It consists of LAN Services, VPN Interface, LDAP Server, and Radius Server Settings.
LAN Services
The IAG can assign access permissions to VPN users, allow a specific IP address or mobile user in the intranet of a branch to access only the specified intranet services provided by specified computers, and set service parameters of inbound and outbound policies for third-party device interconnection. By assigning service access permissions, the device can manage VPN channel security.
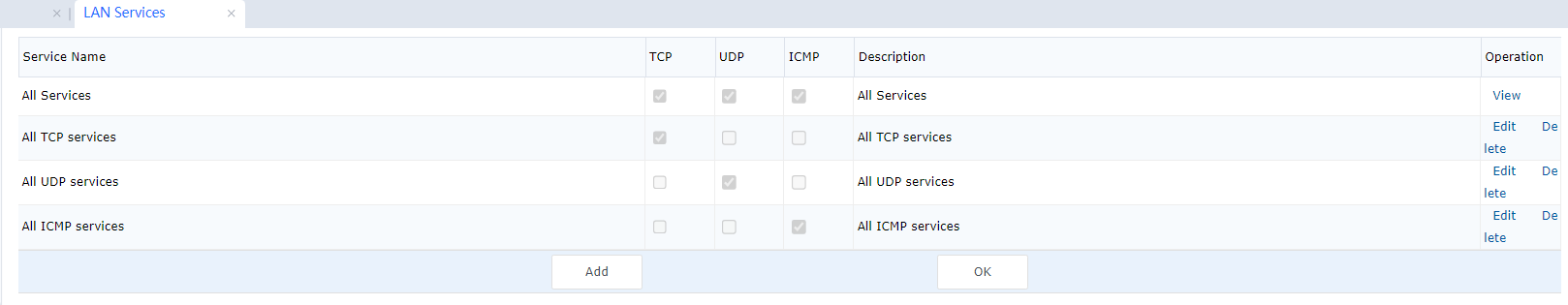
Assigning intranet service permissions includes two steps: creating LAN services and giving permissions to users. By default, the system does not impose access permission limits on VPN users. The following provides an example:
The branch user branch1 with the intranet IP address 172.16.1.200 can access only the HQ's FTP server, whose IP address is 192.168.1.20. Access requests from other IP addresses and requests for accessing other services are rejected. The configuration procedure is as follows:
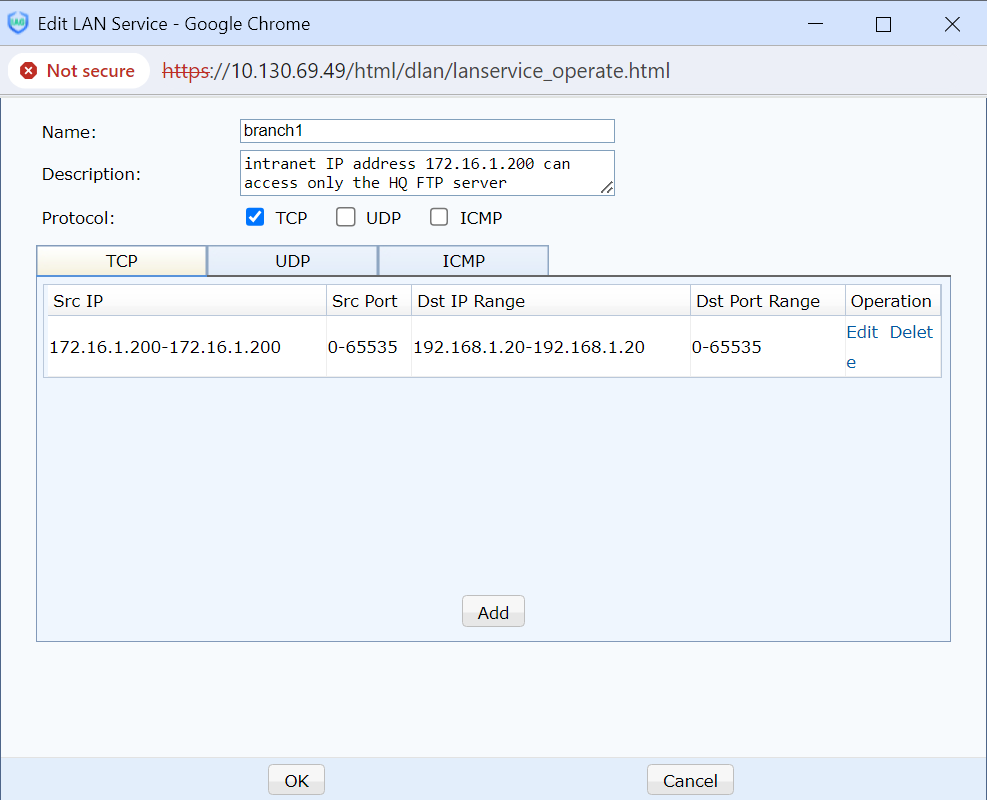
In the LAN Services window, click Add. The Edit LAN Service dialog box is displayed. You can set the Name to a value that can be easily identified. Select a protocol type. (In this example, the FTP service uses the TCP protocol.) See the following figure.
- Click Add. The Edit IP/Port box is displayed. Set the parameters. See the following figure.
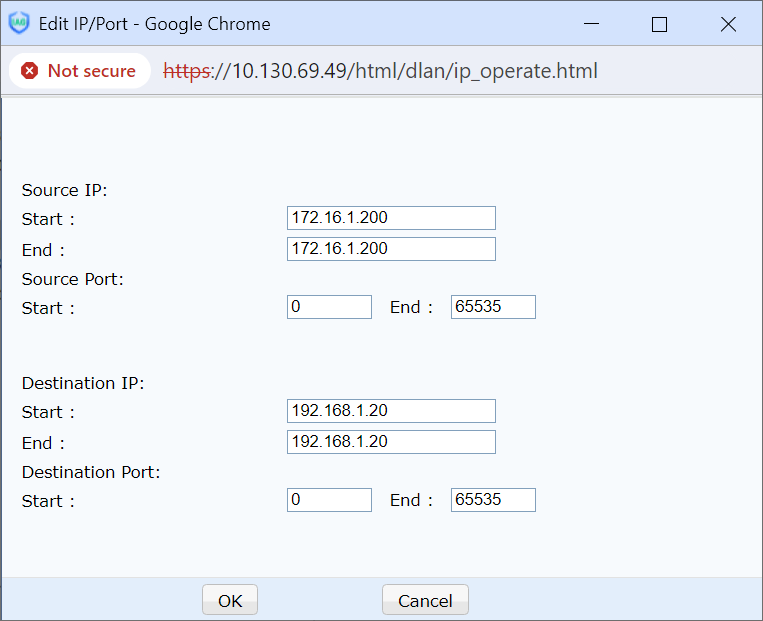
Source IP Address: In this example, set it to the intranet IP address 172.16.1.200 of the peer end in the branch.
Source Port: It ranges from 1 to 65535.
Destination IP Address: In this example, set it to the IP address 192.168.1.20 of the FTP server in the HQ's intranet.
Destination Port: The FTP service port number is 20 or 21.

The intranet service settings configured here are definitions. You then must assign intranet permissions to user accounts in the User Management window. The settings can also be used as the parameters for Local Service in Outbound Policy and Peer Service in Inbound Policy for interconnection with third parties.
- Select Branch1 in the User Management window and click Permission Settings.[A280] See the following figure.[LCH281][A282]
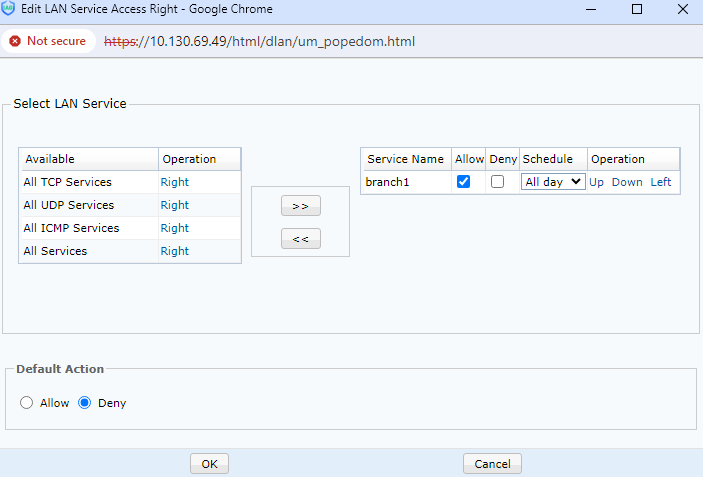
- In the Allow dialog box[A283], move the service configured for Branch1 to the list on the right and select Allow. In this example, only the service is allowed. Therefore, set Default Action to Reject.
After the preceding steps, the branch user branch1 with the intranet IP address 172.16.1.200 can access the HQ's FTP server at 192.168.1.20. FTP server access requests from other IP addresses in the same intranet as Branch1 are rejected.

After the settings are configured, computers at the HQ cannot access Branch1, because the destination IP addresses contained in Branch1's responses to the access requests from the computers are not 192.168.1.20. The responses are blocked according to the intranet permission settings.
VPN Interface
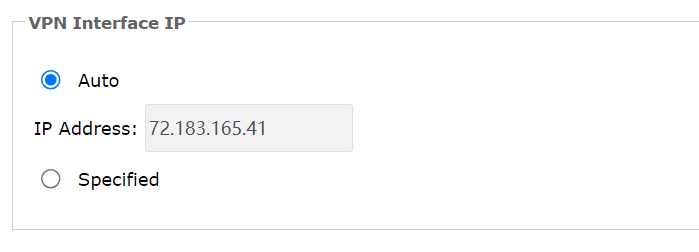
Set the intranet interface mask of the IPSec VPN service and the IP address and mask of the VPN virtual network adapter for the device. See the following figure.
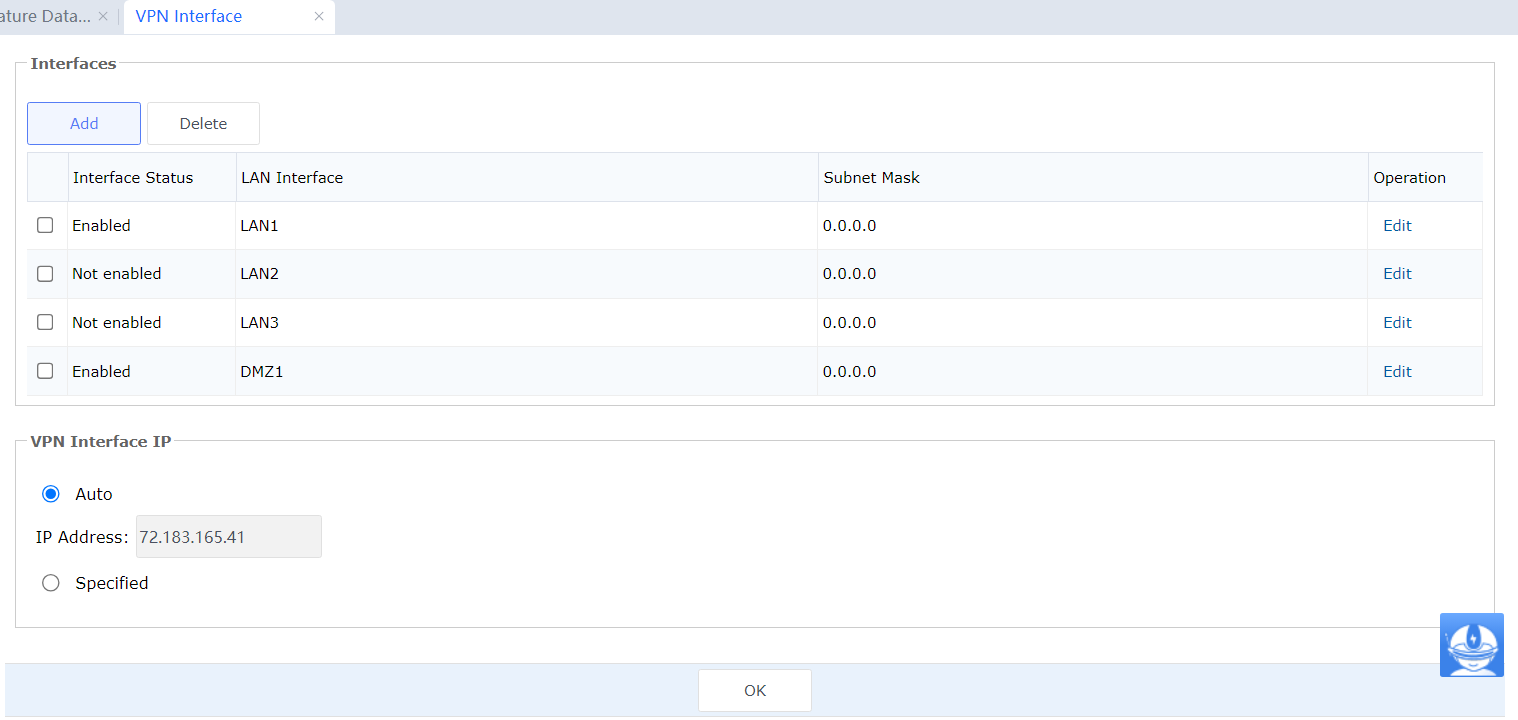
VPN Intranet Settings: Notify the peer VPN device of the mask of the local VPN network segment. If you select an interface mask, the network segment corresponding to the mask is notified to the peer VPN device. If the network segment connected to the DMZ port needs to access the VPN, select the DMZ port and set a subnet mask.
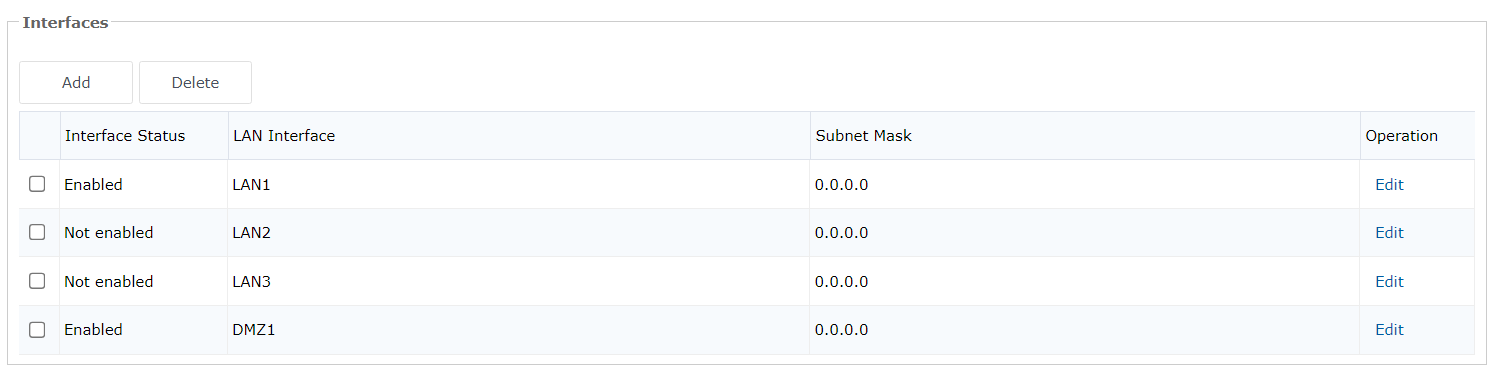
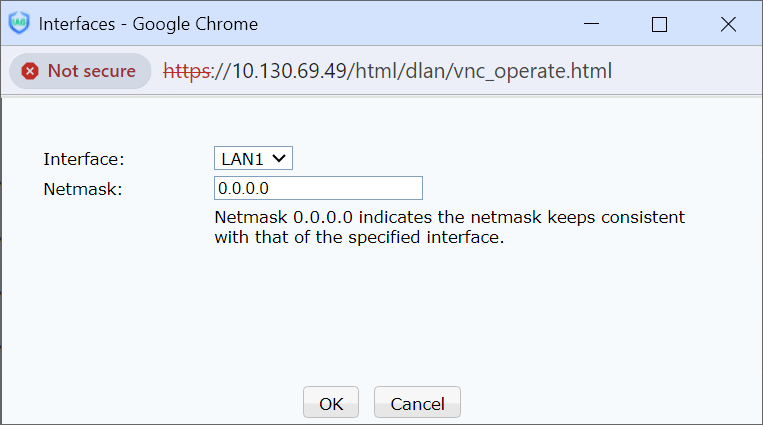
Click Add, add an idle intranet interface, and set the intranet mask of the local VPN device. The value 0.0.0.0 indicates that the mask of the network port is used.
You can select an intranet interface and click Delete to delete it.
You can click Edit and modify the masks of selected intranet interfaces.
Local VPN Interface Settings: Set the IP address and mask of the VPN virtual network adapter of the device. Generally, the default IP address is recommended. However, if an IP address conflict occurs, you can click Specified and enter an IP address not in use.

The VPN interface is a virtual interface of the device but not a physical interface.

Generally, Automatically Assigned VPN Interface IP Address is recommended. However, if an IP conflict occurs, enter an IP address manually. Click Save.

If the configuration is incorrect, an error is reported. See the following figure.
If the Saving settings fails is displayed in the upper-left corner. You can click View Error Information to view the details.
After you click View Error Information, a page detailing the error's cause is displayed.
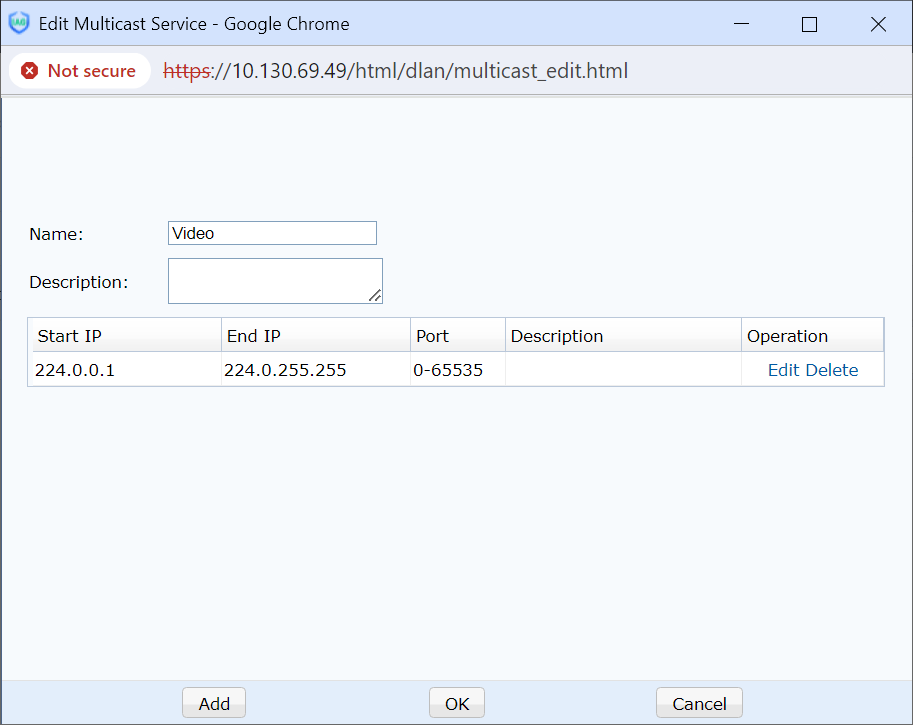
Multicast Service
To meet the requirements of applications such as VoIP and video conferencing applications, Sangfor 's VPN gateway supports the inter-channel multicast service. You can define the multicast service. The IP address range is 224.0.0.1 to 239.255.255.255, and the port number range is 1 to 65535. See the following figure.
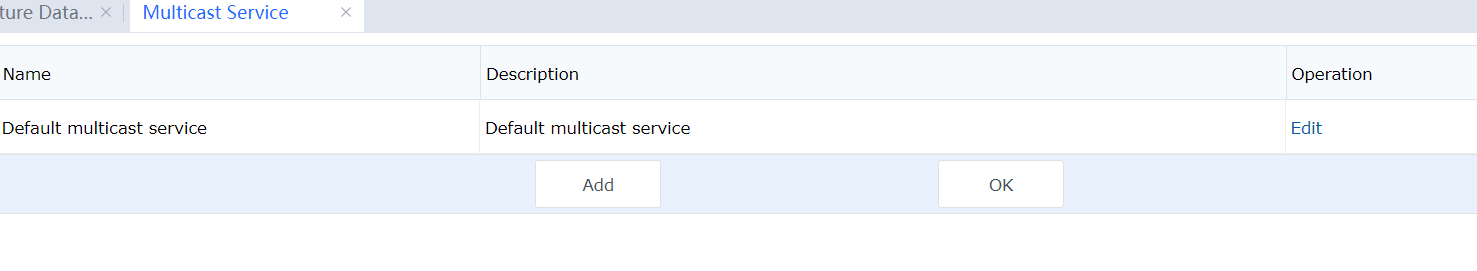
When you click Add, the multicast service editing page is displayed. You can set the IP address and port number of the service. See the following figure.
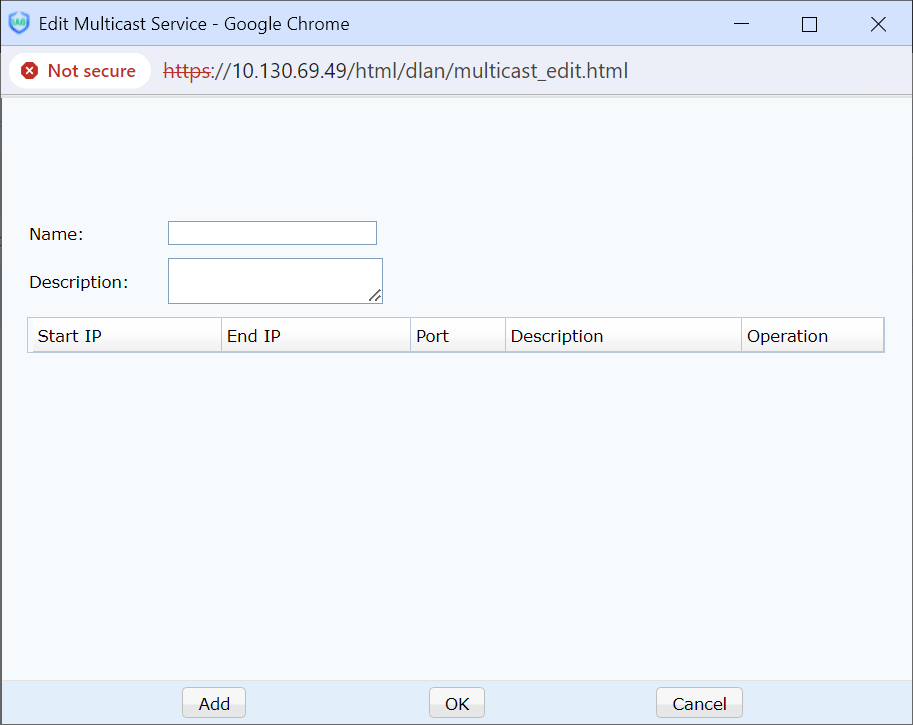
Click Add and add IP addresses and port numbers. See the following figure.
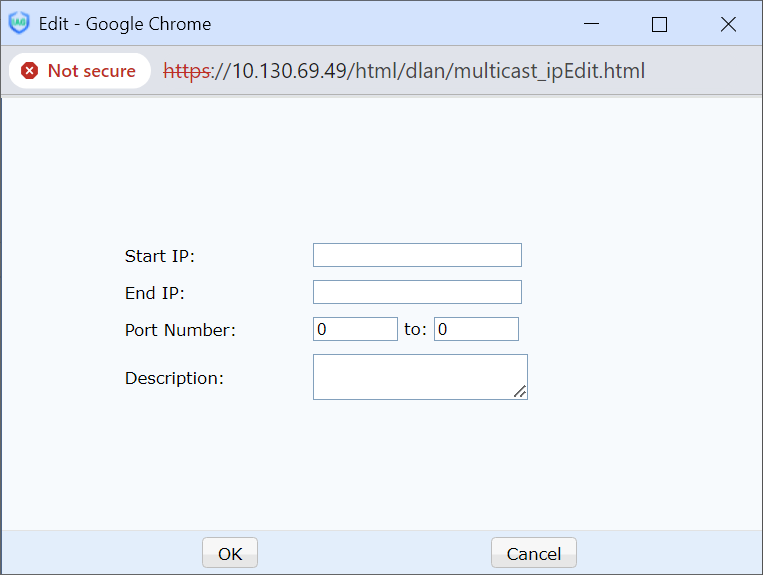
Click OK[A284]. See the following figure.
When creating a user in the User Management window, select the multicast service in Multicast Service. See the following figure.
LDAP Server Settings
The VPN service of the IAG supports third-party LDAP authentication. If you need to enable this-party LDAP authentication, set LDAP information on the LDAP Server Settings tab page (including the LDAP server's IP address, port number, and administrator password). See the following figure.
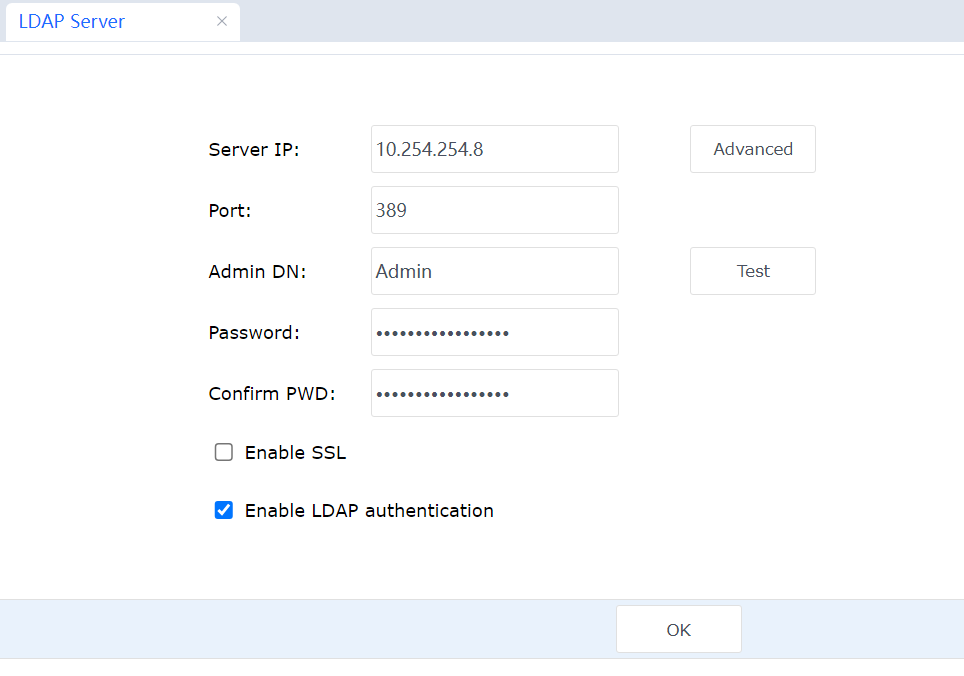
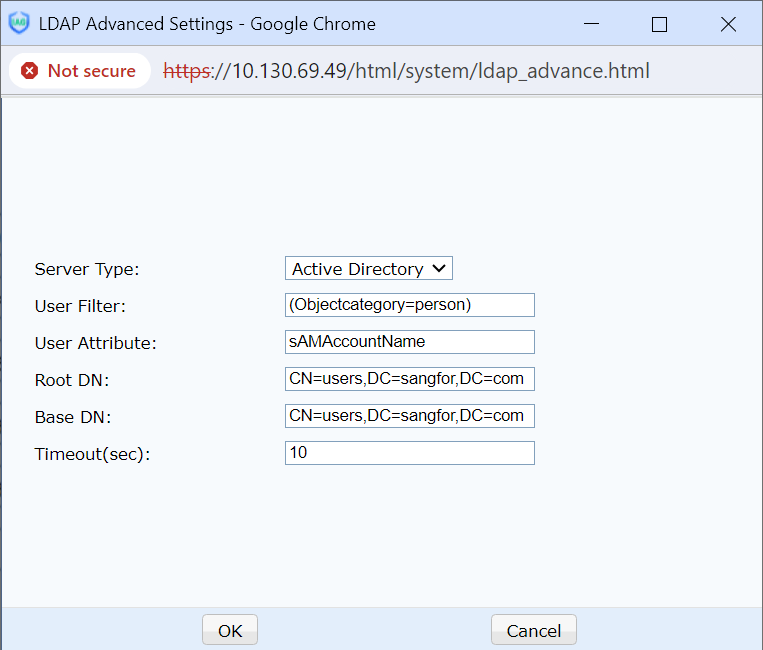
Set the LDAP server information and click Advanced. The LDAP Advanced Settings dialog box is displayed. Set the parameters as required. See the following figure.
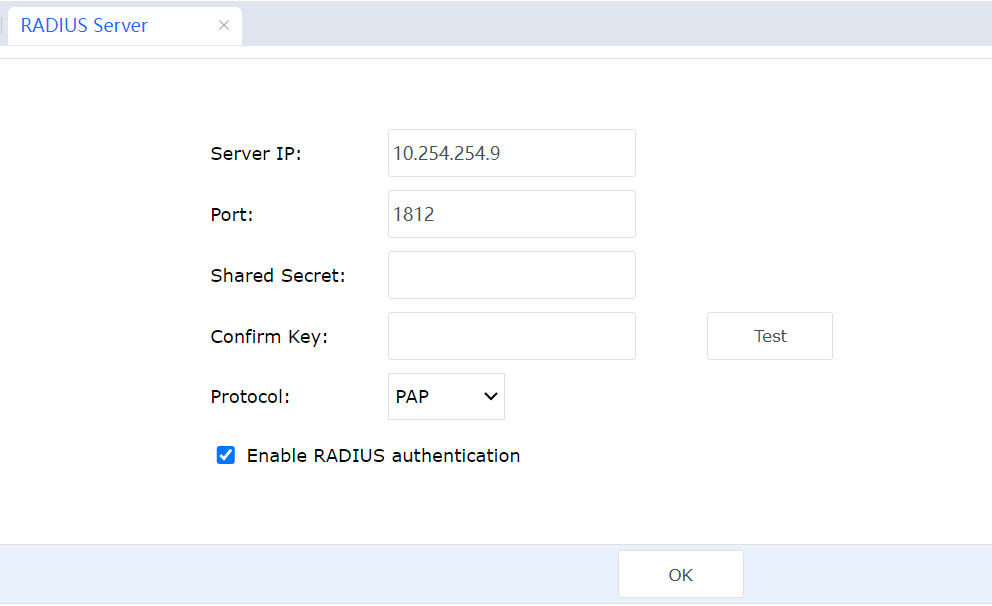
Radius Server
The VPN service of the IAG supports third-party Radius authentication. If you need to enable third-party Radius authentication, set Radius information on the Radius Server tab page (including the IP address, port number, shared key, and Radius protocol of the Radius server). See the following figure.