The IAG provides a function for interconnecting with third-party VPN devices. It can set up standard IPSec VPN connections with third-party VPN devices.
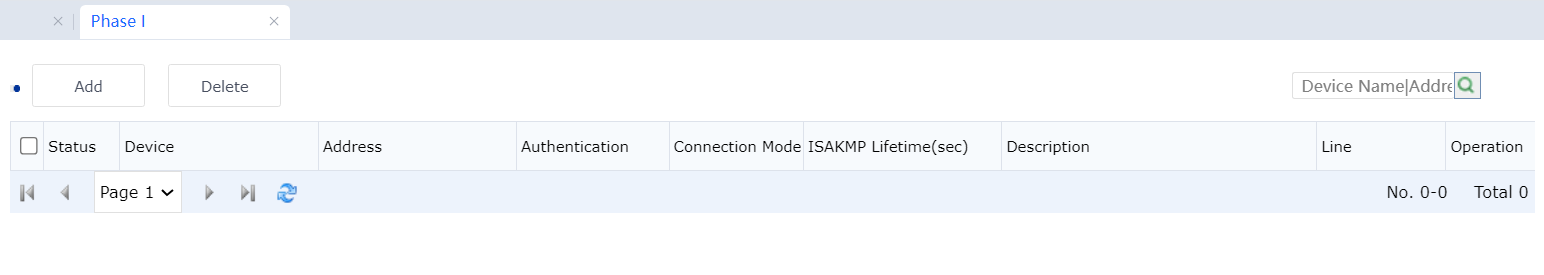
Phase 1
Set the information about the VPN devices that must set up standard IPSec connections with the IAG. See the following figure.
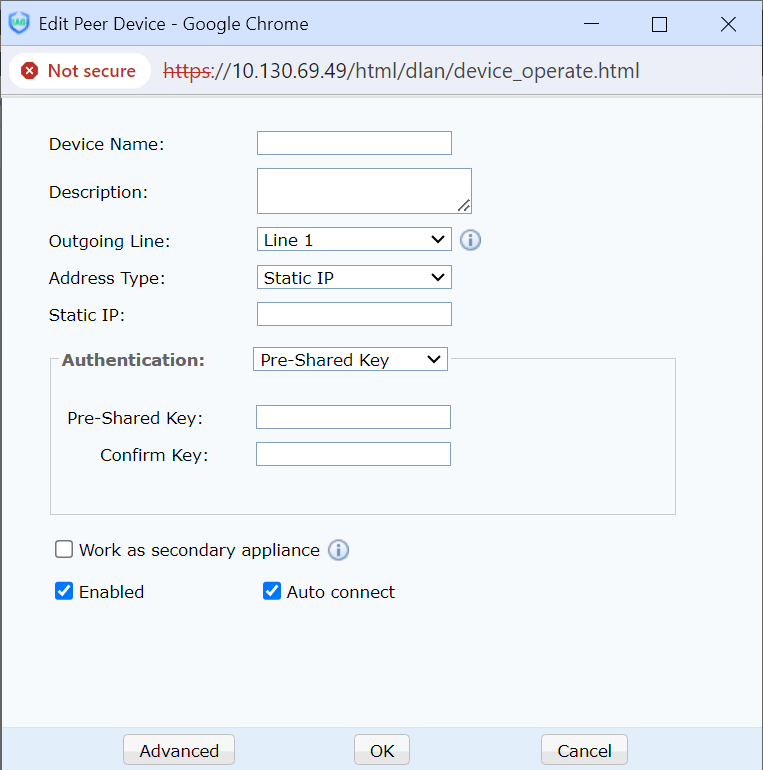
Outgoing Line: indicates the line used to set up standard IPSec VPN connections with the peer end. Select a line egress and click Add. The Edit Peer Device dialog box is displayed. See the following figure.
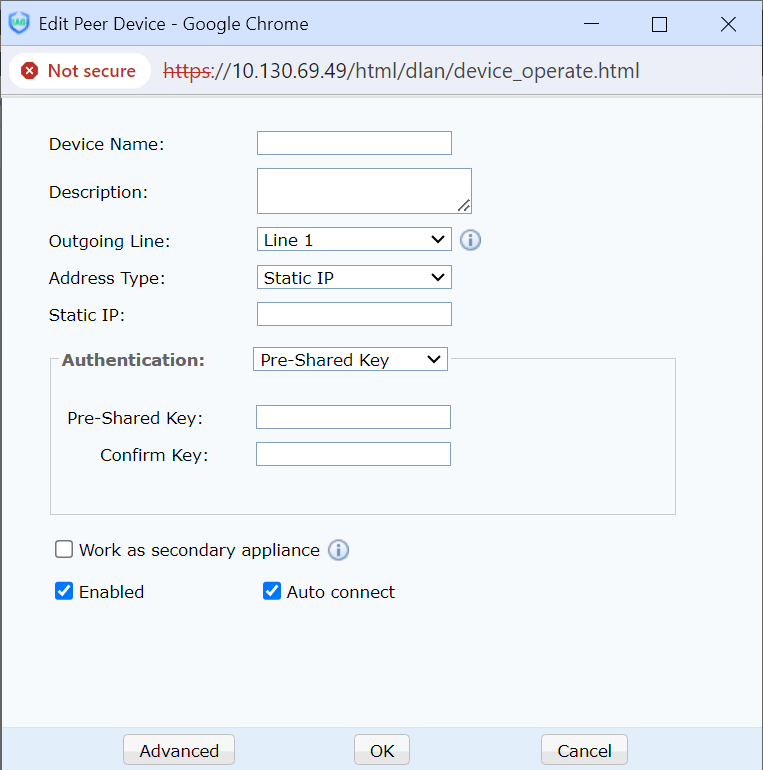
Device Name: Define the name of the phase I policy.
Description: Add a policy description.
Address Type: The types include fixed IP address, dynamic IP address, and dynamic domain name. If you select Static IP, you must enter the fixed IP address and the pre-shared key. See the following figure.
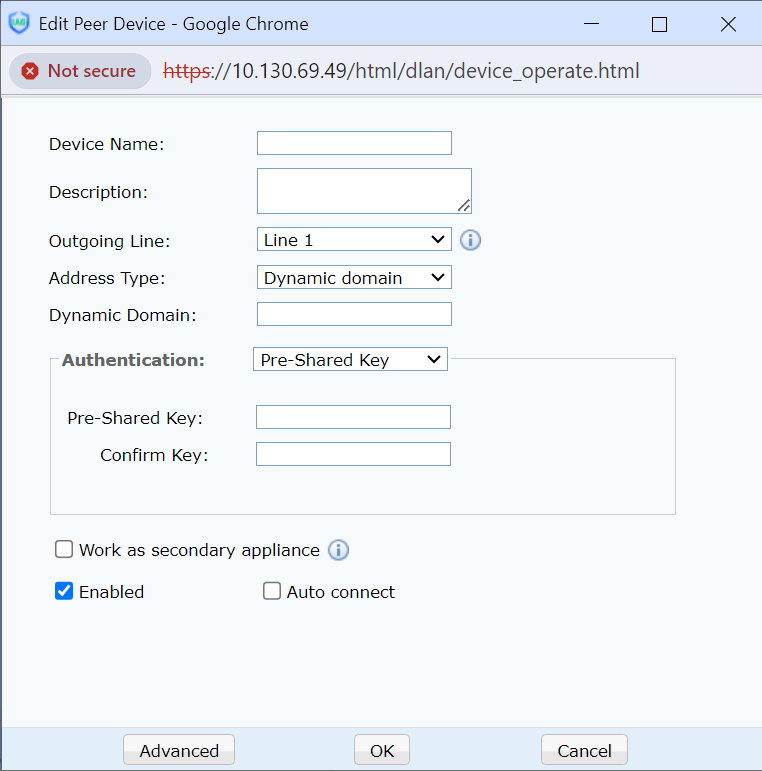
If you select Dynamic Domain, you must set the dynamic domain name and the pre-shared key. See the following figure.
If you select Dynamic IP Address, you must set the pre-shared key. In this case, connections can be set up only in the aggressive mode. See the following figure.
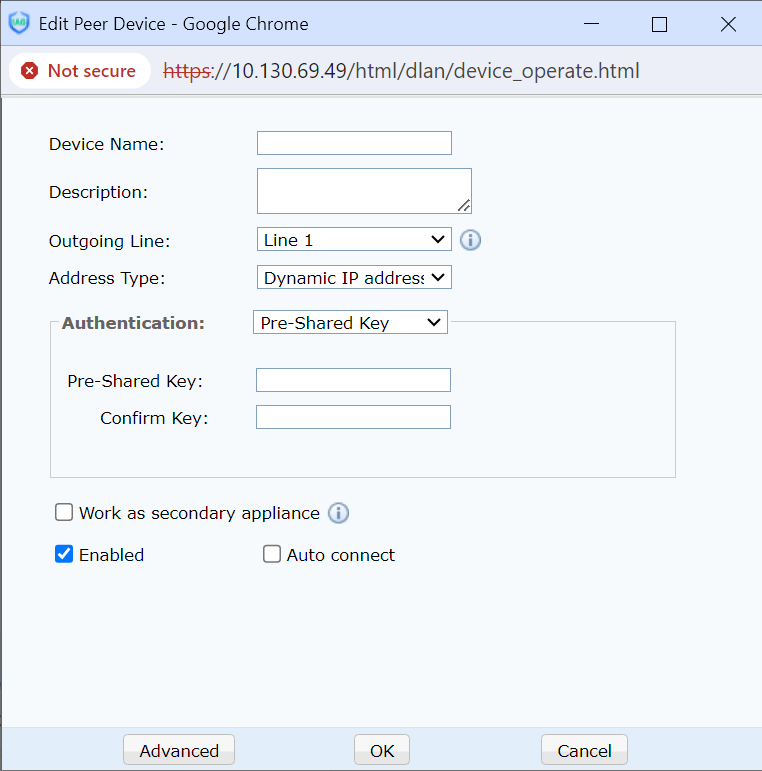
Work as secondary appliance: The same device supports backup tunnels. If the master and backup tunnels are established and the master tunnel is disconnected, data packets will only be sent to the opposite endpoint through the backup tunnel.
When you click Advanced, the Advanced Settings dialog box is displayed. See the following figure.
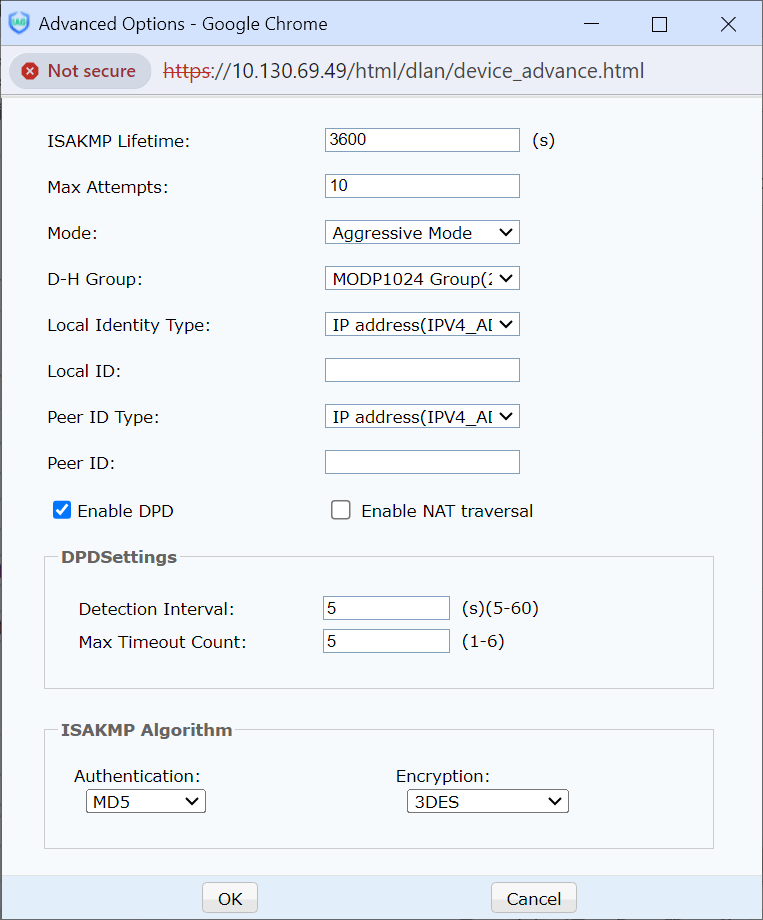
ISAKMP Lifetime: Set the survival period of the phase I policy. The unit can only be second.
Max Attempts: Set the number of retries during negotiation at phase I.
Mode: Specifies the negotiation modes supported in phase I, including the main and aggressive modes.
D-H Group: Set the Differ-Hellman group for the two parties performing negotiation. The options include MODP768 Group (1), MODP1024 Group (2), and MODP1536 Group (5).
Select Enable DPD to enable the DPD function, which helps a VPN device detect faults at the peer end of a channel.
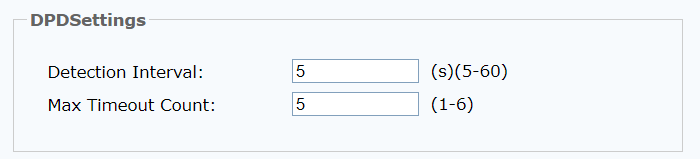
Detection Interval: Set the interval for detecting the peer end status. It ranges from 5s to 60s.
Max Timeout Count: Set the number of times that detecting the peer end status times out. It ranges from 1 to 6. It is regarded that the peer end device is faulty when the number reaches its max.
ISAKMP algorithm list:
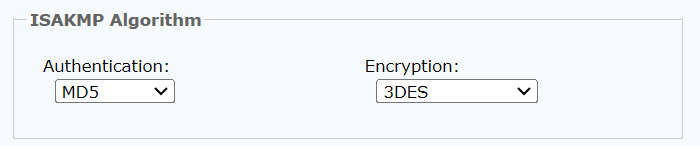
Authentication: Select an authentication algorithm. The options include MD5, SHA-1, and SM3.
Encryption: Select an encryption algorithm. The options include DES, 3DES, AES, SANGFOR_DES, SCB2, and SM4.
Click Save to enable the configured policy.

1. Standard IPSec supports only the routing mode but does not support the bridge and one-armed mode. Standard IPSec does not allow both ends to set their peers to the dynamic IP address mode at the same time.
2. If you set ISAKMP Encryption Algorithm to SANGFOR_DES, both ends must be Sangfor devices.
Phase 2
Configure the inbound policy and outbound policy of VPNs. See the following figure.
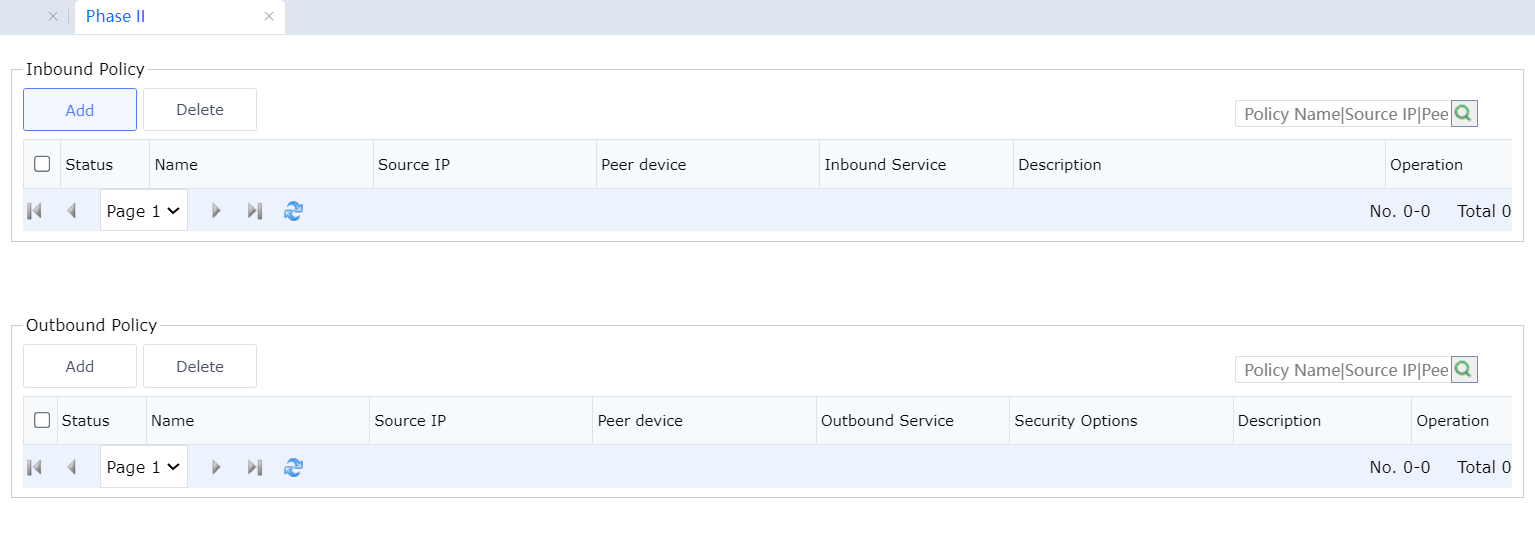
 [LCH273][274]
[LCH273][274]
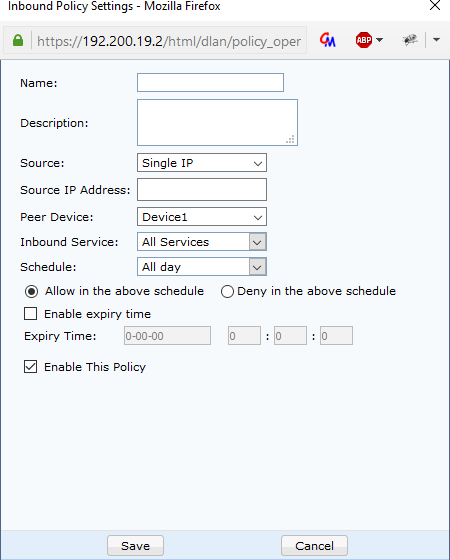
Inbound Policy Settings send rules for the packets sent from the peer end to the local end. Click Add. The Policy Setup dialog box is displayed. See the following figure.
Policy Name: Define the name of the inbound policy.
Description: Add a policy description.
Source Type: Indicates the IP address or IP address segment of the VPN peer end allowed to access the local end.
Peer Device: Select the peer device defined in phase I.
Inbound Service: Select the services that can access the local device. The services must be predefined at System > Sangfor VPN > Advanced > LAN Services.
Expiry Time: Set the effective time of a policy. The time must be predefined at System > VPN > Objects > Schedule.[LCH275][A276]
You can select Enable Expiry Time and set the expiration time of the policy. Select Enable This Policy and click Save.
Outbound Policy Send rules for the packets sent from the local end to the peer end. Click Add. The Policy Setup dialog box is displayed. See the following figure. 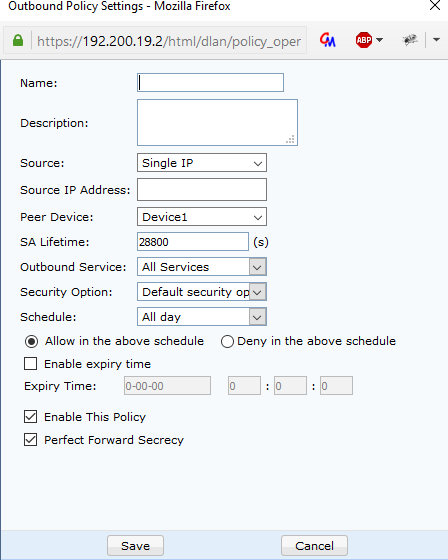
Policy Name: Define the name of the outbound policy.
Description: Add a policy description.
Source: Indicates the IP address or IP address segment of the VPN local end allowed to access the peer end.
Peer Device: Select the peer device defined in phase I.
SA Lifetime: Set the survival period of the phase II policy. The unit can only be second. Outbound Service: Select the services that can access the peer device. The services must be predefined at System > Sangfor VPN > Advanced Settings > LAN Services.
Security Options: Select the security policy for negotiation. Configure the policy on the Security Options tab page.
Expiry Time: Set the effective time of a policy. The time must be predefined at System > VPN > Objects > Schedule.[LCH277][A278]
You can select Enable Expiry Time and set the expiration time of the policy.
Select Enable This Policy. If the peer end adopts PFS, select Enable Perfect Forward Secrecy. Click Save.

1. If PFS is enabled, the DH groups set in phase I and II for the peer VPN device must be the same. Otherwise, IPSec VPN connections cannot be set up.
2. The outbound service, inbound server, and time settings for outbound and inbound policies are extended rules of Sangfor. The rules are effective only for the local device and are not negotiated when VPN connections are set up with third-party devices. The source IP addresses in outbound and inbound policies correspond to Source and Peer Service.




