Access Audit enables auditing on Internet access behavior and content of intranet users accessing the Internet over the IAG.
To audit the application, select Application and click Add to select Item.
HTTP Data Outgoing: You can select Web-based BBS posting to record intranet users’ behavior of visiting and posting on web BBSs. The log records the posting information except for the post subjects and content. You can select Web Mail contents to record intranet users’ behavior of sending mails through webpages. The log records the mail information except for the mail subjects and content. You can select Web-based attachment upload (including WebMail) to audit file names of attachments uploaded over webpages. To audit attachments of webmails, select this check box. You can select Web-based text upload to record behaviors of uploading text over HTTP. If this check box is selected, there will be a large number of logs.
Therefore, you are recommended to select Web-based BBS posting and Web Mail contents instead. You can select Microblogging contents to record intranet users’ behavior of posting microblogs through the Microblog desktop client and web browser. The microblog subjects and content are not recorded. To audit the file names of image and video attachments posted on microblogs, select Include microblog attachment (such as image, video and music).
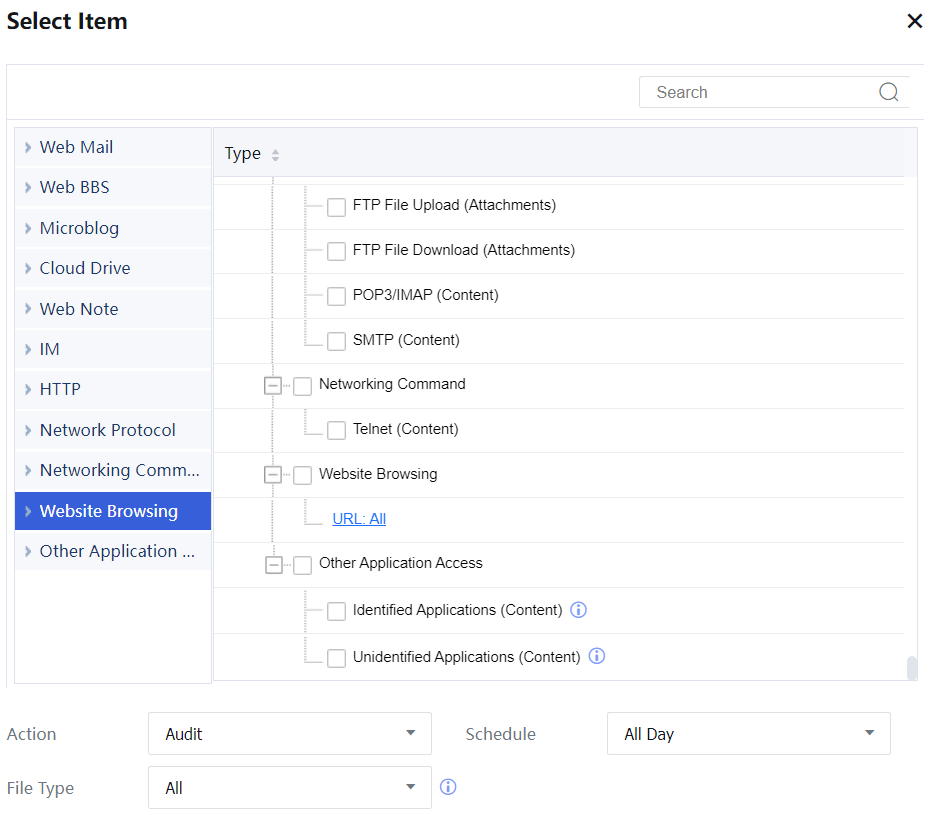
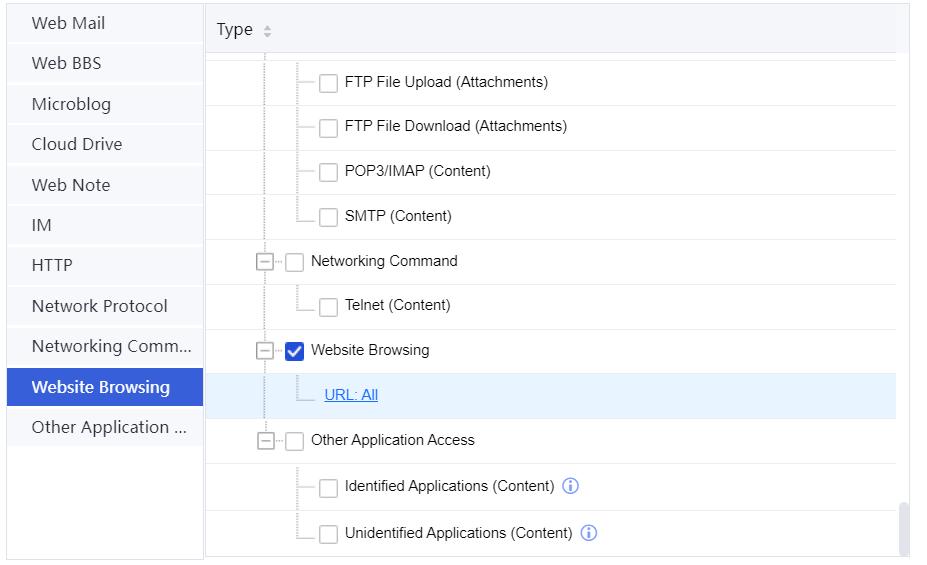
Website Browsing/Downloads: To record the URLs of webpages accessed by intranet users and the names of files downloaded from websites. You can select All to audit all URLs. You can also select Specified to specify URL types so that only access to the URLs of the specified types is recorded. When you click Specified, the Select page is displayed. On the page, you can select the URL group to be audited. (For details of setting URL groups, see Section 3.5.4.) If you select File name of downloaded file, the names of files downloaded from websites using the HTTP protocol are audited, and file content is not recorded.
You can also set the level of URL record details at Activity Audit > Advanced > Logging.
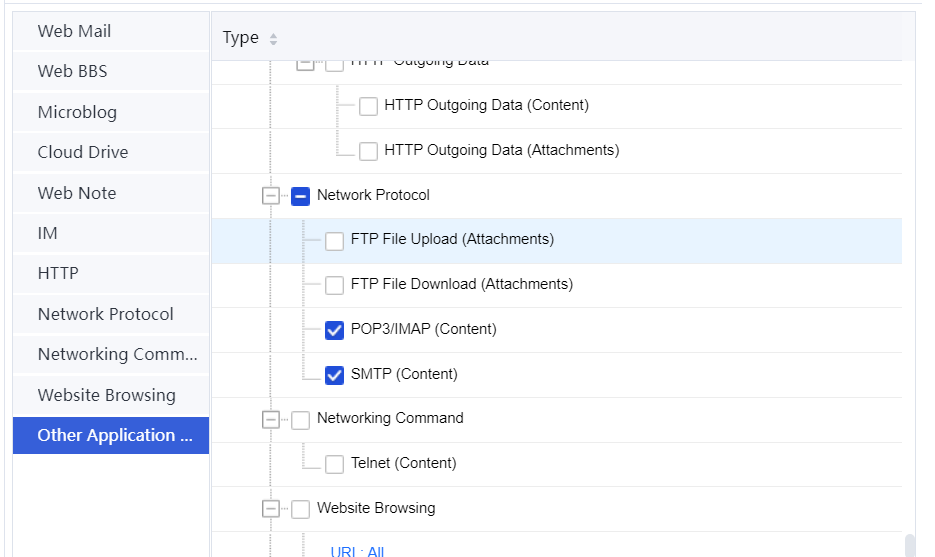
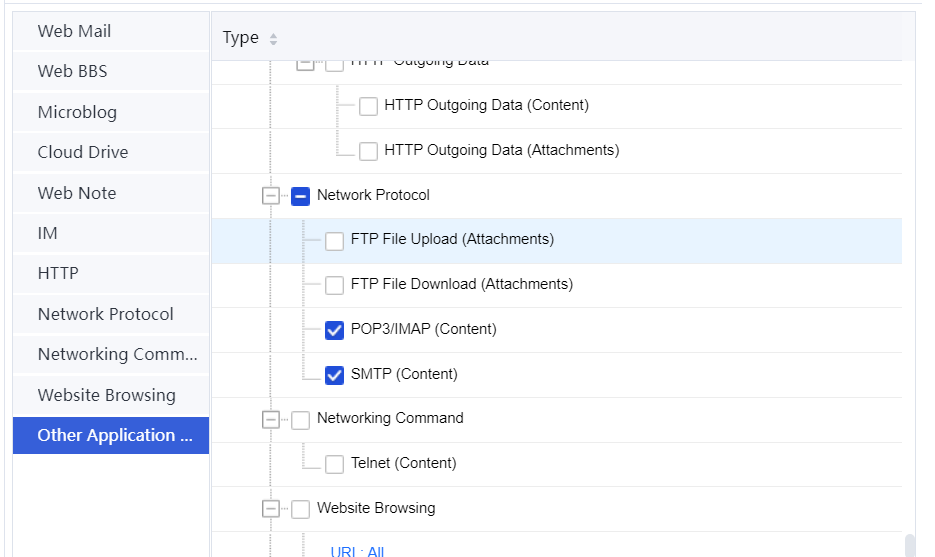
Email: It audits intranet users' attempts to send and receive emails using the mail client. You can select Outgoing email (SMTP) to audit intranet users' attempts to send emails. In this case, mail information excluding subjects and bodies is logged. You can select Incoming email (POP3/IMAP) to record intranet users' attempts to receive emails. In this case, email information excluding subjects and bodies is logged.

The email receiving and sending protocol must be POP3/IMAP and SMTP.
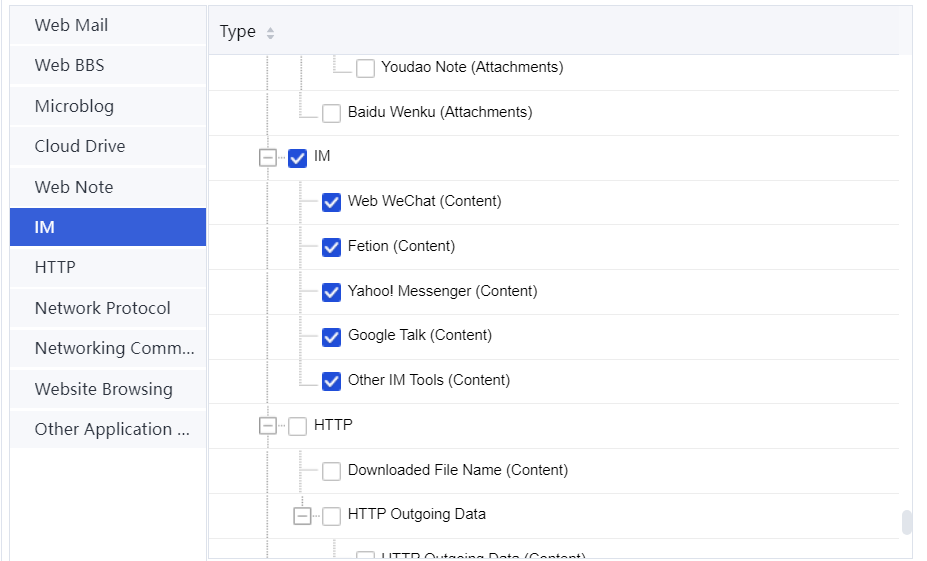
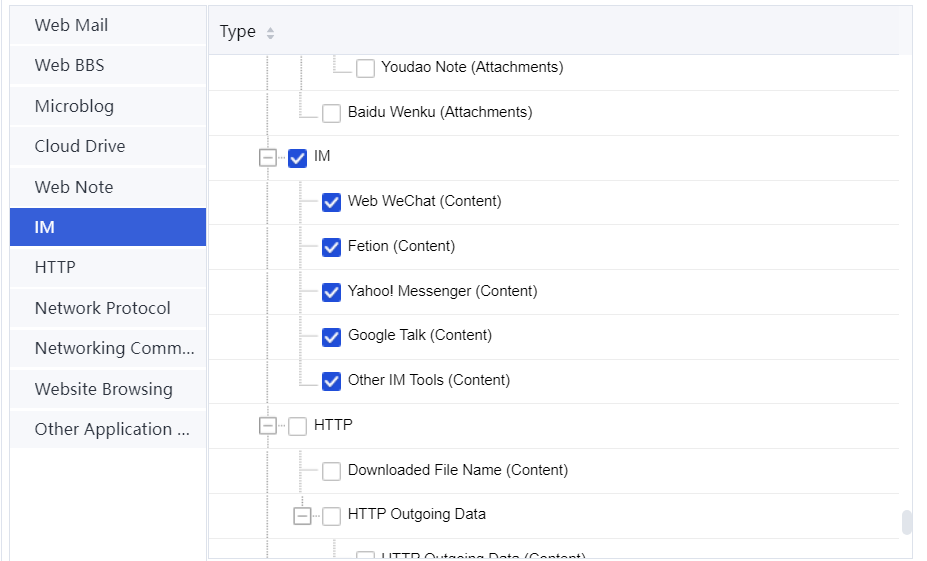
IM: It audits instant messaging between intranet users with IM tools. The tool options include MSN, Yahoo, Google-Talk, Fetion, WebQQ, and Web-MSN. Other IM chats: It specifies whether to audit IM content when an IM type is added to the audit rule library.
FTP: To audit the names and content of files uploaded by intranet users using FTP and the names of files downloaded by intranet users using FTP.
Telnet: To audit the commands run by intranet users using Telnet. The port number must be 23.
Application: To audit intranet users' Internet access behaviors. You can select Access to other applications (exclusive of contents) to audit the identifiable Internet access behaviors. You can also select Access to unidentified applications (on which address and port. It incurs massive logs) to audit the Internet access behaviors that the IAG cannot identify. If this option is selected, the IAG records destination IP addresses and port numbers using a large number of logs. By default, this option is not selected, and you are recommended to use the default setting.
To audit users' content, enable content audit SNs. Then, the outgoing HTTP packets, website visits or downloads, emails, IM content, FTP content, TELNET content, and Internet access behaviors are audited.
Example: Configure a policy for auditing web BBS post content, text, and images sent using microblogs, webmails, and attachments, users' webpage access attempts, names of files downloaded from websites, and various types of identified Internet access behaviors.
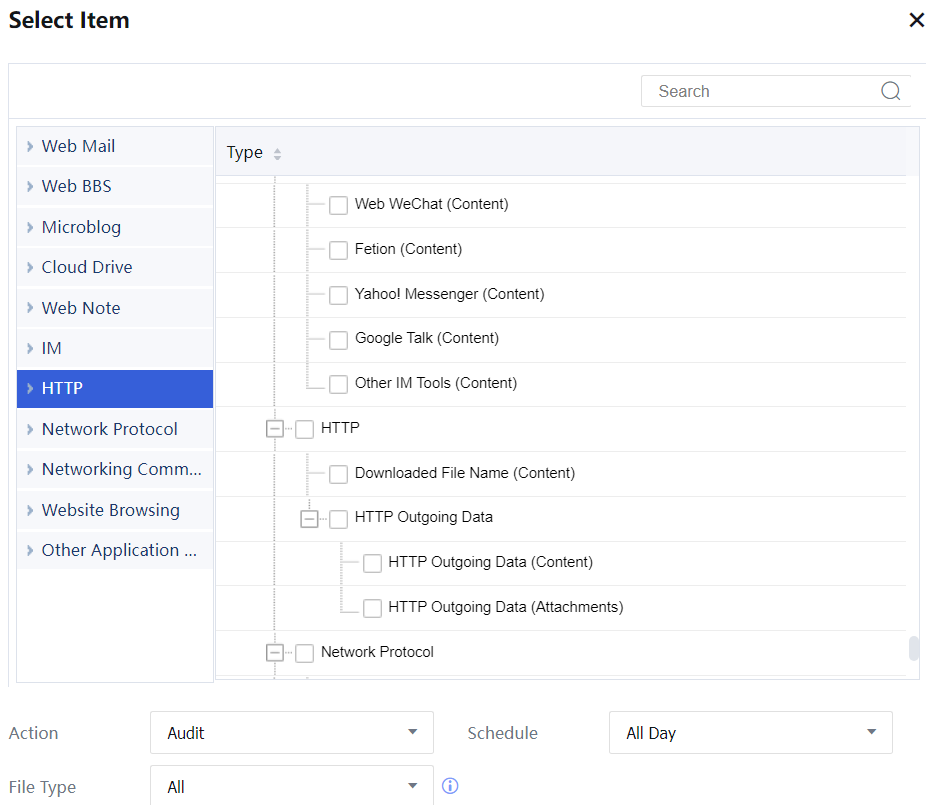
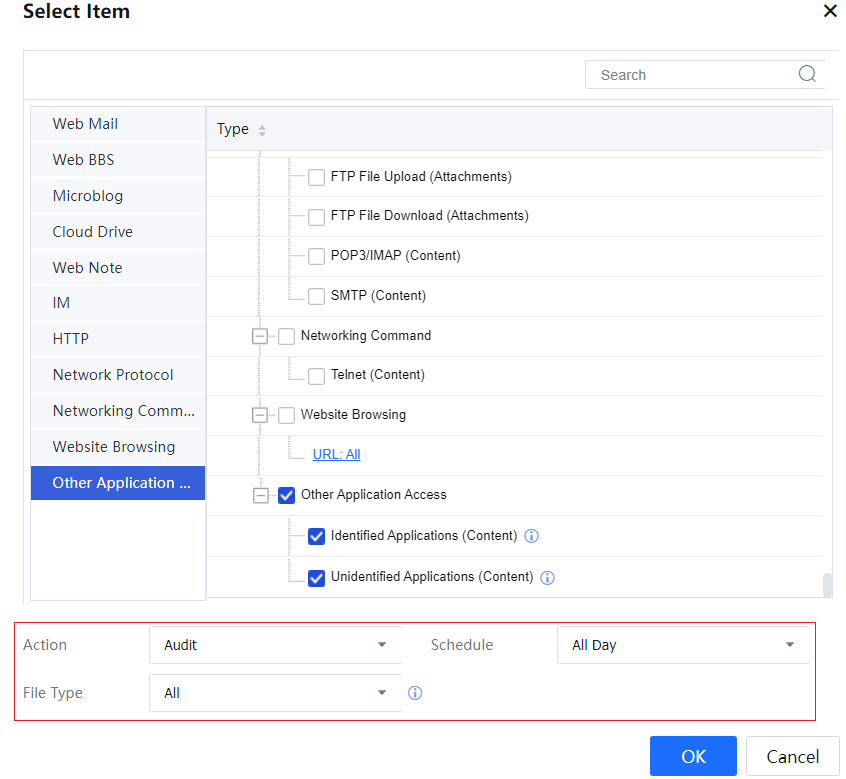
Step 1.Select Access Audit, and the Access Audit page is on the right. Click Add and then the button below Item. In the Select Item window that appears, select the objects to be audited.
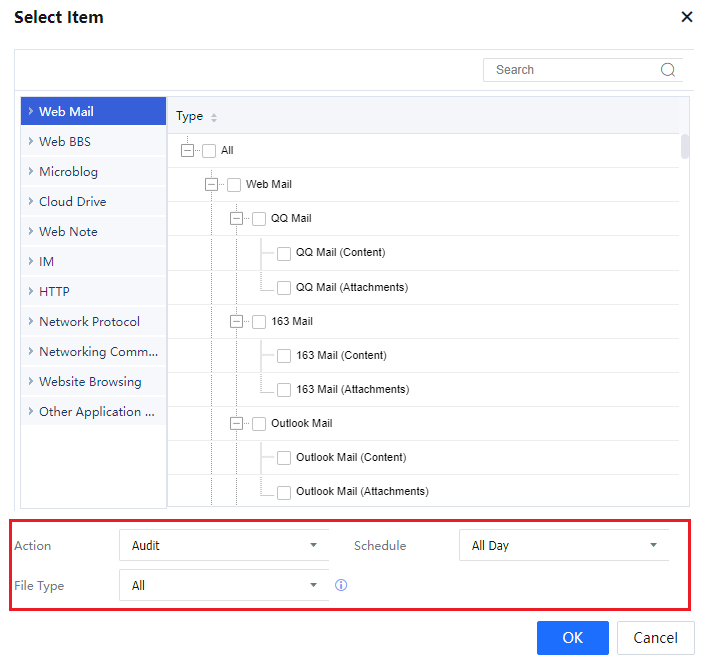
Step 2.The Select Item window includes the HTTP Data Outgoing, Website Browsing/Downloads, Email, IM, FTP, Telnet, and Application menu items. You can click the menu items to go to the corresponding configuration modules.
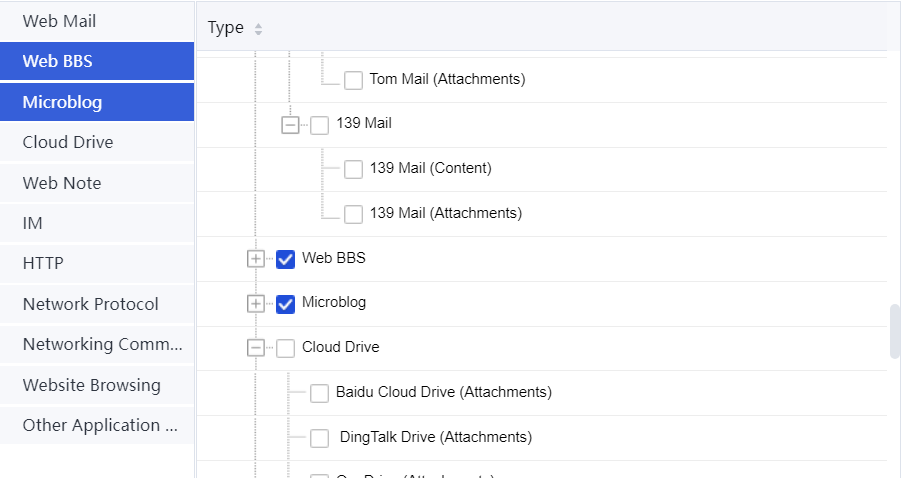
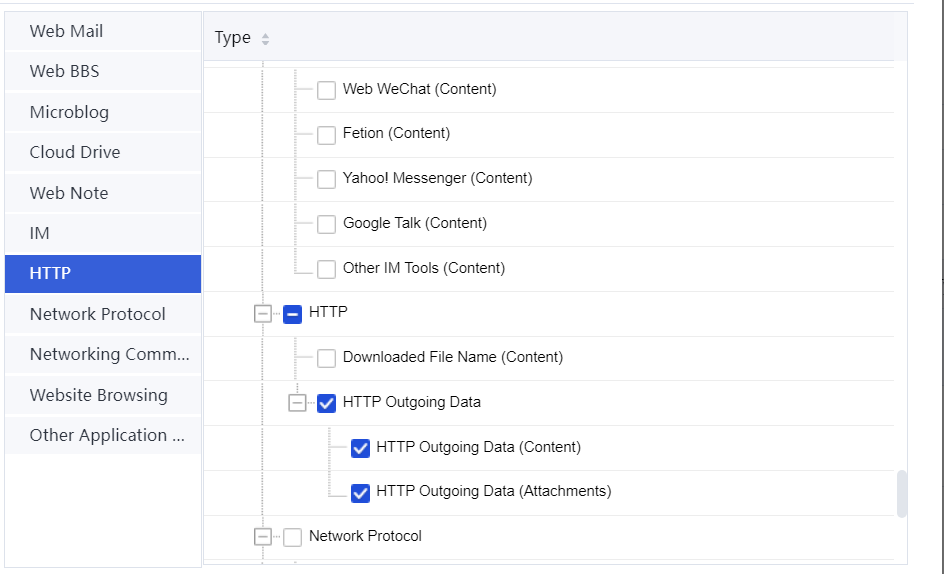
Step 3.Outgoing HTTP Packets: You can select Web-based BBS posting to audit the content of posts created by intranet users in BBSs. The logs record all post information, including subjects and bodies of posts.
You can select Web Mail contents to audit the bodies (excluding attachments) of emails sent by intranet users through webpages. You can also select Web-based attachment upload (including WebMail) to audit the attachments uploaded through webpages. This option is required for auditing webmail attachments. You can select Web-based text upload to record all the text uploaded over HTTP.
If this check box is selected, there will be a large number of logs. Therefore, you are recommended to select Web-based BBS posting and Web Mail contents. You can select Microblogging contents to audit intranet users’ behavior of posting microblogs through the Microblog desktop client and web browser. To audit the images and videos posted on microblogs, select Include microblog attachment (such as image, video and Music). Configure the policy for auditing web BBS post content, text, and images posted using microblogs, webmails, and attachments. See the following figure.
Website Browsing / Downloads: To record the URLs of webpages accessed by intranet users and the names of files downloaded from websites. You can select All to audit all URLs. You can also select Specified to specify types of URLs so that only access to the specified type of URLs is recorded.
When you click Specified, the Select page is displayed. On the page, you can select the URL group to be audited. If you select File name of downloaded file, the names of files downloaded from websites using the HTTP protocol are audited, and the file content is not recorded.
You can also set the level of URL record details at Activity Audit > Advanced > Logging.[A151]
Configure the policy for auditing access of intranet users to webpages and names of files downloaded from webpages.
Email: To audit intranet users' attempts to send and receive mails using the mail client. You can select Outgoing email (SMTP) to audit the information about emails, including email attachments sent by intranet users. You can select Incoming email (POP3/IMAP) to audit the information about emails, including email attachments, received by intranet users.
IM: To audit instant messaging between intranet users with IM tools. The tool options include MSN, Yahoo, Google-Talk, Fetion, WebQQ, and Web-MSN. Other IM chats: To specify whether to audit IM content when an IM type is added to the audit rule library.
FTP: To audit the names and content of files uploaded by intranet users using FTP and the names of files downloaded by intranet users using FTP.
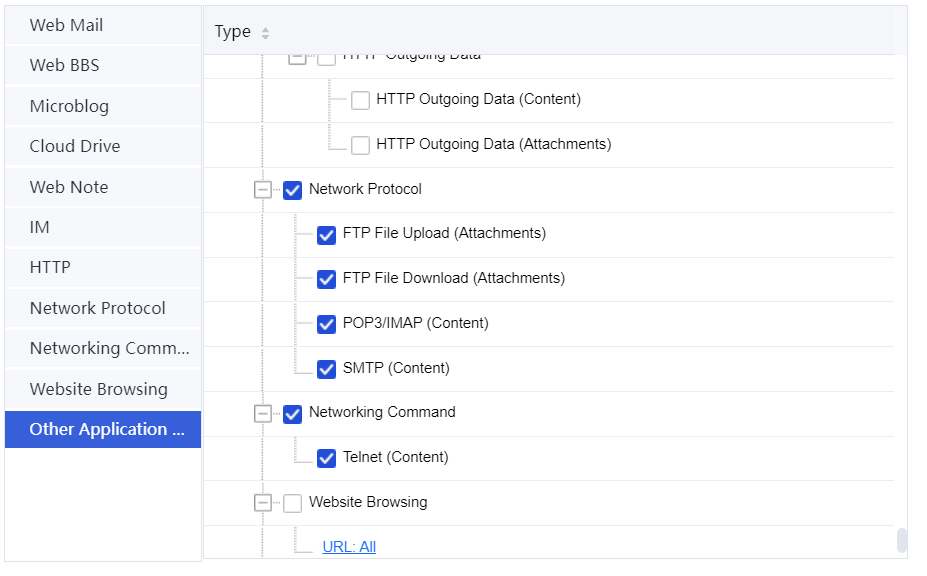
Telnet: To audit the commands run by intranet users using Telnet. The port number must be 23.
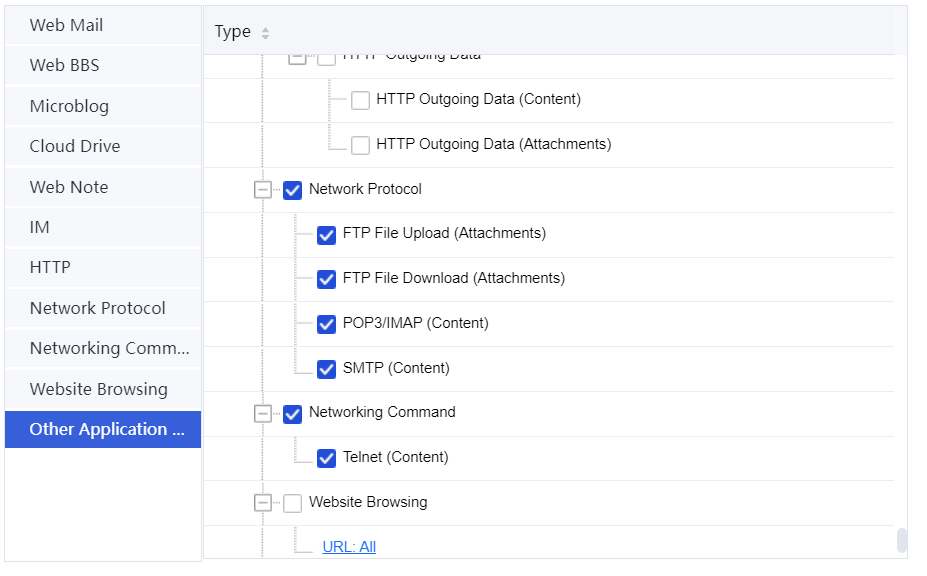
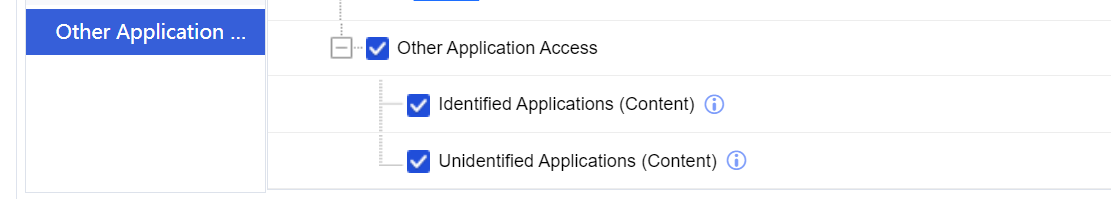
Application: To audit intranet users' Internet access behaviors. You can select Access to other applications (exclusive of contents) to audit the identifiable Internet access behaviors. You can also select Access to unidentified applications (on which address and port. It incurs massive logs) to audit the Internet access behaviors that the IAG cannot identify. If this option is selected, the IAG records destination IP addresses and port numbers using a large number of logs. By default, this option is not selected, and you are recommended to use the default setting.
Configure the policy for auditing various types of identified Internet access behaviors. See the following figure.
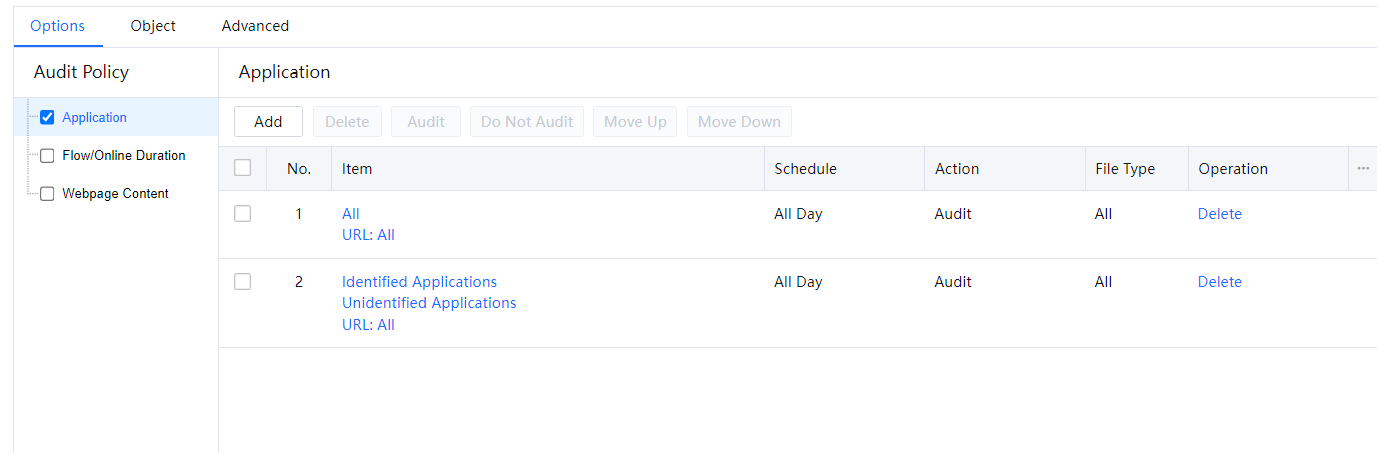
Step 4.Step 3 After selecting audit options, click OK. The Application page is displayed. Set Schedule to All Day and Action to Audit.
Step 5.Click OK. The policy for auditing web-based BBS posting, microblogging content, webmail content, web-based attachment upload, users’ visited URL, the file name of download file, and various types of identified Internet access behaviors is configured.

The behaviors and content of web MSN users can only be audited if the web MSN users log in using HTTP. If the users log in via HTTPS, the behaviors and content cannot be audited.




