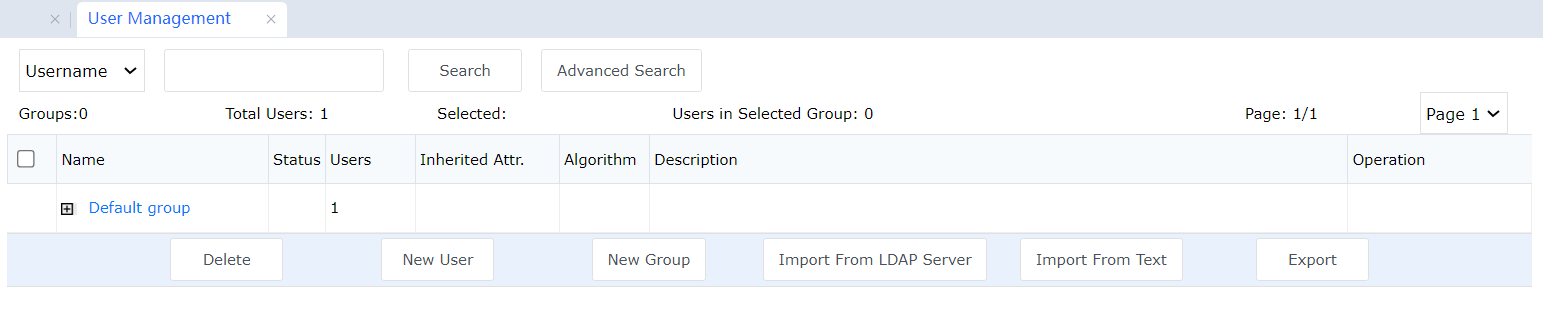
Manage VPN connection account information, set the usernames and passwords that can be used to connect to VPNs, and specify whether to enable hardware authentication or DKEY authentication.
Select whether to use virtual IP addresses, set the account encryption algorithm and account validity period, assign intranet permissions to accounts, group users, and set common attributes for group members. See the following figure.
When you click Detect USB-Key, the system checks whether the computer used to log in to the gateway console is connected with a USB key. If no USB key driver is installed, it asks you whether to download the driver. You can click Download USB Key Driver to download the driver and then install it.

Before generating a USB key, you must install the USB key driver. Otherwise, the computer cannot identify the USB key hardware. To prevent USB key installation failures caused by program conflict, exit the third-party antivirus and firewall software during driver installation.
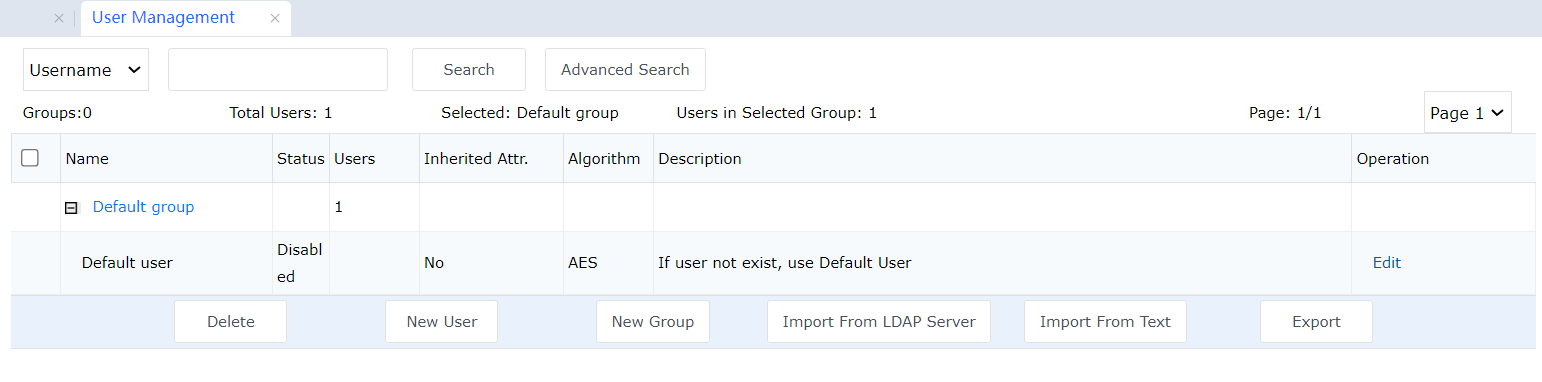
You can enter a username or user group, click Search to find the user or user group, and then edit the found user or user group. A found user is highlighted. See the following figure:
You can click Advanced Search and set filters for searching for users. You can select the username fuzzy match option. (If it is not selected, an exact keyword match is implemented. Separate keywords using a comma.) The search result includes the following information: user group, group attribute (unlimited, enabled, or disabled), status (unlimited, enabled, or disabled), type (unlimited, mobile, or branch), DKEY status (unlimited, enabled, or disabled), and user idleness duration (unlimited, one year, one month, one week, or user-defined). See the following figure.
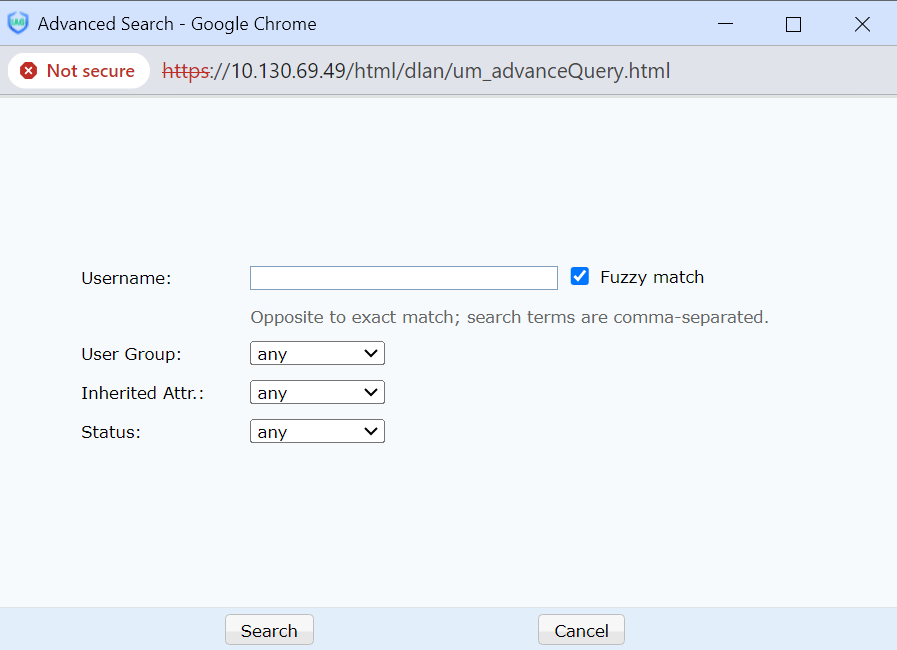
You can click Search to search for information. You can click Cancel to cancel information.
You can click Delete to delete selected users.
You can click New User to set account information, including the username, password, description, algorithm, and type. See the following figure.
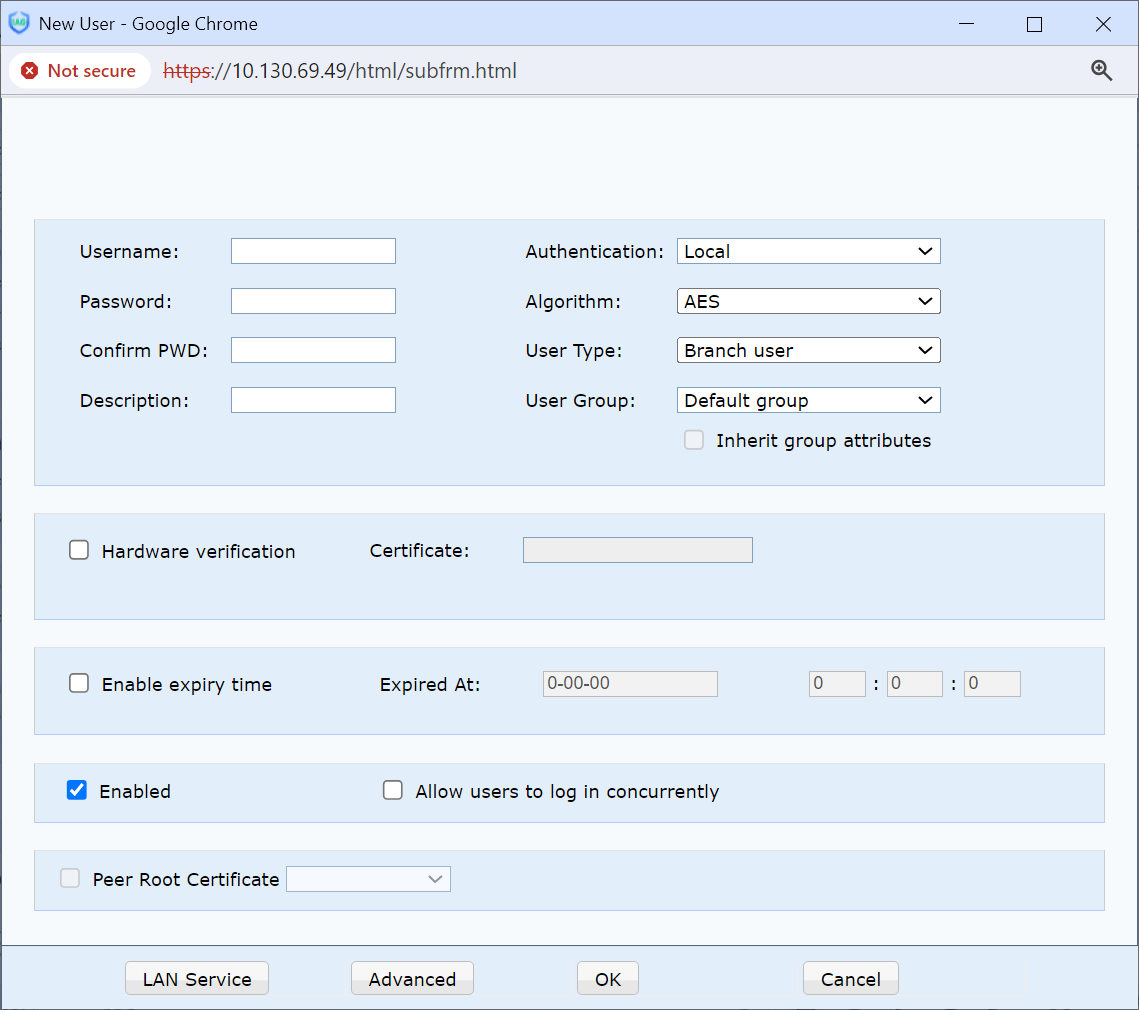
Username: Define the username. If the authentication method is certificate authentication, the username must be the same as the Issued to the field of the site certificate.
Password: Set a password.
Confirm Password: Make sure that the password is correctly set.
Description: Add a description of a new user to facilitate management.
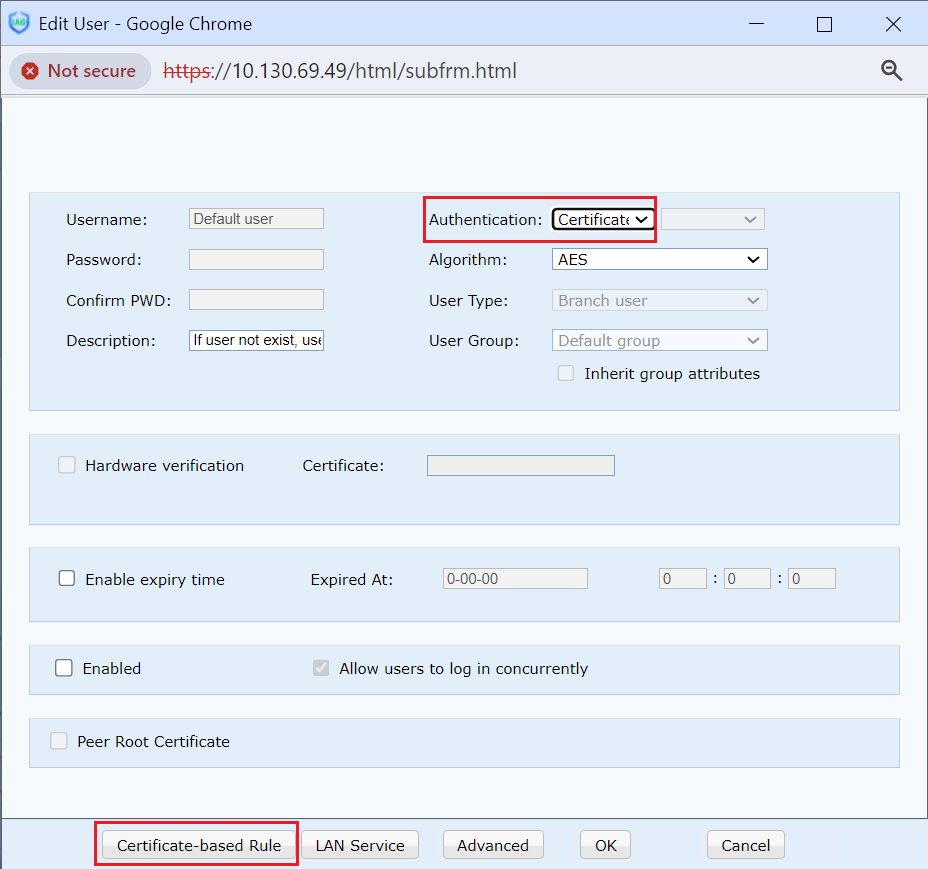
Authentication: Set user authentication types, including local authentication (i.e., hardware device authentication), LDAP authentication, RADIUS authentication, and certificate authentication.

Before using Radius authentication or LDAP authentication, set the authentication server in
LDP Authentication or Radius Authentication.
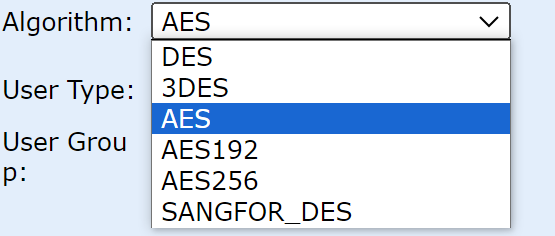
Algorithm: You can select from the DES, 3DES, AES, SANGFOR_DES, AES192, and AES256. Two peers must use the same algorithm.
User Type: Specifies the type of user.
Inherit Group Attributes: To group users. If you select this option, the User Group settings are activated. You can add a user to a user group so that the user uses the common attributes of the group.

Add a user group before using the Inherit Group Attributes option. After a user is added to a group, the Algorithm, Enable My Network Places, Permission Settings, and Advanced parameters cannot be set separately.
Enable Hardware Authentication: Sets certificate authentication based on hardware features. After it is selected, select a certificate file (*.id) corresponding to the user.
Enable DKEY: Specifies whether to enable DKEY authentication for mobile users. If it is selected, connect the DKEY to the computer's USB port and click DKEY Generate DKEY.
Enable Virtual IP Address: Assign a virtual IP address to a mobile user. Suppose Mobile is selected, and a virtual intranet IP address (within the virtual IP address pool) is manually set for the user. In that case, the user uses this IP address as his/her virtual intranet IP address after being connected. If the virtual IP address is 0.0.0.0, the system automatically assigns an intranet IP address from the virtual IP address pool to the user.
Effective Time and Enable Expiry Time: Sets an account's effective time and expiration time.
If a VPN user uses the My Network service, Enable My Network must be selected.
Enable Compression: Use an encryption algorithm to encrypt data transferred between the gateway and a user.

This parameter sets Sangfor 's proprietary VPN technology. It ensures high bandwidth use efficiency when the bandwidth is low and speeds up data transmission. However, it does not apply to all network environments. You can set it based on the actual situation.
Disable Internet Service for the User After Connecting to HQ: This option is valid only for mobile users. If selected, a mobile user connected to a VPN can access the VPN but cannot access the Internet.
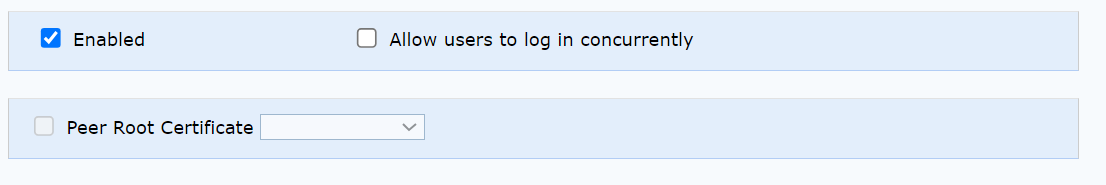
Allow users to log in concurrently: Enable multiple users to log in to a VPN with the same account. Not allow password change online: Specifies whether a mobile user can change its login password after logging in to a VPN. If it is deselected, the password change is allowed.
Edit LAN Service Access Right: Assign permissions to users connected to a VPN. This helps specify the services accessible to users. By default, there is no limit.
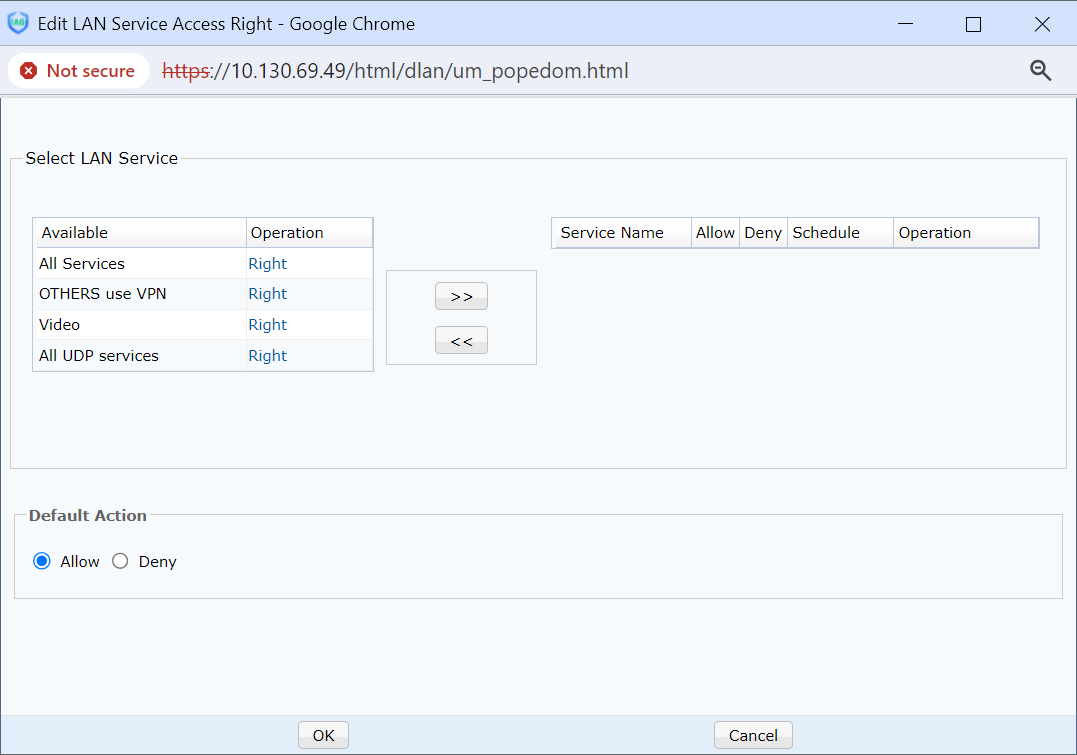

Before assigning permissions, add the required services at Select LAN Service. For details, see the Intranet Service Settings section.
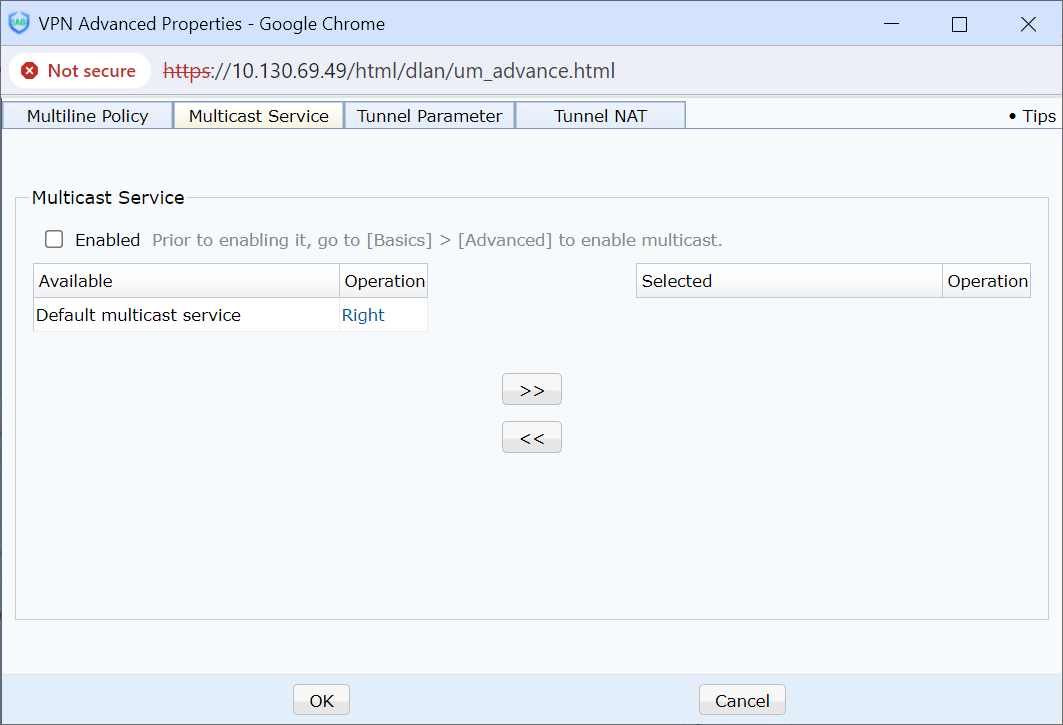
Advanced: Configure advanced attributes applicable to users connected to a VPN, including route selection policy settings, multicast service settings, channel parameter settings, and intra-channel NAT settings. Route selection policy settings are configured to dynamically select the optimal transmission line among multiple lines based on line conditions. Multicast service settings are configured to support the applications such as video applications that use the multicast protocol between servers and branches. Channel parameter settings are configured to control the traffic of branch VPNs. Intra-channel NAT settings are configured to handle the address conflict between two branches when they belong to the same intranet segment and are connected to a server. The following figure shows the configuration page.
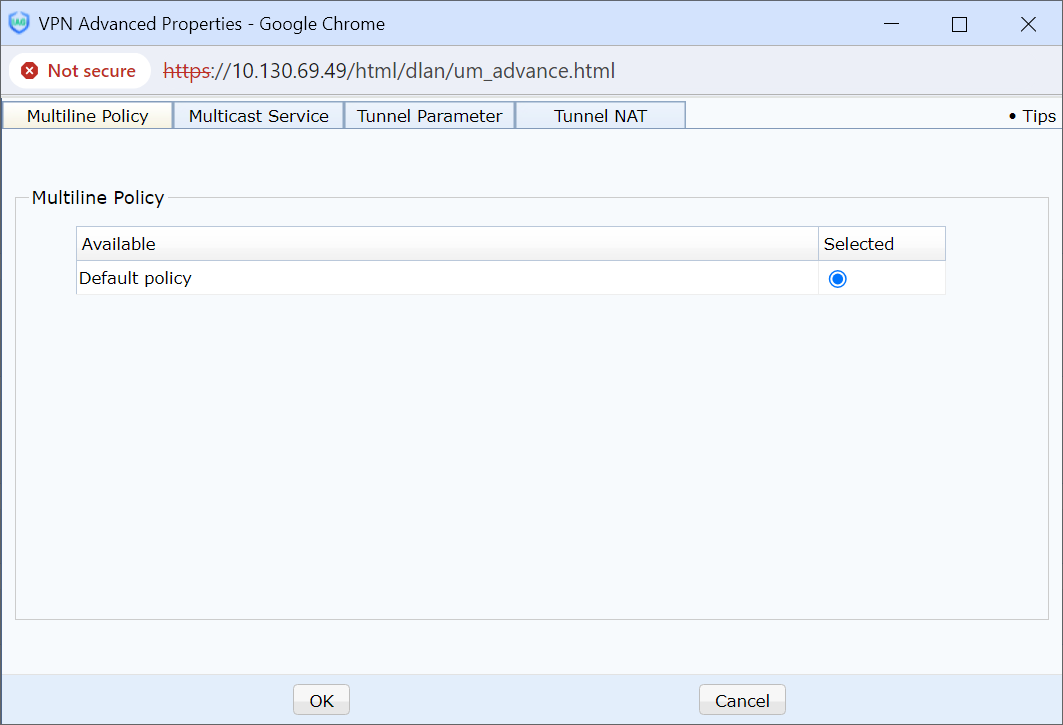
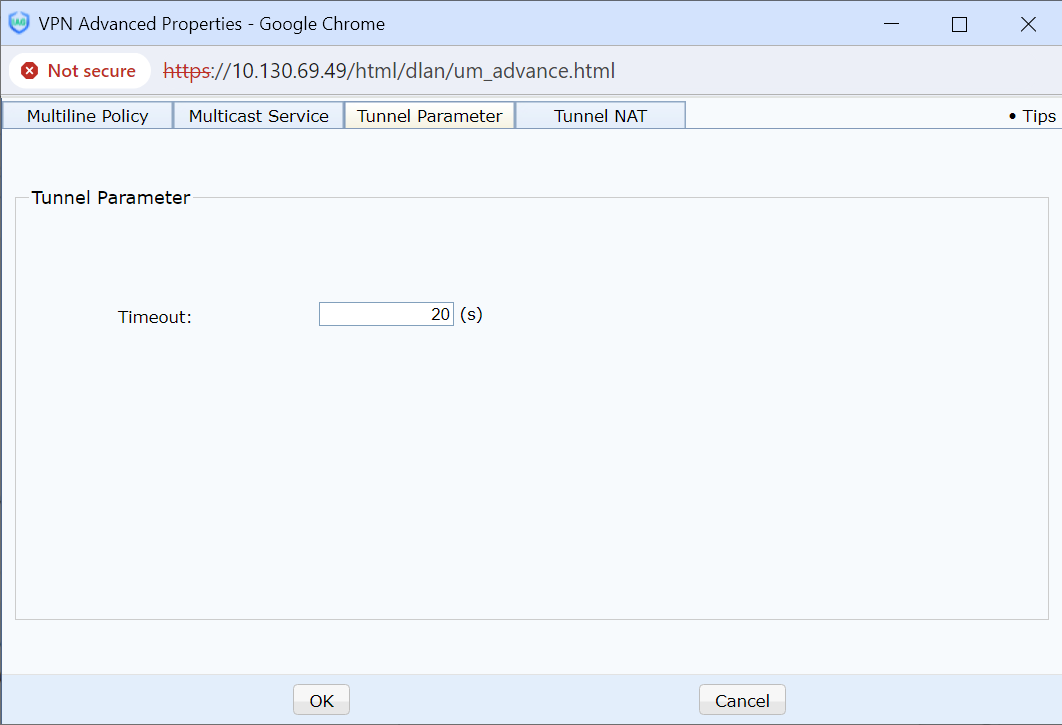
Channel parameter settings cover the VPN channel timeout interval, dynamic rate detection, and channel traffic control.
Timeout: When the network has a significant delay and high packet loss rate, you can set a timeout interval on a Sangfor VPN for the network. The timeout interval of each channel depends on the server configuration. The default timeout interval is 20s. For a poor network environment, you can increase the timeout interval.
Enable tunnel dynamic probe: When the local or peer end has many lines, this option is applicable. After it is selected, the Sangfor VPN regularly detects each line's delay and packet loss rate and selects an optimal line based on the detection result for data transmission.
Enable tunnel traffic control: When there are multiple VPN branches or mobile users, this option prevents one branch or user from occupying all the bandwidth, which slows down data transmission for the other branches or users. You can assign upstream bandwidth and downstream bandwidth to each connected user to ensure each user's appropriate data transmission rate.

The setting of Enable tunnel traffic control is a value range other than a specific value. For example, if you set it to 100 kbps, the bandwidth varies within the 80 to 120 kbps range.
Tunnel NAT: Used to perform SNAT on multiple conflicted site network segments so that each site can access the server and communicate with the server normally without modifying the specific network segment of each site.
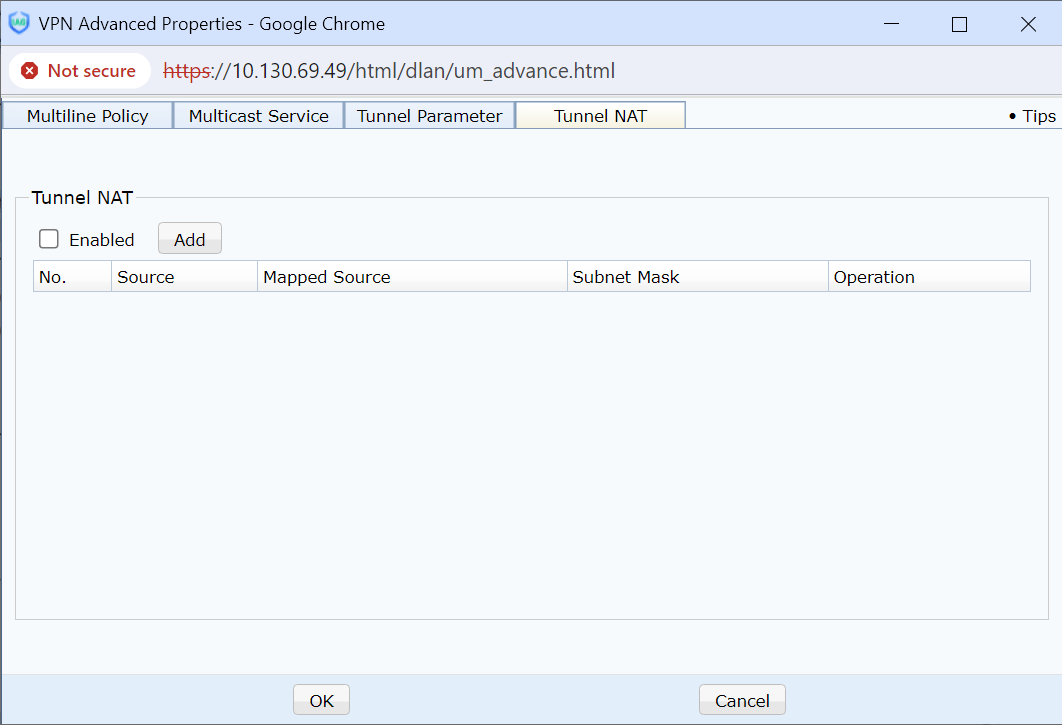

Only site users can enable Tunnel NAT.
Click Add to enter the matched source subnet segment, mapped IP, and netmask [A266]required by this rule in the dialog box and to allow the device to assign an IP segment from the virtual IP pool automatically. The page is as follows:
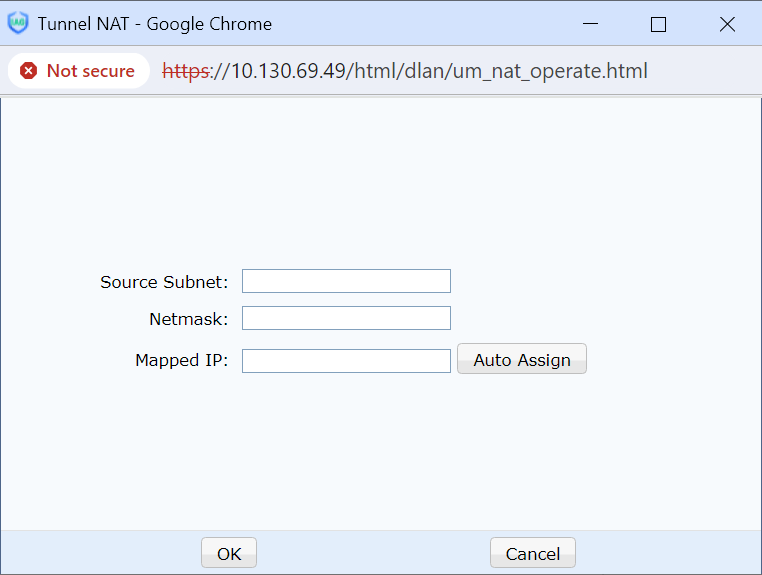
Source Subnet: Real LAN subnet segment of the site.
Mapped IP: Virtual segment of the converted site.
Netmask: Real LAN subnet mask of the site.[LCH267][A268]

The subnet mask must be matched in configuration. NAT in the tunnel only performs NAT on the masked network segment, and the host number remains the same.

Before using Tunnel NAT in Advanced, add the site's required virtual IP network segment in the Virtual IP Pool.
Click New Group to set the user group name, description, and common attributes of group members. The page is as follows:
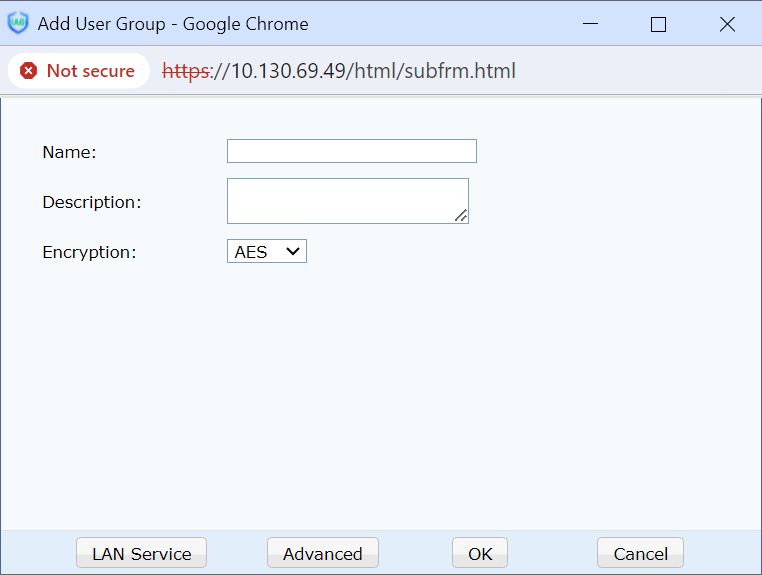
LAN Service and Advanced are the same as those buttons in New User. Please refer to the corresponding description in New User.
Click Import From LDAP Server to import a user account from the LDAP server (set up an LDAP server on the LDAP Settings page before importing). The imported user uses the LDAP authentication method by default and does not contain a password. The page is as follows:
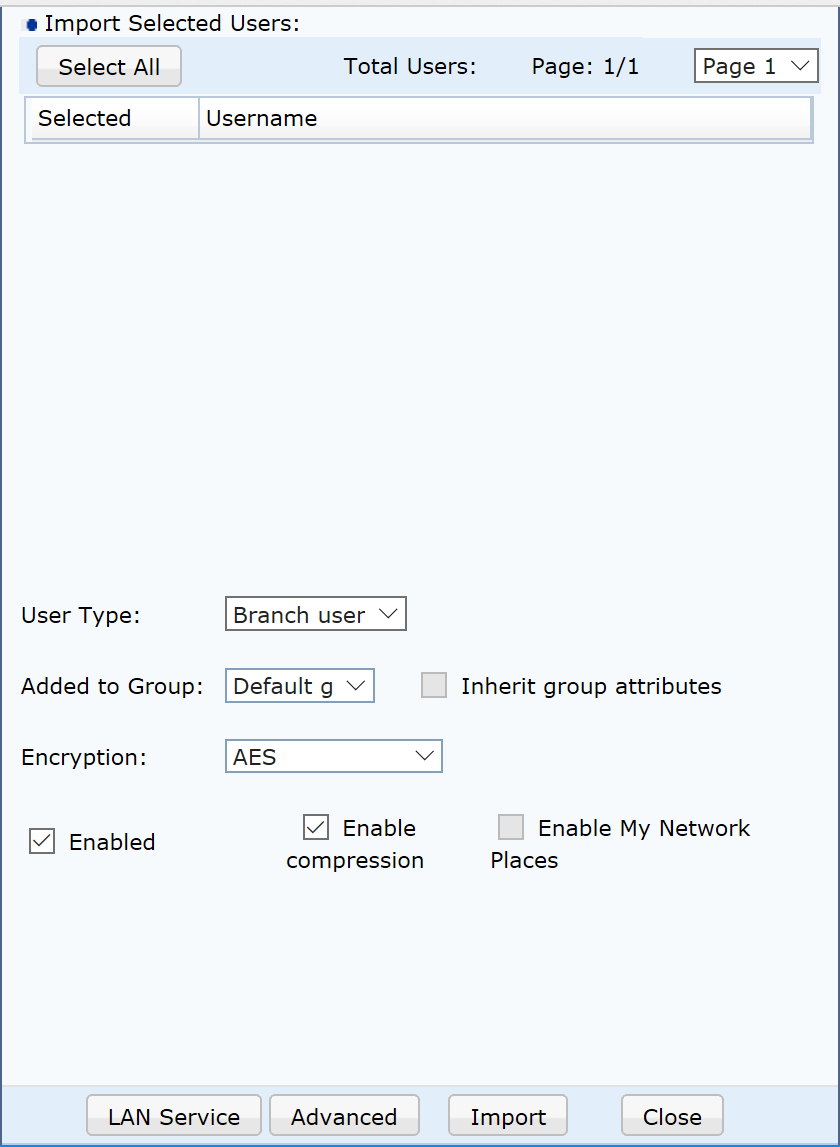
Check the users to be imported, select the user type, including mobile user or branch user, a user group, encryption algorithm, compression, and network neighborhood, and then click Import to import users from the LDAP server into the VPN device.
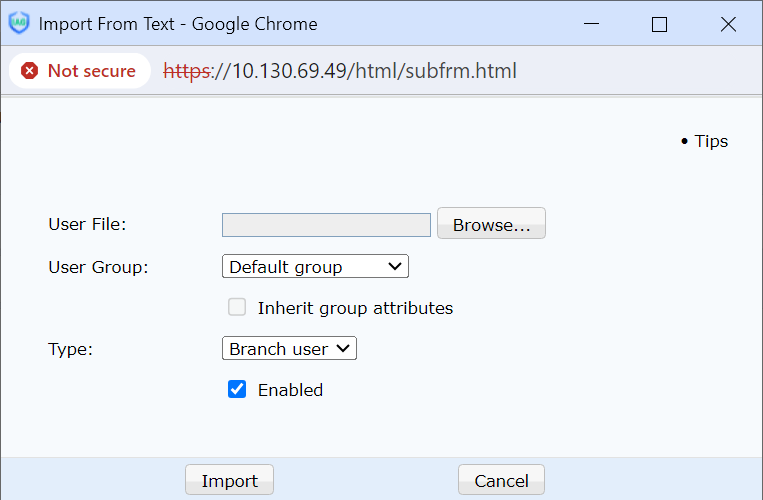
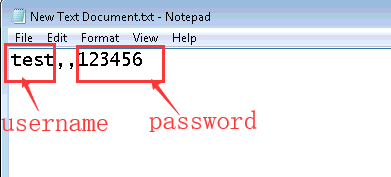
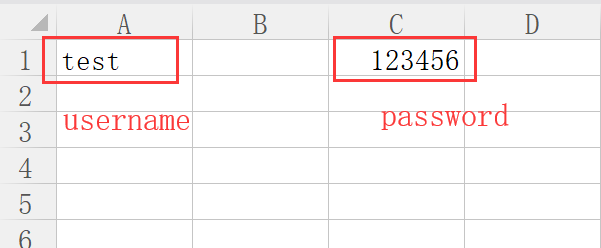
Click Import From Text to import user information from TXT or CSV files. You can choose to import users into a user group and use group properties. You can also set whether the imported user type is mobile or site. TXT file is formatted as username, password, and other users information that cannot be imported. CSV file is formatted the same as TXT files. Replace the English comma with an empty column. The page is as follows:
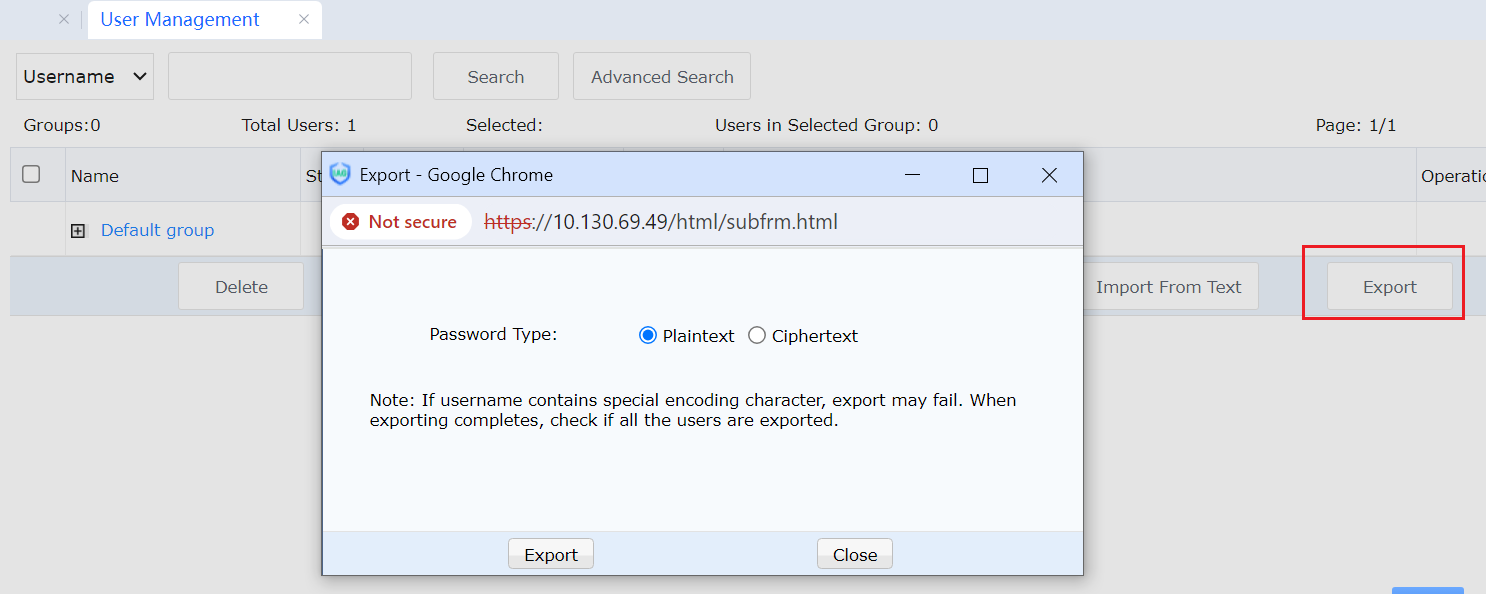
Click Export to export the user from the device to local for saving. You can choose whether the exported user password is encrypted or unencrypted. The page is as follows:
Default User: This will be matched if the user cannot be found in the user list and the authentication method is consistent with the default user. In addition, when there are multiple sites of certificate authentication in LAN, the default user is enabled and selected as certificate authentication, and the corresponding rules are configured. Therefore, it is unnecessary to add certificate authentication users to the user list one by one. The default user with the authentication enabled is configured as follows:
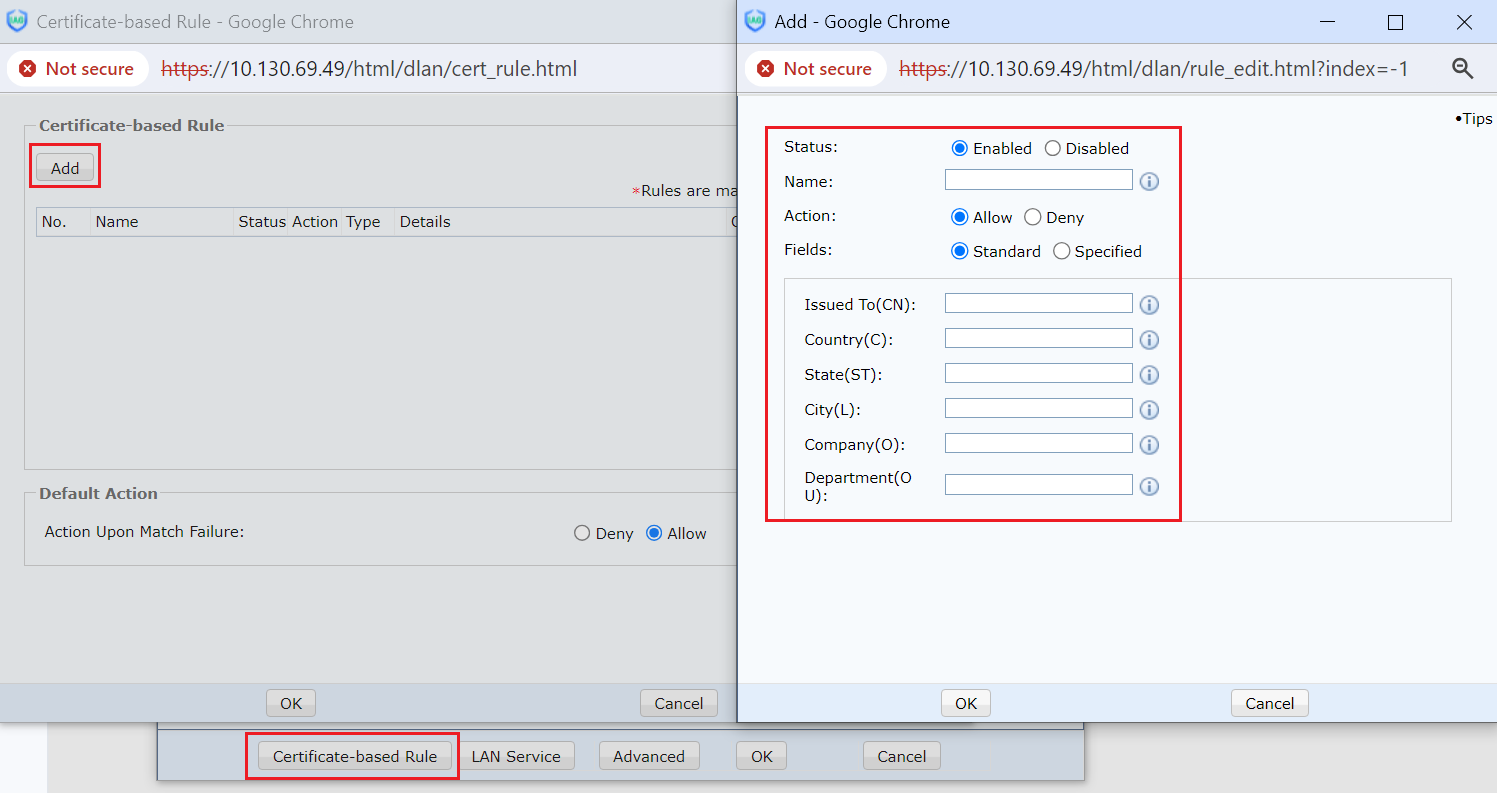
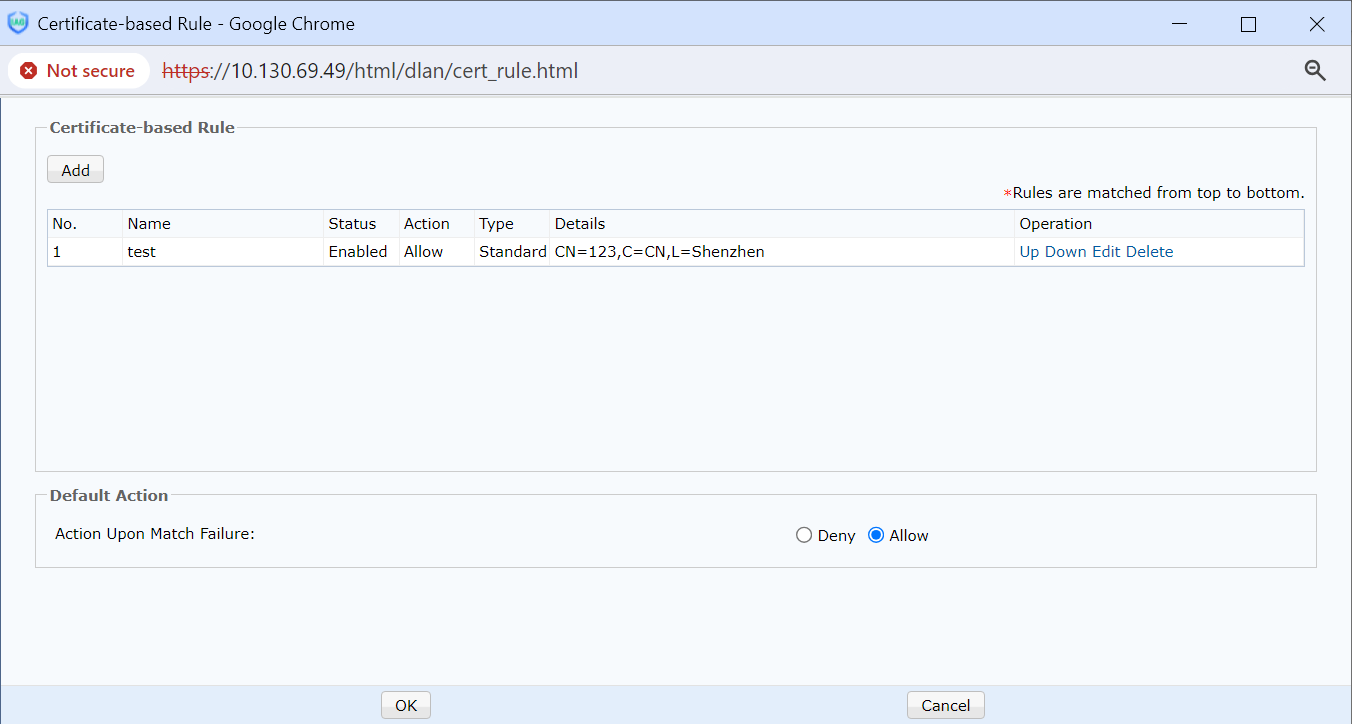
As shown in the above figure, certificate authentication rules are an additional function compared with ordinary users, and the certificate authentication rules can be configured. According to the rules, the peer certificate can be resolved for rule matching. When the matching fails, the default action will be enabled.




