Ingress detection involves detecting PCs on the intranet by using an Ingress program installed on the client. Detected contents include the OS, processes, files, and registries. Encrypted IM chat contents and files transmitted over QQ or MSN can be audited through Ingress control. You can set detection (Ingress) rules on the Ingress Rule Database page, which will be applied on the page displayed after you choose Access Mgt > Endpoint Check > Check Policies.[A224] If an Ingress system is configured, a user can access the Internet only when related rules are met. When a user accesses the Internet for the first time, an Ingress control must be installed. Multiple Ingress rules are embedded into the device. You can also define Ingress rules as required.
Ingress Rules
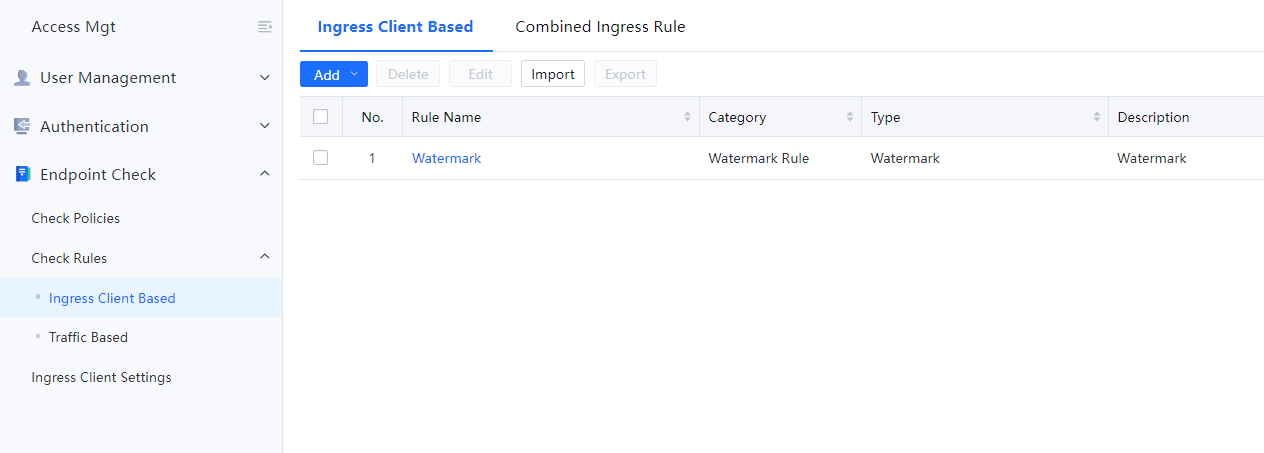
Navigate to Acess Mgt > Endpoint Check > Check Rules > Ingress Client Based. On the Ingress Rules page, you can add or delete Ingress rules.[A225]
Adding Ingress Rules
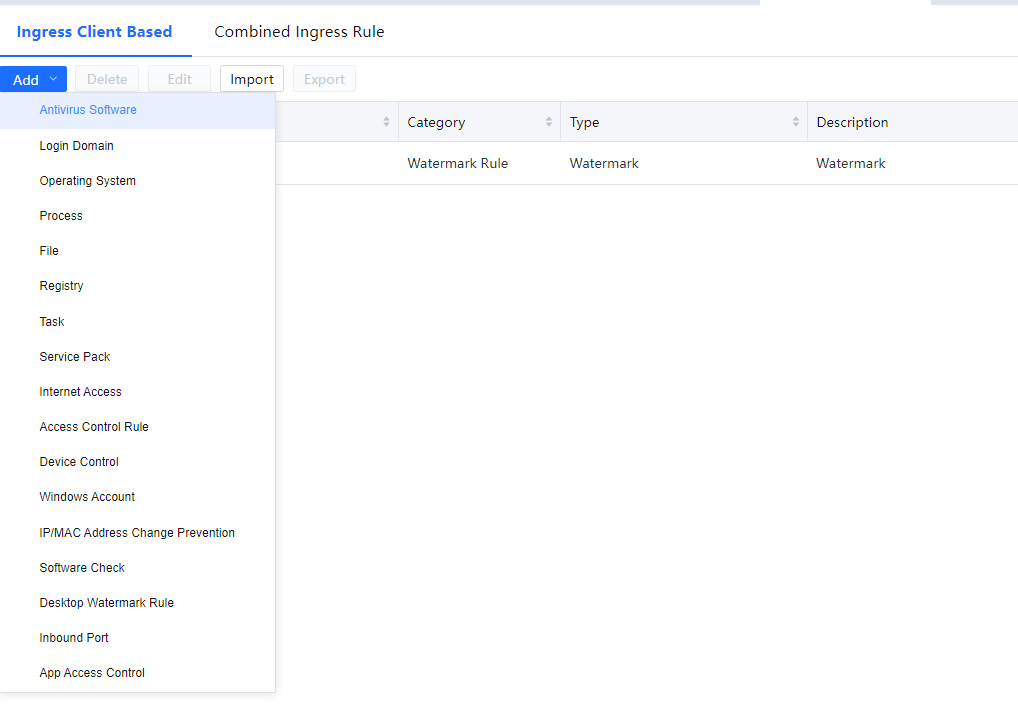
On the Ingress Rules page, click Add and select a rule type, which may be an operating system-based rule, process-based rule, file-based rule, registry-based rule, task-based rule, service pack-based rule, etc. See the following figure.
3.11.1.1.10.1 Adding Operating System Based Rules
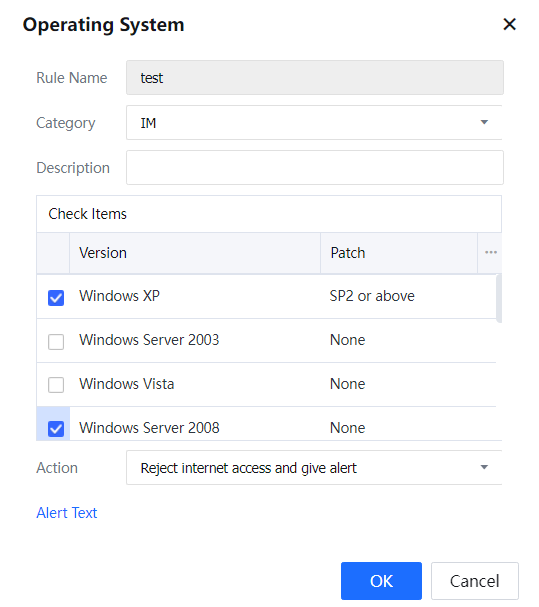
You can set rules for detecting the OS of clients. Go to the Ingress Rules page, click Add, and select Operating System. The Operating System page is displayed.
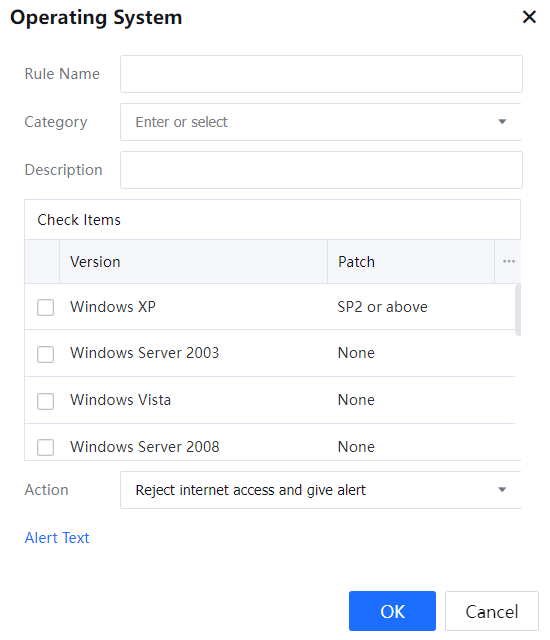
Rule Name: specifies the name of the rule to be added. The length of the rule name must be equal to or shorter than 95 characters.
Category: specifies the type of the rule. You can select a rule type from the drop-down list or enter a rule type. The length of the entered rule type must be equal to or shorter than 95 characters.
Description: specifies the description of the rule.
Check Items[A226] lists the OS versions allowed on intranet PCs that need to access the Internet through the device. For example, Sangfor requires that all PCs on the intranet run Windows XP and that SP4 must be installed on the PCs to protect against viruses. PCs that do not meet the requirements cannot access the Internet through the device. The settings are shown in the following figure.
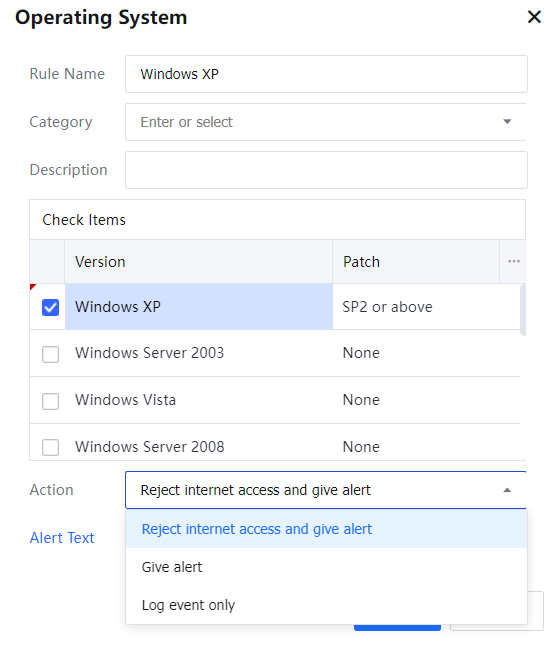
Action: Select the actions of the device on users who do not conform to the rules, such as Reject request and give alert, Give alert, or Log event only (Log event only means that no action is taken on client data, and logs will be recorded in the console and the data center).
3.11.1.1.10.2 Adding Process Based Rules
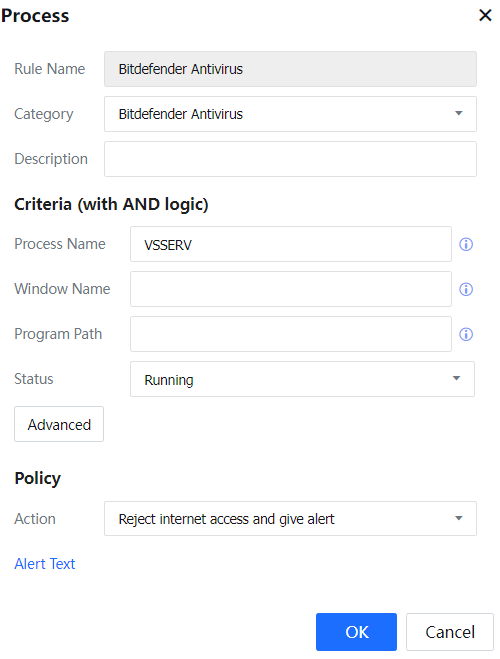
You can set rules for detecting processes running on clients.
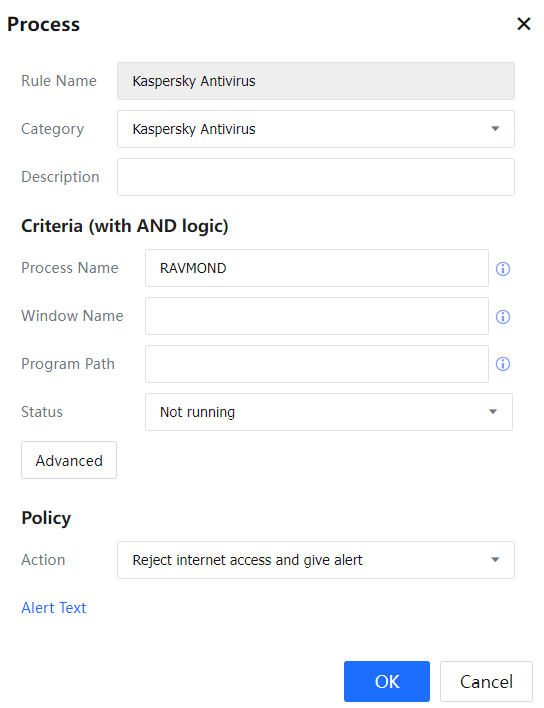
Go to the Ingress Rules page, click Add, and select Process. The Process page is displayed.
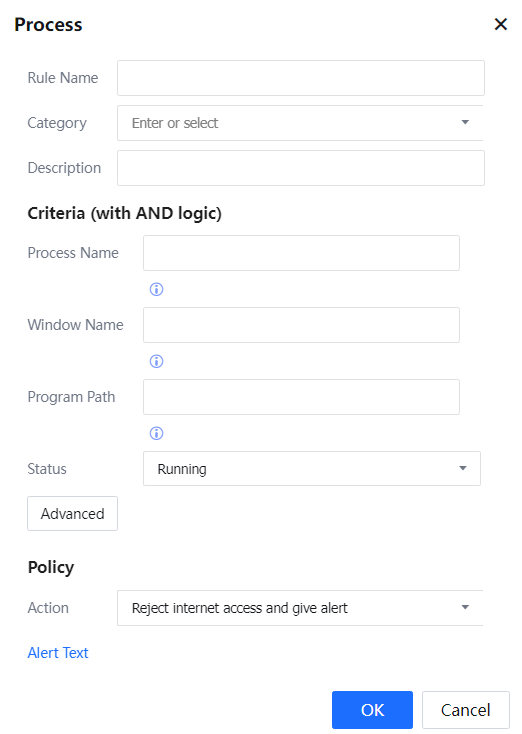
Rule Name: specifies the name of the process rule to be added.
Category: specifies the type of the rule. You can select an embedded rule type or define one.
Description: specifies the description of the rule.
Status: specifies the status of processes to which the rule is applied. If Running is selected, you can select Reject request and give alert, Stop the process, Give alert, or Report only from Action.
If Not running is selected, you can select Reject request and give alert, Start process, Give alert, or Report only from Action.
Process Name: specifies the full name of a process. No wildcard is supported.
Window Name: specifies the full name of a window. No wildcard is supported.
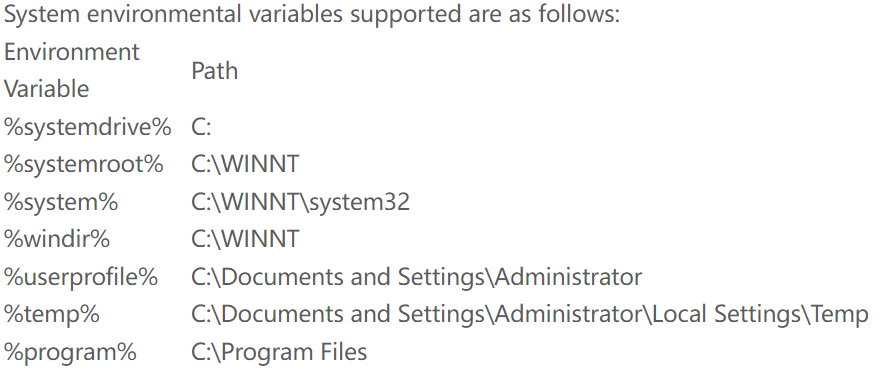
Program Path: specifies the installation path of the program. System environment variables are supported. See the following figure.
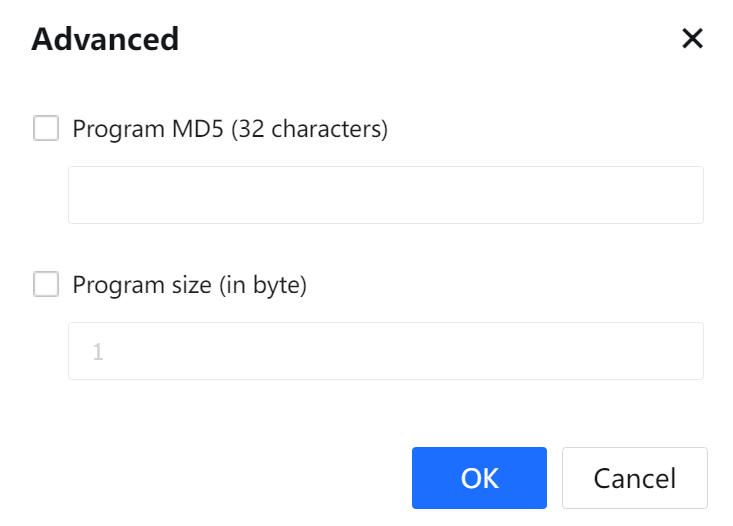
Status can be set to Running or Not Running. If Running is selected, you can set advanced conditions, including the process's MD5 value and program size. See the following figure.
If Running is selected for Status, you can select Disable Web access, Stop the process, or Not operating (only submitting report) in Rule Operation.
If Not Running is selected for Status, you can select Disable Web access, Start the process, or Not operating (only submitting report) in Rule Operation.
3.11.1.1.10.3 Adding File Based Rules
You can set rules for detecting files on clients.
Go to the Ingress Rules page, click Add, and select File. The File page is displayed.
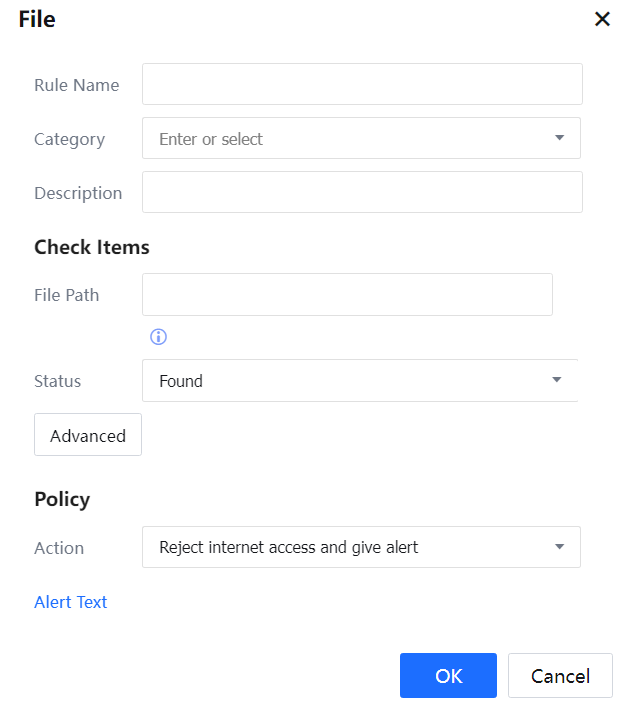
Rule Name: specifies the name of the rule to be added.
Category: specifies the type of the rule. You can select an embedded rule type or define one.
Description: specifies the description of the rule.
Status: specifies the status of files to which the rule is applied. If File Exists is selected, you can select Reject request and give alert, Delete file, Give alert, or Log Event only from Action.
If File does not exist is selected, you can select Reject request and give alert, Give alert or Log Event only from Action.
File Path: specifies the storage path of files. System environment variables are supported. See the following figure.
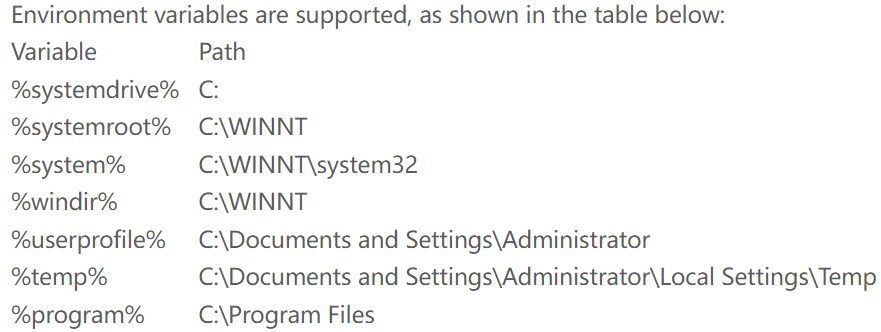
If Exist is selected, you can set advanced conditions. See the following figure.
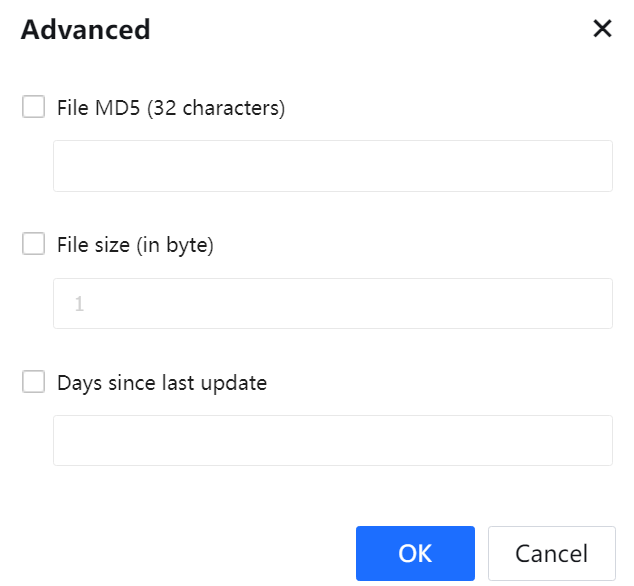
You can set the MD5 value, file size, and the number of days after which files are updated. Click OK.
If File exists is selected for Status, you can select Disable Web access, Delete file or Not operating (only submitting report) in Rule Operation.
If File does not exist is selected for Status, you can select Disable Web access or Not operating (only submitting report) in Rule Operation.
3.11.1.1.10.4 Adding Registry Rules
You can set rules for detecting registries on clients.
Go to the Ingress Rules page, click Add, and select Registry. The Registry page is displayed.[A227]
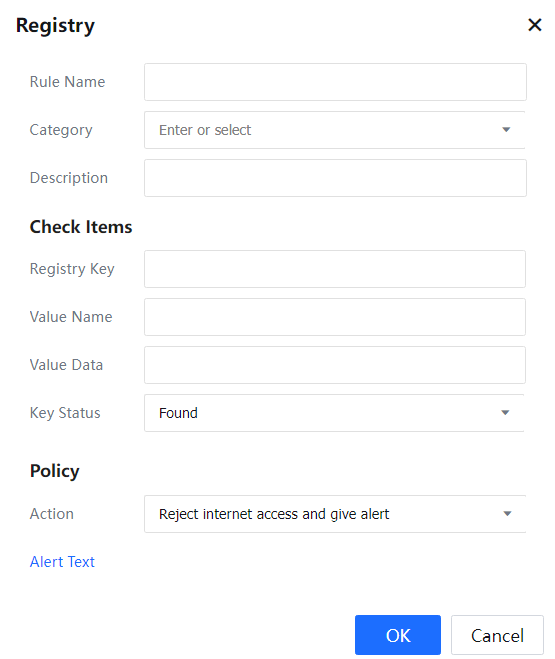
Rule Name: Specifies the name of the registry rule to be added.
Category: Specifies the type of the rule. You can select an embedded rule type or define one.
Description: Specifies the description of the rule.
Status: Specifies whether an entry is available in the registry. If a Specified item exists in the registry is selected, you can select Reject request and give an alert, Delete the entry, Give alert, or Log Event only from Action.
If Specified item does not exist in the registry is selected, you can select Reject request and give alert, Give alert or Log Event only from Action.
Registry Item: Specifies an entry, the path displayed on the left pane of the Required Registry Item window.
Key: Specifies the key of the entry.
Value: Specifies the value of the registry.
You can set the status to specify items in the registry or specify items not in the registry.
3.11.1.1.10.5 Adding Task Based Rules
You can set scheduled tasks. The Ingress client invokes custom executable programs, JavaScript, and VBScript. You can set return values in these executable files. The Ingress client takes actions based on the return values.
Go to the Ingress Rules page, click Add, and select Task. The Task page is displayed.
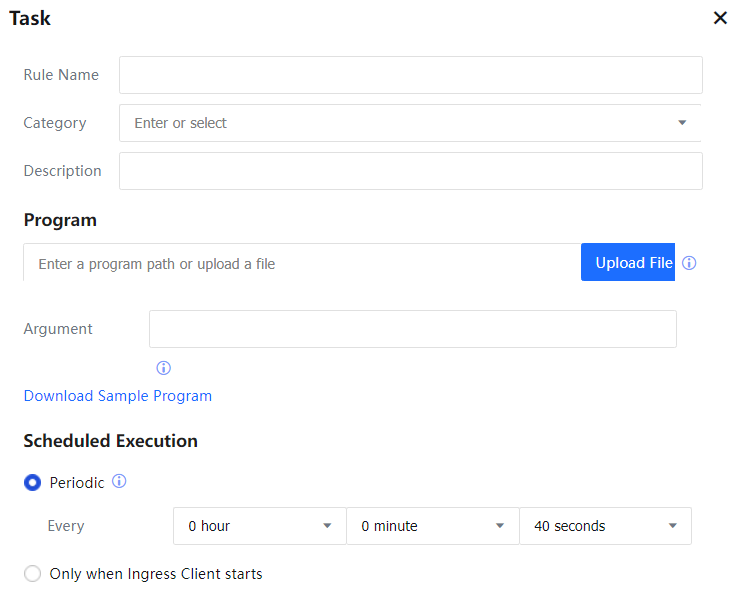
Category: Set the type to which the rule belongs.
Rule Name and Description: Set the name and description information of the rule.
Execute program:
Program Type includes Executable Program, Jscript, and Vbscript.
Program Path: Used to enter the detailed path of the program script stored on the server. The path must be a network address where all users applying to this rule can execute permissions.
Scheduled Execution includes Start running periodically and run only once when the ingress program starts on the computer.
Execution Permission includes Execute as the current user and Execute as SYSTEM User. Execute as the current user refers to the permission of the PC account logged in by the current user, and Execute as SYSTEM User refers to the account with the highest level of system permission. With Execute as SYSTEM user, the low-level account has no execution permission that can be prevented.
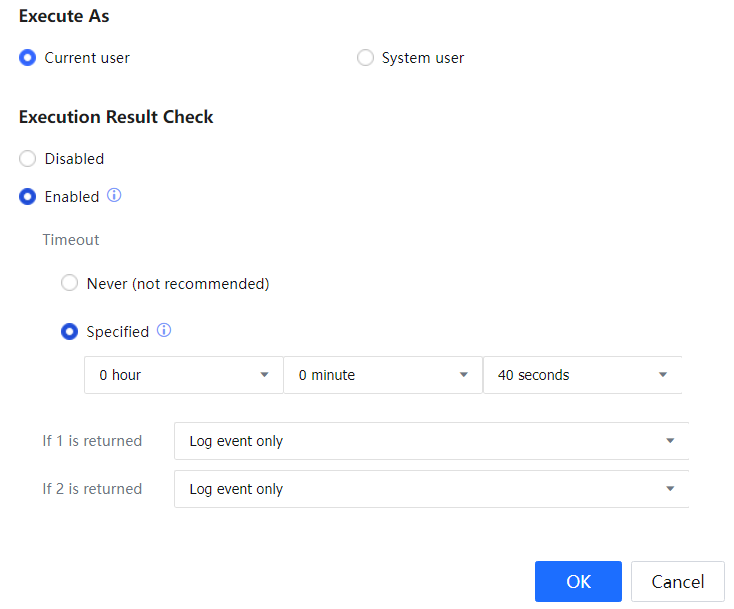
Execution Result Check includes Check returned results and Disabled, and is used to set whether the execution results of the task script need to be checked. Operation timeout is to set the timeout duration. If 1 is returned and If 2 is returned, process the different return results obtained after the task script check. Actions can be selected as Log event only, give alert, and Reject request and give alert.

When the program path is configured, the program execution will fail if the server is configured with the account and password for login again, and the client does not save the account and password. You have to access the server via the client and save the account and password. If the server does not set the account and password, the planned task can be successfully executed.
3.11.1.1.10.6 Adding Service Pack
Service Pack checks whether the endpoint updates the vulnerability patch in time as required by the organization.
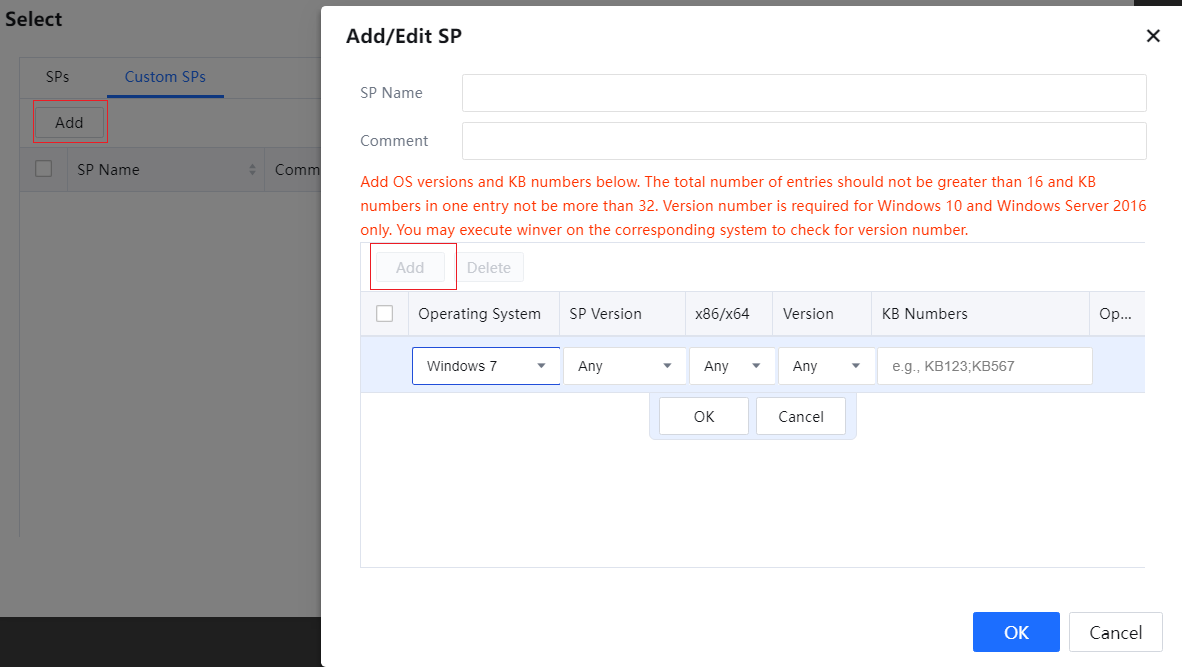
On the Ingress Rule edit page, click Add, and select Service Pack to add a service pack-based rule.[A228]
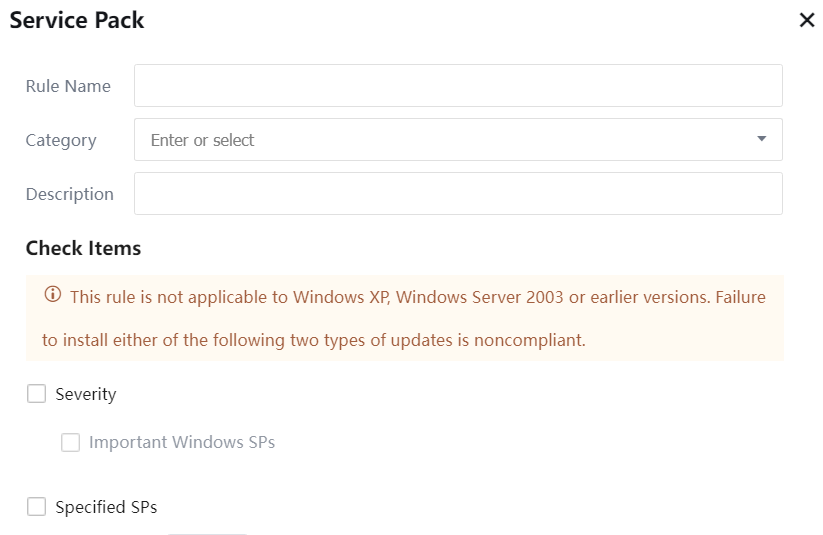
Category: Set the category to which the rule belongs.
Rule Name and Description: Set the name and description information of the rule.
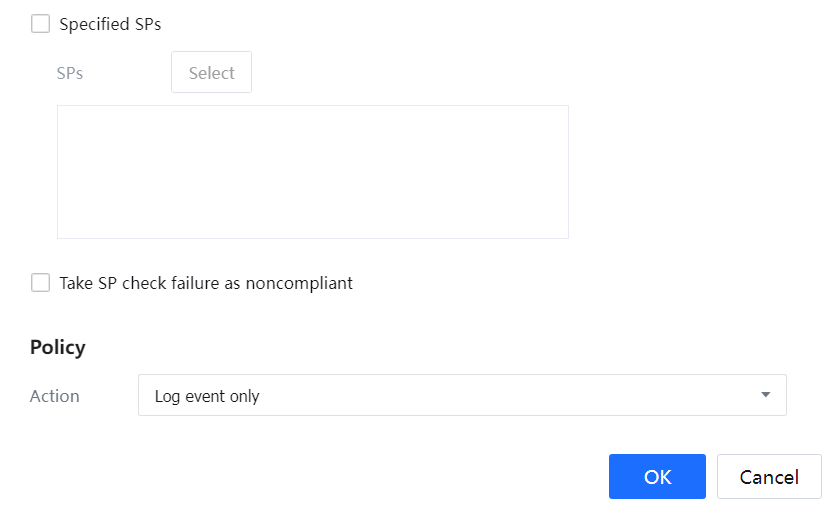
Patch Check: You check by Severity or Specified patches.
For Severity, you can check Critical Windows Updates. Severity customizes the patches in patch checking. For patch names and details, please refer to the patch contents.
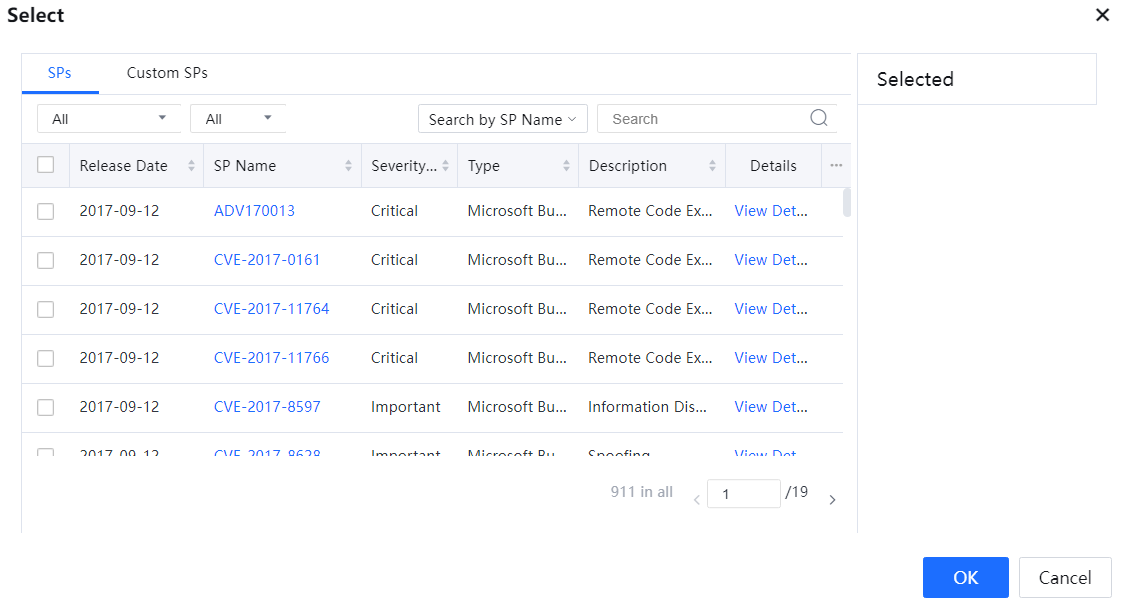
Patches include some commonly used patches. If you need to customize patches, you can edit Custom Patches.
Check Failure in obtaining PC patch information shall be processed as violation. If the detection fails, it shall also be processed as a violation.
Action: Select the actions of the device on users who do not conform to the rules, such as Give Alert or Log event only (Log event only means that no action is taken on client data, and logs will be recorded in the console and the data center at this time).
3.11.1.1.10.7 Adding Windows Account Rules
Go to the Ingress Rules page, click Add, and select Windows Account. The Windows Account page is displayed.
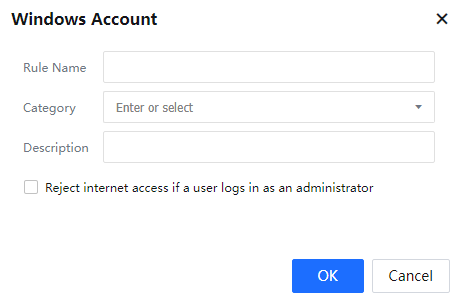
If Reject user who logs in as Administrator is selected, you can prevent clients from accessing the Internet as the super administrator.
Deleting Ingress Rules
On the Ingress Rules page, select a custom Ingress rule and click Delete. The displayed message asking for your confirmation, click Yes.
Modifying Ingress Rules
On the Ingress Rules page, select a custom Ingress rule and click its name. Then, in the dialog box for editing the Ingress rule, modify the settings as required except the rule name.
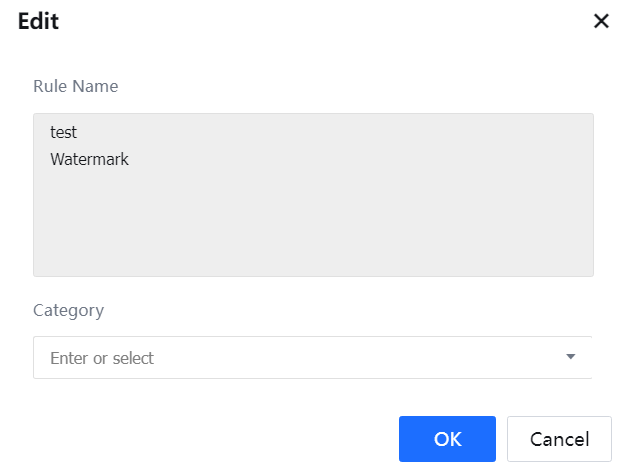
Editing Ingress Rules in Batches
On the Ingress Rules page, select multiple custom Ingress rules and click Edit. You can edit only the rule type in batches.
Importing and Exporting Ingress Rules
On the Ingress Rules page, select custom Ingress rules and click Export. Embedded Ingress rules cannot be exported. Click Import and select an Ingress rule file to import and Ingress rule.

The imported rule file must be in ZIP format and must contain IngressRuleExport.conf, and the IngressRuleExport.conf file must be at the outermost layer.
Combined Ingress Rule
You can combine Ingress rules in AND or OR relationships.
Adding Combined Ingress Rule
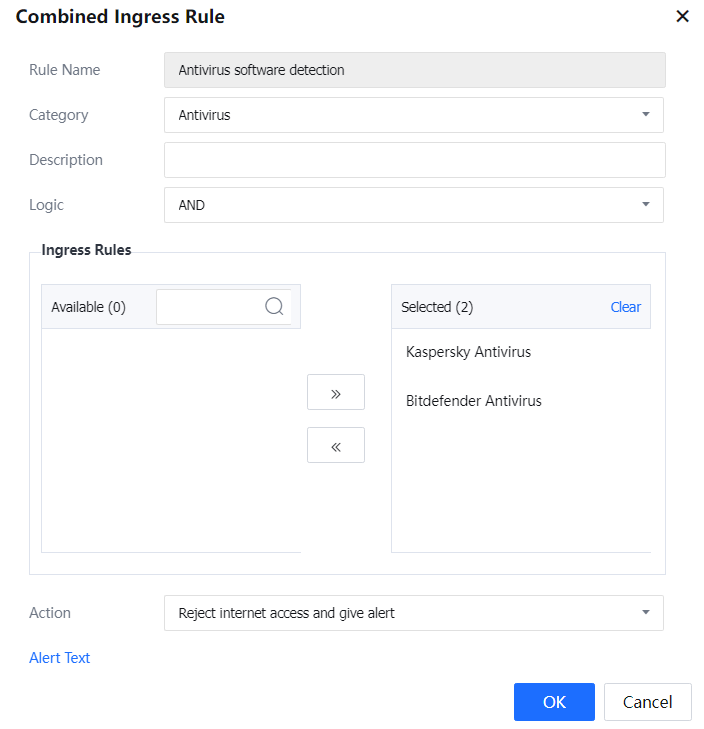
Navigate to Access Mgt > Endpoint Check > Check Rules > Ingress Client Based > Combined Ingress Rule. On the Combined Ingress Rule page, click Add. The page shown in the following figure is displayed. [A229]
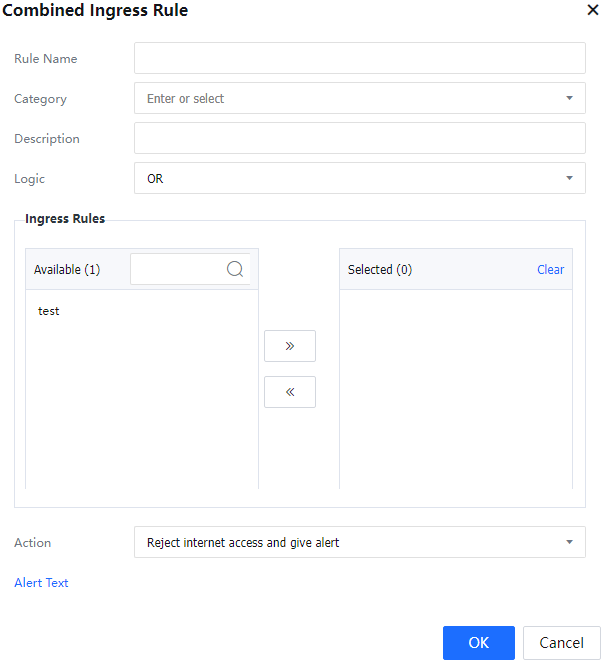
Rule Name: Specifies the name of the Combined Ingress Rule to be added.
Category: Specifies the type of the Combined Ingress Rule.
Action: Specifies the action to be performed if the rule is not met. It can be set to Reject or Report only.
Logic: Specifies the condition for the Combined Ingress Rule to take effect. A Combined Ingress Rule can be set to take effect when any member rule is effective or when all member rules are effective. When the specified member rule is met, the specified action will be performed.
Ingress Rules: Select a custom rule and click Add to move it to the right pane.
Example: The administrator requires intranet users to install Kaspersky or Rising. If an intranet user does not install either antivirus software, the user cannot access the Internet.
- Set two Ingress rules for detecting Kaspersky and Rising. The device detects the processes of the antivirus software.

The actual antivirus software processes prevail. The process names provided in this example are for reference only.
- Set a Combined Ingress Rule to combine the preceding two rules. According to the customer requirements, Internet access is allowed if either antivirus software is installed. Therefore, set Logic to Rules are with AND logic. The Combined Ingress Rule takes effect when neither antivirus software process is running. Set the action to Reject.
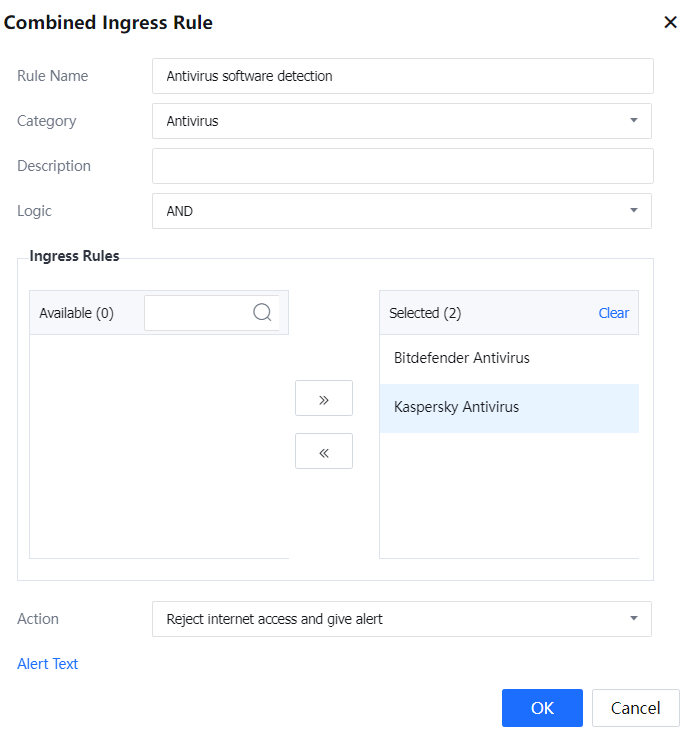
- Associate the composite Ingress rule with an Internet Access Policy and associate the policy with users/user groups.
Deleting and Modifying Combined Ingress Rules
On the Combined Ingress Rule List page, select a Combined Ingress Rule and click Delete. Alternatively, click the name of a Combined Ingress Rule and modify the settings as required except the rule name. See the following figure.