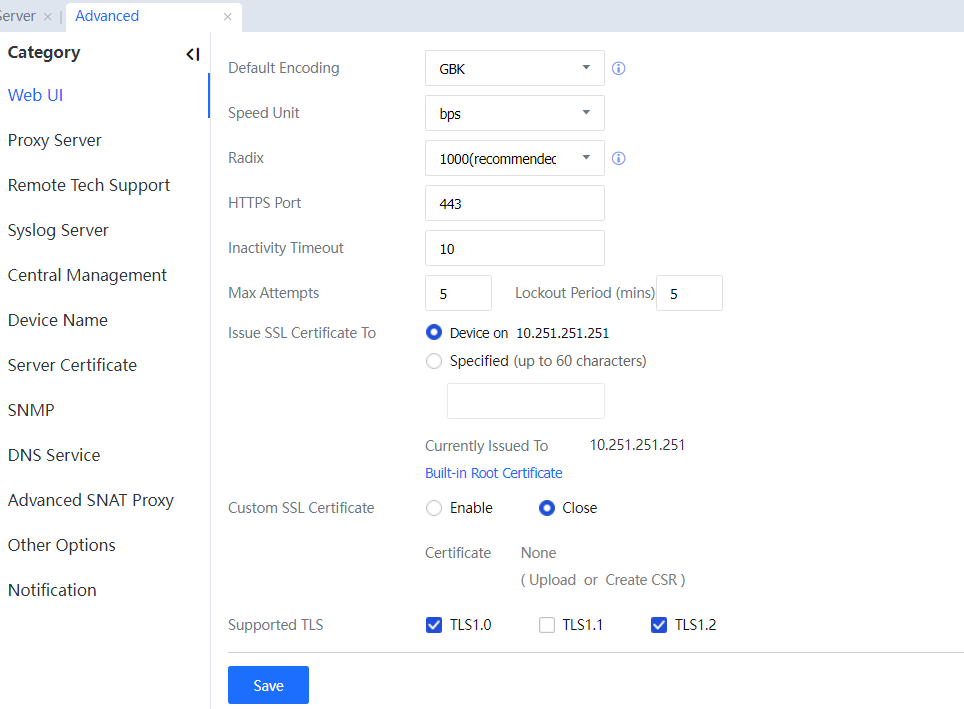
On the Advanced page, you can complete other device system settings, including Web UI, Proxy, Remote Tech Support, Syslog Server, Central Management, Device Name, Server Certificate, SNMP, and other Options.
Web UI
On the Web UI page, you can set the Default Encoding, Speed Unit, Radix, HTTPS Port, Inactivity Timeout, and Issue SSL Certificate To, and click Certificate to download a certificate. See the following figure.
 [ZY308]
[ZY308]
Default Encoding: specifies the default code for processing monitored data when the code of the data cannot be recognized. The default code can be GBK or BIG5.
Speed Unit: specifies the unit of monitored network traffic. Click  to select a unit.
to select a unit.
Radix: specifies the conversion scale of the traffic unit. It can be 1000 or 1024.
HTTPS Port: specifies the port used for logging in to the console. The default port is TCP 443. Inactivity Timeout: specifies the timeout duration of the console. If the administrator does not perform any operation on the console within the specified period, the system will be automatically disconnected.
Max Attempts: The default allowed login number is 5, which is consistent with the default value of the old version and can be modified in the new version within 1 - 90.
Issue SSL Certificate To: specifies the IP address or domain name to which the SSL certificate for logging in to the console is issued.
Click Certificate to download an SSL certificate of the console. After this certificate is installed, the SSL certificate warning message will no longer be displayed on the login page of the console.
Custom SSL Certificate: The console uses a custom SSL certificate: You can enable and upload a custom SSL certificate to remove the SSL certificate warning when logging in to the console interface. Applicable to the existing CA certificate center in the enterprise, the administrator computer has installed the root certificate of the CA, the IAG device creates a certificate request, the CA certificate center issues the server certificate for IAG, and finally uploads the server certificate (including the public key and private key) to IAG.[ZY309]
Click Save to save the settings.[A310]
Proxy Server
When a proxy server is required for Internet access, all user data is forwarded to the proxy server. Modules include the firewall determining whether to reject a connection based on the destination address and port. Therefore, many functions are unavailable. To ensure that modules including the firewall are functional, the modules must correctly identify the destination address and port of data forwarded to the proxy server.
The following figure shows the network topology.
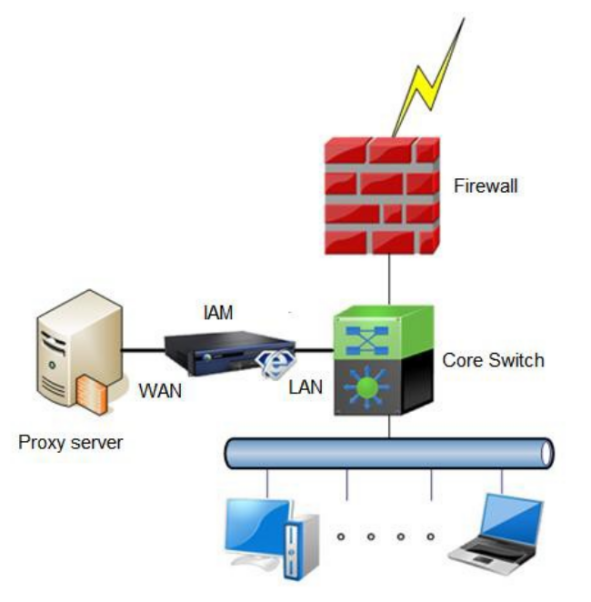
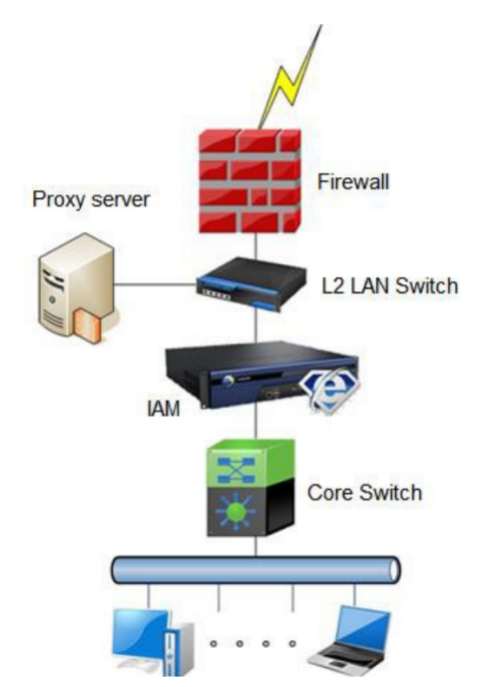
Ensure the data bound to the proxy server is forwarded to the device first. The proxy server must connect to the WAN interface of the device.
By default, the device will detect all proxy data. You can configure the device to detect the data of a fixed proxy server on the Proxy page. See the following figure.
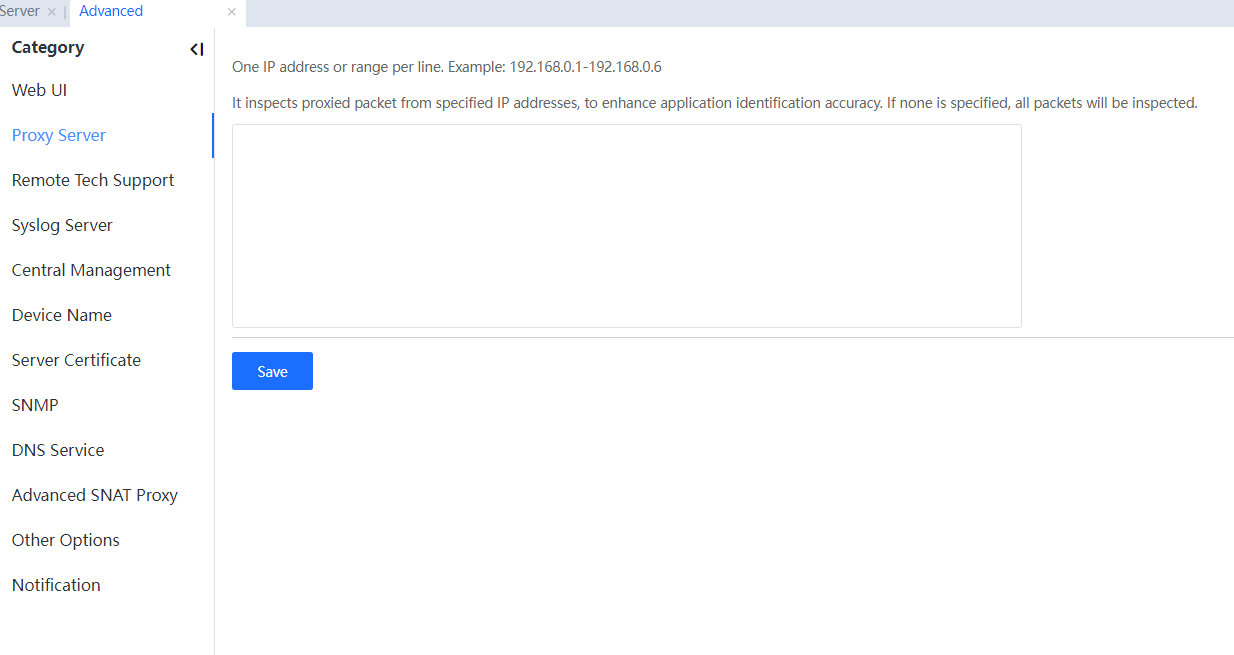
Enter the IP address of a proxy server or an IP address range.
The device will detect whether the data destined for an IP address listed on the Proxy page is proxy data and control the Internet access permission accordingly. If the list is blank, the device will detect all data, which reduces the working efficiency of the device. Therefore, it is recommended that the IP address of a proxy server is listed.
Click Save to save the settings.[A311]
Remote Tech Support
On the Remote Tech Support page, you can set whether to allow remote login to the device from a WAN interface, Report unidentified URLs, Report system errors, Report unidentified applications, and whether to Enable Firmware Updater.[A314]
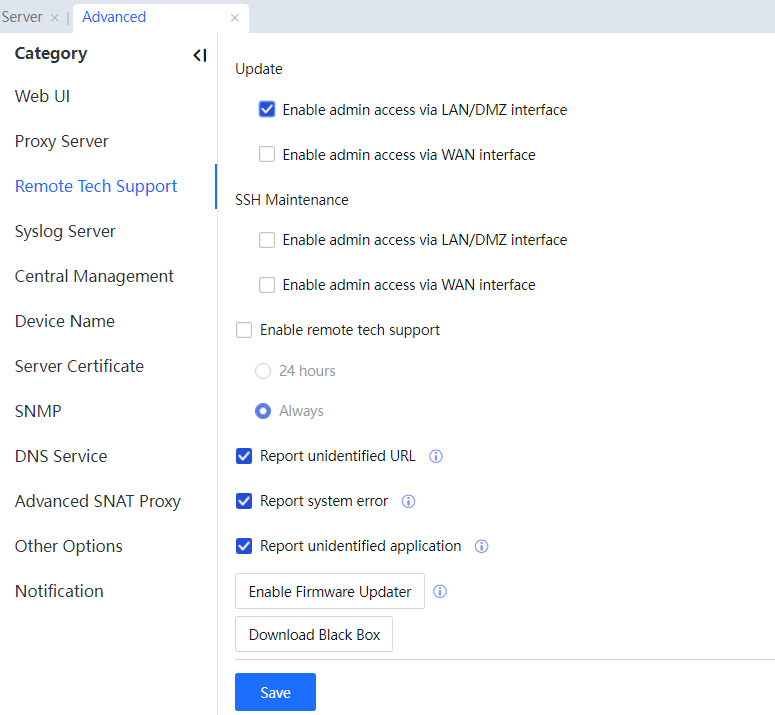
Update: Specifies whether to allow remote login to the device from a WAN interface. If this option is selected, the ping function is automatically enabled for the WAN interface of the device.[A315][U316]
SSH Maintenance: Specifies the admin access interface. Select Enable admin access via LAN/DMZ interface or Enable admin access via WAN interface as needed.
Enable remote tech support: Specifies the time for remote technical support. Select 24 hours or Always as needed.
Enabled: Specifies whether to allow remote login to the device from a WAN interface. If this option is selected, the ping function is automatically enabled for the WAN interface of the device.
Report unidentified URL: Specifies whether to upload unrecognized URLs automatically. After this option is selected, URLs that the URL Database cannot recognize will be reported to the manufacturer. Information about the company will not be leaked.
Report system error: Specifies whether to report system errors automatically. After selecting this option, the manufacturer will automatically report information about system errors. Information about the company will not be leaked.
Report unidentified application: Specifies whether to upload unknown application information automatically. After this option is selected, information about unknown applications will be automatically reported to the manufacturer. Information about the company will not be leaked.
After technical support assistance is enabled, technical support engineers can remotely connect to the device and intranet.
Click  to enable access to the system backstage, which will be disabled after one day by default.[A317]
to enable access to the system backstage, which will be disabled after one day by default.[A317]
To download the black box in the last 1- 30 days, click the Download Black Box button.
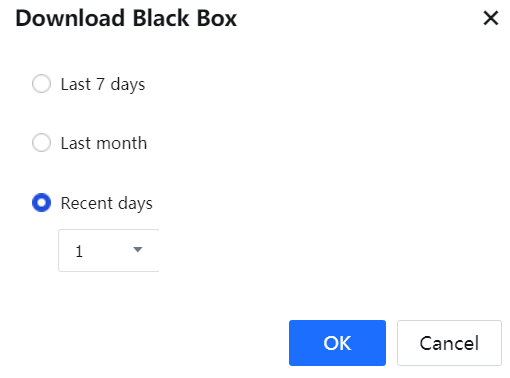
Click OK to save the settings.[A318]
Syslog Server
On the Syslog Server pane, you can synchronize the System Logs, Email Alarm Logs, and Admin Logs on the device to the configured Syslog server.
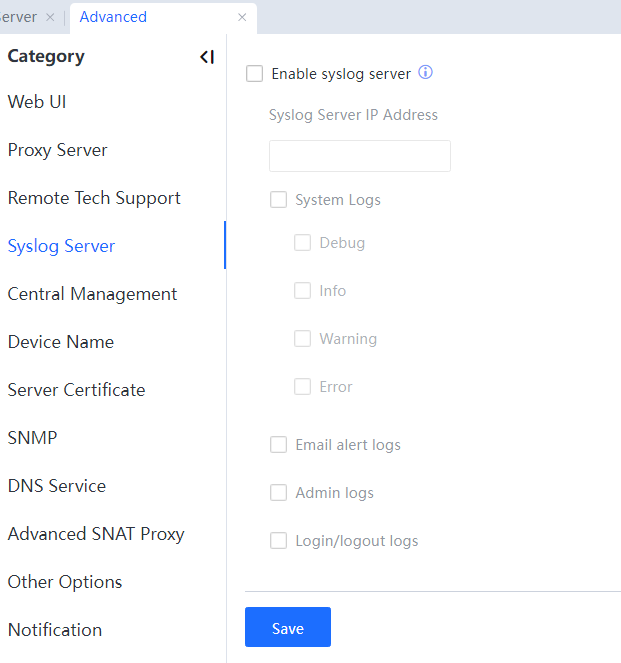
Syslog Server IP Address: specifies the IP address of the Syslog server.
System Logs: includes debugging logs, information logs, alarm logs, and error logs. Select Debug Logs to synchronize the debugging logs on the device to the Syslog server. Select Info Logs to synchronize the information logs on the device to the Syslog server. Select Warning Logs to synchronize the alarm logs on the device to the Syslog server.
Select Error Logs to synchronize the error logs on the device to the Syslog server.
Select Email Alarm Logs to synchronize the email alarm logs on the device to the Syslog server. Select Admin Logs to synchronize the administrator operation logs to the Syslog server.
Central Management
On the Central Management page, you can set whether to incorporate the IAG into centralized management. After the IAG is incorporated into centralized management, the administrator of the central end can deliver policies to the IAG. In addition, the permission of a controlled end can be assigned by the central end.
The device supports central management and control of BBC or X-Central (cloud image).
Configuration for connection to BBC:
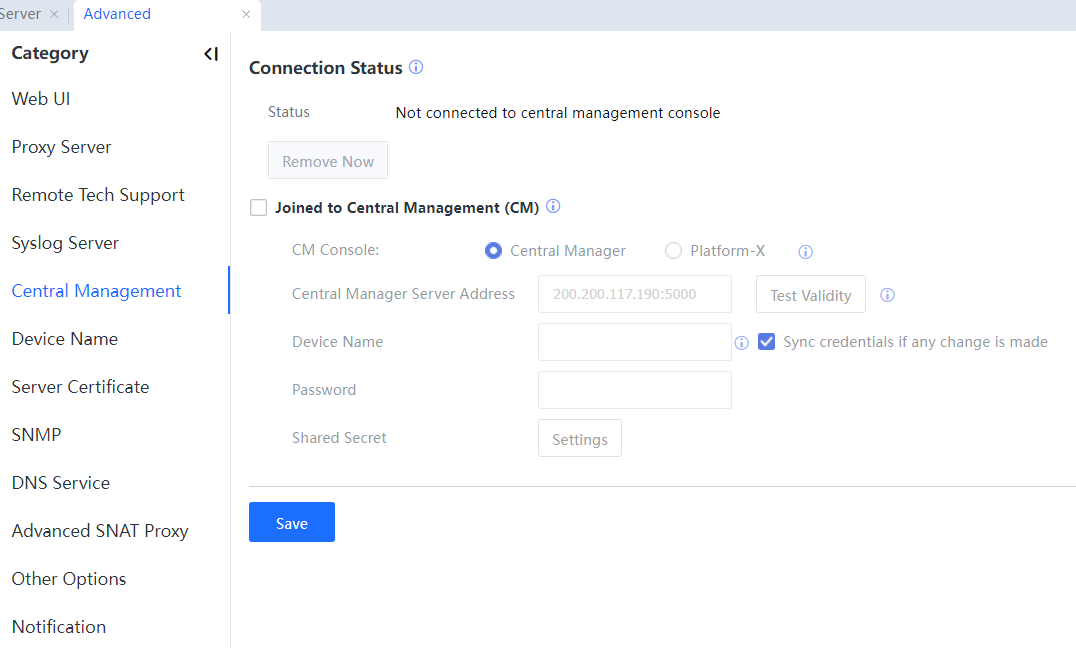
Not connected central management console is for decontrol by entering password after adding into central management. The administrator of the central endpoint owns the password. Here, the option is grey, meaning the device is not connected to the central endpoint. You can click after connecting to the central endpoint.
Central Manager Server Address sets the central management device to be connected. The administrator of the central endpoint owns the address.
Click Test Validity to test whether the IP address and port number can be connected.
Device Name is for entering the username of the central endpoint of central management.
Selecting Sync credentials if any change is made means that the device name of the local controlled endpoint will synchronize with that set in this endpoint.
Password: Enter the password for connecting to the central endpoint of central management.
Configuration for connection to X-Central:
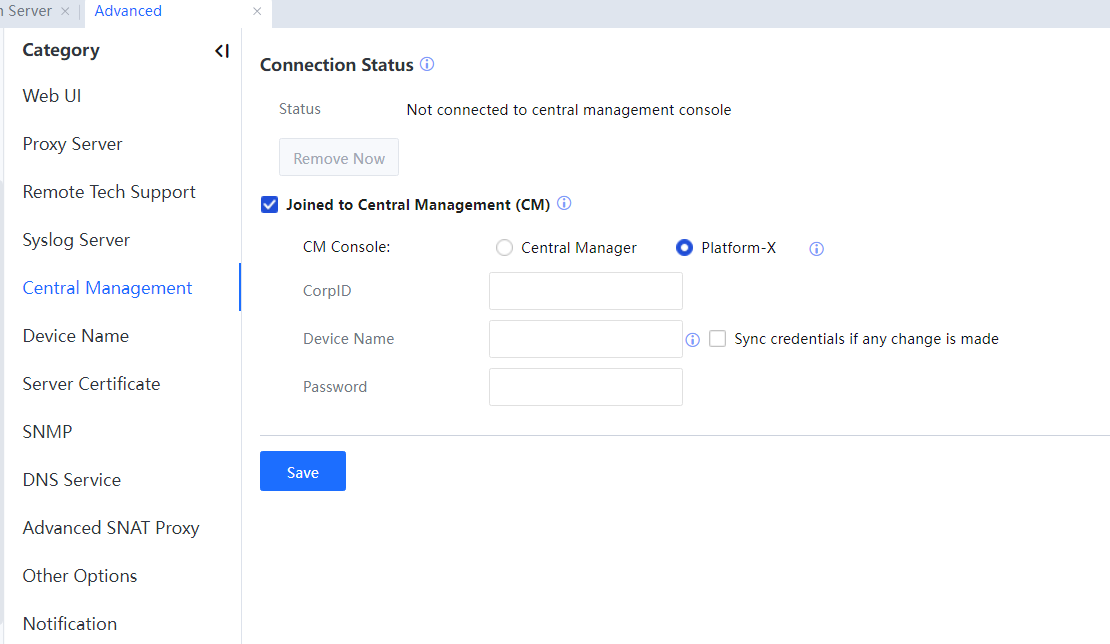
CorpID is for entering the corporate ID of X-Central.
Device Name is for entering the username of the central endpoint of central management.
Selecting Sync credentials if any change is made means that the device name of the local controlled endpoint will synchronize with that set in this endpoint.
Password: Enter the password for connecting to the central endpoint of central management.

After the IAG is connected to the center end for centralized management, the configurations delivered by the central end cannot be edited or deleted on the controlled end.
Device Name
You can set device names to distinguish controlled devices when multiple devices are connected to the central end or to distinguish devices that synchronize data to the external data center when multiple devices synchronize data using the same account. See the following figure.
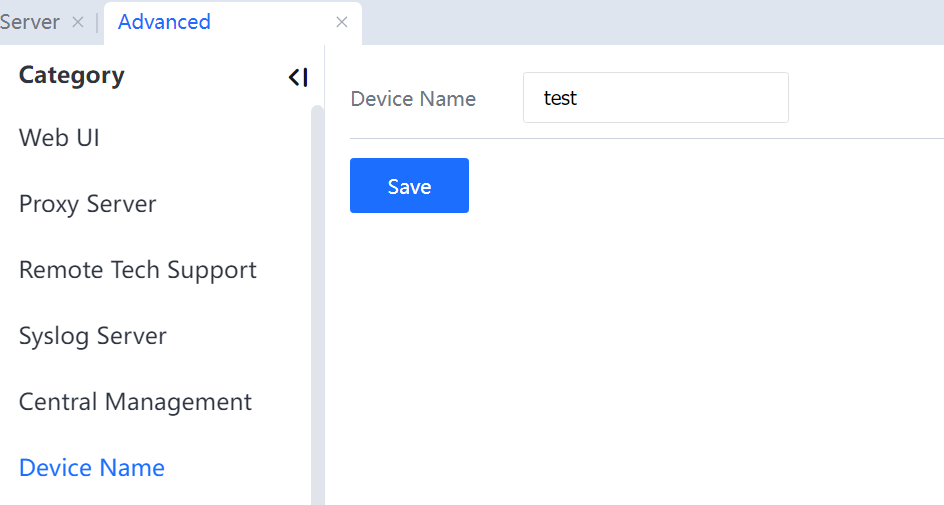

If no device name is set, the centralized management account is used as the device name by default after the device is connected to the central end for centralized management.
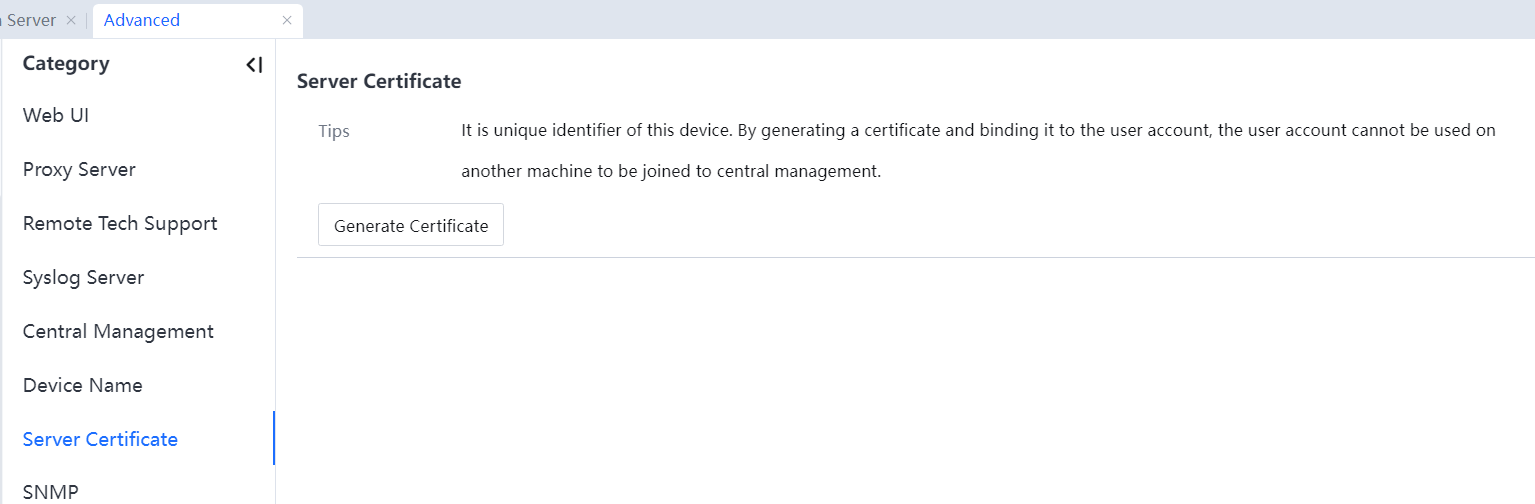
Server Certificate
A certificate needs to be generated when the device is connected to the central end for centralized management. A hardware certificate uniquely identifies an IAG. A hardware certificate can be generated and imported to the central end to prevent another IAG from connecting to the central end using the same account. See the following figure.
SNMP
On the SNMP page, you can set and enable the SNMP function for the IAG. See the following figure.
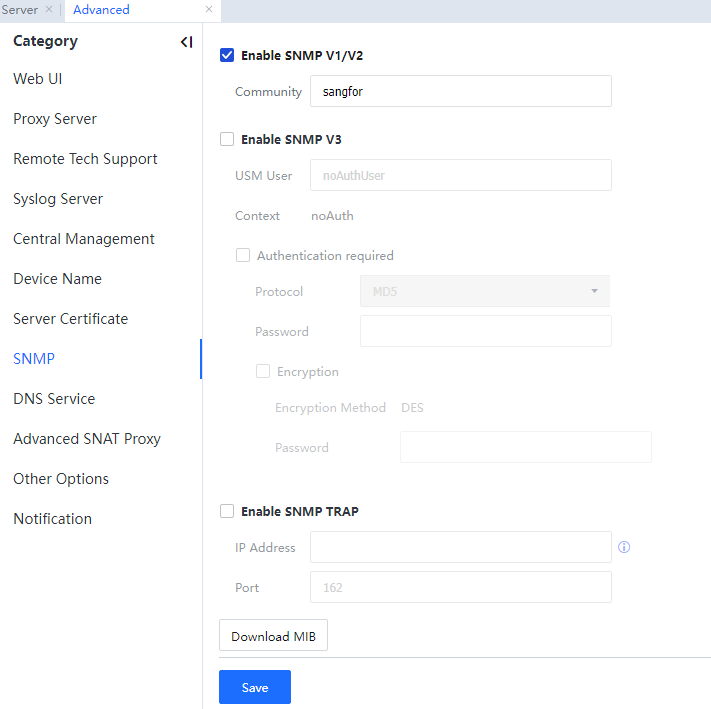
Enable SNMP V1/V2: To enable SNMP V1 and SNMP V2. You need to set a community name. You can view the running status of the device based on the specified community name on an SNMP client.
Enable SNMP v3: To enable SNMP V3.
UMS User: Specifies the UMS username.
Authentication Required: To enable identity authentication and set an identity Auth Method, which can be set to MD5 or SHA.
Encryption: To enable DES encryption and set an encryption password.
Enable SNMP TRAP: Used to actively send the device alarm log to the SNMP server. It is disabled by default, and the default port is 162.
Download MIB: Click this button to download the MIB of the device and import it to the SNMP management software to monitor its parameters.
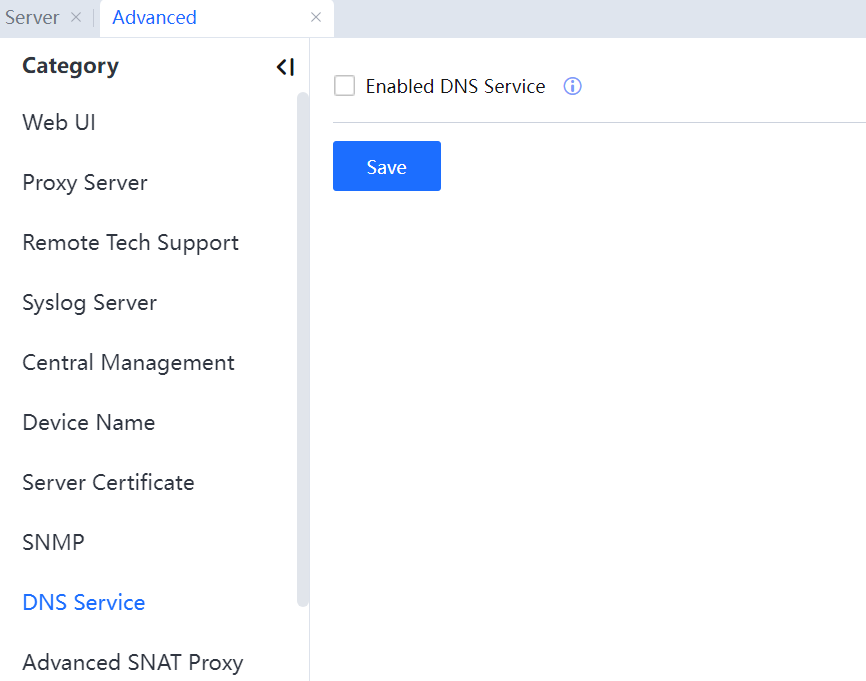
DNS Service
To use IAG as a DNS server, select Enabled DNS Service.
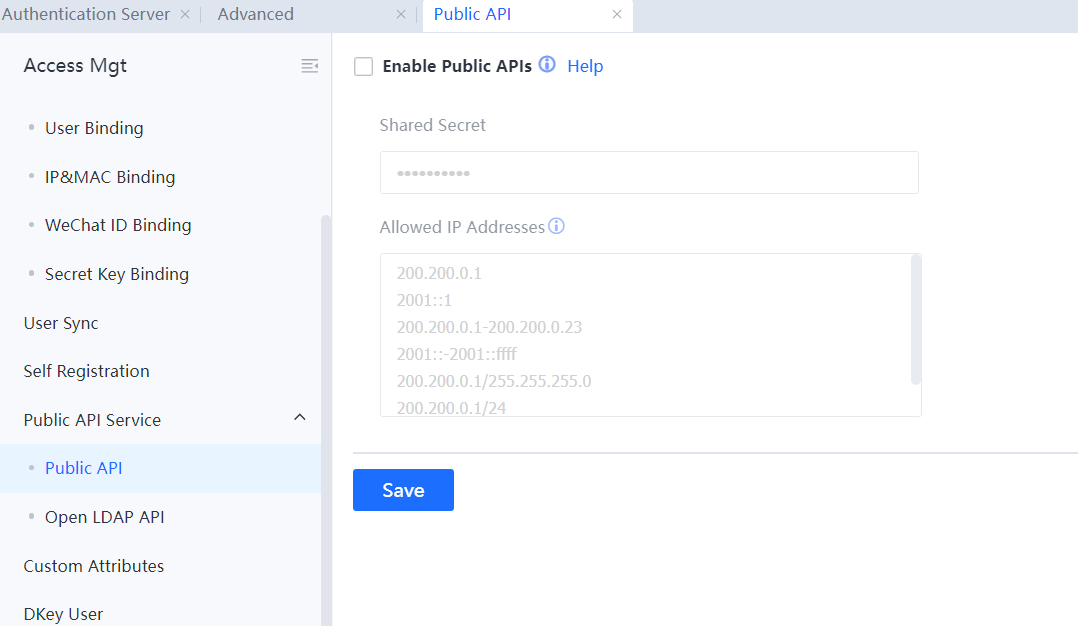
Public API Service
Increasingly more client environments are deployed with a centralized management platform, and the administrator intends to realize centralized management and maintenance of IAG devices, etc.

The systems that support the restful interface all support data reading and management of IAG devices through the Public API Service function.[A321]
 [A322]
[A322]
Shared Secret Key is for setting the shared password for the third-party management platform.
Allow IP using this interface is the IP of the third-party management platform.
See Download Help Document for details.
Other Options
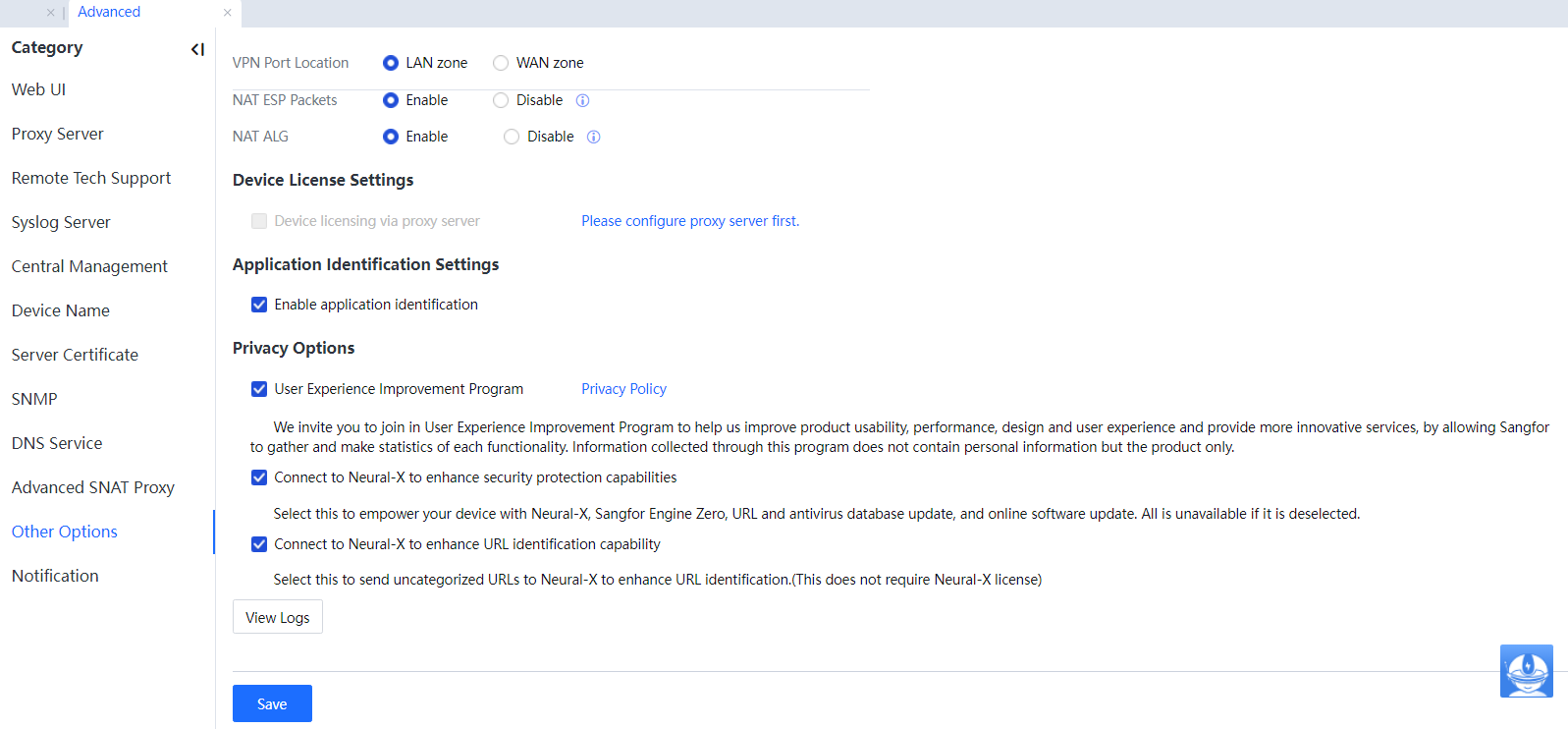
VPN Port Location: Includes the LAN and WAN.
LAN zone: This is the default value, indicating that the VPNTUN interface belongs to the LAN by default.
WAN zone: If WAN zone is selected, all data passing the VPNTUN interface will be regarded as data sent from the LAN to the WAN and be authenticated, audited, and controlled.
NAT ESP Packets: It is enabled by default. Under special circumstances, when IPSec Encapsulating Security Payload (IPSec ESP) protocol is used, and the security parameter index (SPI) values in the same connection are inconsistent, this function must be disabled.
NAT ALG: It is enabled by default. With this function enabled, the device configures the network address translation on the application level gateway (NAT ALG) for SIP and H323 video protocols. When the video client enables NAT traversal, this function needs to be disabled.
Device licensing via proxy server: Before you can use this feature, first configure a proxy server as instructed. To be specific, before you can go to System > General > Advanced > Other Options > Device License Settings to select Device licensing via proxy server, you must first go to System > General > Update > Proxy to configure a proxy server. Otherwise, this feature is unavailable.
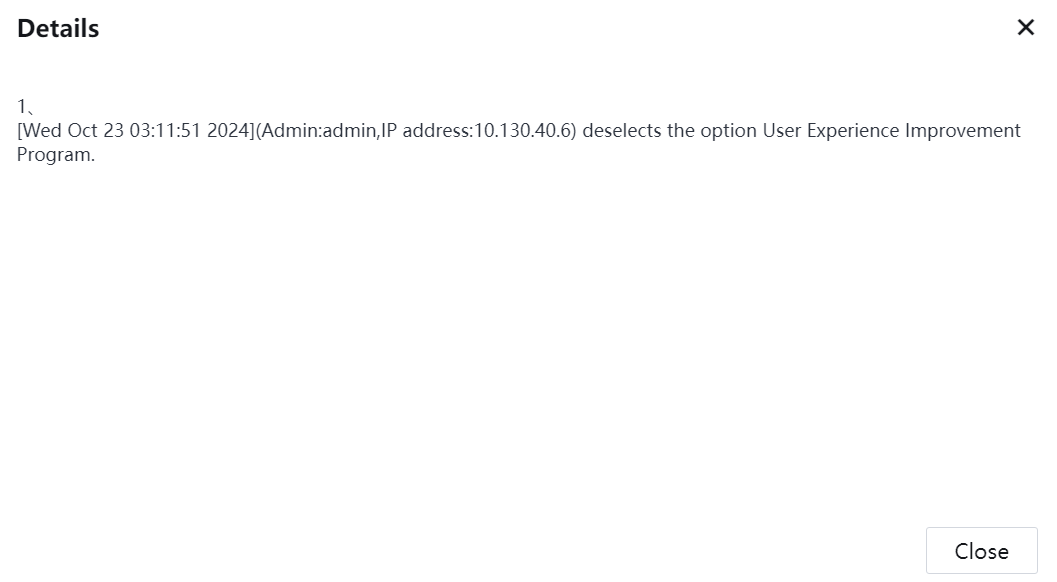
Privacy Options: Provide the option to join the User Experience Improvement Program.
View logs: Show privacy log.
Redirection/Proxy
When the IAG is deployed in bridge mode, if the bridge IP address cannot communicate with endpoints, functions involving redirection such as web authentication, Ingress, and proxy detection, require communication with PCs on the intranet, which can be implemented by the IAG using virtual IP addresses by default.
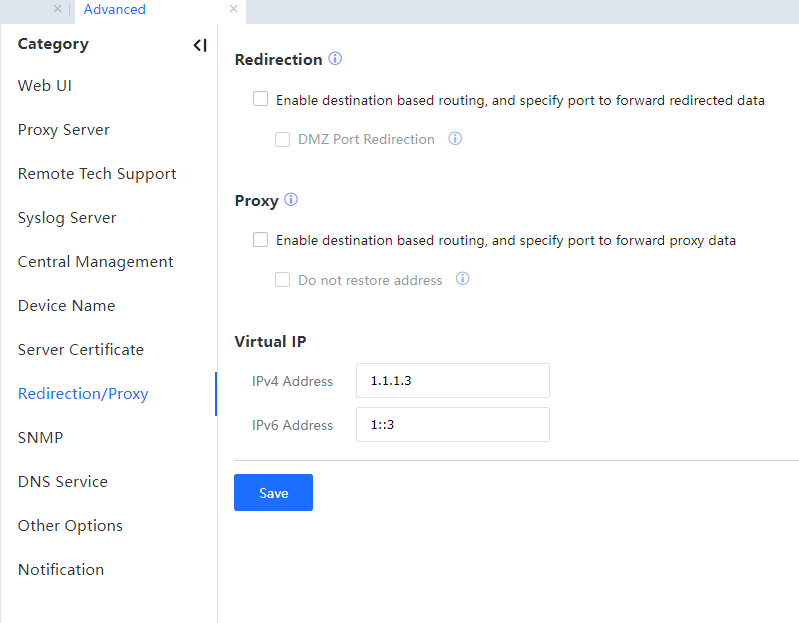
Redirection: Involves authentication redirection and rejection redirection.
If Enable destination-based routing, and specify port to forward redirected data is selected, the device will query routing rules and select an egress before sending redirection packets. By default, the WIWO principle is observed in sending redirection packets.
Proxy: Includes mail proxy and SSL proxy.
If Enable destination-based routing, and specify port to forward proxy data is selected, the device will query routing rules and select an egress before sending proxy data. By default, the WIWO principle is observed in sending proxy data.
Select Do not restore address to disable the address recovery function. In bridge mode, the proxy address recovery function is enabled by default. However, the address recovery function is not supported in route mode.
In Virtual IP, set virtual IPv4 and IPv6 addresses. The client will be redirected to a virtual IP address.
Advanced SNAT Proxy
After the device starts the SNAT proxy function, when LAN users access the public network, the source IP addresses and source ports of LAN users are transformed into device IP addresses at the WAN interface and a random port that has not been occupied.
Because a user IP address seen in the public network is a device IP address at the WAN interface and the port is a random value, the network supervisor cannot trace its source by public network information. For this reason, the source port of every LAN user passing the NAT is stipulated to remain in a given range.
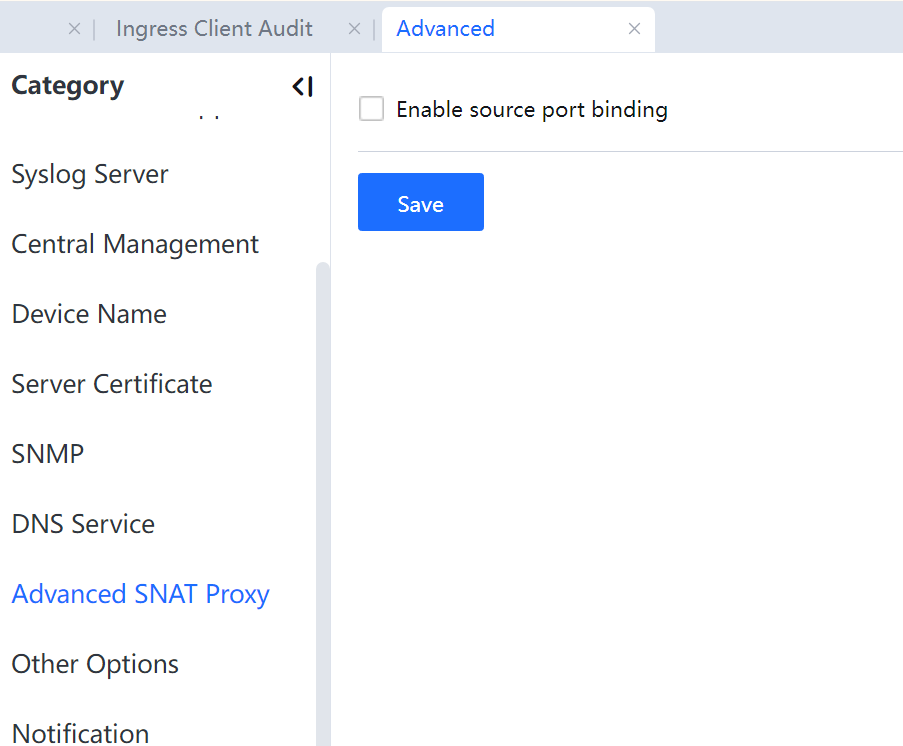

This function is not enabled by default and is only used for network security connections.
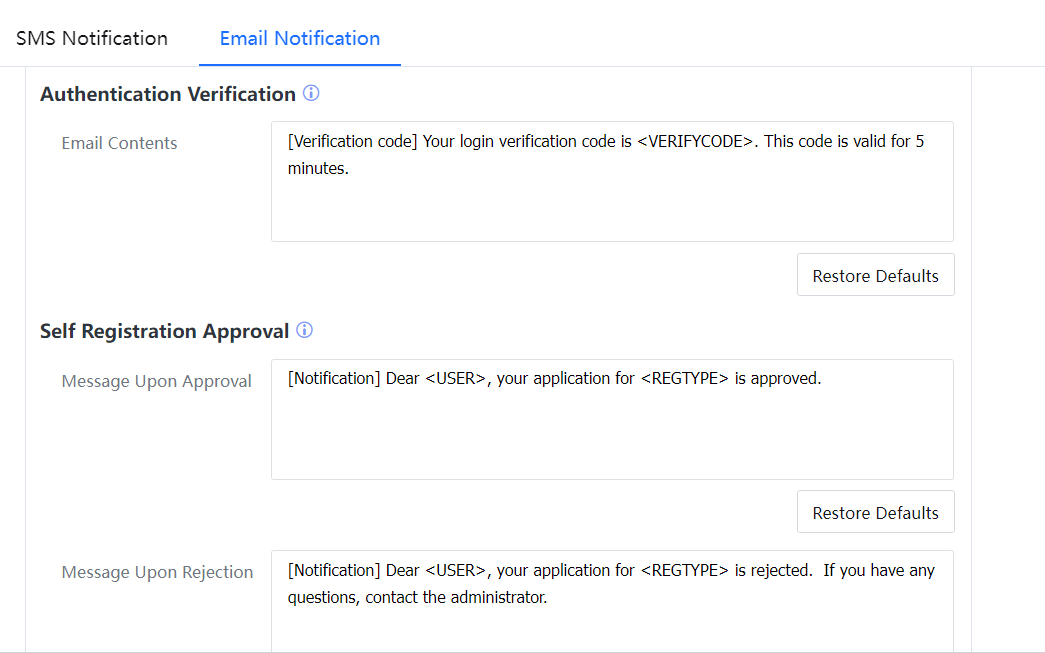
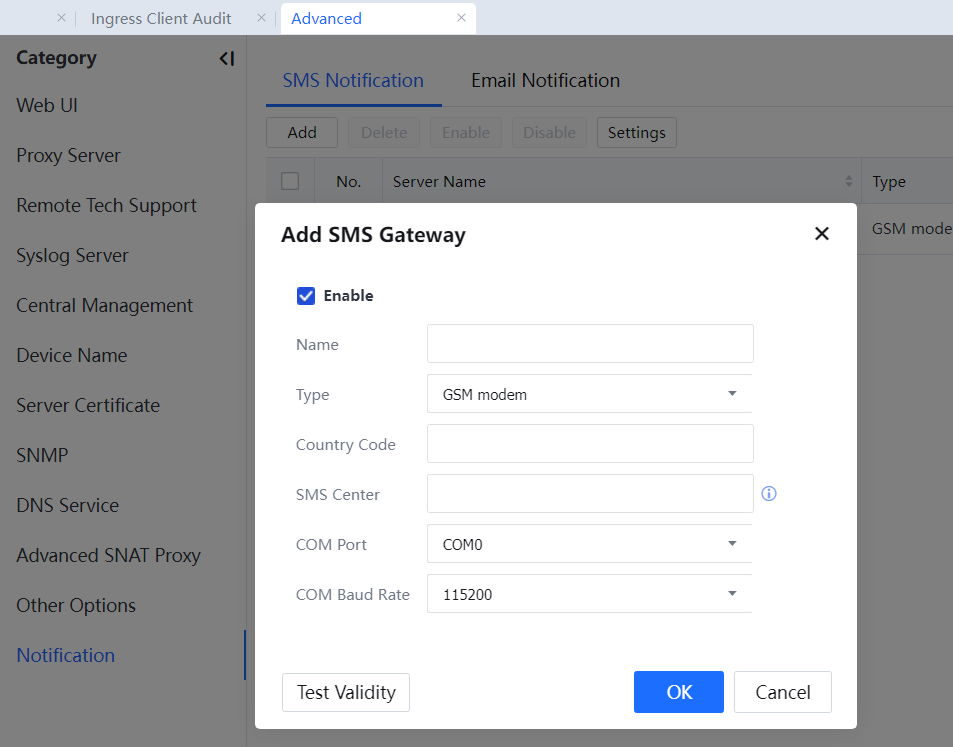
Notification
The notification options include SMS Notification and Email Notification.
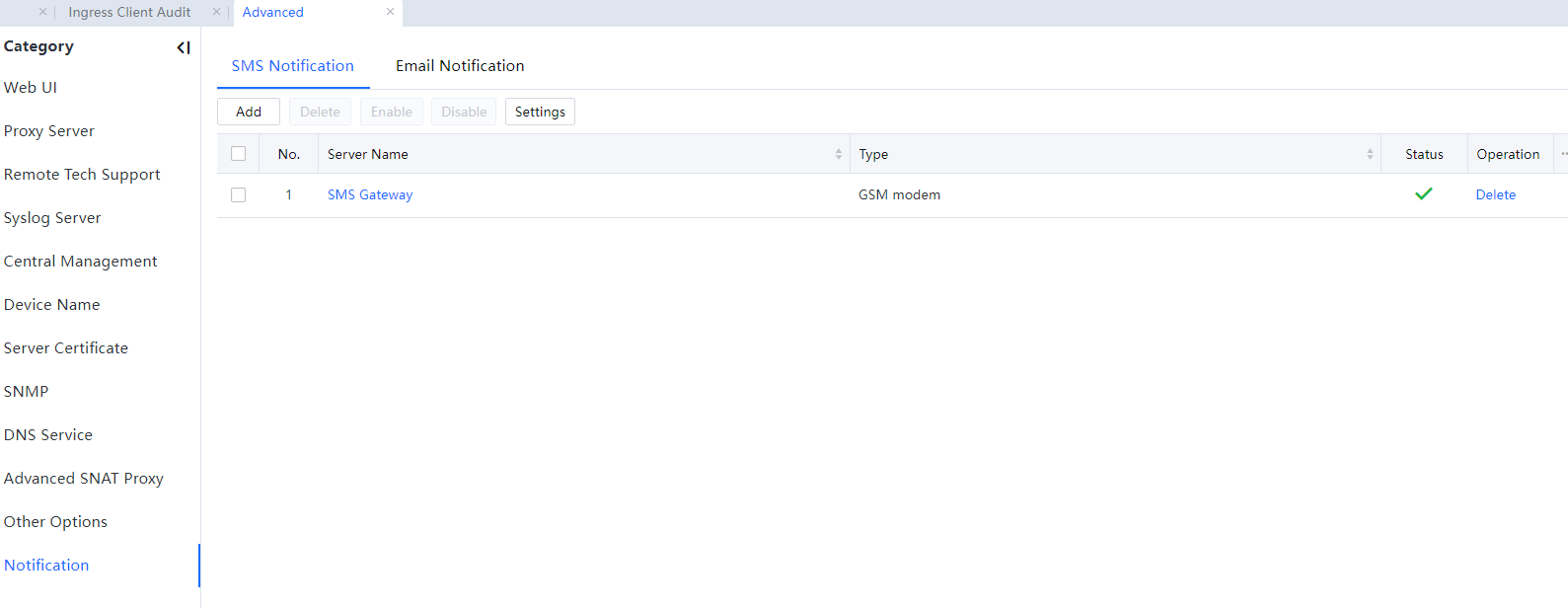
3.11.5.10.14.1 SMS Notification
Add the SMS notification server and complete its configuration.
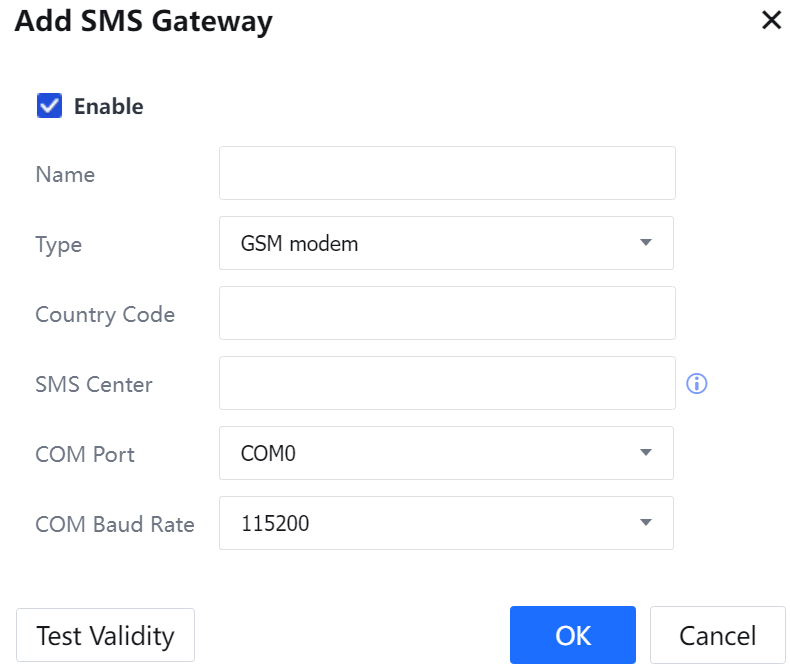
Configuration for SMS platform
The configuration panel is in System > Advanced > Notification > SMS Notification.
The delivery Module includes two categories: Deliver by predefined SMS module and Delivery by SMS module on the external server.
The default selection is Deliver by predefined SMS module, which is for the following two scenarios:
- Message delivery by GSM modem is directly connected to the IAG device serial port.
- The message is delivered by an external SMS gateway or server.
Delivery by SMS module on an external server is for the following scenario:
Message delivery by GSM modem is not directly connected to the device but to another PC. In this case, the PC should be installed with a message delivery program. Click Download to get the program. After installation, enter the IP address and the SMS central port of the PC.
The configuration is shown in the picture below:
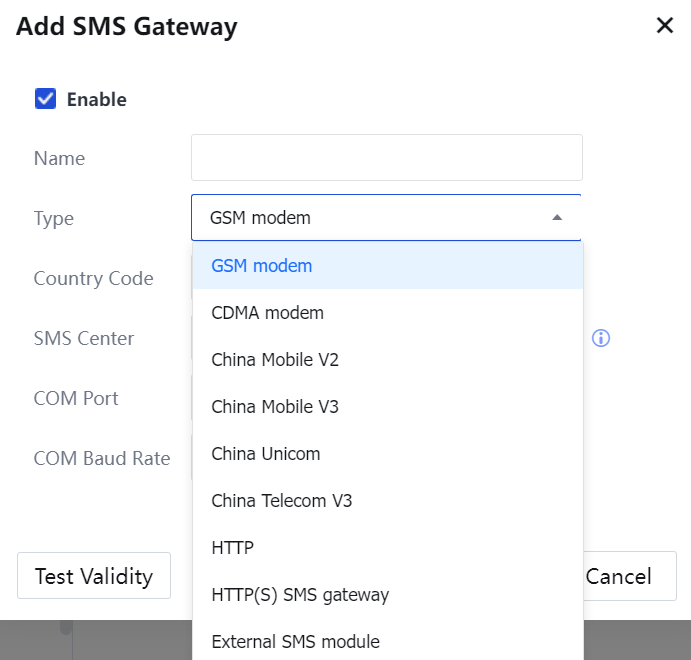
GSM modem: for GSM SIM cards, typically those of China Mobile and China Unicom.
CDMA modem: for SDMA SIM cards, typically those of China Telecom. China Mobile V2, China Mobile V3, China Unicom, and China Telecom V3 are the SMS gateway types of various ISPs.
HTTP: used in combination with the Webservice SMS gateway.
Type: When the GSM modem is selected, configure it as follows:
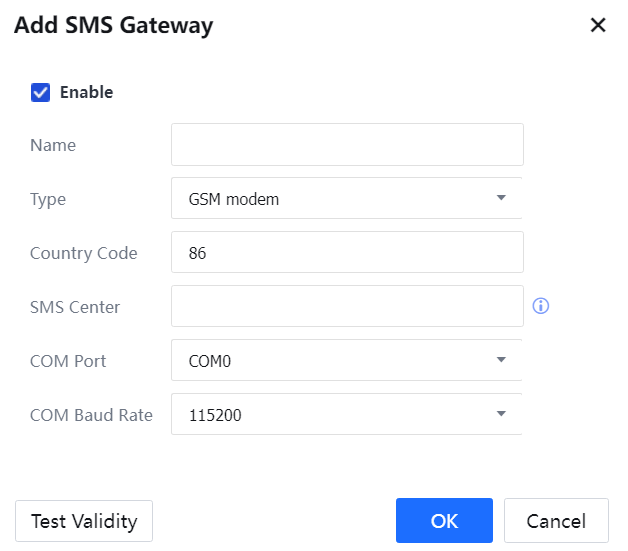
Country Code: The country code corresponding to the phone number. For example, 86 is for China.
SMS Center: The SMS Center number of the corresponding ISP to which the SIM card in the GSM modem belongs.
COM Port is the serial port that the GSM modem uses. Available options are COM0, COM1, and COM2.
COM Baud Rate: The default selection is 115200, which applies to the corresponding GSM modem of IAG. Other COM Baud rates cannot be chosen for the GSM modem of IAG; otherwise, it may not send the message.
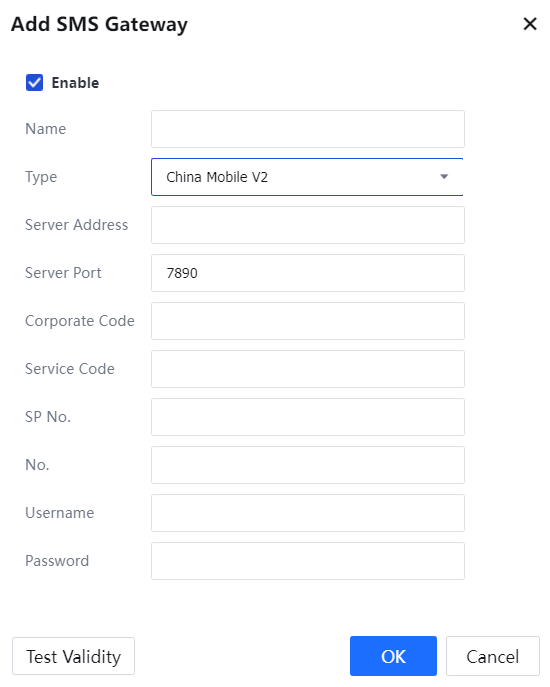
When China Mobile V2, China Mobile V3, China Unicom, or China Telecom V3 is selected, configure it as follows:
Server Address is for entering the IP address of the SMS gateway.
Server Port: Enter the port monitored by the SMS gateway.
Enter the rest relevant parameters of Parameter Setting, as provided by the SMS provider, including Corporate Code, Service Code, SP No., No., Username and Password.
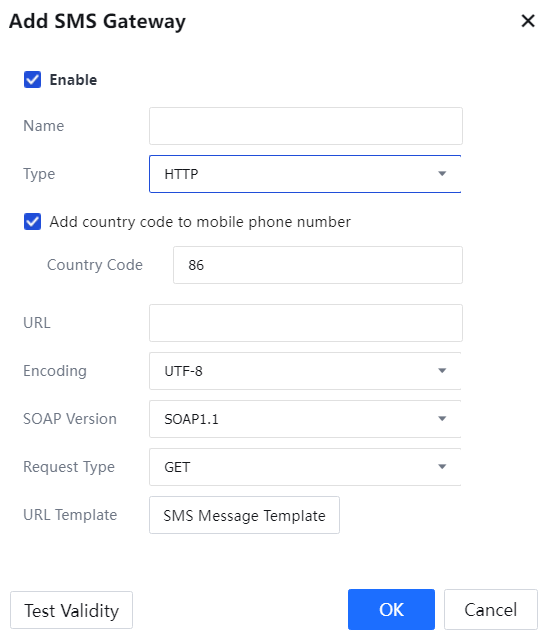
The HTTP is selected when the client has a Webservice SMS gateway server. The device sends some parameters to the server's URL, and the interface of the SMS gateway sends messages accordingly when receiving the parameters.
Country Code: the country code corresponding to the SMS platform. For example, 86 is for China.
URL: Enter the interface URL address to receive the SMS parameters in the gateway.
Encoding, SOAP Version, and Request Type: Select according to the server type.
SMS Message Template: The command template is sent to the SMS server when IAG needs to send messages. It is provided by the SMS server maintenance personnel and imported into this configuration page.
Click Test Validity, and the configuration page for testing SMS appears:
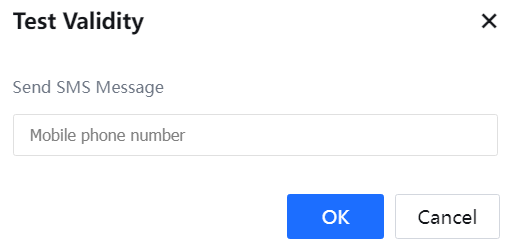
Test Validity tests whether the GSM modem or the SMS gateway can send messages. Enter the phone number for receiving messages and click Commit to send the testing message.
After configuring the SMS notification server, enable it on the SMS platform in Access Mgt > Authentication > Web Authentication > Authentication Server > Add > SMS Based Authentication.[LCH324][A325]
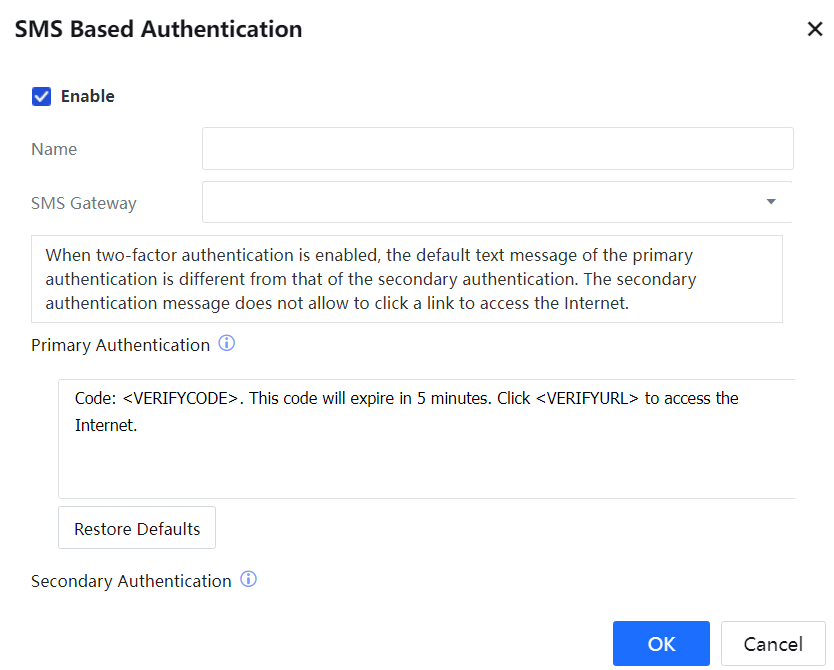
Alternatively, go to System > General > Advanced > Notification > SMS notification, and click Settings [LCH326]to select the configured SMS gateway server.[A327]

Sangfor's modems are shown in the picture below, having two types: GSM and CDMA.

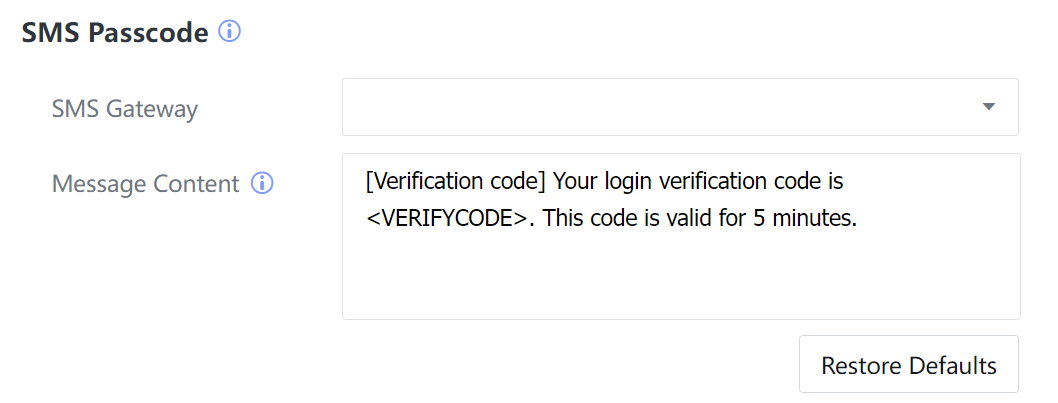
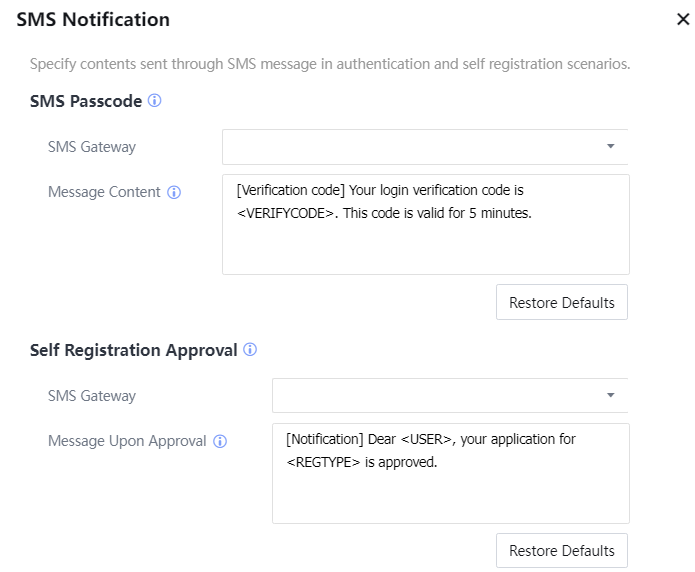
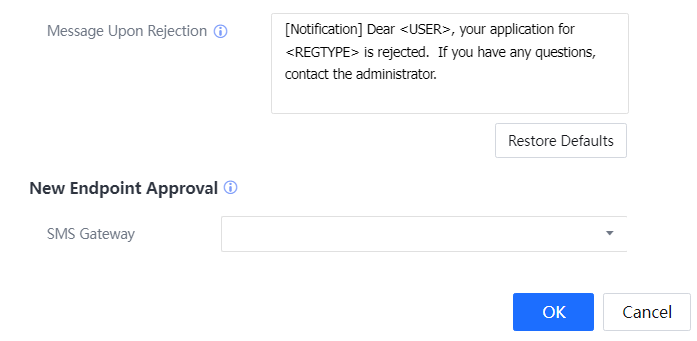
Configure SMS Notification. Select the SMS server, and define SMS content. It supports SMS passwords, self-registration approval, and new endpoint approval.
3.11.5.10.14.2 Email Notification Server
Configure the email notification server:
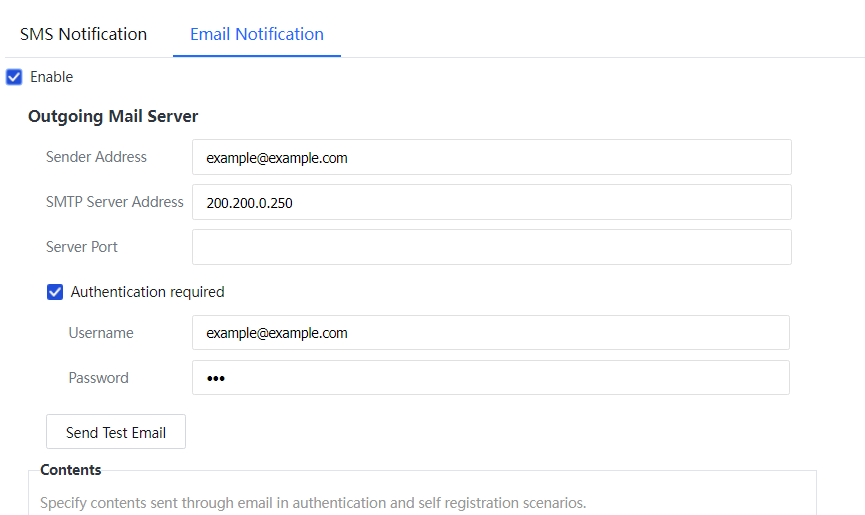
The notification content supports authentication verification and self-registration approval: