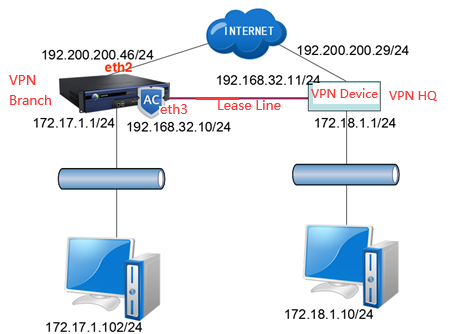
Scenario
The client's branch uses IAG on the prefectural-municipal port, and employees in the branch need to access the LAN applications in the provincial branch’s intranet. The IAG in the branch and the port device in the provincial branch (the headquarters) are connected to the VPN; meanwhile, the branch and the provincial branch also are connected to the leased line. When the leased line is normal, the branch should access the applications in the provincial branch using this line. When the leased line is disconnected, it is automatically switched to a VPN line.
Implementation Method:
The IAG is equipped with link load balancing, and it will go through a leased line by default and switch to the VPN when the leased line is abnormal.
Test Topology:
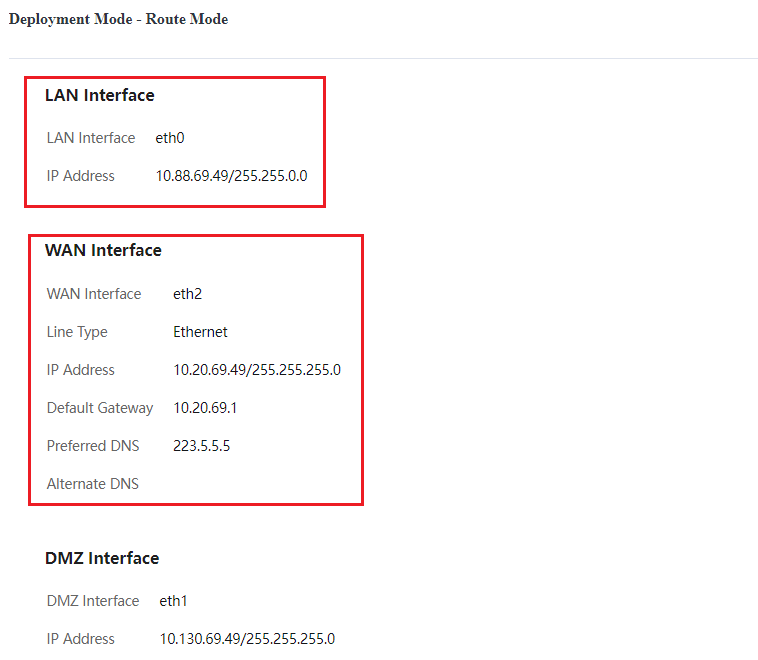
Configuration of device route mode: There are two WAN lines, one connects to the VPN, and the other one connects to the headquarters as the leased line.

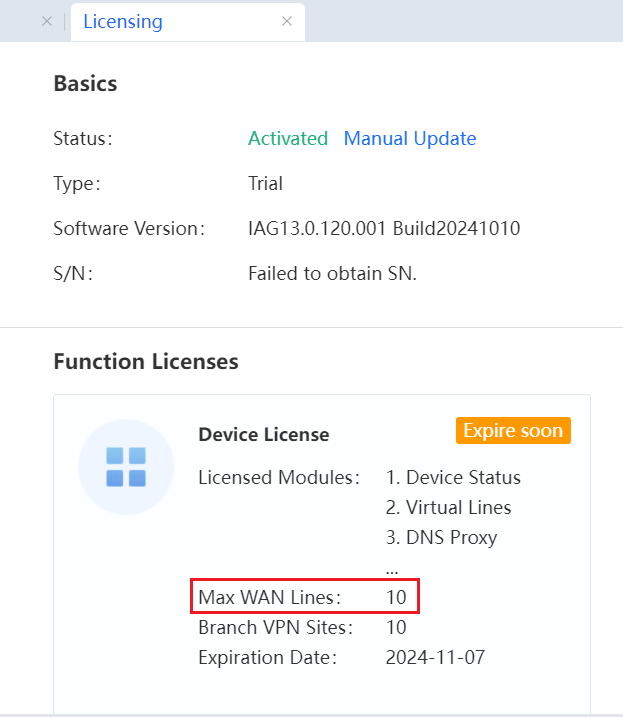
Prerequisites:
The IAG is equipped with two WAN lines, at least. One is connecting the VPN, and the other is used to connect the leased line.
Describe the network segment of the branch LAN and the network segment of the headquarters LAN to be accessed to introduce overall deployment in the branch and the headquarters. For example, which device in the headquarters offers a VPN connection, and the leased line is connected to which device networking interface.
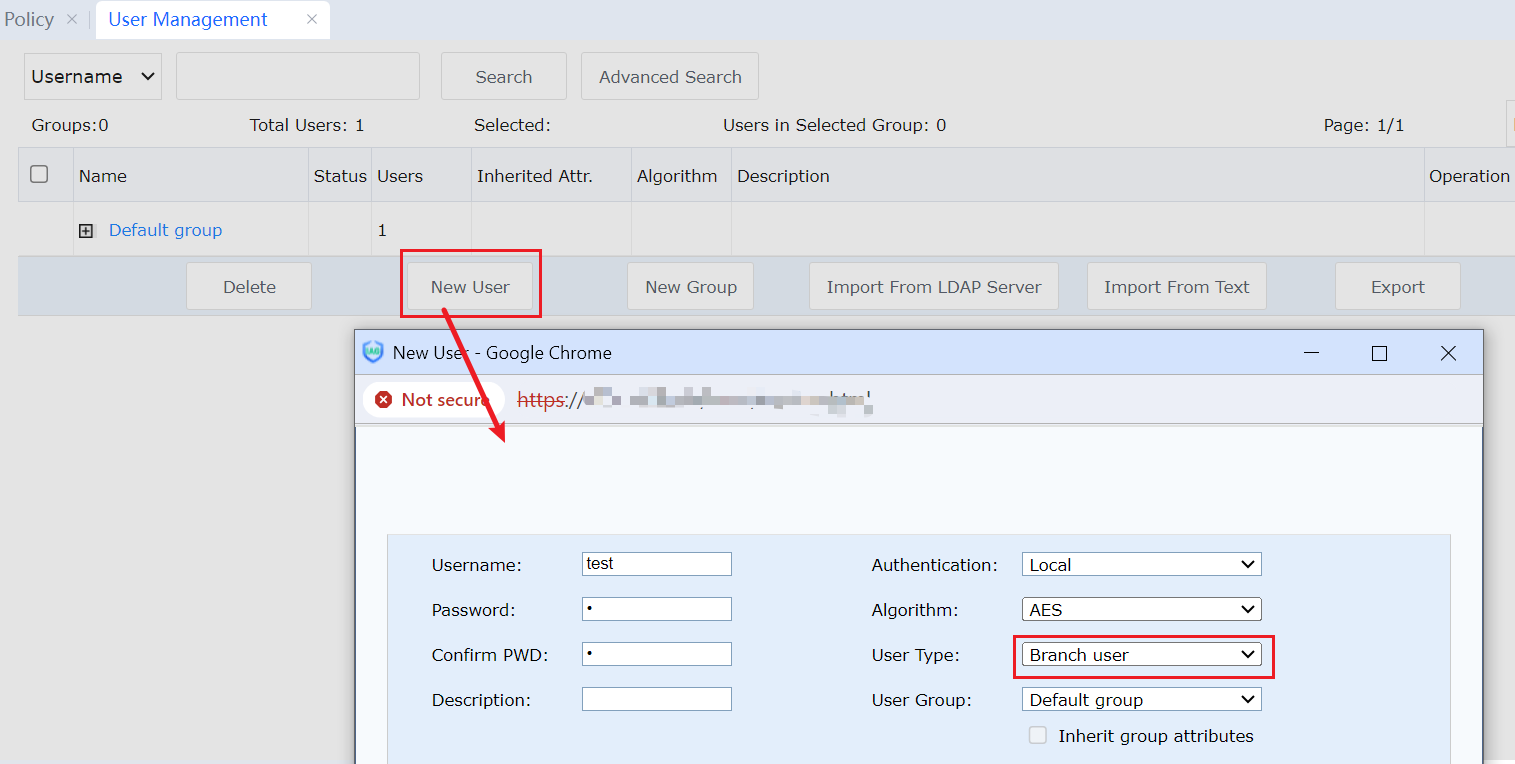
Confirm whether the VPN device in the headquarters is our VPN device or a third-party VPN device. If it is our VPN device, the headquarters should create a VPN account in advance for the connection of the branch VPN; if it is a third-party device, we should know the parameters related to connection from stage 1 to stage 2 of the third-party VPN.
Expected Result:
When the leased line and VPN are connected, the branch preferentially goes through the leased line to access the applications in the headquarters and switches to the VPN line when the leased line is disconnected.
Configuration Method:
Configuration of VPN branch IAG.
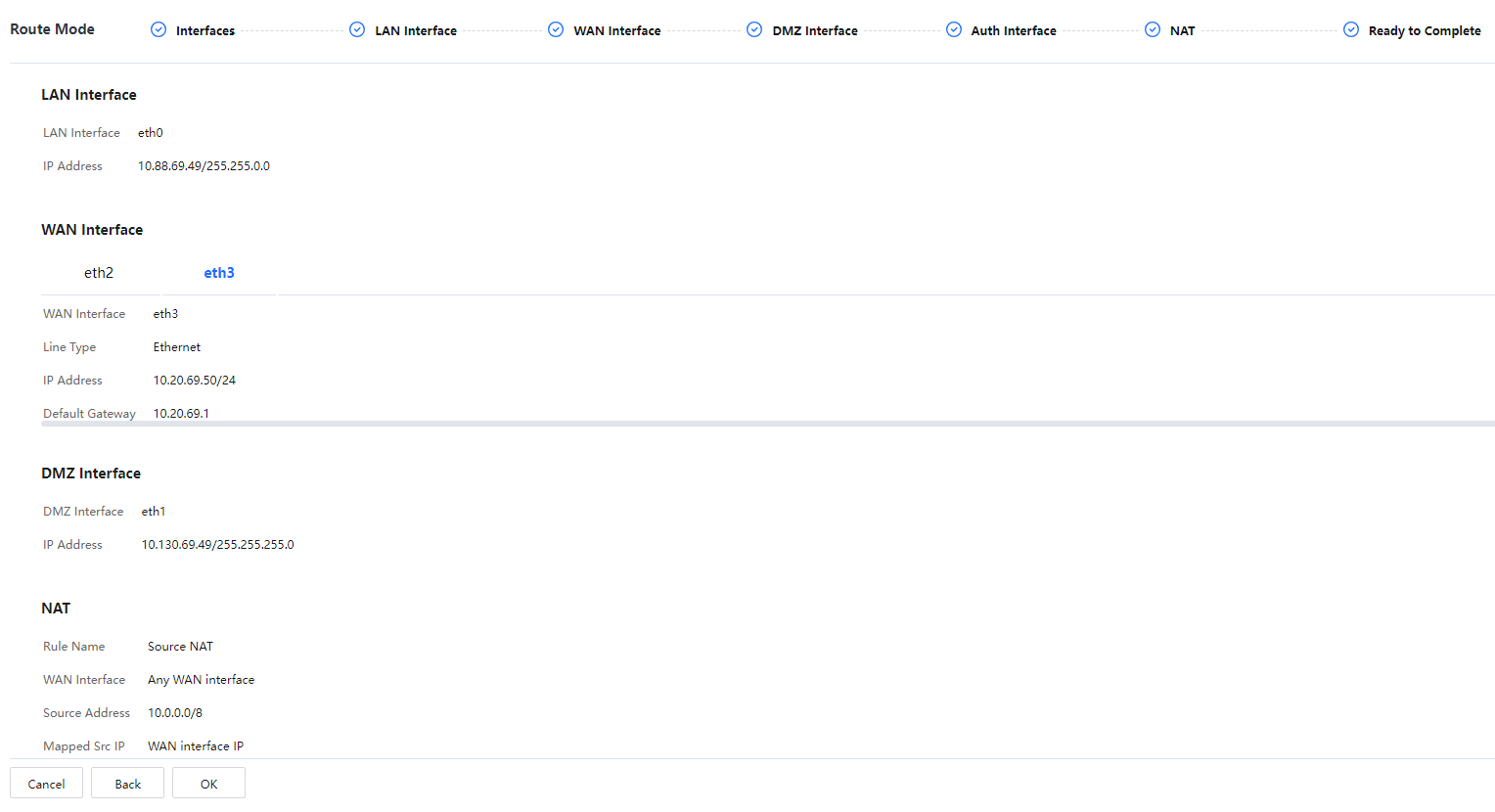
Configuration of deployment mode: Configure the deployment mode as the route mode, and configure LAN and WAN interfaces and IP addresses of two LAN and WAN lines.
Configuration of static route: If the branch LAN is a three-tier environment, a return route gateway of LAN also needs to be added to direct to a three-layer switch of LAN. The static route is not required because the LAN is a two-tier environment in this environment.
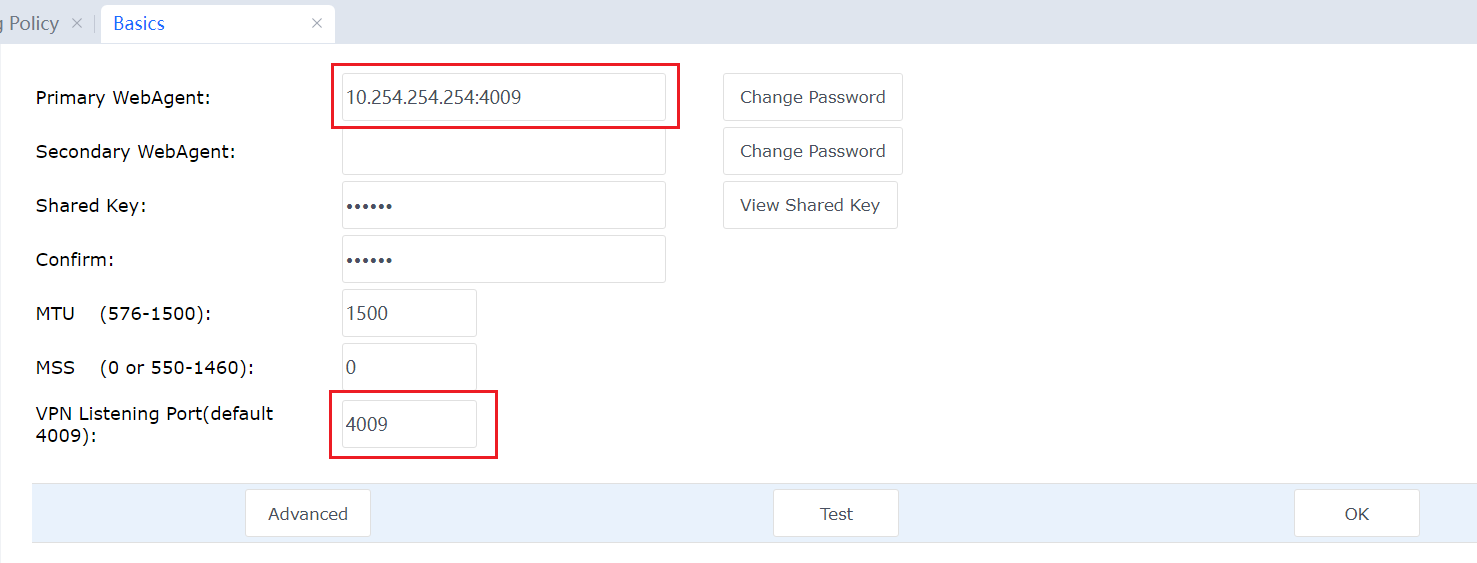
VPN configuration: Configure VPN Connections to connect the VPN device in the headquarters.
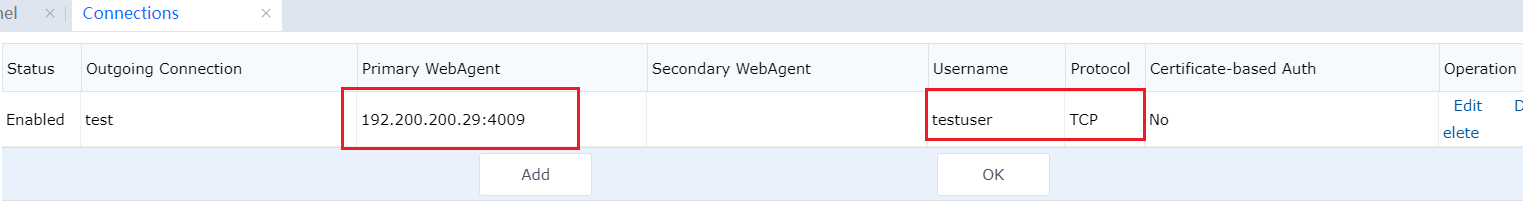
After the configuration is complete, the VPN connection is successful. Then you can see the VPN connection is successful. The network segment of the headquarters LAN route directs to the VPNTUN port.
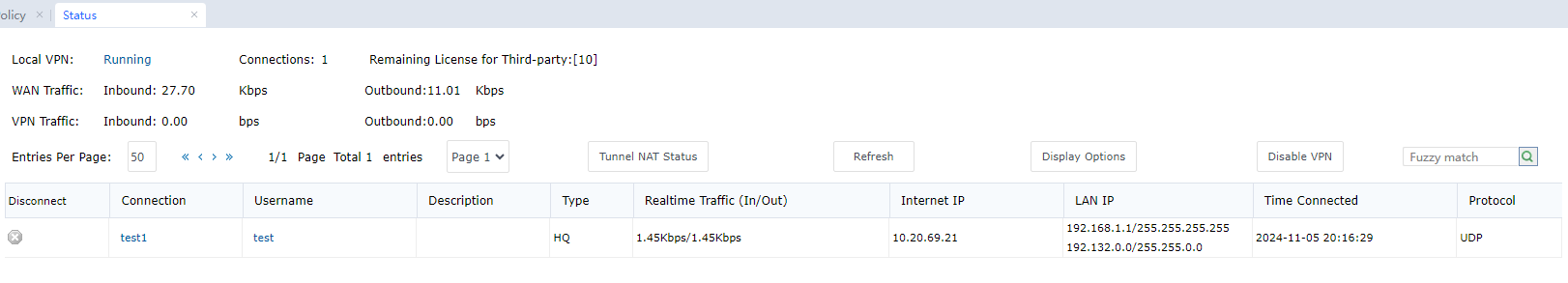 [A144]
[A144]

A third-party VPN device is also supported by the headquarters. However, the third-party connection shall be configured for VPN configuration. Moreover, if the headquarters' VPN device or network is to support the leased line for the branch LAN's access to headquarters applications, the return from the headquarters to the branch LAN should use the leased line. If the branch LAN accesses headquarters' applications via the VPN, the return should use the VPN.
Link Load Configuration
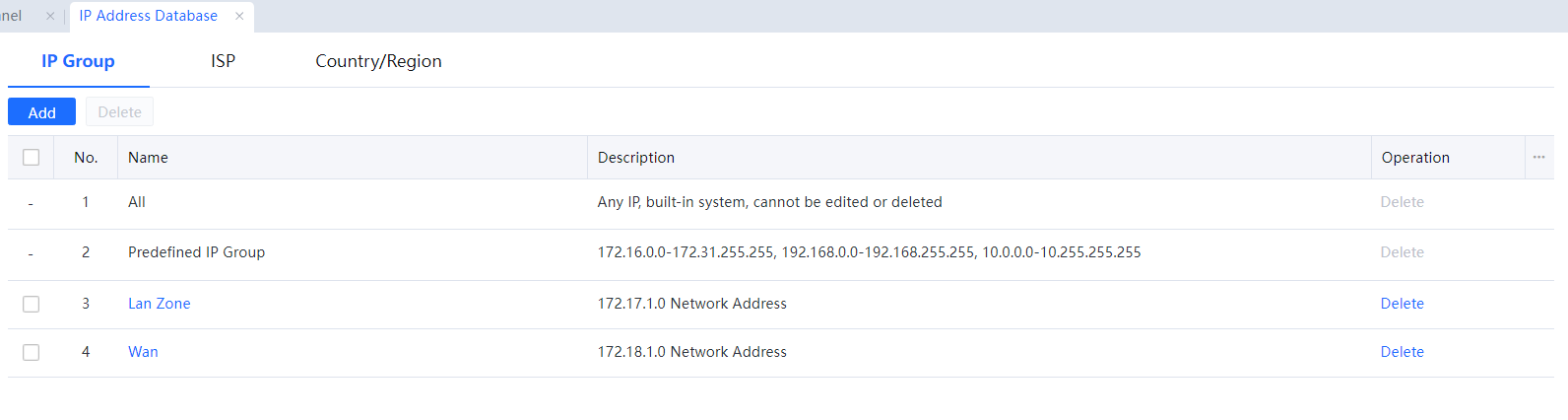
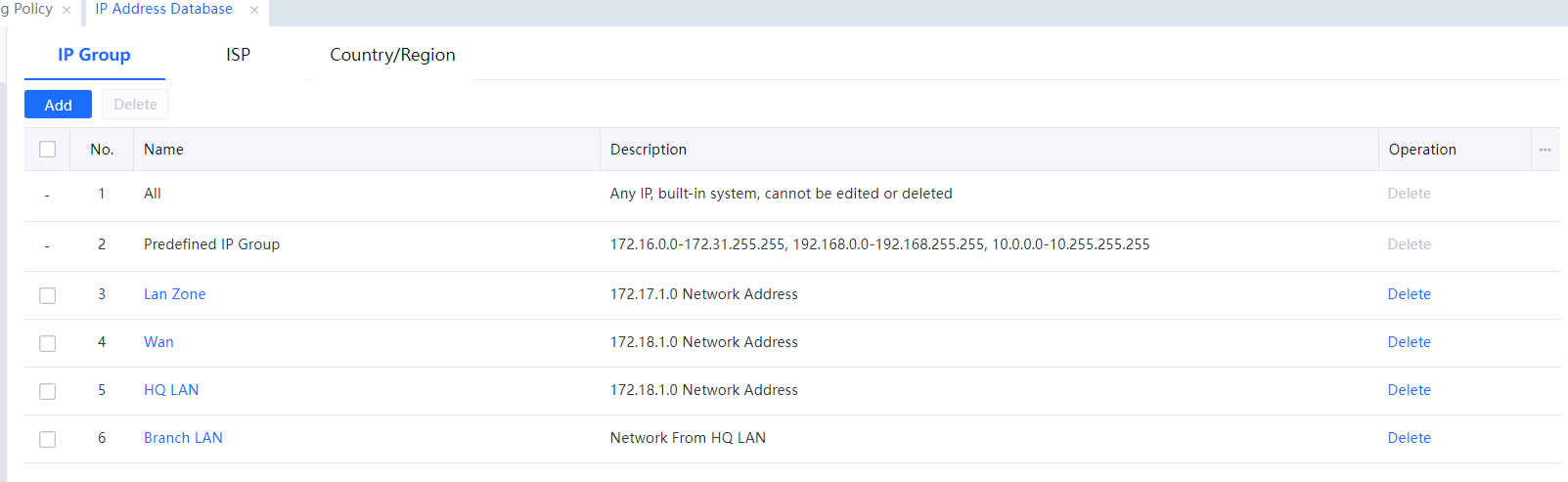
- Configure the IP groups in the LAN and headquarters for branch IAG.
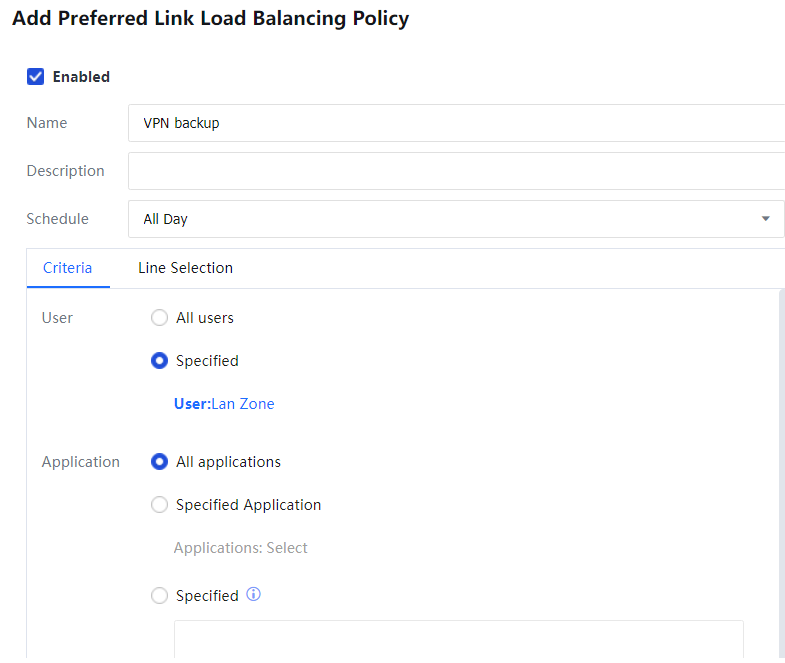
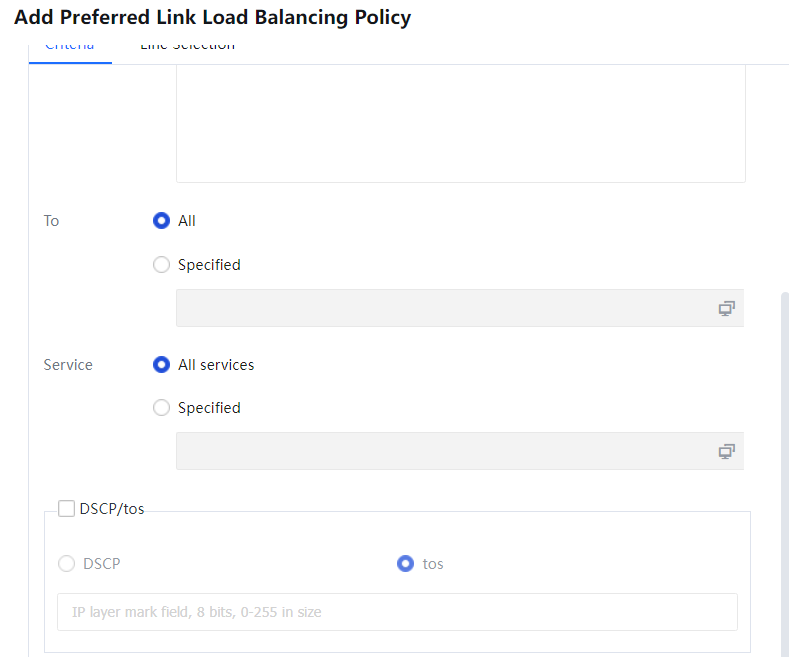
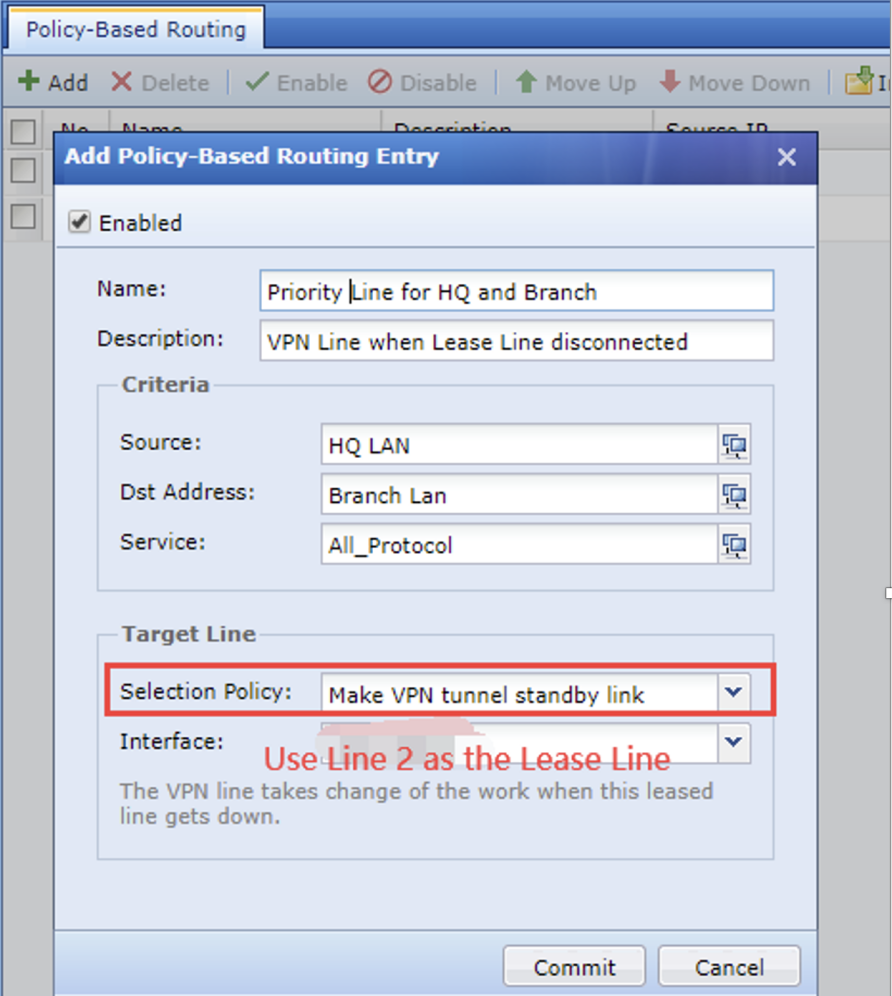
- In Link Load, go to Bandwidth Management > Load Balancing Policy > Preferred Link Load Balancing Policy, and click Add[A145] to add a new multi-line load routing as the backup for the VPN leased line.
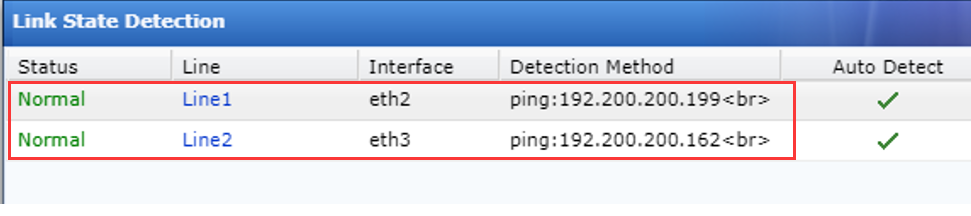
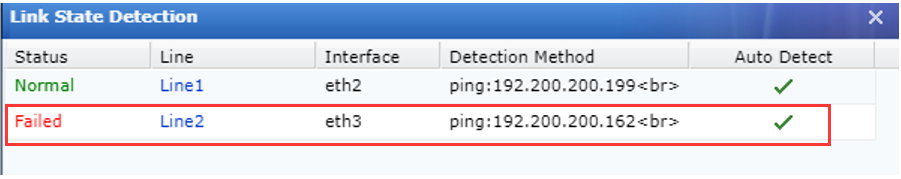
- In Link Load, perform link failure detection for the two WAN lines.
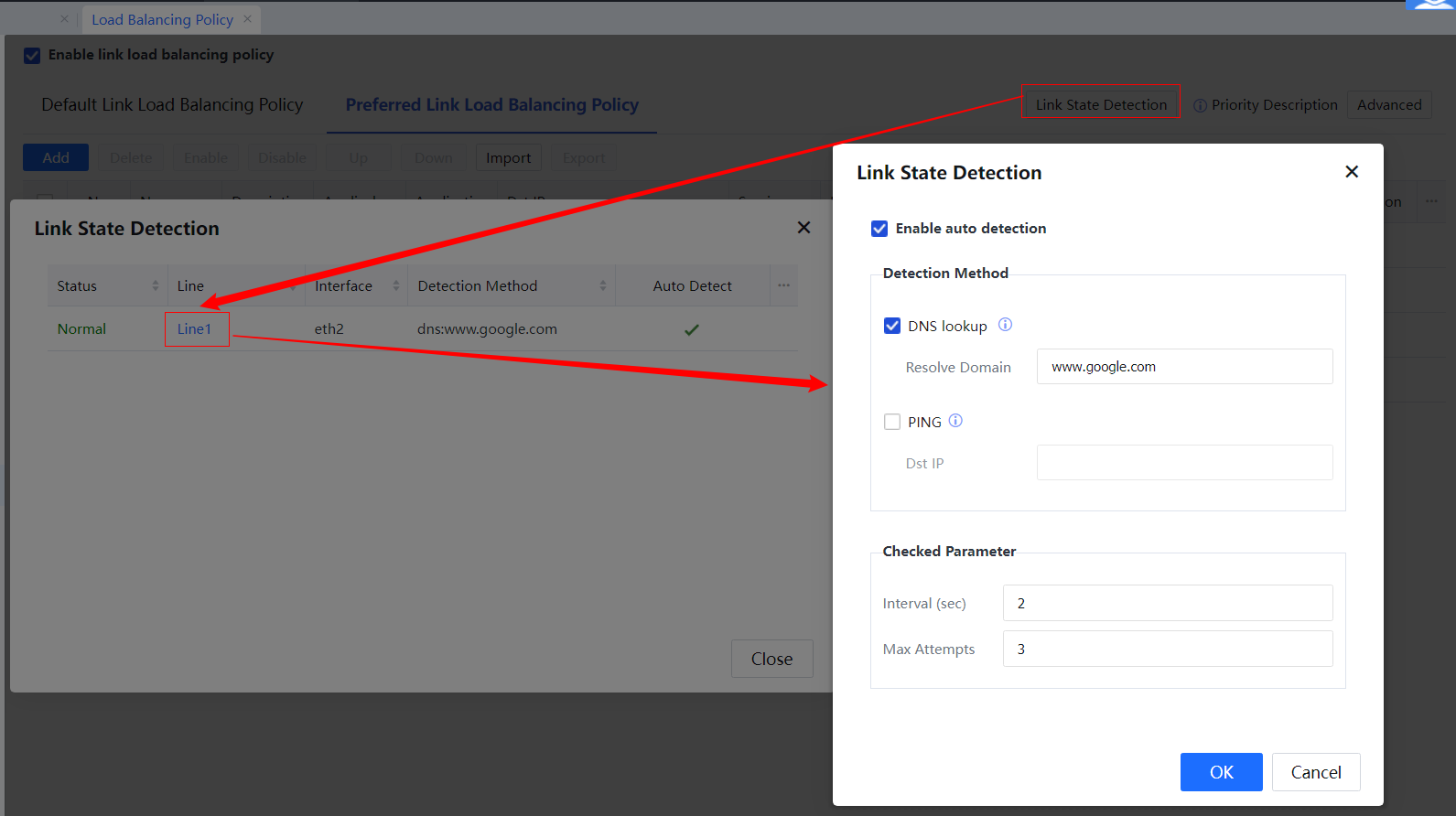

Regarding link failure detection, two link status detection options are available: DNS resolution and ping command.
Disconnection detected by either the ping command or DNS server means the line is disconnected.
You can enter multiple addresses for the ping or DNS server, and if anyone from these addresses is successfully connected, the line can be connected.
Auto Detect indicates whether automatic detection is enabled. If not, the network is deemed connected as long as the networking interface has power.
Screenshots of the VPN configuration in the headquarters
Generally, the VPN in headquarters is pre-installed, and route deployment and settings are already configured in advance.
Check deployment mode. The deployment mode is configured with the gateway mode and two WAN lines. Line 2 is a leased line connected to branch IAG.
- Static route: The IAG LAN is a two-tier environment without static routes.
- VPN configuration: Configure the addresses and ports for monitoring the server with the headquarters VPN and create an account.
Link Load Configuration:
• Define IP groups.
• Configure the multi-line Load routing.
 [A146][147]
[A146][147]

1. The headquarters device can be a Sangfor or third-party VPN device. The private branch line can connect to the headquarters via the headquarters' VPN device or other devices in the headquarters LAN. However, the headquarters should ensure that the return from the headquarters uses the leased line if the branch LAN data access headquarters applications via the leased line, and the same goes for VPN. The headquarters should have relevant Link Load Balancing or routing rules configured.
2. Headquarters accessing branch LAN can use the leased line preferentially and, if disconnected, use the VPN line after the routing policy is configured at the headquarters.
Testing
- Normally, the IAG LAN tests applications in the headquarters LAN via the leased line, and there should not be traffic on the IAG VPN.
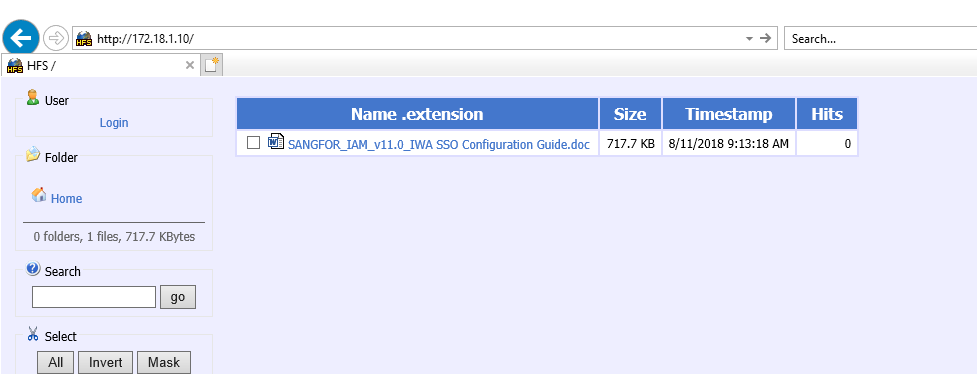
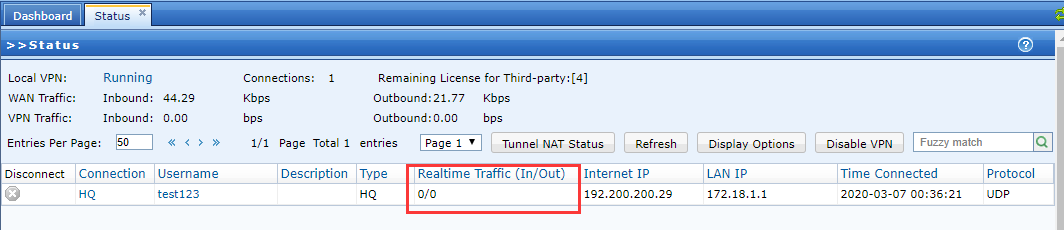
- Unplug the leased line for the WAN line on the eth1 port, and the data should switch to the VPN. Data can be found on the VPN.
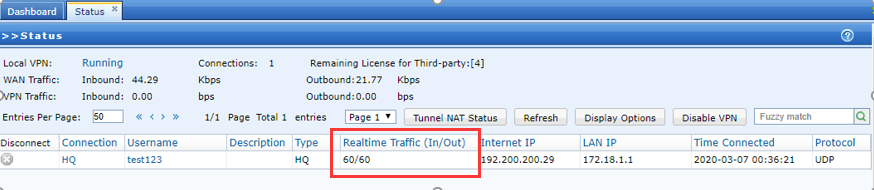

Distinct applications for unplugging-and-switch testing are recommended. For example, test http://172.18.1.10 when the leased line is in normal status and test other servers' applications when the leased line is disconnected. Disconnect the application before beginning a new test if the same application is used for the unplugging-and-switch testing.




