The IAG provides a powerful Tunnel Route function for VPNs. It enables interconnection among VPNs (software/hardware) to create a real mesh VPN network.
For example, the HQ (Shenzhen 192.168.1.x/24) and the branches (Shanghai 172.16.1.x/24 and Guangzhou 10.1.1.x/24) set up VPN connections (the branches connect to the HQ through connection management), but the two branches do not have VPN connections. A Tunnel Route rule can be set to connect the branches. The configuration procedure is as follows:
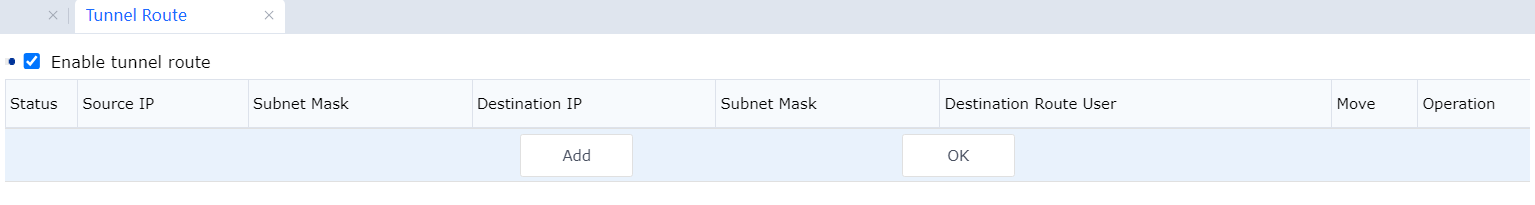
- Select Enable Routing in the Tunnel Route Settings window for the Shanghai branch, click Add, and add the route to the Guangzhou branch. See the following figure.
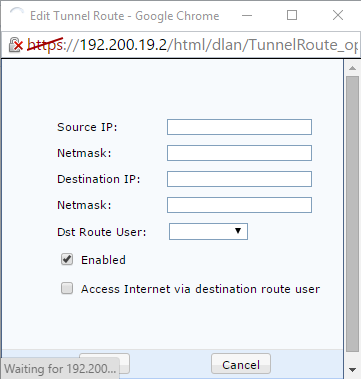
Source IP: Indicates the network ID of the source IP address. In this example, set it to 172.16.1.0. Subnet Mask (Source): Indicates the subnet mask of the source IP address. In this example, set it to 255.255.255.0.
Destination IP: Indicates the network ID of the destination IP address. In this example, set it to 10.1.1.0.
NetMask: Indicates the subnet mask of the destination IP address. In this example, set it to 255.255.255.0.
Dst Route User: Indicates the VPN user to whom the route points.

Source IP and Destination IP are used to match the source IP address and destination IP addresses of data. When data in a VPN channel matches the settings, the route is used to send the data to the specified VPN device. Destination User indicates the destination VPN device of data to be routed. In this example, the username shanghai is specified in the Connection Management window for the Shanghai branch to connect to the HQ through a VPN. Therefore, data with the username shanghai is sent to the HQ.
- Select Enable Routing in the Tunnel Route Settings window for the Guangzhou branch, click New, and add the route to the Shanghai branch. See the following figure.
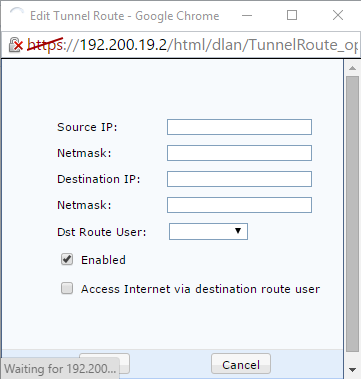
Source IP: Indicates the network ID of the source IP address. In this example, set it to 10.1.1.0. Subnet Mask (Source): Indicates the subnet mask of the source IP address. In this example, set it to 255.255.255.0.
Destination IP: Indicates the network ID of the destination IP address. In this example, set it to 172.16.1.0.
Netmask: Indicates the subnet mask of the destination IP address. In this example, set it to 255.255.255.0.
Dst Route User: Indicates the VPN user to whom the route points. In this example, set it to Guangzhou.
The Tunnel Route function can also be configured to send branches' Internet data to the HQ, which is forwarded to the Internet through the HQ's Internet egress. For example, you can set the Shanghai branch to access the Internet through the HQ.

If a branch accesses the Internet through the HQ, you must choose System > Firewall > NAT Proxy and [LCH271][272]add proxy rules for VPN network segments. For details, see the firewall setup description.




