It is to set the maximum number of endpoint devices allowed for a single IP address or user, preventing intranet users from functioning as Internet proxies for others. The IP address or user is locked when the shared connection is detected and the limit is exceeded. See the following figure.
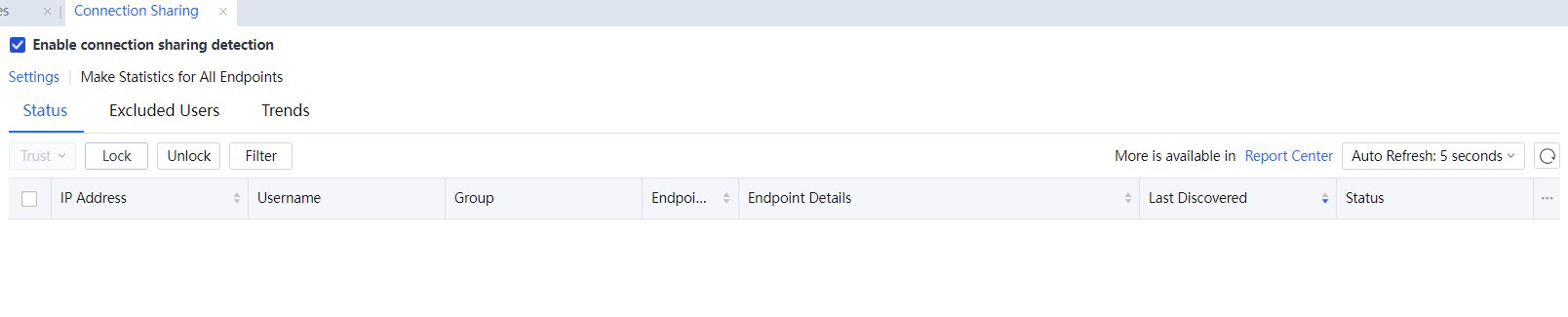
Enable connection sharing detection: To enable the shared connection detection function.
Settings: Click Settings, and the Connection Sharing Options window will be shown[LCH158][A159].
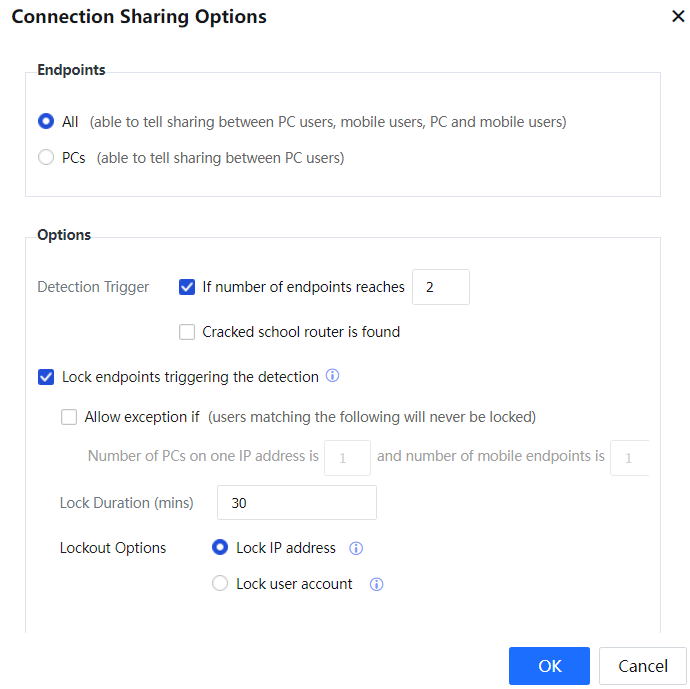
Endpoints:
All: indicates that connection sharing between PC users, mobile users, PCs, and mobile users is detected.
PCs: indicates that connection sharing between PC users is detected[LCH160][161].
Detection Trigger: indicates that the number of endpoints reaches 2 or a cracked school router is found.[A162]
Lockout Options: It is to disable Internet access when the maximum number of endpoint devices sharing a connection is reached.
Allow exception if: It is to specify the exceptions where Internet access is not disabled when the maximum number of endpoint devices sharing a connection is reached. For example, suppose the maximum number is set to 2, but one PC and one mobile endpoint device can use the same IP address to access the Internet. In that case, Internet access is not disabled, and connection sharing is recorded.
Lock IP Address: indicates that all Internet access data from a specified IP address is rejected when connection sharing using the IP address is detected.
Lock user account: indicates that all Internet access data of a specified user is rejected when connection sharing using the username is detected.
Click OK[A163].
Status List: It displays the IP addresses and usernames that are used to share Internet connections. You can lock and unlock users on the page or add users to the excluded users list.
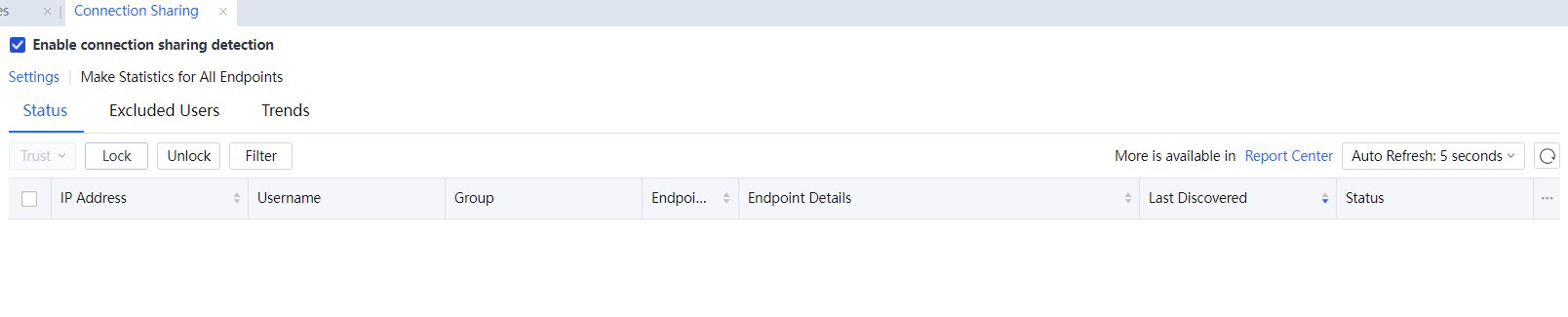
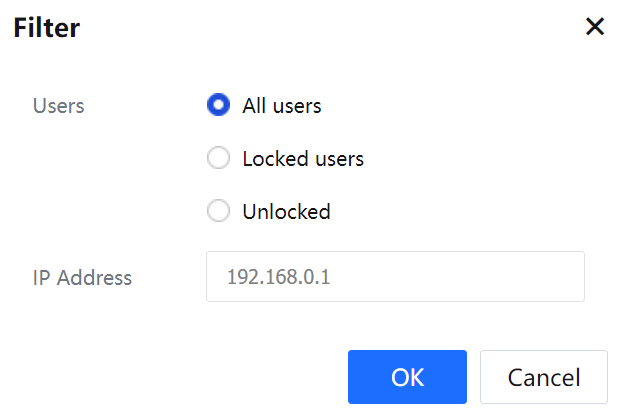
Filter: It is to filter user types in the list. You can select all users, locked users, unlocked, or select users based on IP addresses.
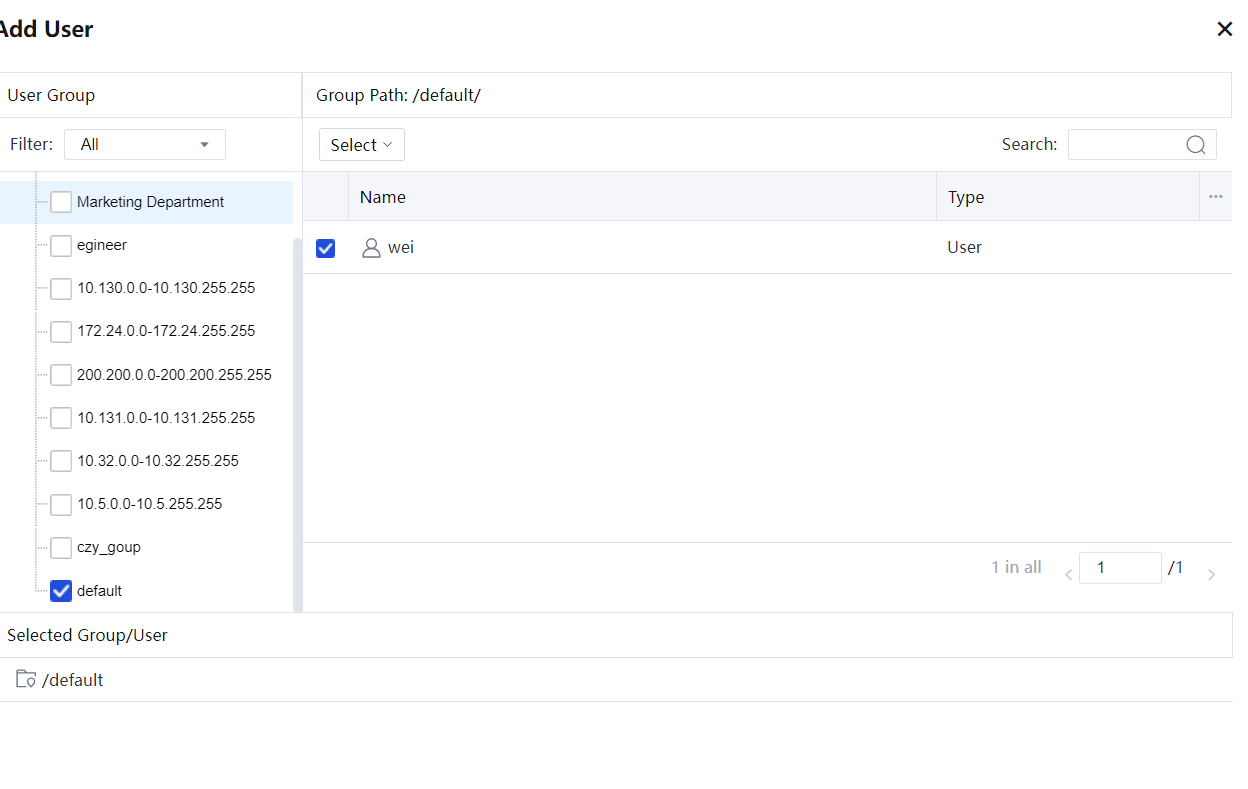
Excluded Users: It is to add users, user groups, and IP addresses to a list so that they are excluded from detection of connection sharing.
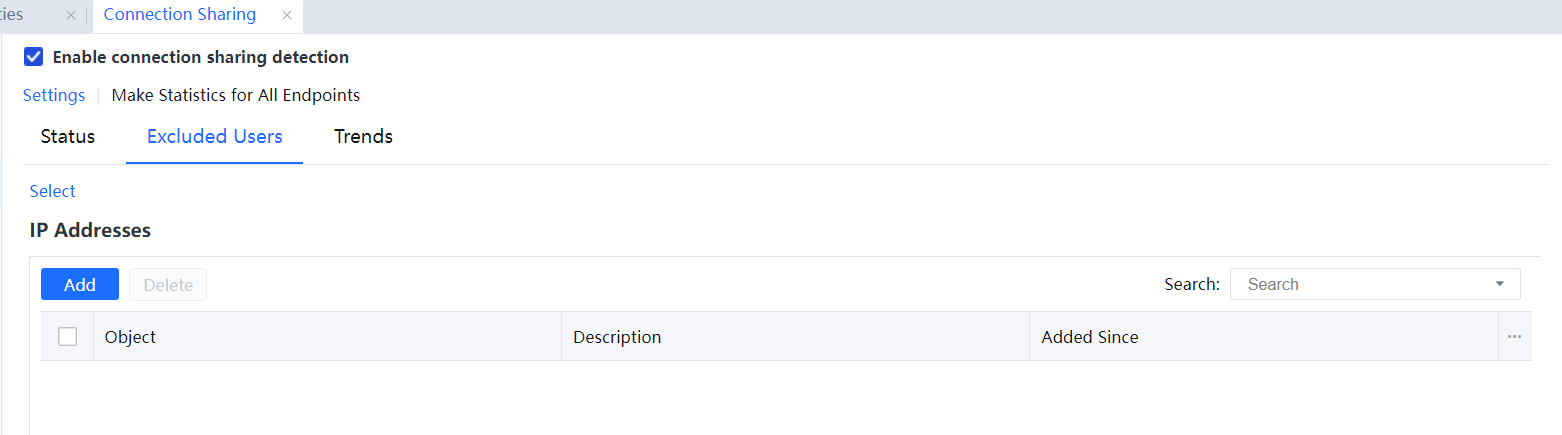
Click Excluded Users (Groups) and select trusted users and user groups. See the following figure.
Under IP Address, click Add and enter the trusted IP addresses or IP address ranges. See the following figure.
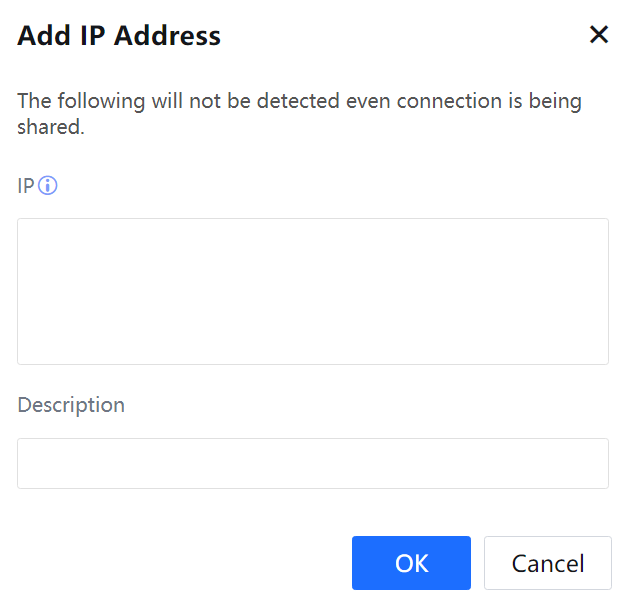
Click OK[A164].
Trends: It calculates the number of users who have used shared Internet connections in the last 7 or 30 days. The statistics can be collected by source IP address or username. See the following figure.
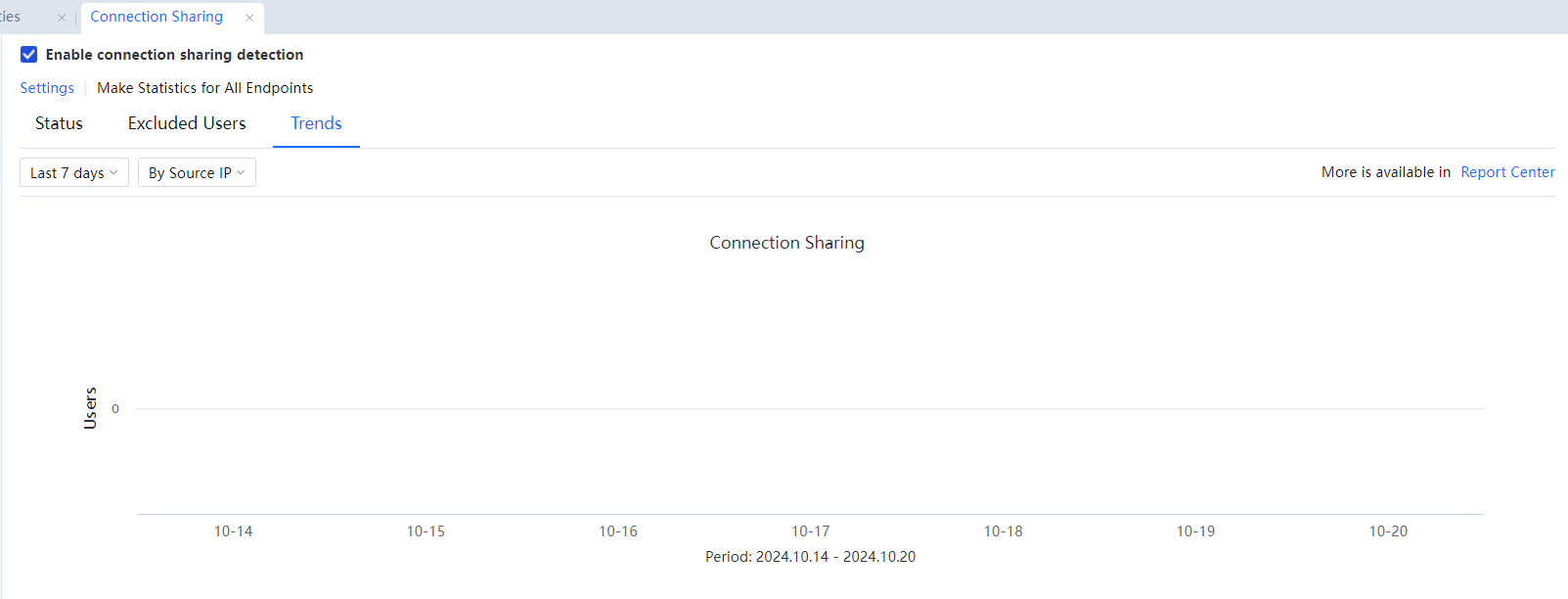
To view more information about users who use shared Internet connections, click Report Center.




