The configuration page of the Internet security module.
All Endpoint Security
Three parts are included: Malware Detection, End Secure (SANGFOR ENDPOINT SECURE), and Patch Check.
3.10.2.2.1.1 Malware Detection
Sangfor Malware Detection uses the combination of botnet behavior analysis and feature recognition to identify and block Malware suspected of having Trojan in the LAN security domain. It has built-in cloud security detection technology and reports the unknown virtual risk to the cloud virtual sandbox to Execute and release the analysis result report, effectively preventing the host from accessing the illegal malicious URL.
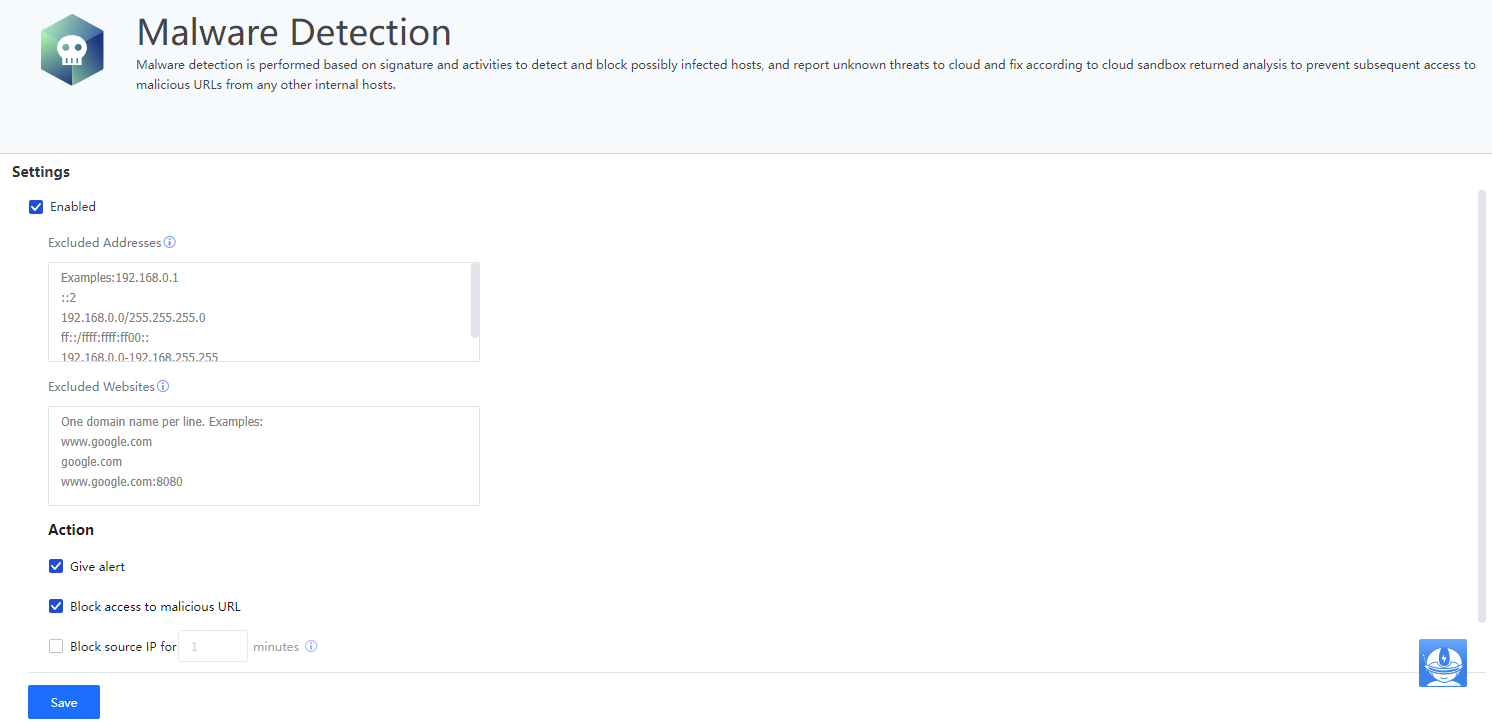
Select Enabled.
Excluded Addresses: IP addresses that do not need to be detected and can be added to the whitelist.
Excluded Websites: Websites that do not need to be detected and can be added to the whitelist.
Action: You can choose to Give Alert (combination with the System > General > Alert Option and Block access to malicious URLs or Block source IP.[A184]
3.10.2.2.1.2 Endpoint Secure
As an endpoint detection and response platform and a lightweight endpoint + management platform solution, Sangfor Endpoint Secure utilizes the capability of constant detection of endpoint threats and the response option of isolating threat events with one click. The Sangfor Endpoint Secure, with correlated response in combination with NGAF, IAG, and Cyber Command products, constitutes the new generation of the secure protection system.
This function applies to scenarios already using Endpoint Secure products.
In the endpoint deployment of Endpoint Secure, Correlation to Sangfor IAG is added. See the picture below: 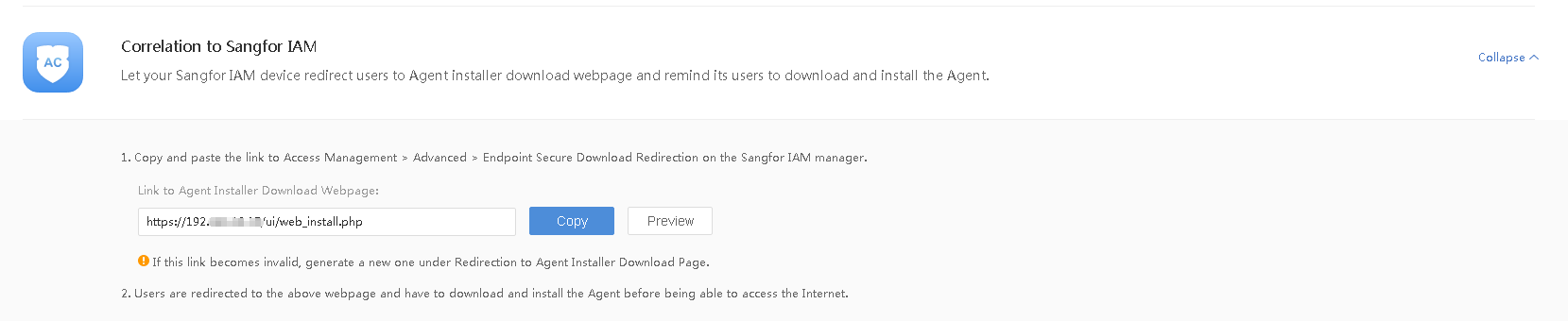
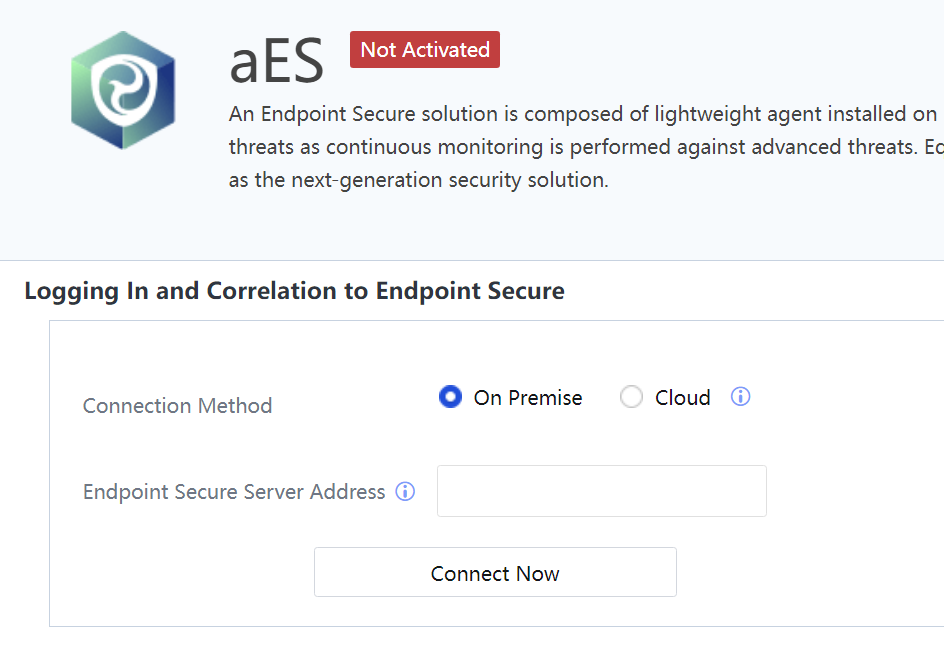
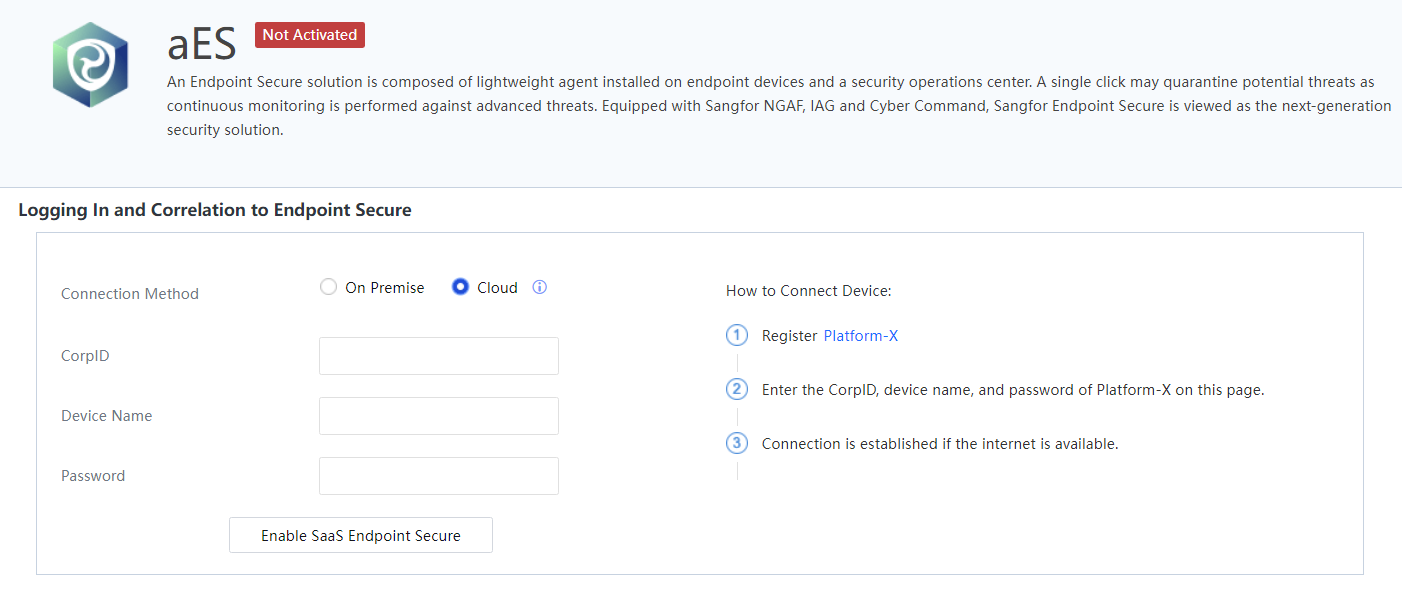
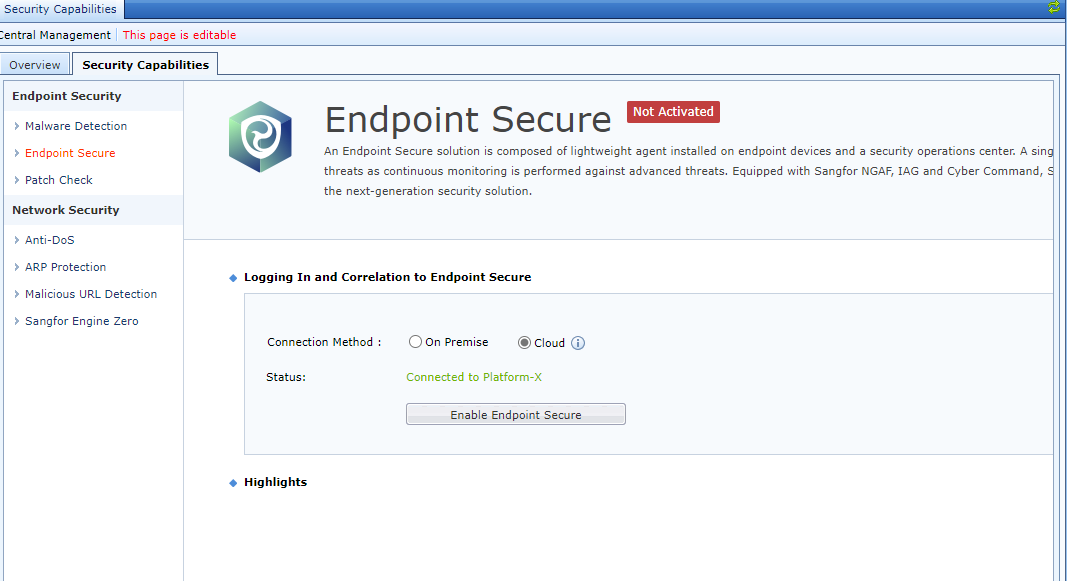
On the Endpoint Secure page, enter the IP address of the Endpoint Secure platform to connect to the platform. The Connection Method is On Premise or Cloud.
After the connection is complete. The page displays Endpoint Secure's service details, the number of connected endpoints, etc[LCH185]. 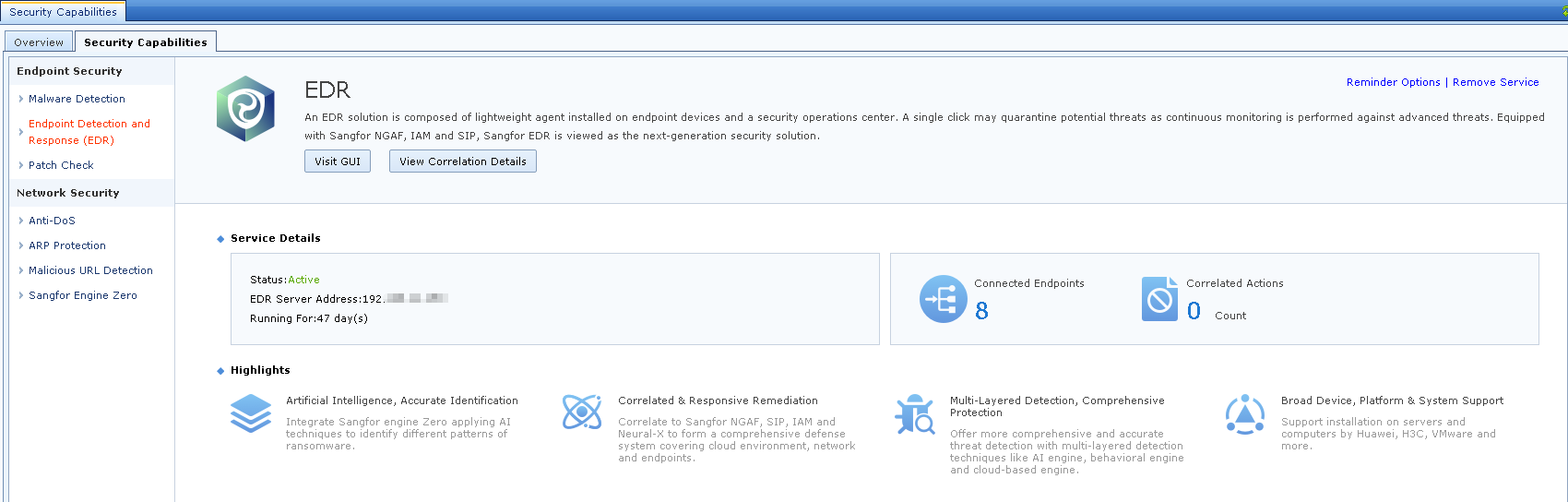 [A186]
[A186]
Endpoint Secure on the cloud:
 [A187]
[A187]
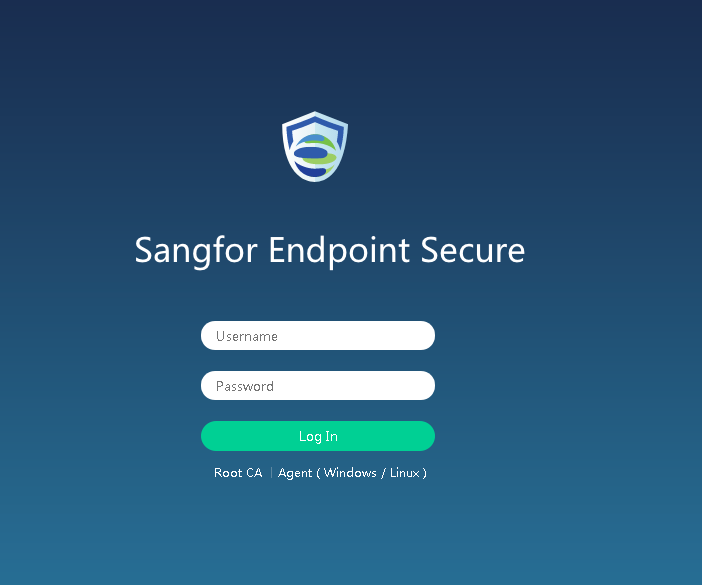
Click Visit GUI to go to the management platform of Endpoint Secure.
Click View Correlation Details to go to the details page of the correlated endpoint. 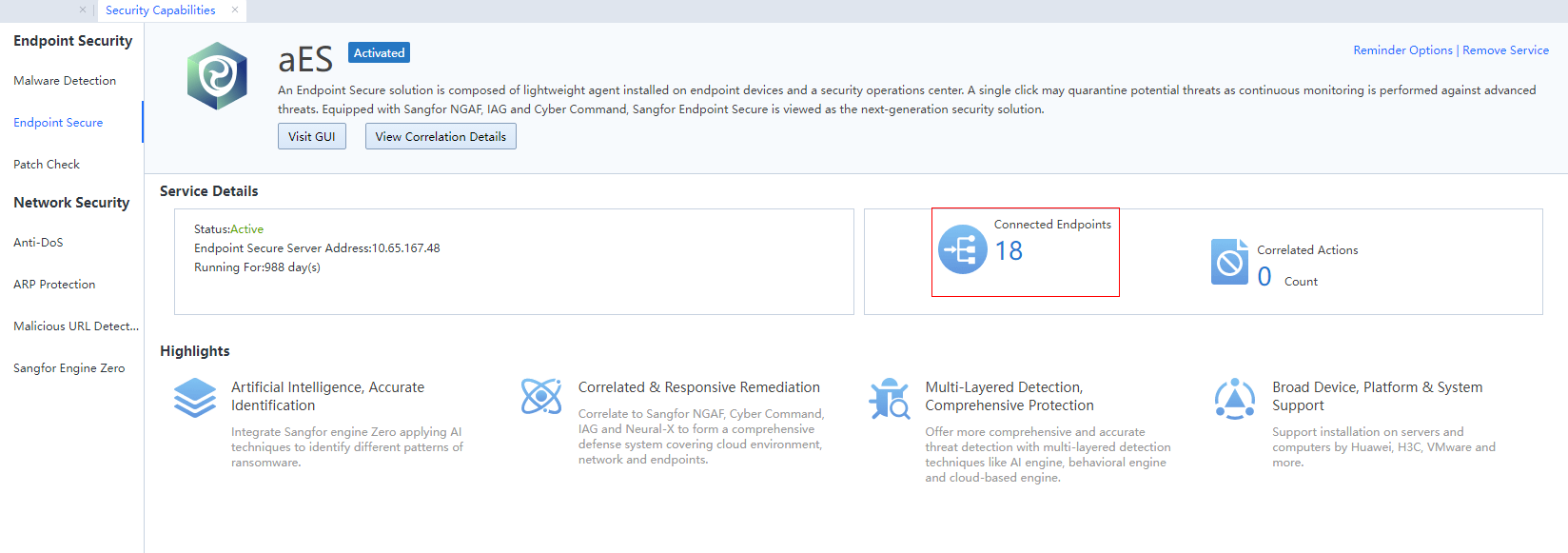

[A188]
Click Push Configuration to enable this function and configure Applicable Object of this policy. This realizes pushing the reminder web page of deploying Endpoint Secure client to endpoints within the applicable scope, helping the LAN promote the Endpoint Secure client.
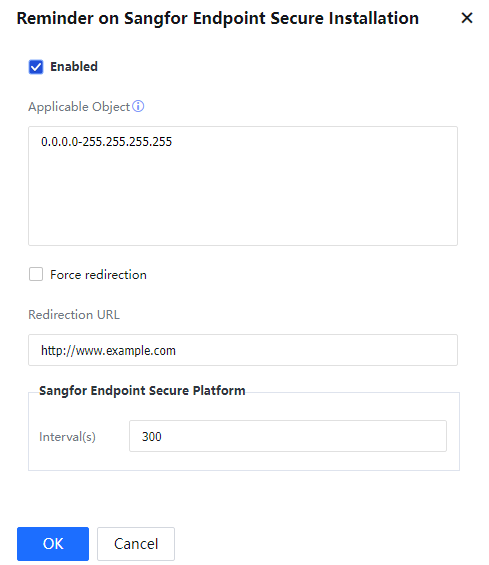
Enable Push Configuration: This function is disabled by default. Please enable it on demand.
Applicable Object: applicable to LAN IP addresses or IP segments.
Redirection URL: for generating, copying, and adding Endpoint Secure devices.
Connection configuration for Endpoint Secure SANGFOR ENDPOINT SECURE.
Interval(s): define the interval for pushing the web page to clients who do not have the agent installed. It is 300 s by default.
For endpoints within the applicable address scope that do not have the agent installed, the timed redirection page is as follows: 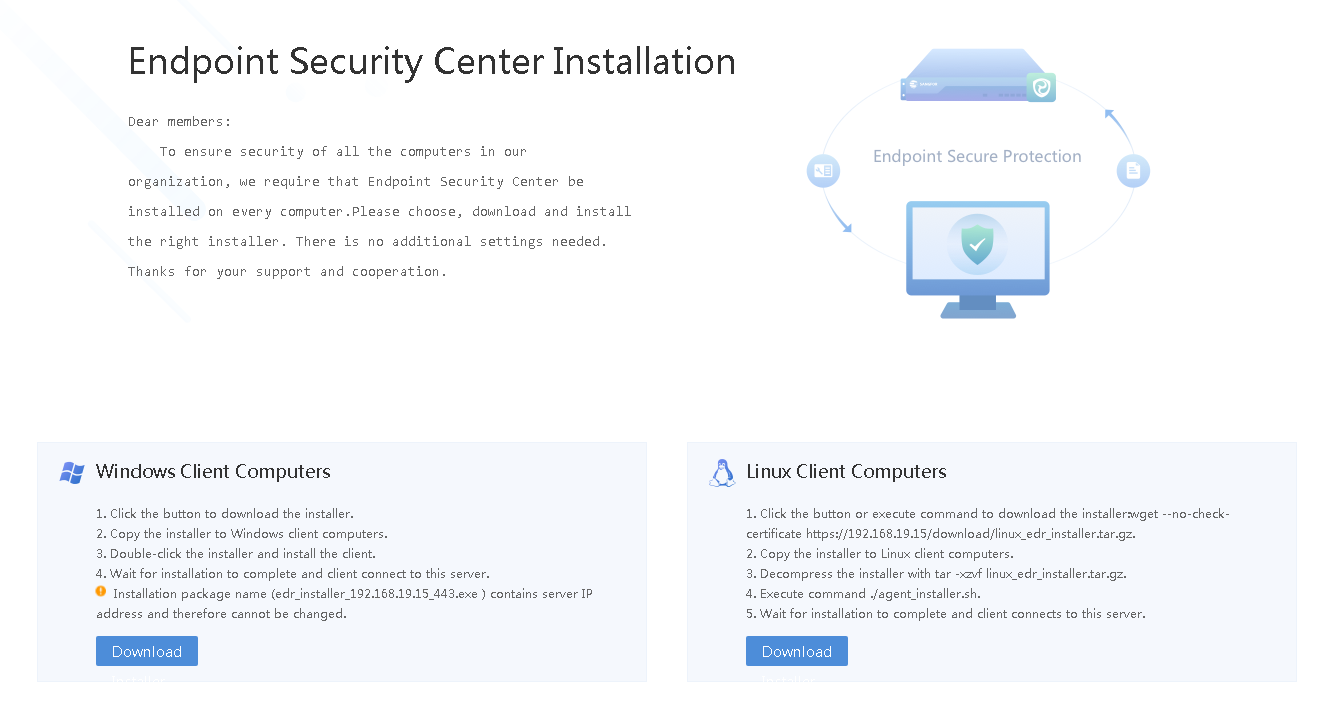
Upon receiving this redirection page, download the corresponding installation package for the operating system to the client and complete the installation.

Access to the HTTP web page is not supported. Only redirection of accessing the HTTP web page is supported.
Click Disconnect from SANGFOR ENDPOINT SECURE to disconnect the correlation between the device and Endpoint Secure. [A189][LCH190]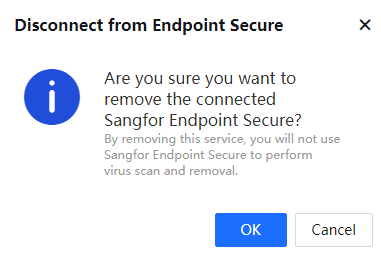
3.10.2.2.1.3 Patch Check
The Windows patch detection function can detect patches and patch update prompts not currently installed on the client computer on time, enabling users with insufficient security awareness to actively improve the operating system's security and help administrators reduce the work pressure from the LAN security.
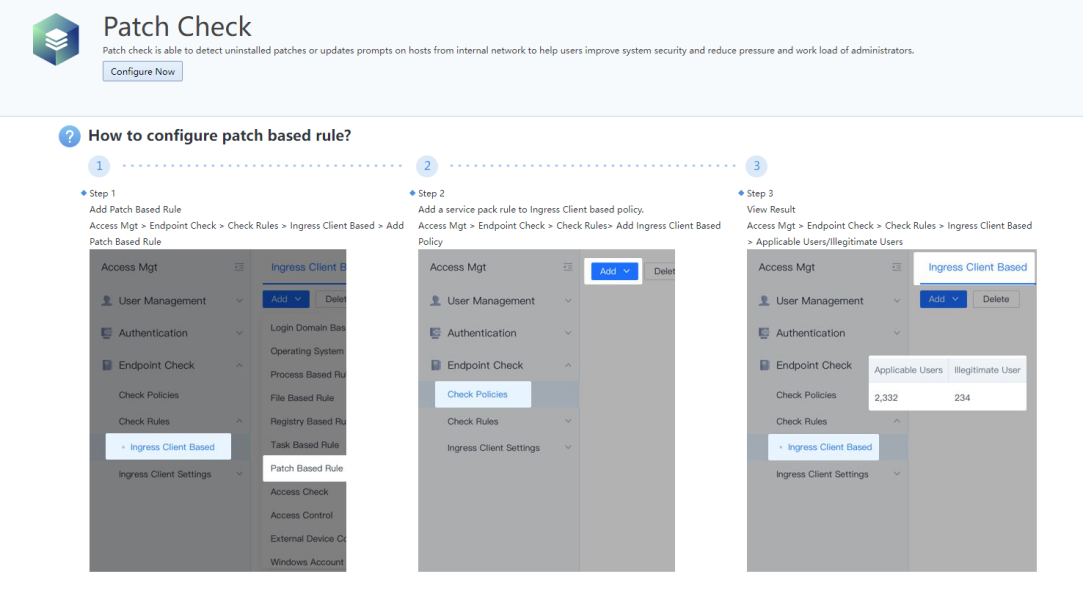
Click Configure Now to start configure. For more details, go to Access Mgt > Endpoint Check > Check Rules > Ingress Client Based > Ingress Client Based, click Add, and select Service Pack.[LCH191][192]
Network Security
3.10.2.2.2.1 Anti-DoS
A DOS attack (denial of service attack) aims to consume server-side resources and force the service to stop responding. The server responds to the blocking by forging the request data that exceeds the server's processing power so that the normal user request cannot be answered. The Anti-DoS function of the Sangfor device can prevent the DOS attack on the LAN from the external network and prevent the poisoning of the LAN or the DOS attack initiated by the attack tool.
The LAN DOS attack function of the IAG only focuses on the direction of the LAN port.
The configuration interface is as follows:
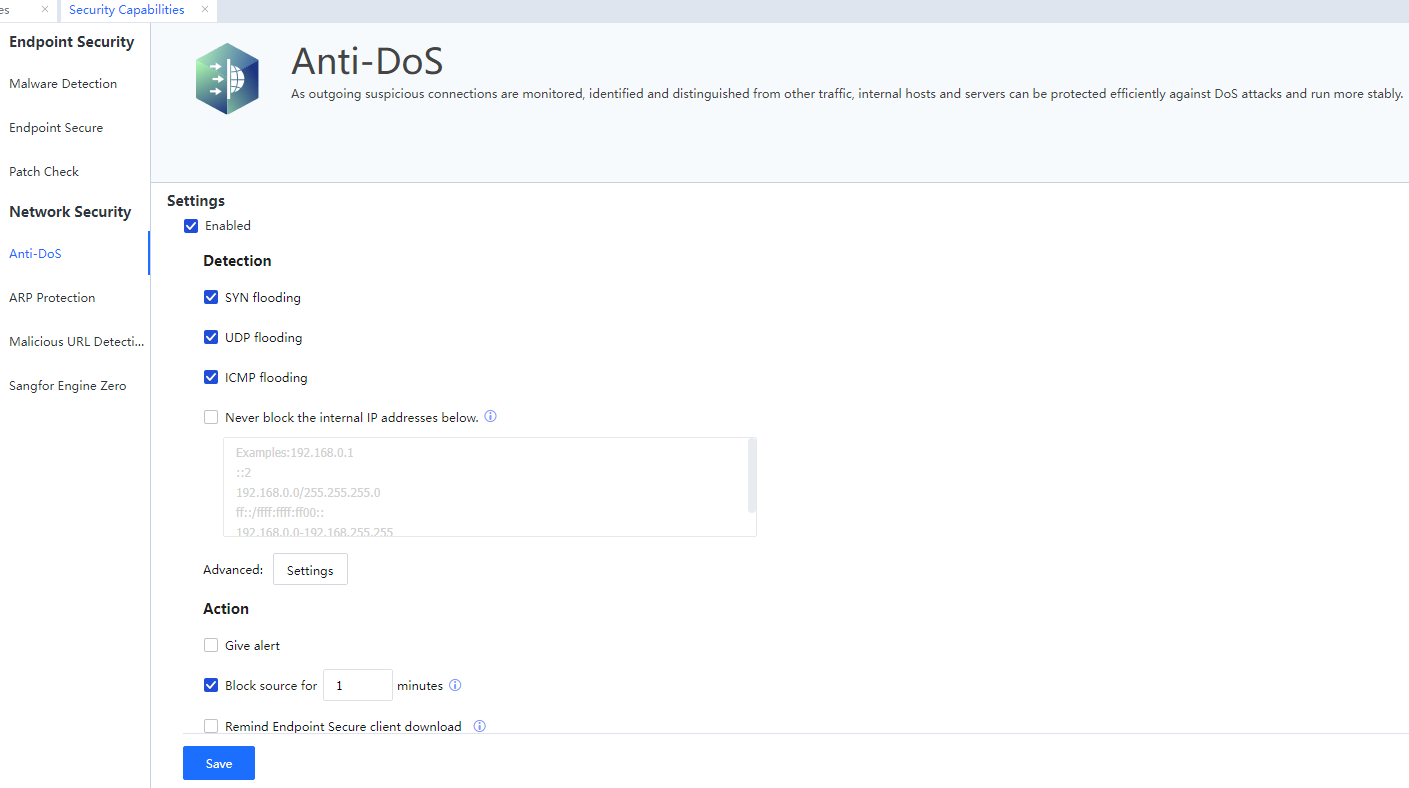
Enabled: Click to enable Anti-DoS. There are three detection methods: SYN flooding, UDP flooding, and ICMP flooding.
SYN flooding: TCP SYN flooding occurs in the fourth layer of OSI, using the characteristics of the TCP protocol, i.e., the three-way handshake. The attacker sends a TCP SYN, the first packet in the TCP three-way handshake. When the server returns an ACK, the attacker does not re-confirm it. Then, the TCP connection is in a suspended status called the semi-connected status. If the server does not receive the re-confirmation, it will repeatedly send an ACK to the attacker. It will cause further resource waste to the server. The attacker sends a large number of such TCP connections to the server. Since each packet cannot complete the three-way handshake, these TCP connections will consume CPU and memory due to the suspended status on the server, and the server may crash.
UDP flooding: The attacker sends a large number of UDP packets to the server, and the server sends a large number of replies.
ICMP flooding: The attacker sending the packet's source IP address is the attacker's IP address, and the destination IP address is the broadcast address of the network segment where the attacker is located so that a large number of ICMP echo replies are sent to the attacker.
Never block the internal IP below: Do not perform DOS defense on the IP address filled in the list. For example, the intranet has a server that provides services to the public network and provides more connections to the public network. In this case, excluding the server's address is recommended to avoid being considered illegal by the DOS defense.
Advanced
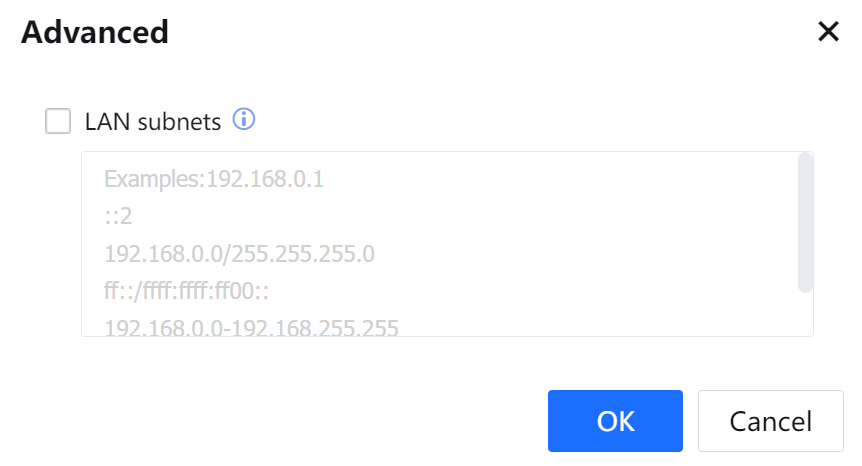
LAN subnets: The LAN subnets refer to the LAN segment that accesses the Internet through the device. It is enabled, user data not in the list will be blocked, and users in the list will be blocked if there is an attack.
Block for (minutes): Sets the blocking time of the attacking host after the device detects the attack in the unit of a minute.
Select Give Alert to enable mail alert. For details, see System > General > Alert Options.[A193]
Click OK to save the configuration.
3.10.2.2.2.2 ARP Protection
ARP spoofing is a common LAN virus. A computer with this virus sends an ARP spoofed broadcast packet to the LAN irregularly, which will interfere and damage the LAN machines' regular communication. In severe cases, the entire network is disconnected.
The device realizes the ARP Protection by cooperating with the accessing client of the LAN PC.
The device protects the ARP cache by refusing ARP requests or replies with attack features to achieve its immunity.
If the access control user of the device is bound to the IP/MAC, the bound IP/MAC information will prevail in the device.
The LAN PC executes the ARP Protection through cooperation with the accessing client. After the accessing client is installed, the accessing client communicates with the device to obtain the correct IP/MAC relationship between the device and the gateway and perform the static binding.
The configuration interface is as below:
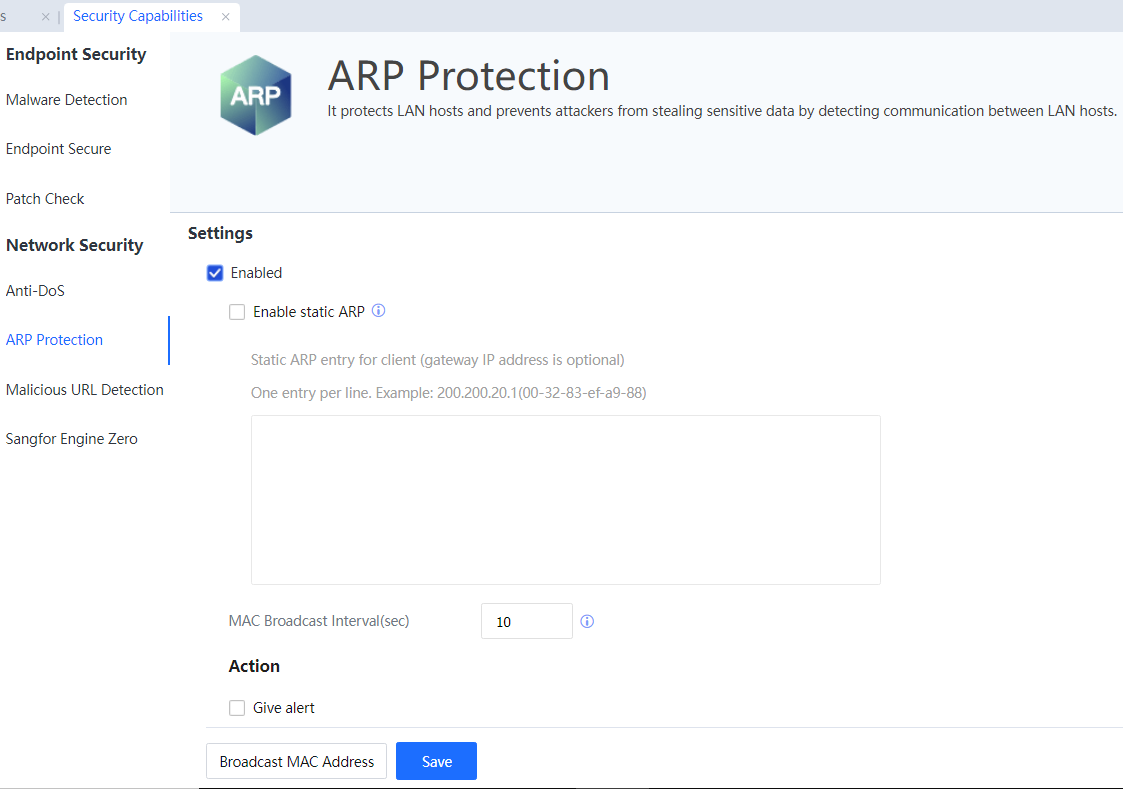
Enable ARP Protection: It is the master switch that enables ARP protection.
Enable static ARP: If the LAN PC's gateway is not the device's interface address, it needs to be set here. For example, if the device uses the bridge mode, the gateway address of the LAN PC should be the interface address of the front router (or firewall). Then we can fill the interface IP/MAC of the front router into the box below. Suppose the LAN PC is installed with the accessing client. In that case, it can obtain the correct gateway IP/MAC for binding, ensuring the correct IP/MAC of the PC gateway and normal communication between the PC and the gateway.
MAC Broadcast Interval (sec): Set the interval for the broadcast gateway (that is, the LAN interface of the device) MAC. The recommended interval is 10 seconds.
Select Give Alert to enable mail alert. For details, see System > General > Alert Options[A194].
Click Save[A195] to save the configuration.
3.10.2.2.2.3 Malicious URL Detection
Based on the Sangfor Cloud-based Engine and multi-malware detection mechanism, comprehensive judgment can be made using static detection, dynamic sandbox, taint checking, manual analysis, and other technologies. Malicious URLs are identified in real time to protect user services from impacts, including phishing and malicious websites, vulnerability exploitation, mining page, malicious jumps, cross-site scripting attacks, and virus files.
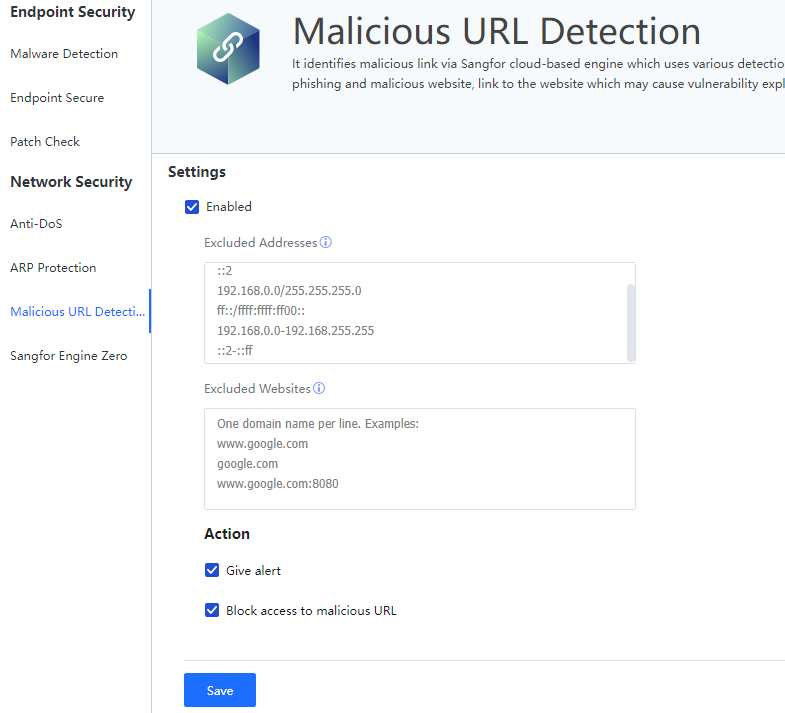
Select Enabled.
Excluded Addresses: IP addresses that do not need to be detected and can be added to the whitelist.
Excluded Websites: Websites that do not need to be detected and can be added to the whitelist.
Action: Select the Give alert combined with the System > General > Alert Options[A196] and Block access to malicious URL.
3.10.2.2.2.4 Sangfor Engine Zero
Sangfor Engine Zero exploits ensemble learning to make the best of different machine learning and deep learning algorithms. By efficiently extracting effective features from files, Sangfor Engine Zero achieves an industry-leading ransomware detection rate. Collaborating with Sangfor Neural-X and NGAF, Sangfor Engine Zero is able to continuously evolve and improve its detection capability.
Sangfor Engine Zero is for virus scanning and removal of the data passing through the device to protect the security of the LAN computer. The device can perform virus scanning and removal under four common protocols: HTTP, FTP, POP3, and SMTP. The device has a built-in Sangfor Engine Zero developed by Sangfor, with a high virus recognition rate and scanning and removal efficiency. Unlike the traditional rule base update, the Sangfor Engine Zero is still in a rule base to maintain the habit. The current update cycle is two months.
The Sangfor Engine Zero settings interface includes the antivirus switch for four protocols, and websites with no need for antivirus or file whitelist.
The Settings interface is as shown in the following figure.
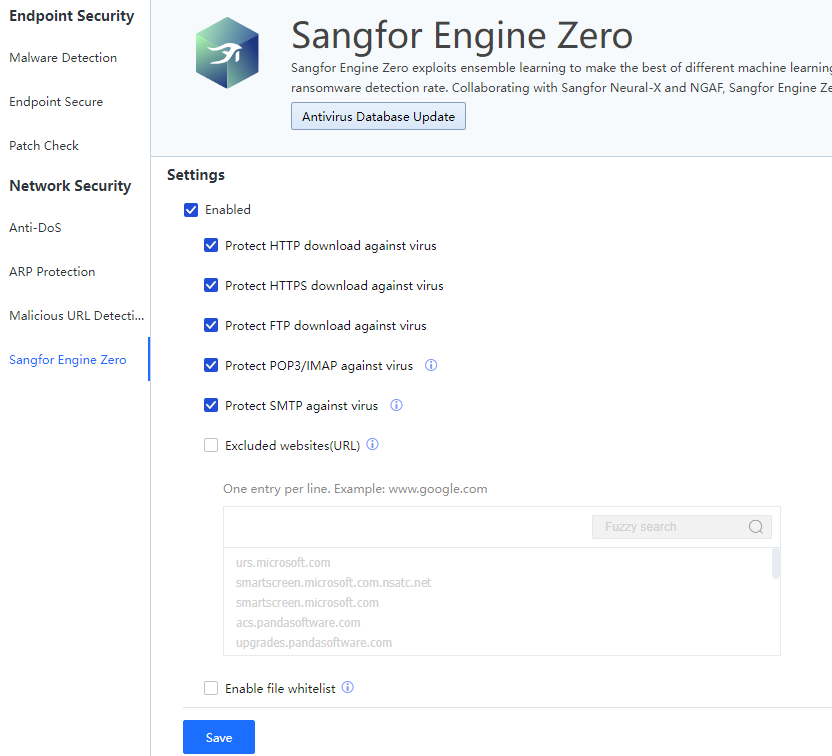
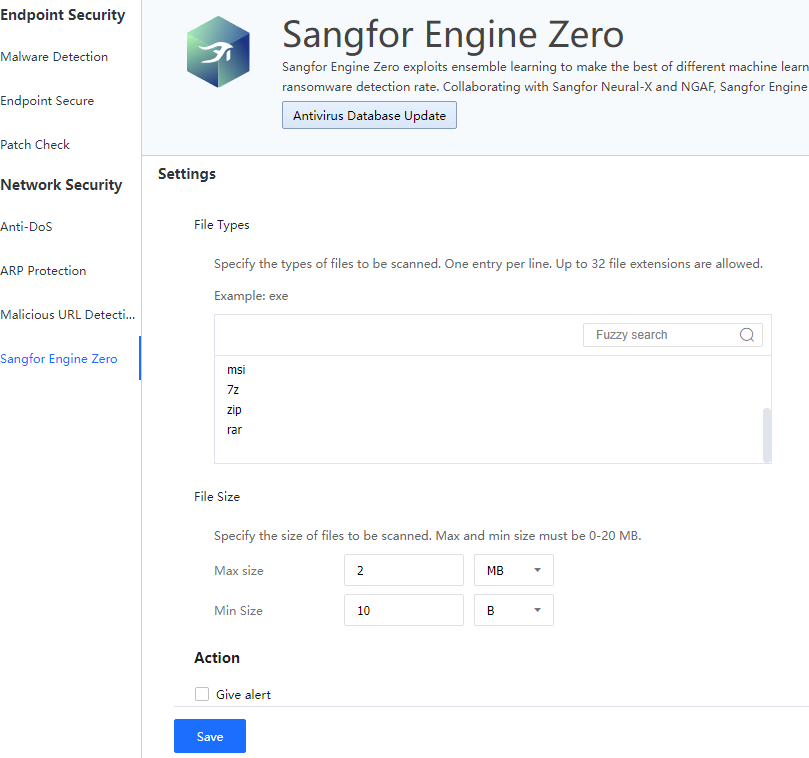
Select Protect HTTP download against virus, Protect HTTPS download against virus, Protect FTP download against virus, Protect POP3/IMAP against virus, and Protect SMTP against virus to enable the antivirus switches for these five protocols.
Excluded Websites (URL): Set the access data to particular websites with no need for antivirus. The input is in URL format, supporting the wildcard and one entry per row.
Enable file whitelist: To define files that do not require antivirus.
Action: Select the Give alert and combined with the System > General > Alarm Option.
Click OK to save the configuration.
Antivirus Database Update:
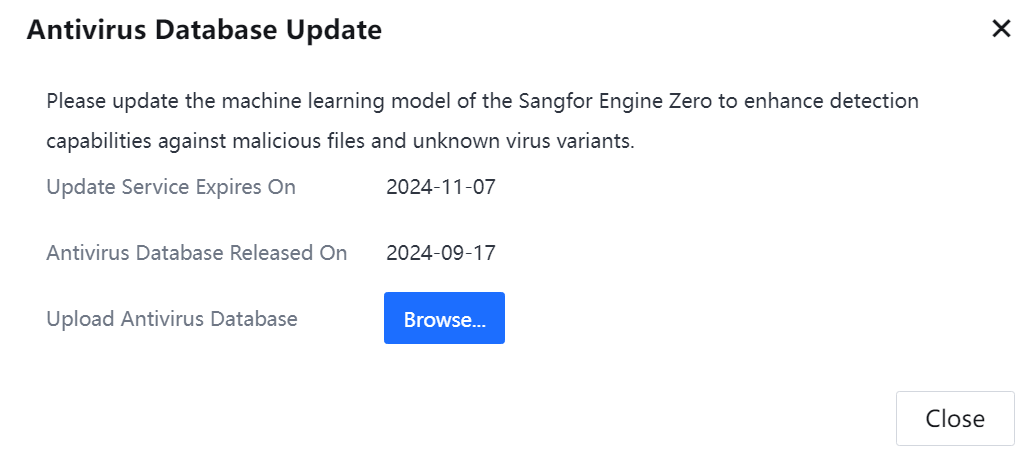
Update Service Expires On: It displays the automatic update expiration date of the Sangfor Engine Zero. During the expiration date, the device will automatically connect to the server of Sangfor Technologies Inc. to update the Antivirus Database.
Antivirus Database Release On: It displays the current date of the Antivirus Database.
Upload Antivirus Database: Manually import the downloaded Antivirus Database file into the device and complete the Antivirus Database update. Click Browse to select the Sangfor Engine Zero model file to be imported and complete the Antivirus Database update.




