There are two types of application characteristics identification libraries.
The first type of application identification rule aims to detect the application type of packets based on multiple conditions, including the characteristic value or protocol, port, direction, packet length, and packet content. This type of rule can effectively detect application types that cannot be identified by port or protocol, such as Facebook and P2P applications.
The first type of rules can be further divided into embedded rules and custom rules. Embedded rules cannot be modified and are updated by the device periodically. A license is required to authorize the update of embedded rules, and Internet access must be available. Custom rules can be added, deleted, and modified. SSL management, Internet access audit, endpoint reminders, and Bandwidth Management are controlled and audited based on application identification results. Therefore, the application library is very important. An embedded application identification library cannot be edited or deleted. Some applications can be disabled, but those involving basic protocol identification cannot be disabled.
The second type of application refers to URL groups defined on the page displayed after choosing Objects > Application Signature Database. URL groups are a sub-class of the Visit Web Site. This type is used to recognize websites visited by intranet users based on HTTP data. URL groups are classified into embedded URL groups and custom URL groups. URL groups cannot be edited or added to the Application Signature. Instead, they are reused here. To edit a URL group, choose Objects > Application Signature Database.
Application identification rules can be referenced on the page displayed after you choose Online Activities > Access Control [A214][LCH215]to control the application types and visited website types.
View the Application Signature
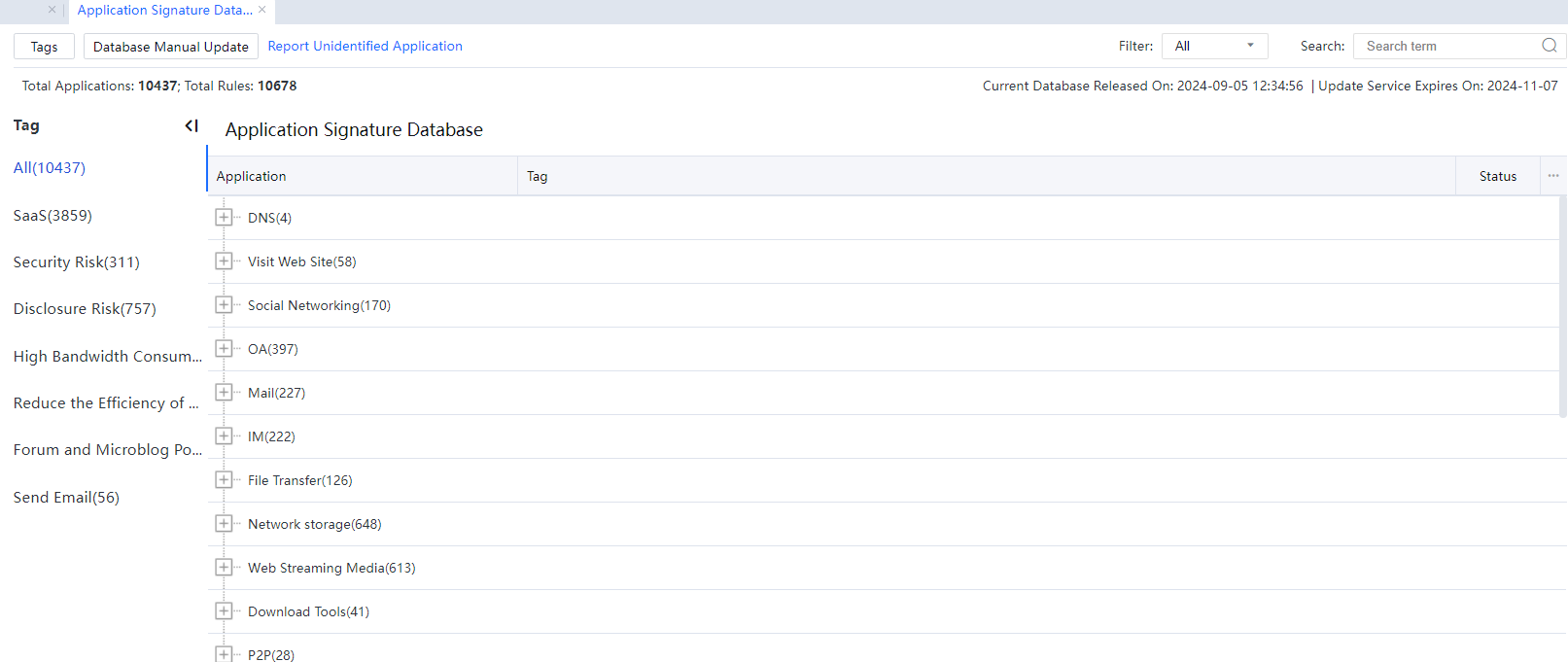
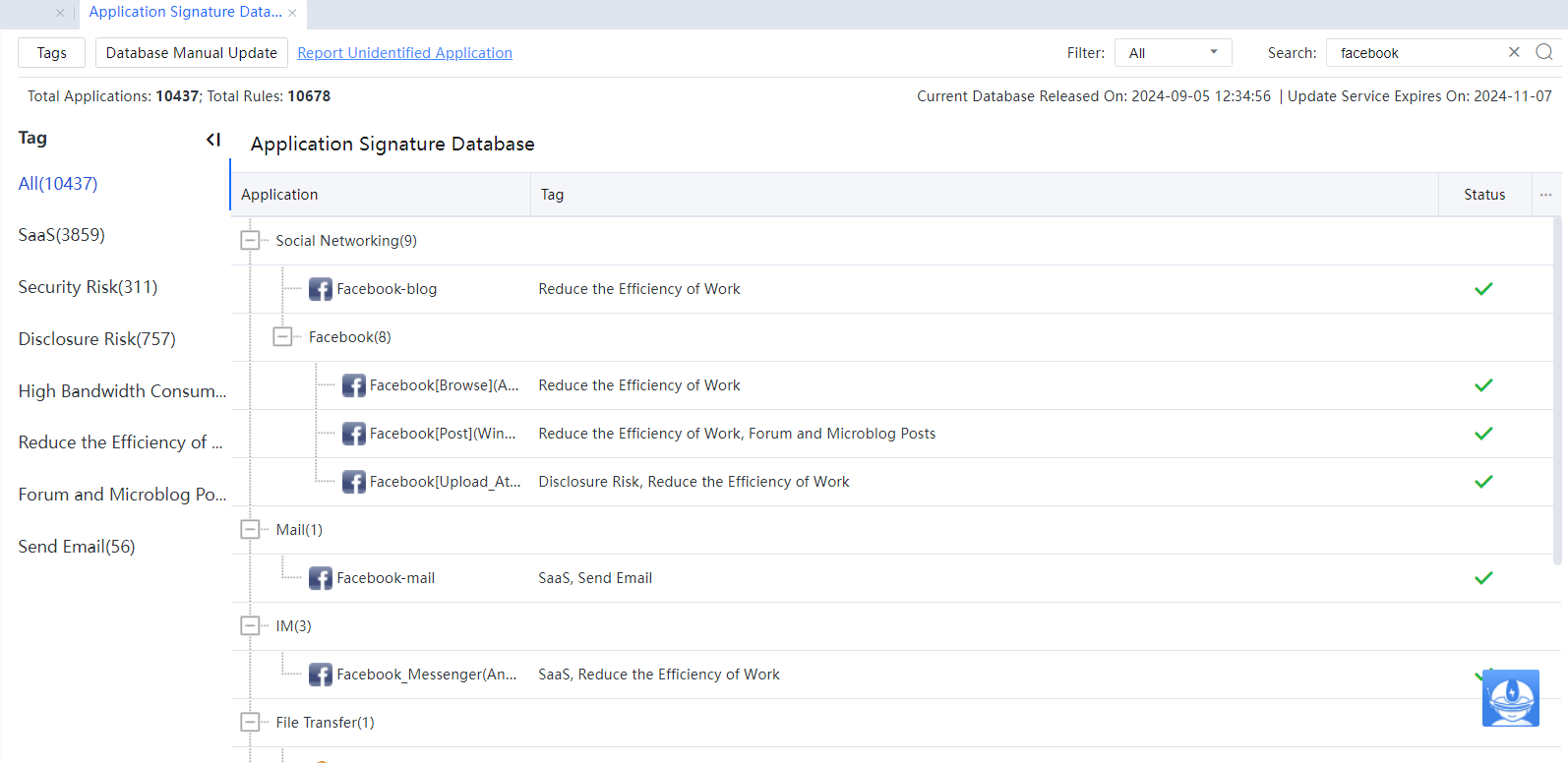
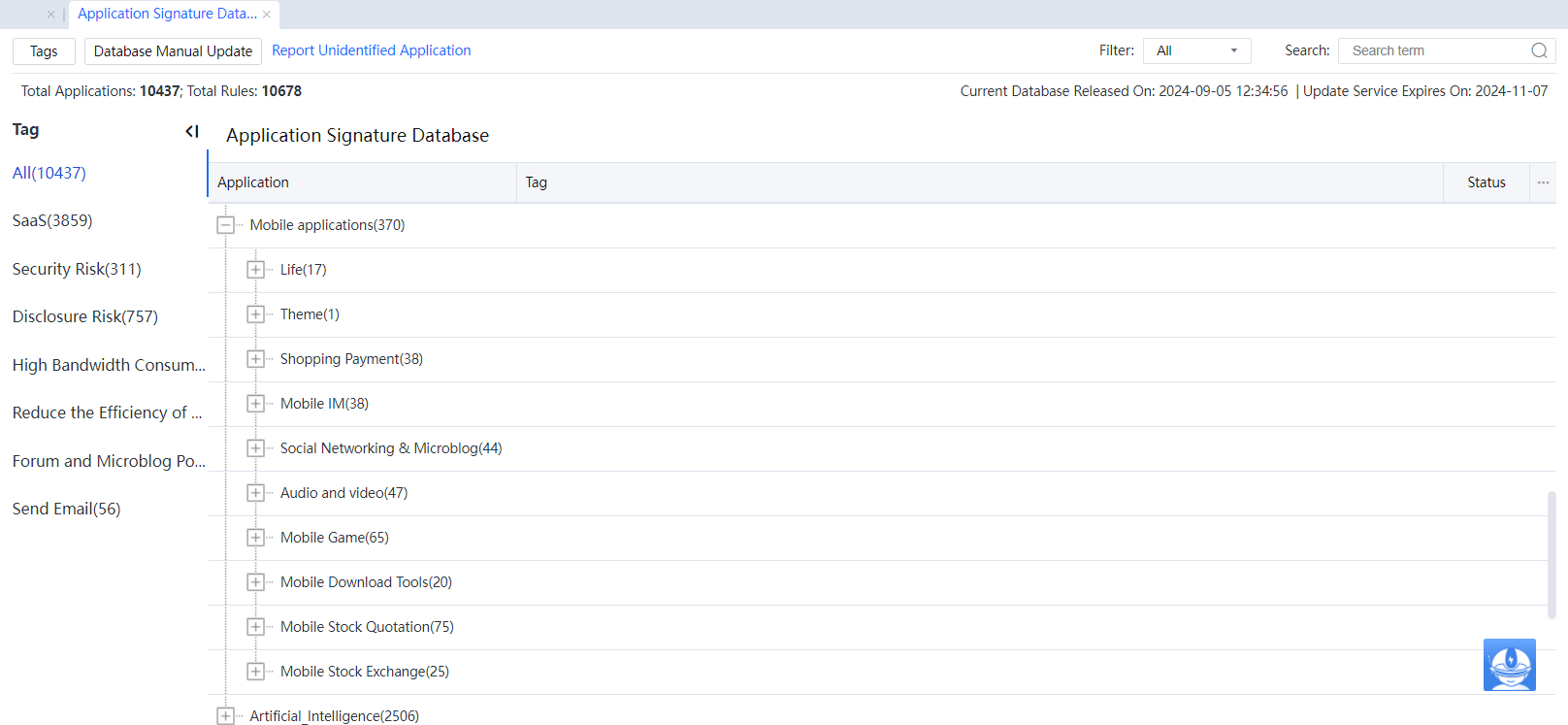
Navigate to Objects > Application Signature Database. The Application Signature Database pane is on the right.
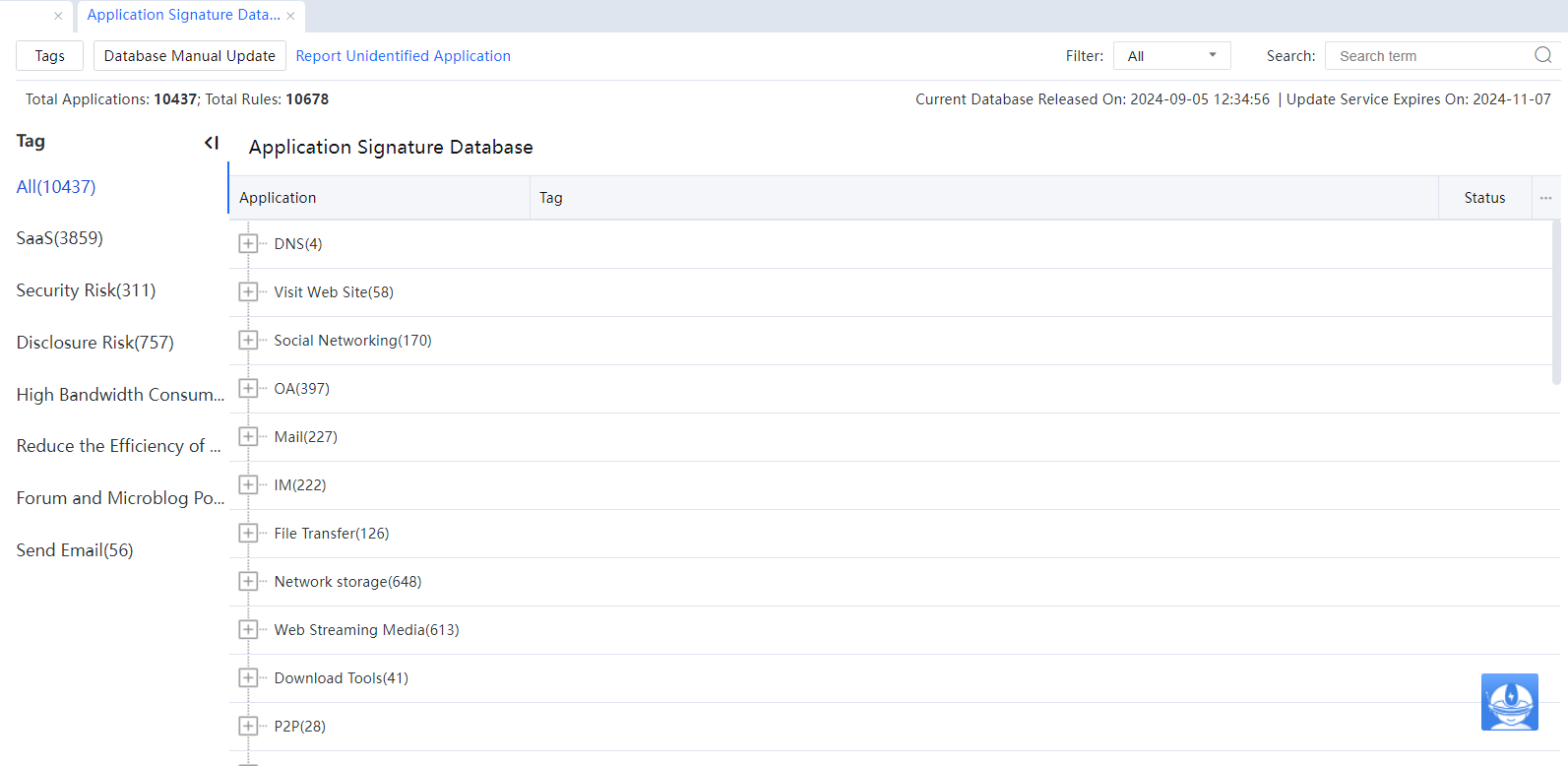
The value behind Total Applications indicates the total number of embedded application rules and URL groups on the device.
Current Database Released indicates the date of the embedded application identification library. Update Service Expires On indicates the upgrade validity period of the embedded application identification library.
Application classification labels are displayed in the Tags column. The application name is a type of additional classification information about applications. An application can belong to only one application class but can have multiple labels. For example, Xunlei Download belongs to the Download Tools class and has two labels: High Bandwidth Consumption and Reduce the Work Efficiency. Labels may be referenced in defining Internet access policies, which facilitates Access Control.
Click All, and all application types will be displayed on the Application Signature pane on the right. The device has six embedded labels: Security risks, Send Email, High Bandwidth Consumption, Reduce the Efficiency of Work, Forum and Microblog Posts, and Disclosure Risk. These embedded labels will be updated accordingly as the application identification library is updated. Applications with embedded labels cannot be deleted or added. To define labels, click Tags. All labels can be referenced on the page displayed after choosing Online Activities > Access Control.[A216][LCH217]
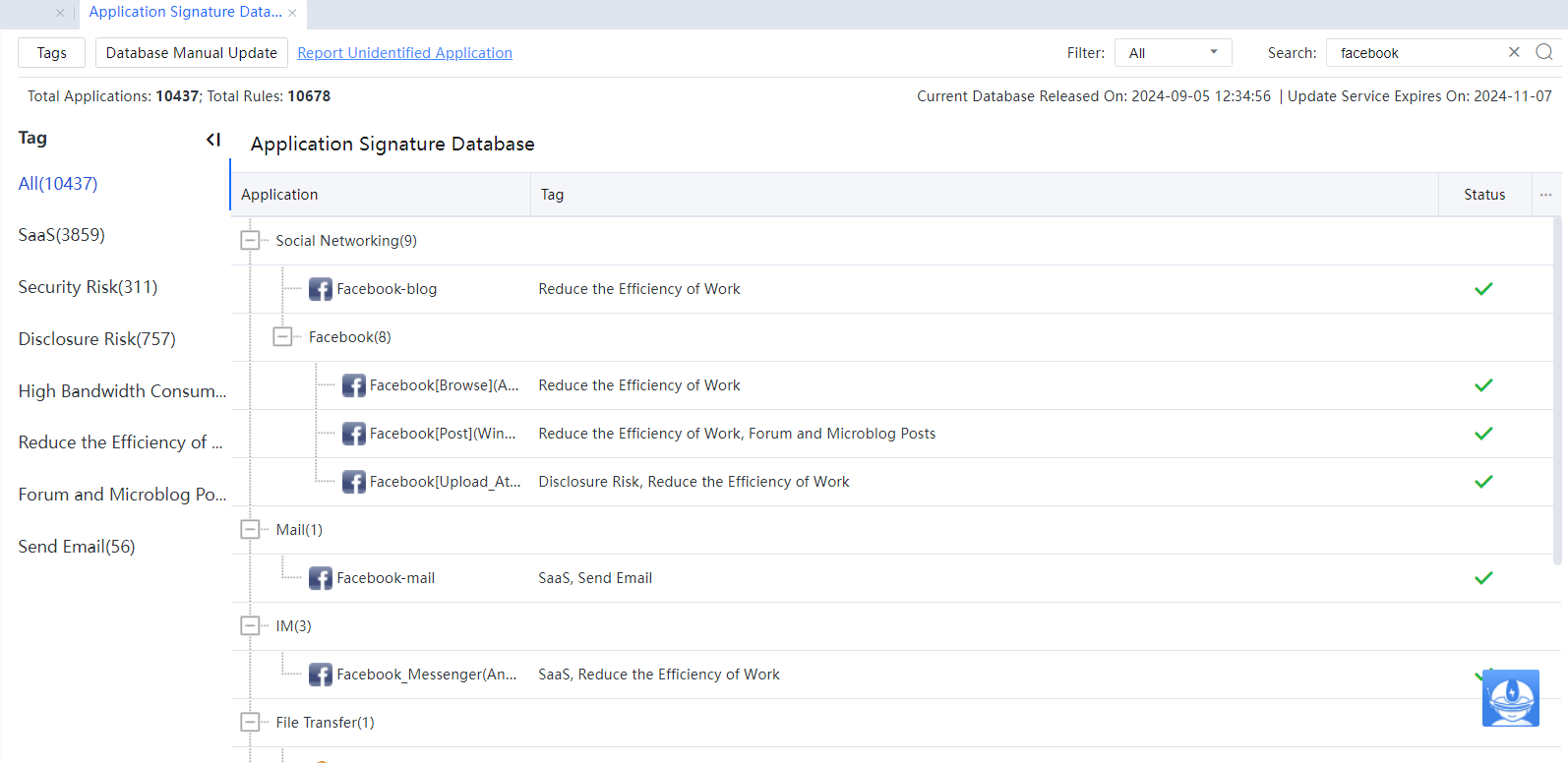
In Filter, select a rule type. Select All to filter all rules meeting the search condition, Enabled to filter enabled rules meeting the search condition, and Disabled to filter disabled rules meeting the search condition. Input a keyword in Search, for example, Facebook, and press Enter, as shown in the following figure.

Click Database Manual Update to manually import application identification rule files to the device.
The procedure for adding a label and associating it with applications is as follows:
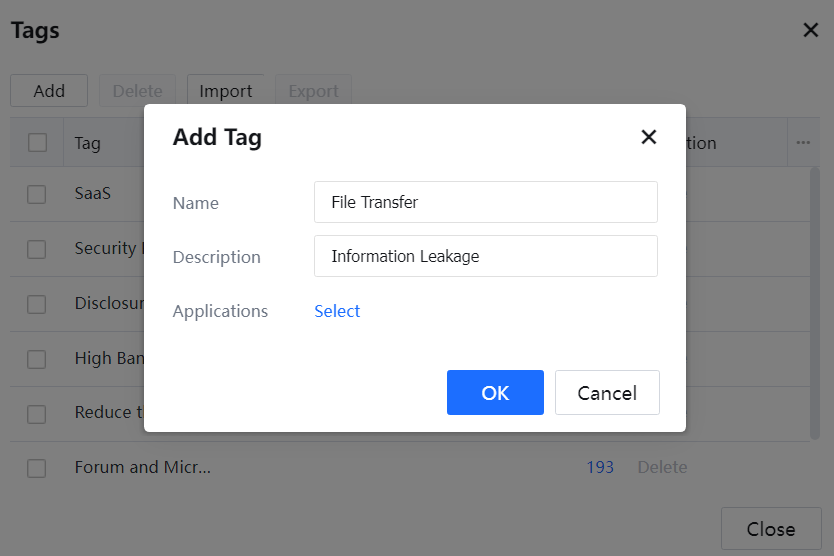
Click Tags, click Add, and enter the label name.
In the position for associating applications, click Select and select applications as required.
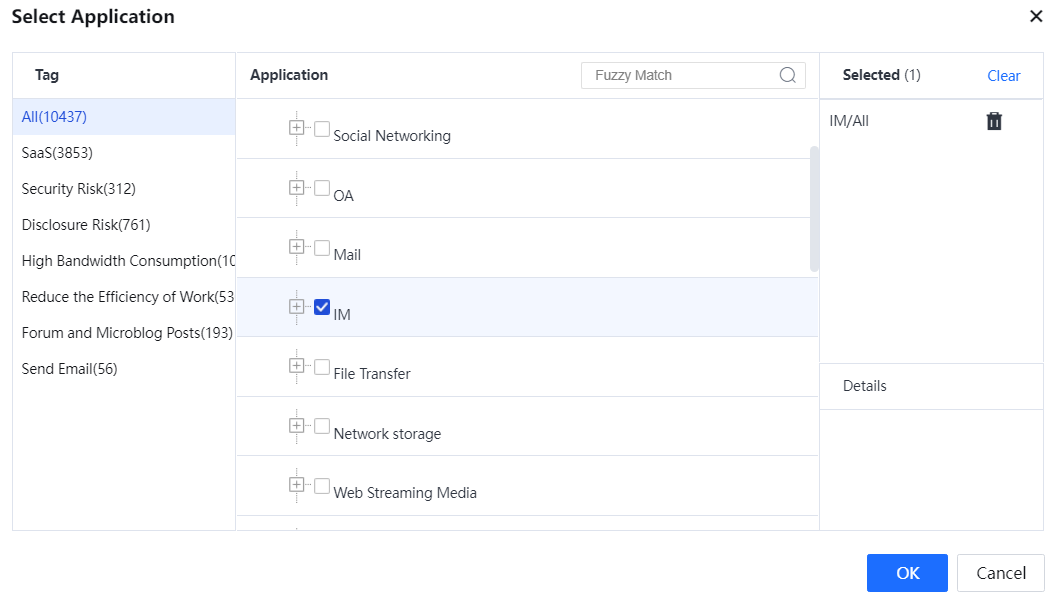
Click OK. A label is added and associated with applications successfully.
Enabling/Disabling Application Identification Rules
Navigate to Objects > Application Signature Database. The Application Signature Database pane is on the right. Next, select an application. For example, to disable the application rule of transferring files through Facebook, filter out the applications for transferring files through Facebook, as shown in the following figure.
On the Status column, click  of an application to disable a type of application rule. Click
of an application to disable a type of application rule. Click  of an application to enable a type of application rule.
of an application to enable a type of application rule.

1. The application identification rules of some basic protocols cannot be disabled, such as HTTP. If a basic protocol is disabled, the data identification based on this protocol will be affected. Therefore, it is not allowed to disable such rules on the device.
2. In the Application Signature, the Mobile Applications maps application software runs on mobile endpoints such as smartphones and tablets.
3. Some URL groups are not included in the application type Visit web site. Instead, they belong to the corresponding application type as web applications. For example, microblog URLs are included in the application type Microblog. Suppose control of microblog applications is enabled in Internet access policies. In that case, the device can control the behaviors of accessing microblog applications by using a web browser and the behaviors of accessing microblog clients.
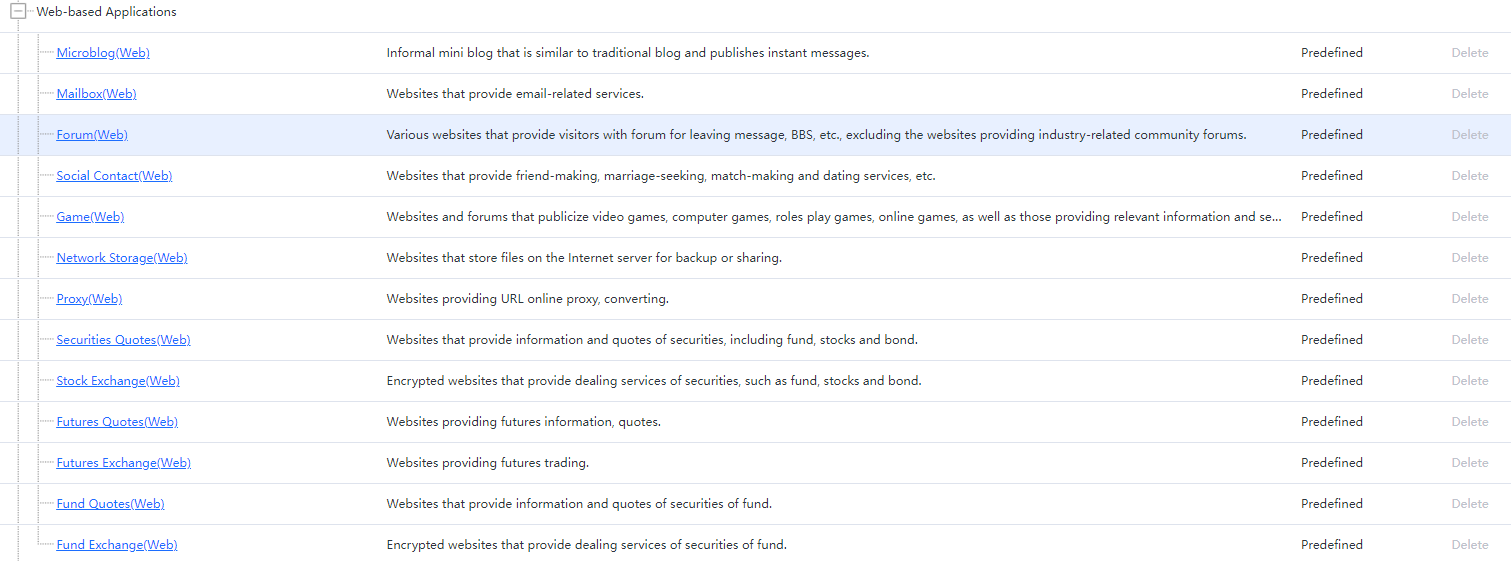
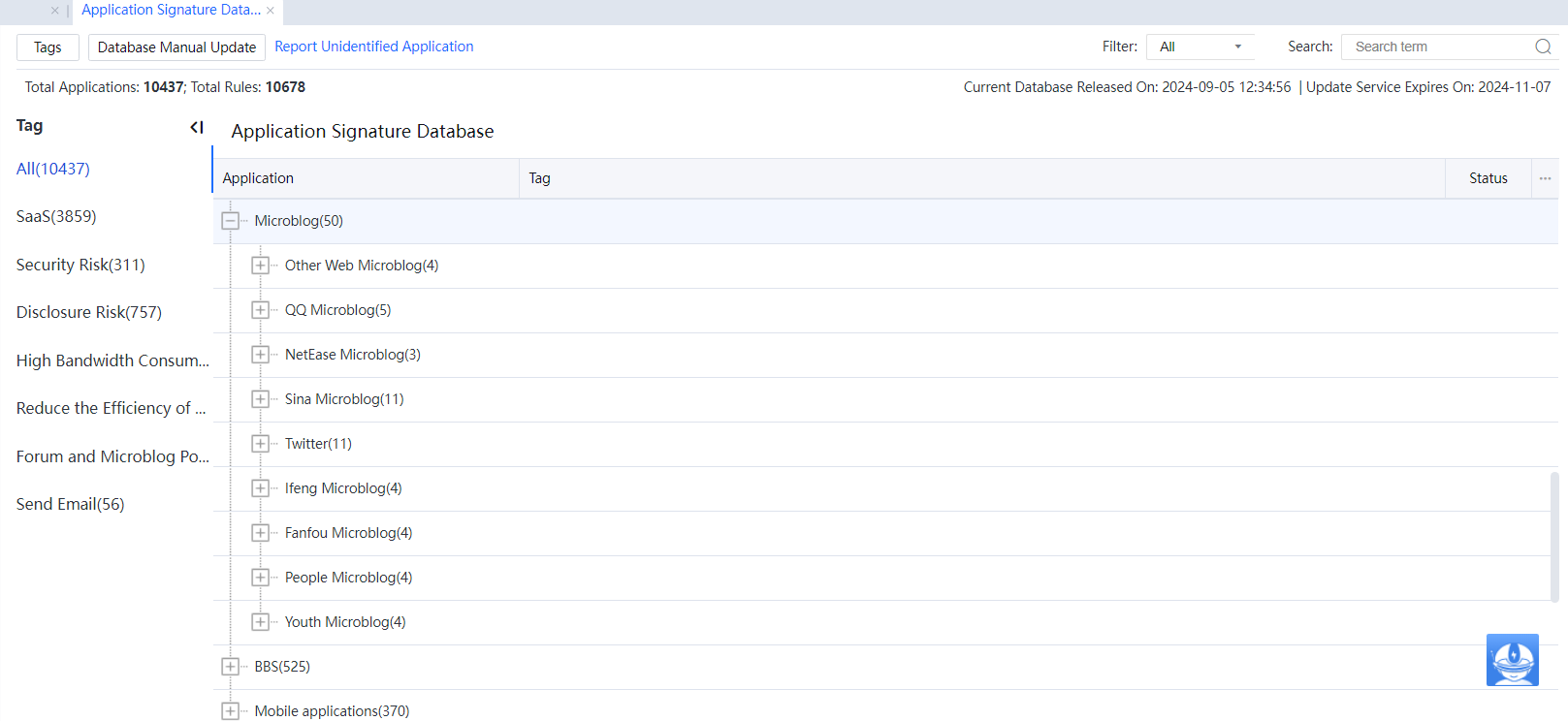
The following figure shows the web-based applications.




