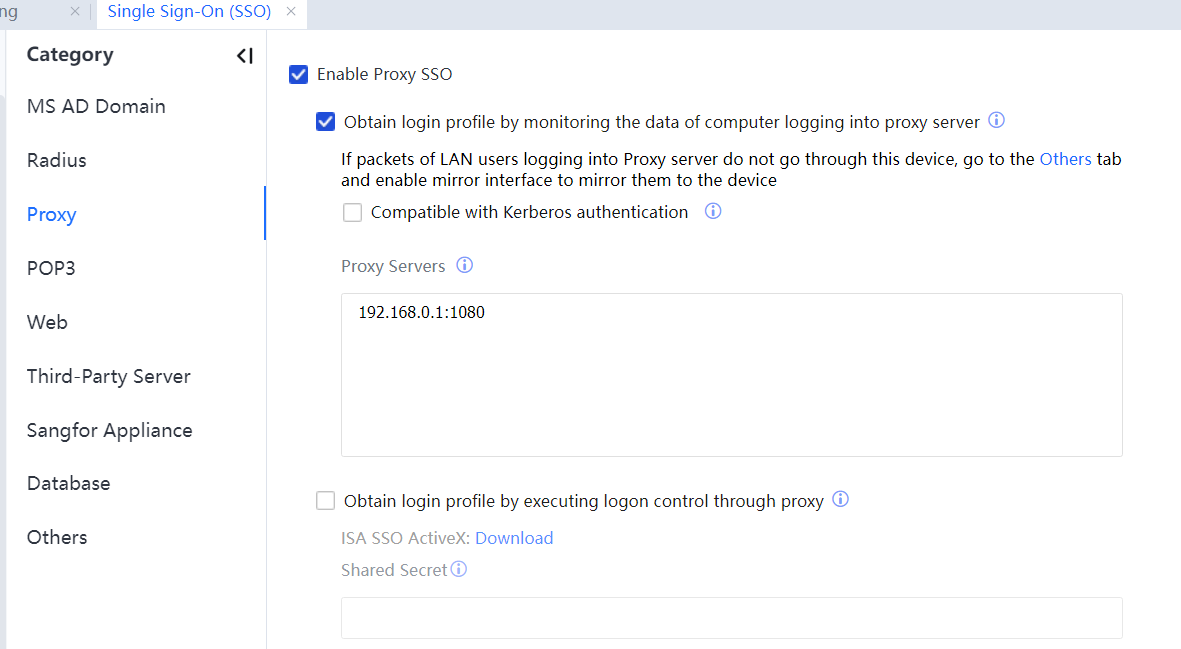
Step 2.Navigate to Access Mgt > Authentication > Web Authentication > Single Sign-On(SSO) > Proxy and tick Enable Proxy SSO.
Select Obtain login profile by monitoring the data of the computer logging into proxy server.
In Proxy Servers, enter the proxy server's IP address and listening port. If multiple proxy servers exist, enter one IP address and port number in each row. Set the port numbers to those for proxy authentication. See the following figure.
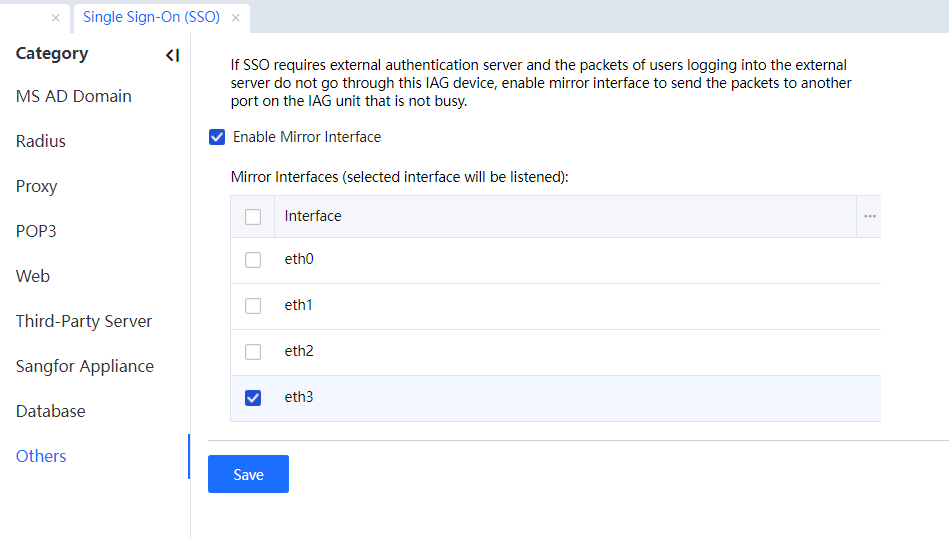
Step 3.If the login data does not pass through the device, set a mirroring port connected to the mirroring port on the switch forwarding login data packets. Click Others, and set the mirroring port. The mirroring port must be an available one not in use.
Step 4.Log in to the proxy server on a computer. If the login is successful, you can access the Internet.

This mode does not support Compatible with Kerberos.




