It is to detect and block untrusted mobile endpoint devices’ Internet access attempts. See the following figure.
Enable Mobile Endpoint Verification: It enables or disables the global mobile endpoint device detection function. Click Settings, and the Options window pops up.
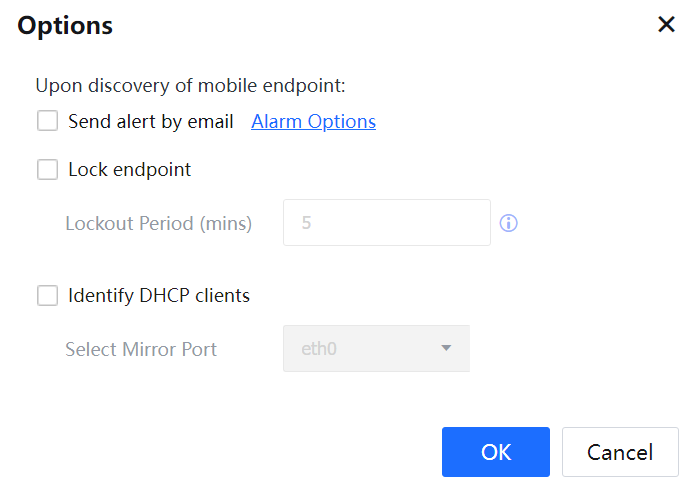
Upon discovery of mobile endpoint: To specify the method for handling a detected attempt of a mobile endpoint device. The options include Lock Endpoint and Send alert by mail. If the Lock Endpoint is not selected, the IAG does not block the Internet access attempts of the APs and mobile endpoint devices in the mobile endpoints list.
You can select Send alert by mail, click Alert Options, and set alert options.
You can select Lock Endpoint and define the lockout period.
Select Identify DHCP clients to strengthen the capability to identify such endpoints after the mobile endpoint accesses the network. This function is new, in addition to the existing application capability of endpoint identification. To support the function of DHCP mobile endpoint identification, mirror the DHCP protocol to the device. This requires configuring the mirror port in the device gateway page to allow the device to capture data package at a specified networking interface.
DHCP mobile endpoint identification is the endpoint type displayed in the online user list and the mobile endpoint interface. The types include Android, IOS, etc.
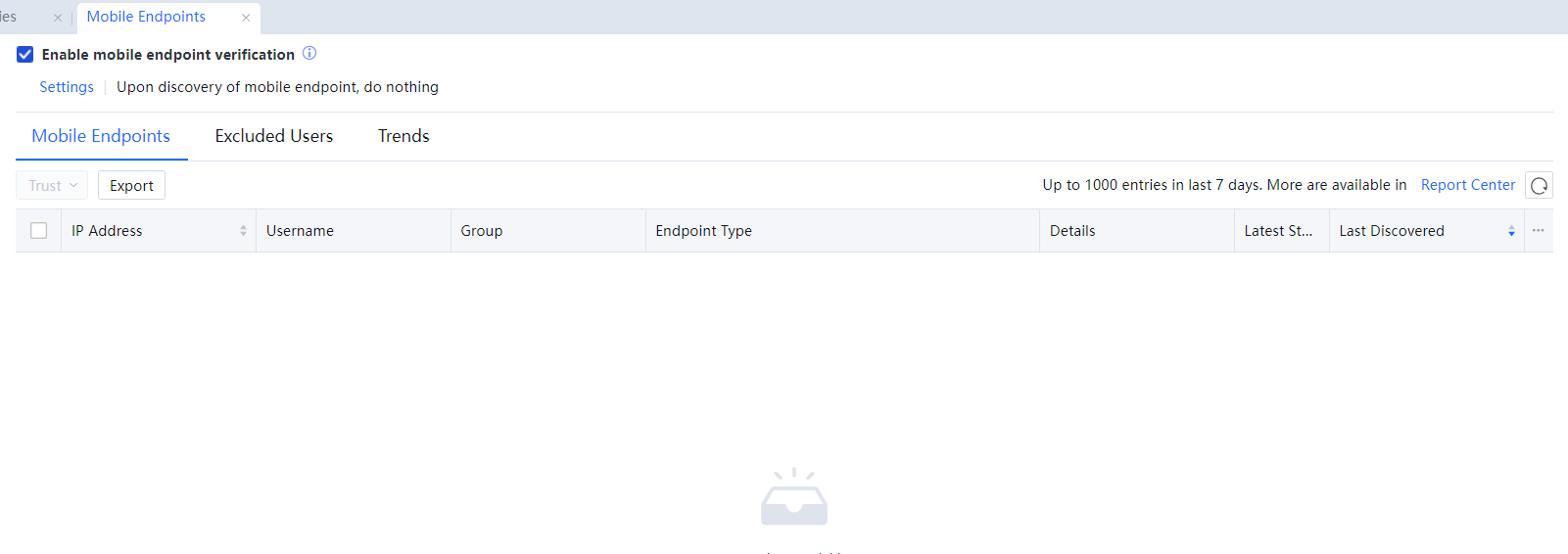
Mobile Endpoints List: It displays the IP addresses, usernames, home groups, endpoint types, details, status, and last detection time of connected mobile endpoints. Mobile endpoint detection is implemented based on traffic characteristics. A hotspot IP address is displayed if an AP works in NAT mode. If the AP works in another mode, a mobile endpoint IP address is displayed.
Click Export List to export the mobile endpoints list to a CSV file. The content and format of the file are the same as the mobile endpoints list.
The mobile endpoints list page displays up to 1000 entries generated within the previous week. You can click Report Center and query for more information on the mobile endpoint management page.
Excluded Users: It is for administrators to prevent the IAG from blocking the Internet access attempts of listed mobile endpoints.
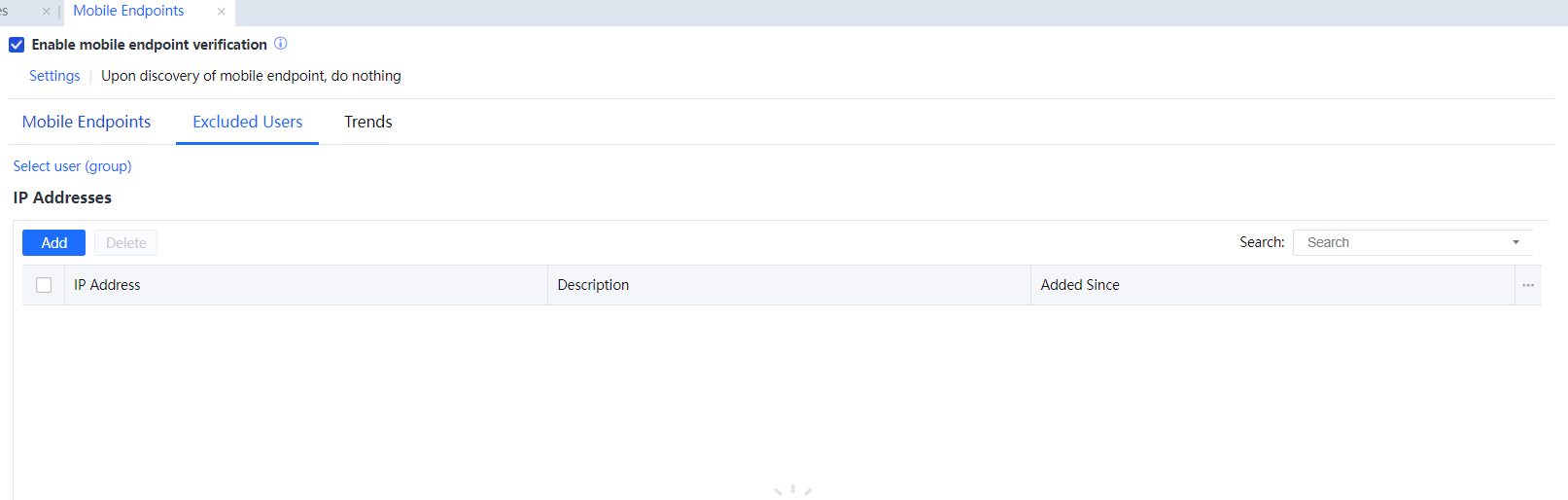
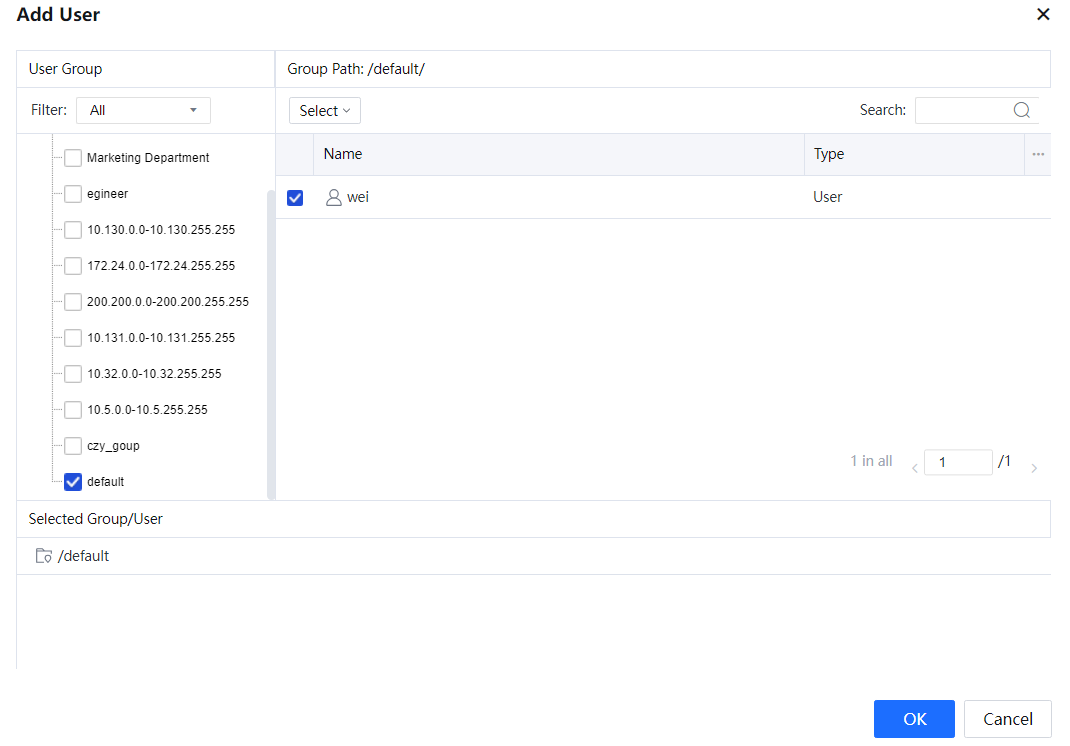
Click Select User(group) and select trusted users and user groups.
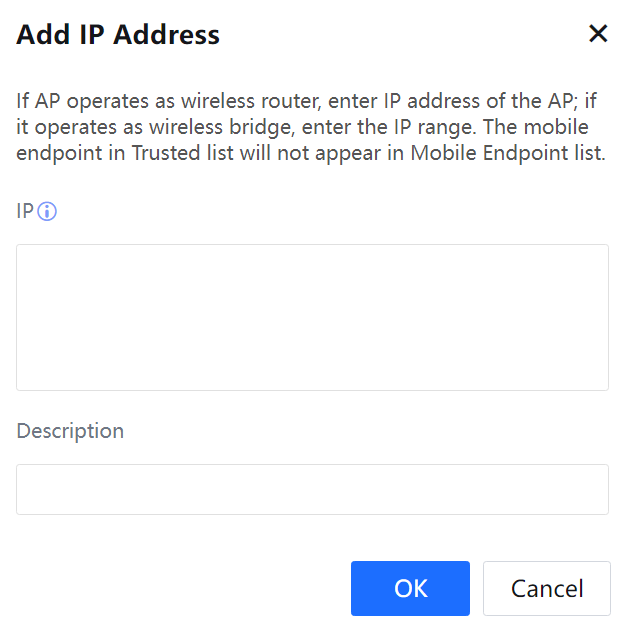
Click Add and enter the IP addresses of APs or the network segments where the APs provide the DHCP function.
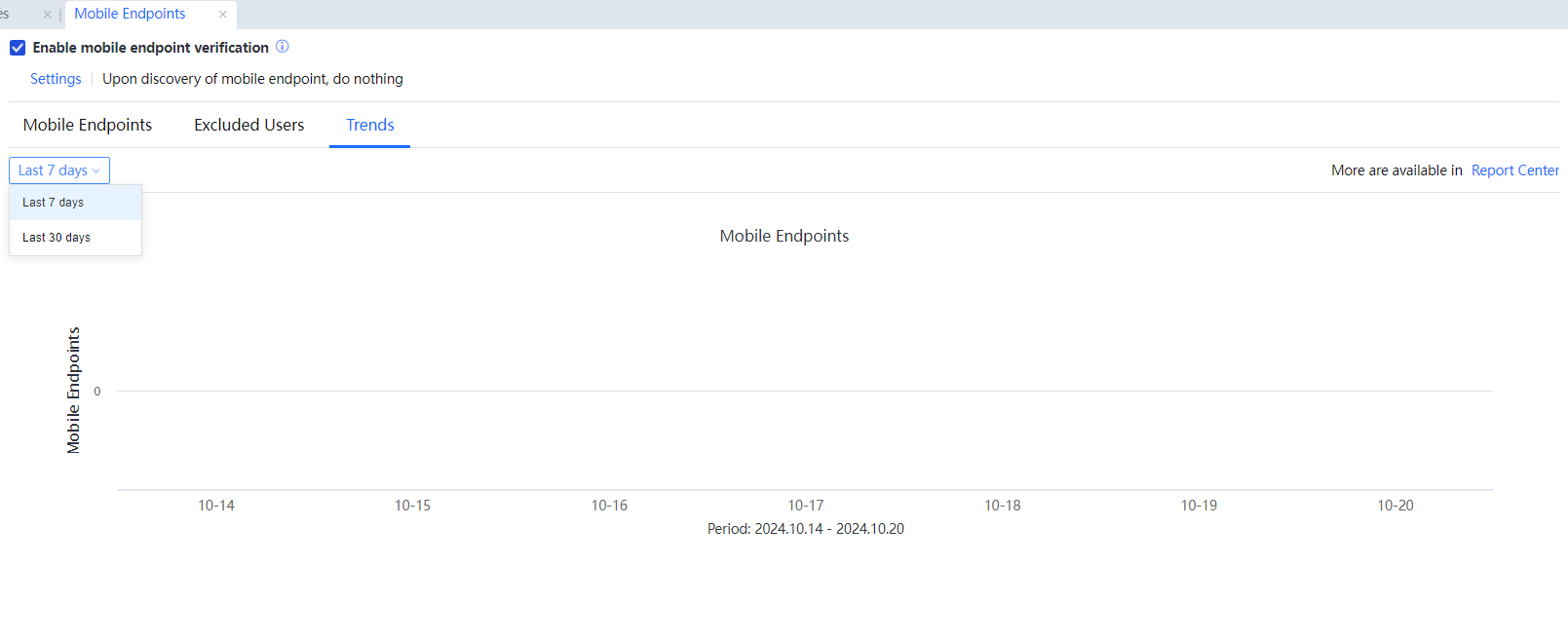
Trends: It calculates the number of mobile endpoints detected in the previous 7 or 30 days. You can click Report Center and query for more information on the mobile endpoint management page. See the following figure.