Scenario
Telecom provides schools with basic broadband access equipment. It has formulated management regulations to stipulate that students cannot use telecom campus accounts to share the Internet. As long as school students use a proxy or private proxy tools, high-privileged users will act as low-privileged users to access the Internet. The management system is useless.
Some management devices use the method of installing controls and blocking the process to disable the proxy, which is extremely inconvenient; the use of the anti-proxy function of IAG can provide the function of disabling the endpoint to use the intranet proxy without plug-ins.
Configuration Steps
Step 1.In the Endpoint Mgt > Connection Control > Connection Sharing in the navigation menu page, enter the configuration page of connection sharing, and select Enable connection sharing detection.
Step 2.On the connection sharing options page, click setting, and select the statistics method to count all endpoints. Set the number of endpoints reached two or more, and lock the user for 30 minutes.
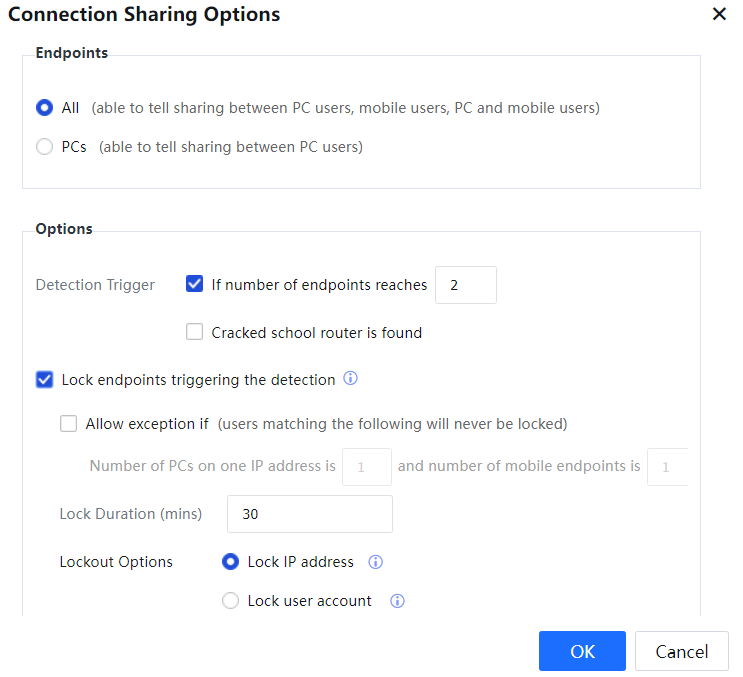
Endpoints Select All to identify the sharing between PC and PC, PC and mobile endpoint, and mobile endpoint and mobile endpoint.
What Would You Like to Lock: Select Lock IP address. Only one user is allowed to go online for one IP address.
Step 3.Verification method:
• After the PC is connected to the network, the IP address is automatically obtained through DHCP. The test account is used to pass the IAG platform authentication, and it can go online normally.
• Install 360 computer WIFI on the PC, start 360WIFI, and release the hotspot.
• The mobile phone connects to the SSID sent by the PC, and the proxy can go online.
• Use the browser on the PC to access the webpage and use the WeChat and other App applications on the mobile phone. After some time, the two endpoints are detected as shared Internet access.

Exceptions are allowed: the number of single IP computer endpoints is 1, and mobile endpoints are 1. Refers to the sharing of Internet access between a computer and a mobile endpoint will be allowed. The shared surfing behavior of two PCs or two mobile endpoints will be blocked.
Step 4.Effect.
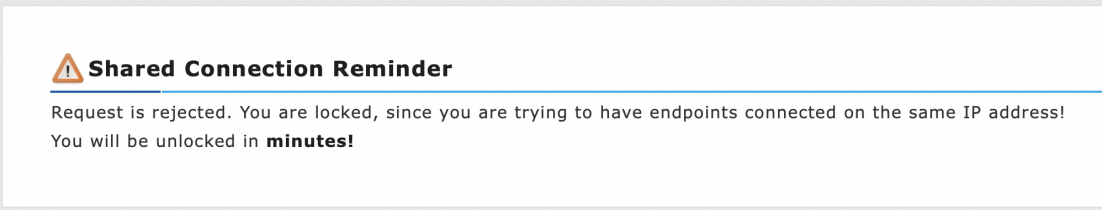
Mobile phone one and mobile phone two access the Internet through a proxy within 5 minutes (the fastest test is about 1 minute). There will be a web page that is blocked by the device's anti-sharing Internet access. The shared access management page recognizes the type of mobile phone and endpoint. The rendering of the mobile phone opening the web page is as follows.