Add Access Control Policies
The procedure for setting an Internet access permission policy is as follows:
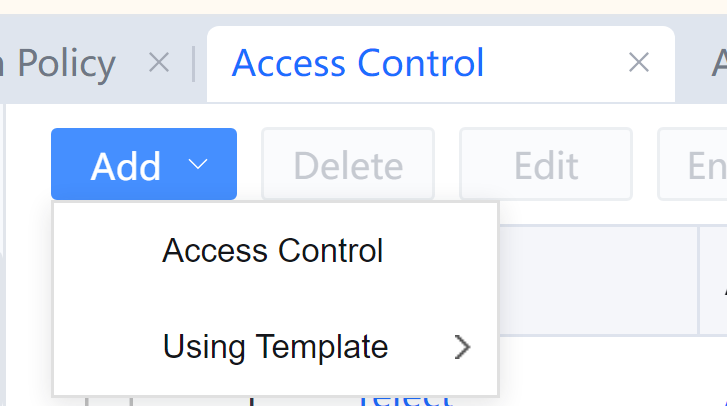
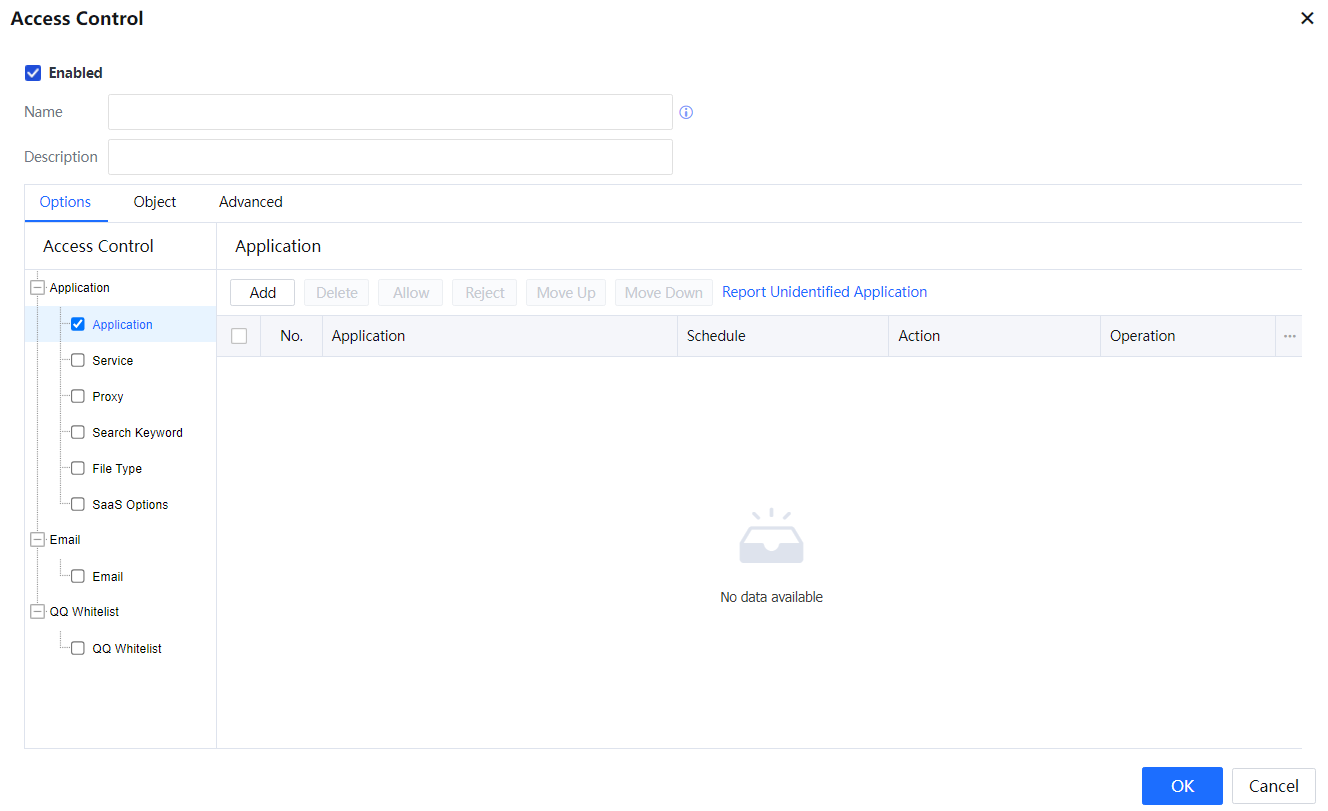
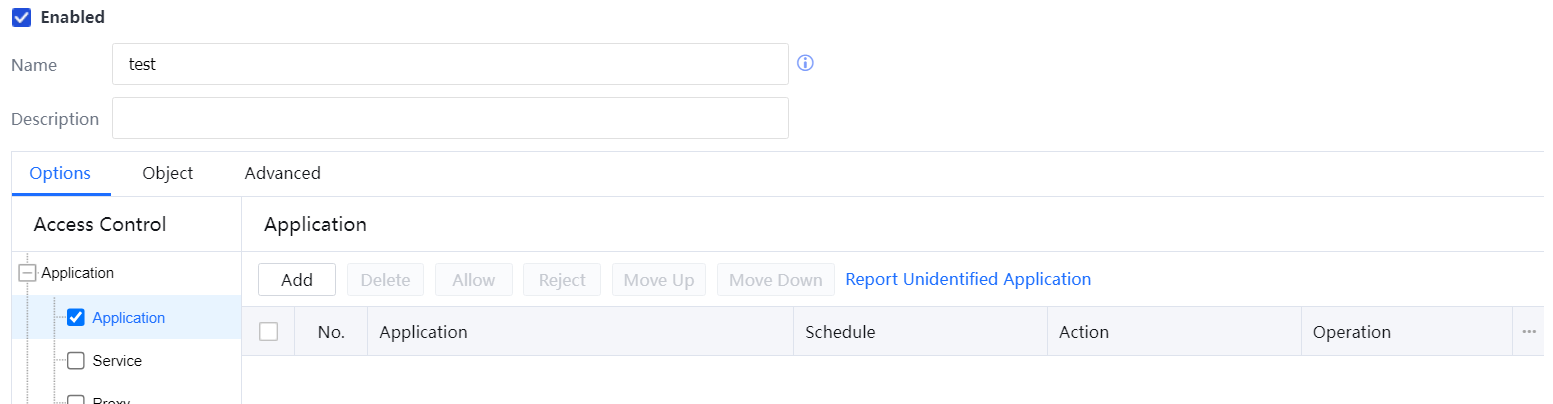
- On the Access Control page, click Add, and select Access Control.
- On the Access Control page, select Enabled. If this option is not selected, the added policy will not take effect.
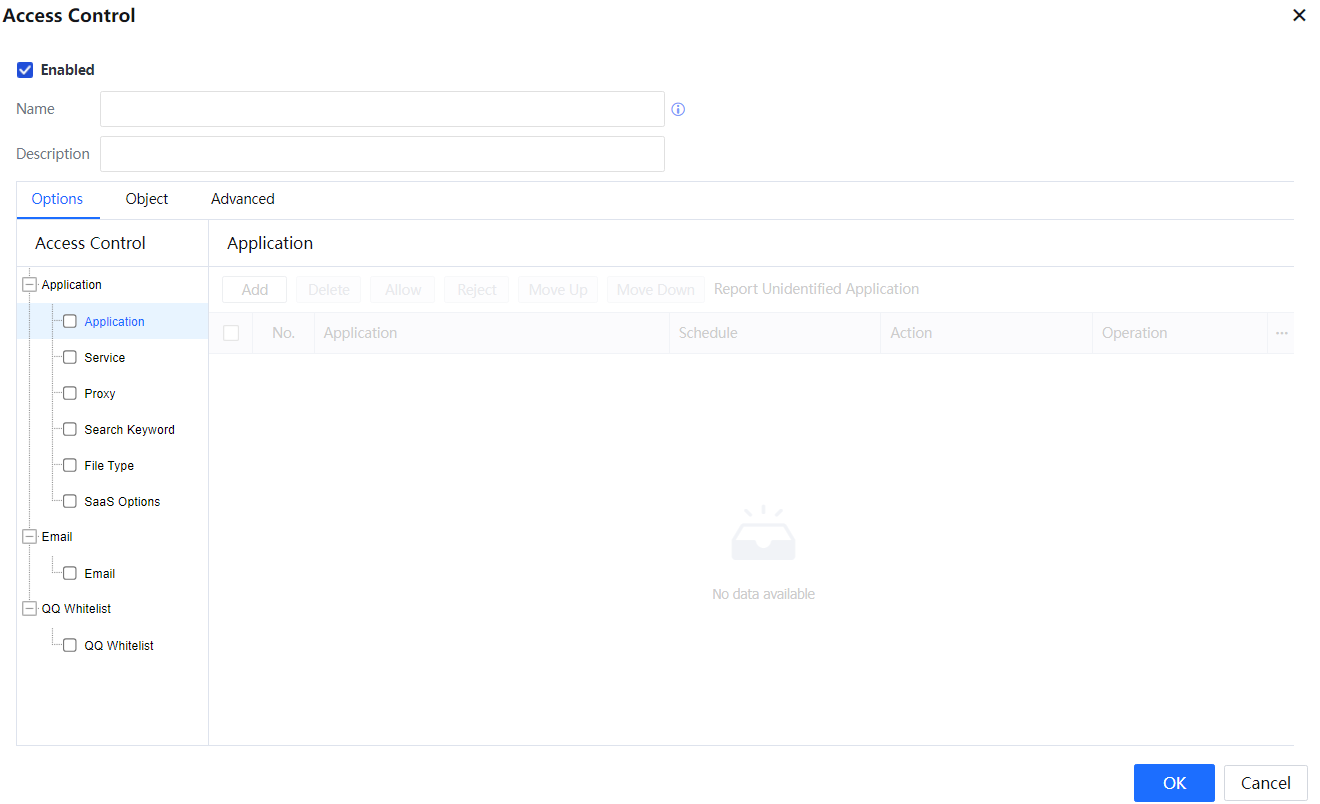
- Enter the policy name and description. The policy name uniquely identifies a policy. It is mandatory and must be unique. The description is a summary of the policy and is optional.
- On the Options tab page, set the Internet access permission policy as required. Select a control type on the Access Control pane and set details on the right pane. Access Control consists of three modules: Application, Email, and QQ Whitelist. For more information, see the following sections.
- On the Object tab page, set the applicable user, location, endpoint device, and destination for this policy.
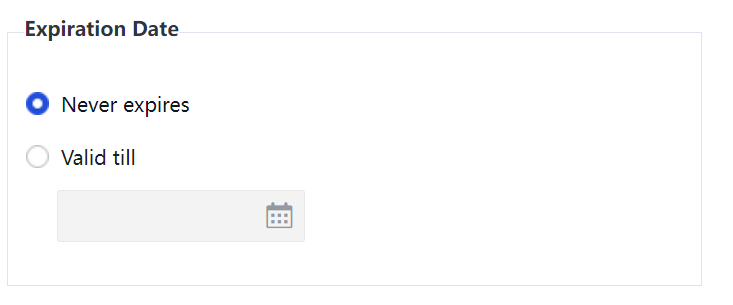
- On the Advanced tab page, set the expiry date, whether to allow other administrators of the same level to view and edit the policy, and whether to allow lower-level administrators to view the policy.
If Never expires is selected, the policy will be valid permanently. If Valid till is selected and a date is set, for example, 2016-06-01, the policy will expire after January 1, 2016.
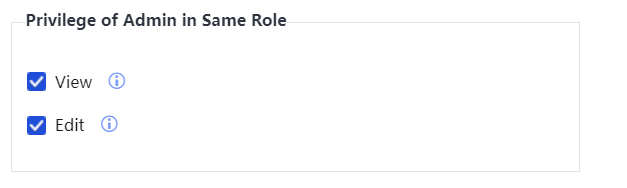
In Privilege of Admin in Same Role, set whether to allow other administrators of the same level to view and edit the policy. If two administrators are of the same role on the page displayed after you choose System > General > Administrator, they are of the same level. If only View is selected, another administrator of the same level can view this policy but cannot edit it. If Edit is selected, another administrator of the same level can view and edit this policy by default. The jurisdiction scope of this administrator must be the same or wider.
If Give view privilege to administrator in lower-level role is selected, a lower-level administrator can view this policy but cannot modify it. A lower-level administrator refers to an administrator whose role specified on the page displayed after you choose System > General > Administrator is lower than the administrator who creates this policy.
- Click OK[A79].
3.6.1.5.1.1 Access Control
3.6.1.5.1.2 Application
A. Application
The IAG has an application rule library set for all types of common network applications and a URL Database set for websites. The Application module references these rules to implement permission control on network applications and websites.
The Application module can detect packet contents to control applications. You need to set control policies for identified and unidentified applications, such as P2P applications, QQ, and mail applications.
The Application module can also filter website access behaviors, including HTTP URL filtering, HTTPS URL filtering, and HTTP uploading filtering.
The following introduces the procedures for configuring Access Control based on application types and configuring HTTP URL filtering.
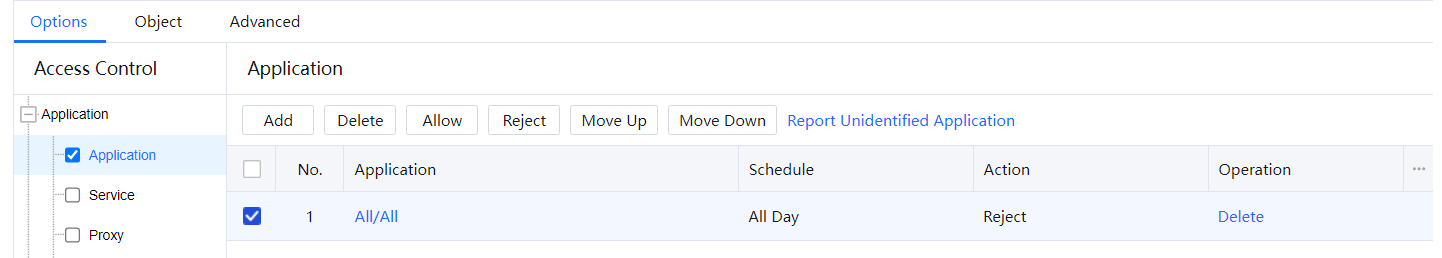
i. Control based on application types
The following is a configuration example of rejecting P2P applications.
- Select Application. Click Add and choose Application. Click
 under Application. The Application Signature, Advanced Application Signature, custom applications, and schedule groups are referenced.[LCH80][81]
under Application. The Application Signature, Advanced Application Signature, custom applications, and schedule groups are referenced.[LCH80][81]
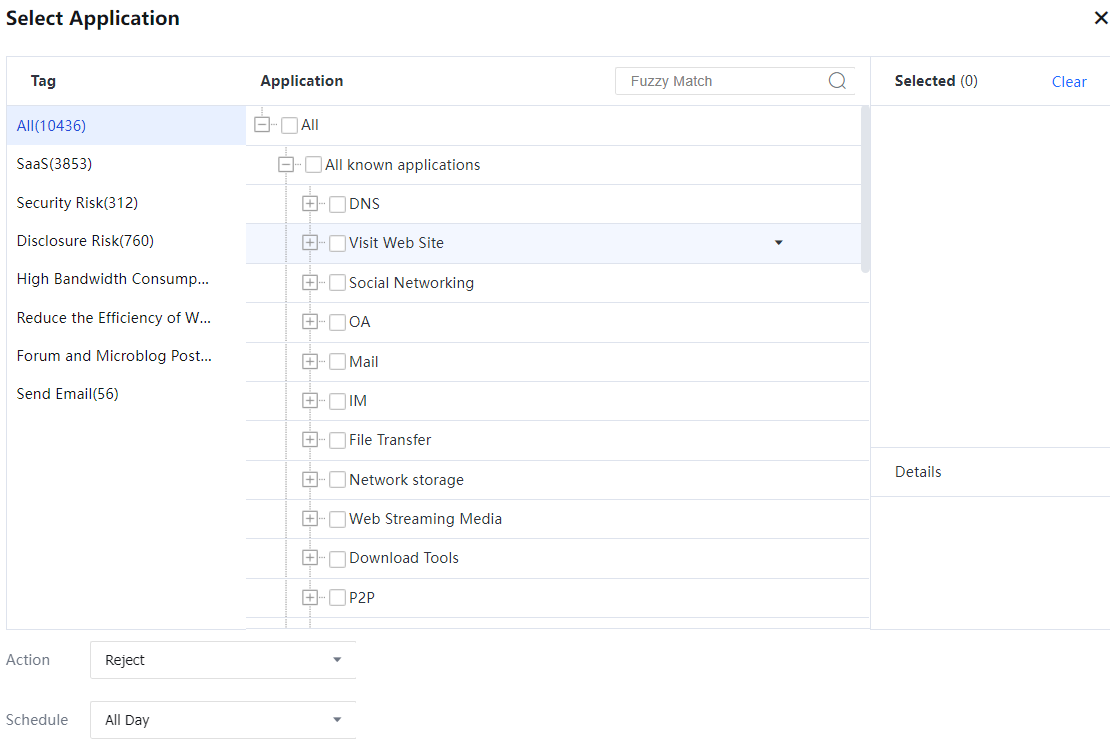
- On the Select Application page, select P2P.
- Set Action to Reject, Schedule to All Day, and click OK. The policy for rejecting P2P applications is set successfully.
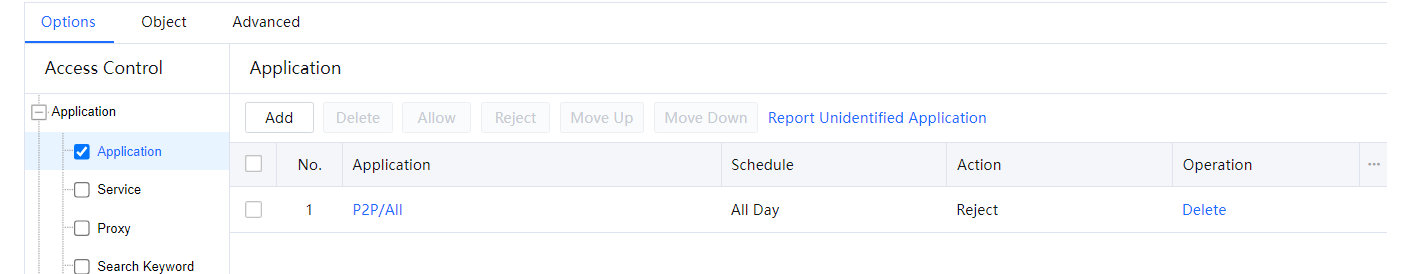
- To modify the Access Control policy, select P2P and click Delete to delete the policy. You can also select Allow in Action, or select Reject. Click Up or Down to change the priority of the policy. Policies are matched from top to bottom.
- If only Access Control is required, click OK. If other policies need to be edited, continue with the procedure.

By default, the IAG allows access to applications for which no control policy is set.
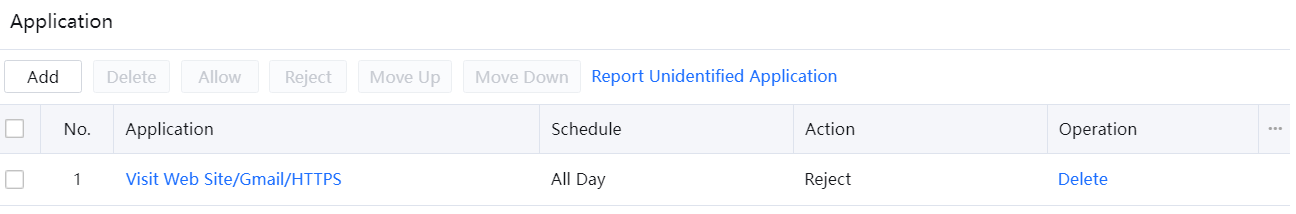
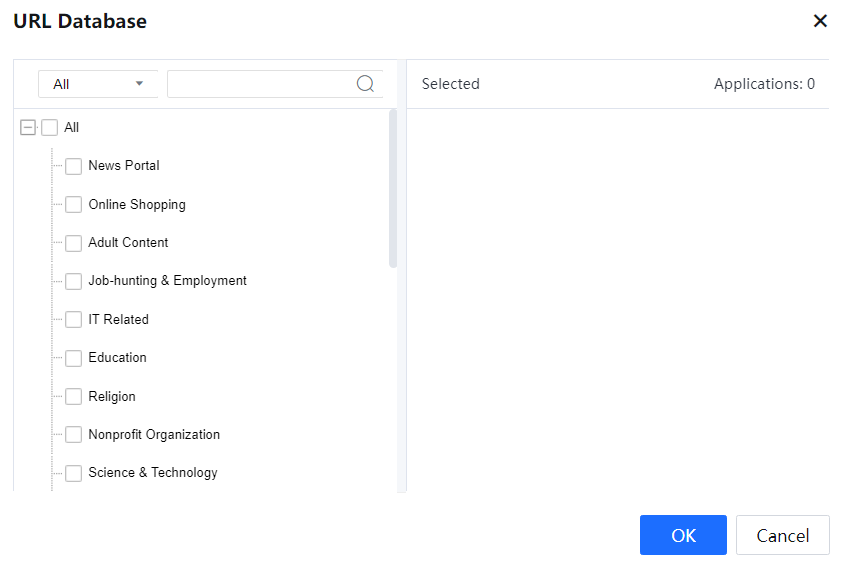
ii. HTTP URL filtering
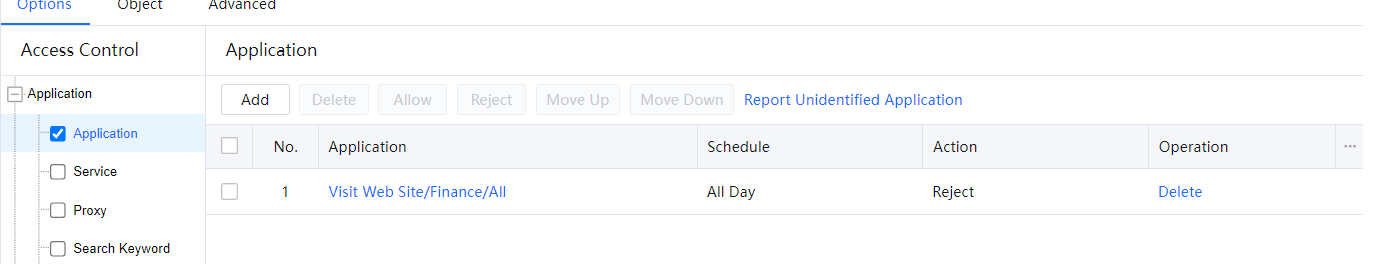
Configure the IAG to control website access behaviors by detecting the URLs of visited websites. Example: Set a policy to prevent users from accessing e-banks and bank websites during working hours.
- Select Application and click Add.
- In the Select Application window, find the Visit Web Site type, and select Finance.
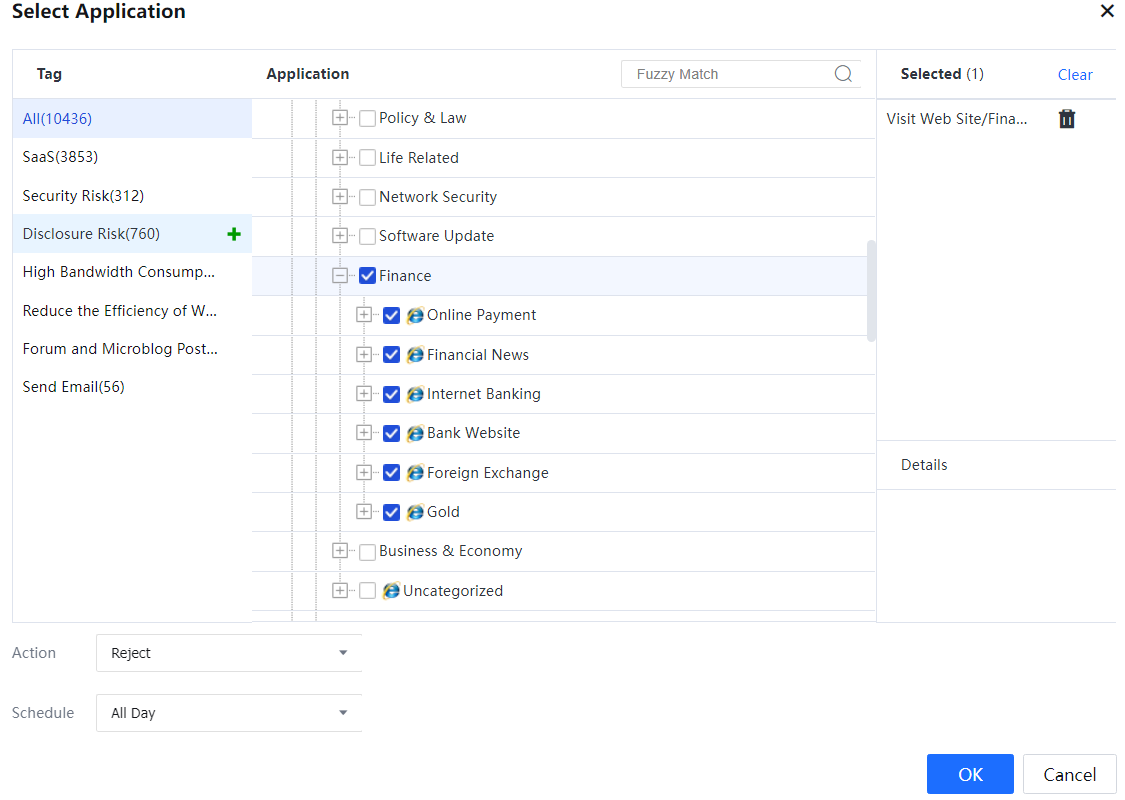
- Set Action to Reject and Schedule to All Day, and click OK. The policy is set successfully.

In control of file uploading and other uploading, the IAG filters behaviors of uploading files through HTTP POST or other contents based on URL groups.
iii. HTTPS URL filtering
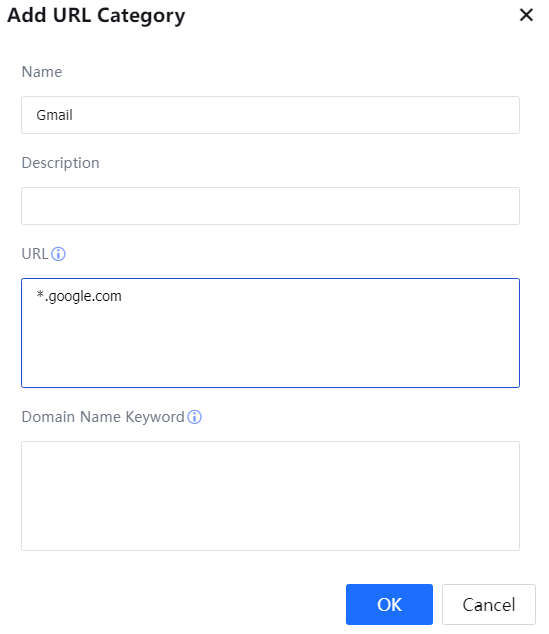
HTTPS URL filtering involves filtering websites that are visited over HTTPS. For example, you can configure a policy to prevent intranet users from accessing the encrypted website https://mail.google.com/.
The procedure for setting a policy to reject access to Gmail all day is as follows:
- In the URL Database, no URL group is specific to Gmail. Therefore, set a URL group and add the URL of Gmail before setting the policy.
- Choose System > Objects > URL Database and click Add. Enter the URL group name, description, and URL. In the URL, enter the value of Issued To in the SSL certificate issued by the website. HTTPS URLs support wildcards. Therefore, enter *.google.com.
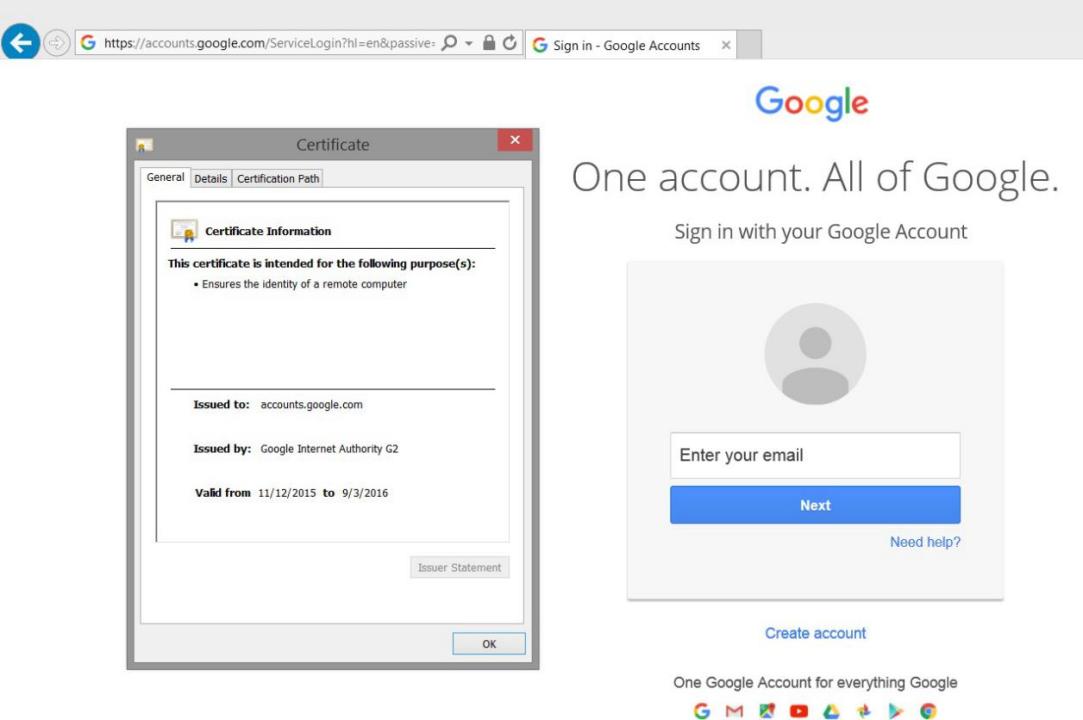
- Select Access Control. Click Add and choose Application.and click Add under Application[A82].
- In the Select Application window, find the Visit Web Site type and select HTTPS under Gmail.
- Set Action to Reject and Schedule to All Day and click OK. The policy of preventing access to Gmail all day is set successfully.

When a user visits a secure website through HTTPS, data is encrypted, and the IAG cannot detect the URL. Generally, the URL of a secure website is the same as the address specified in Issued To of an SSL certificate. Therefore, the IAG can detect this value in the SSL certificate to obtain the URL of the visited security website. To define the URL of an HTTPS website, set the URL based on the value of Issued To in the certificate issued by the website.
B.Service
Port control is performed based on the destination IP address and port of packets, and the time segment. For example, you can set a policy to block access from the intranet to port 80 of an IP group.
The following is an example of setting a policy to reject access to ports 1000 and 1001 of the IP group
200.200.200.1-200.200.200.254 in working hours.
- Select Service. On the Service pane, click Add and set related parameters. It will refer to the IP groups, network services, and schedule groups defined earlier.
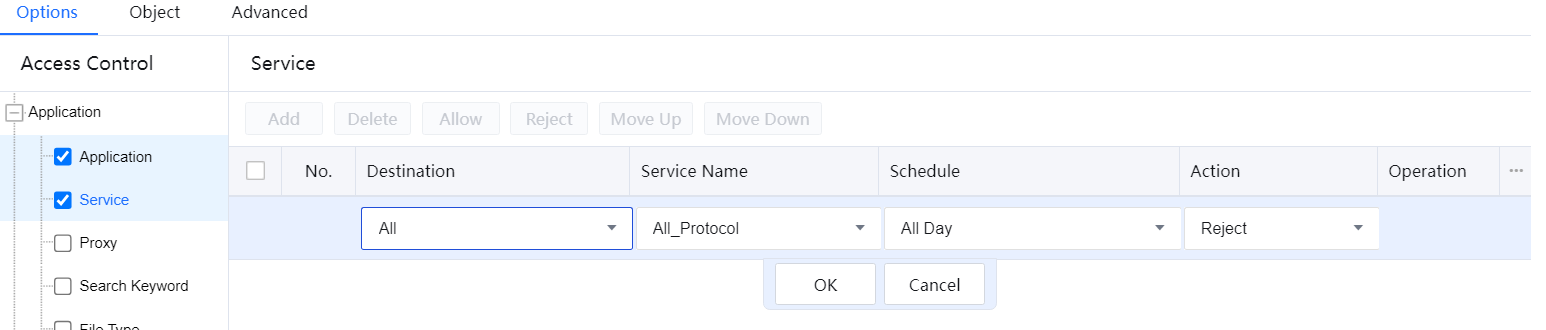
- Select a target IP group from the drop-down list. If the required IP group does not exist, click Add IP Group at the bottom of the drop-down list to create it. Click OK.
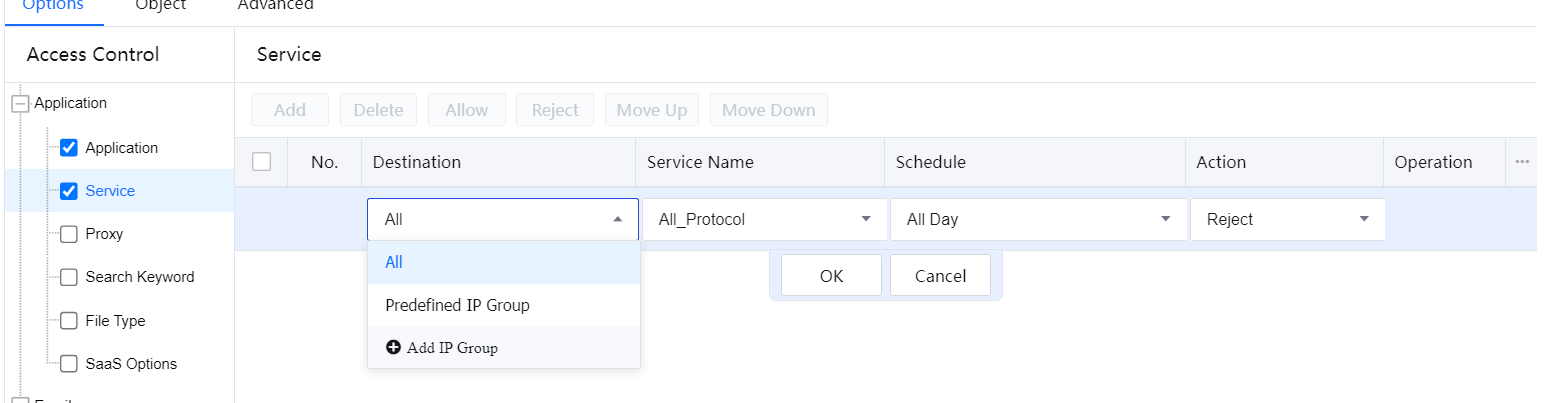
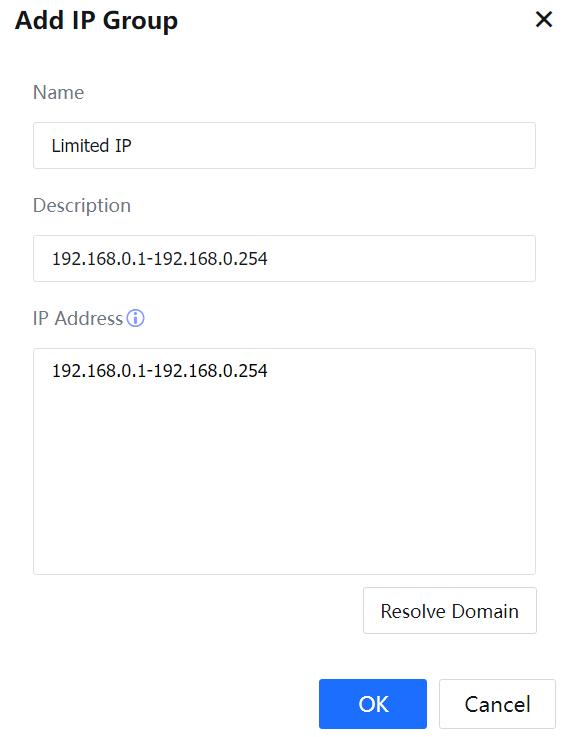
- Add IP Group: This item is linked to the page displayed after you choose Objects > IP Group. Enter the IP group name, description, and IP address in the Edit IP Group dialog box, and click OK[A83].
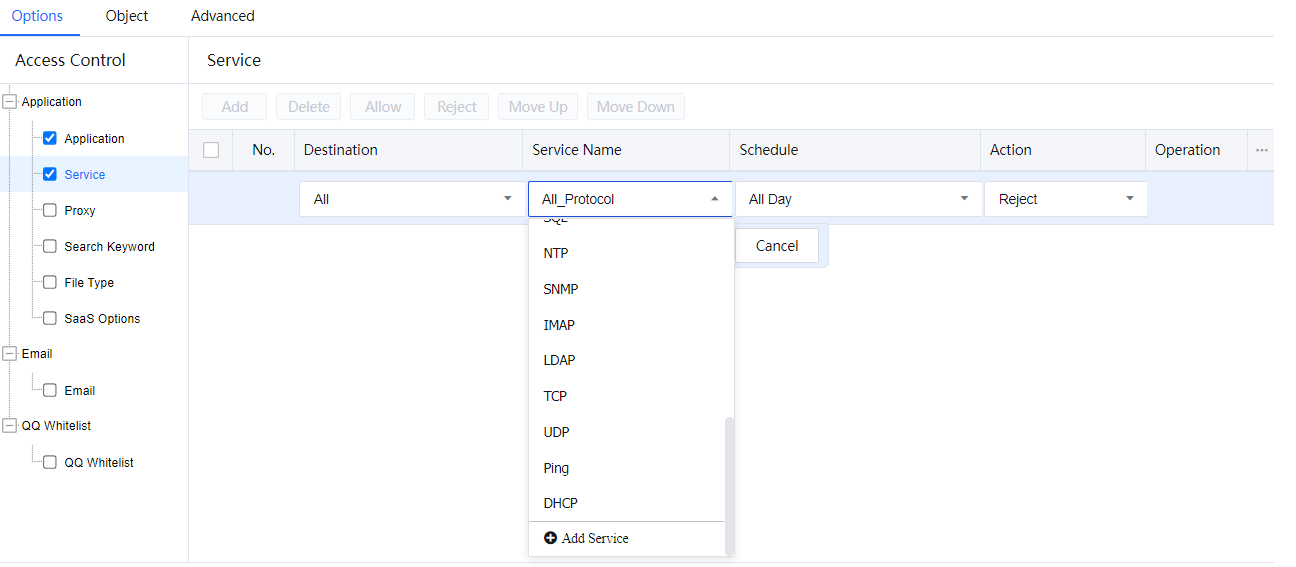
- Select a service from the drop-down list. If the required service does not exist, select Add Service at the bottom of the drop-down list to create it. Click OK[A84].
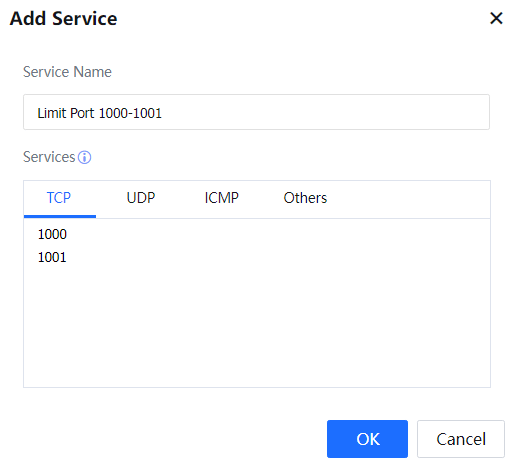
- Add Service: This item is linked to the page displayed after you choose Objects > Service. In the Add Service dialog box, enter the service name and port or protocol ID, and click OK[A85].
- Set Action to Reject and Schedule to All Day and click OK.
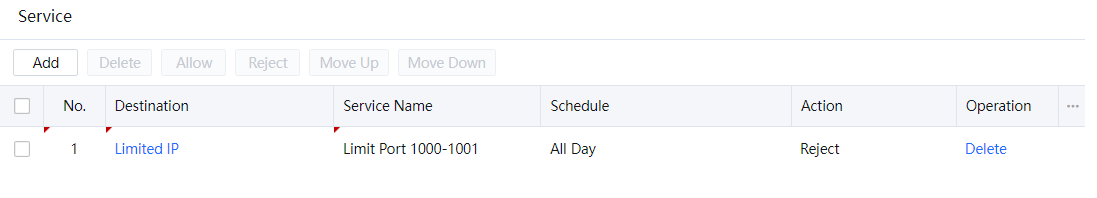
- To modify the port control policy, select the corresponding network service and click Delete to delete the policy. You can also select Allow in Action or select Reject. Click Move Up or Move Down to change the priority of the policy. The policies are matched from top to bottom.
- If only port control is required, click OK. If other policies need to be edited, continue with the same procedure.

By default, the IAG allows access to network services for which no control policy is set.
C.Proxy
Proxy control involves controlling behaviors of using HTTP and SOCK proxies and using other protocols on a standard HTTP or SSL port. See the following figure.
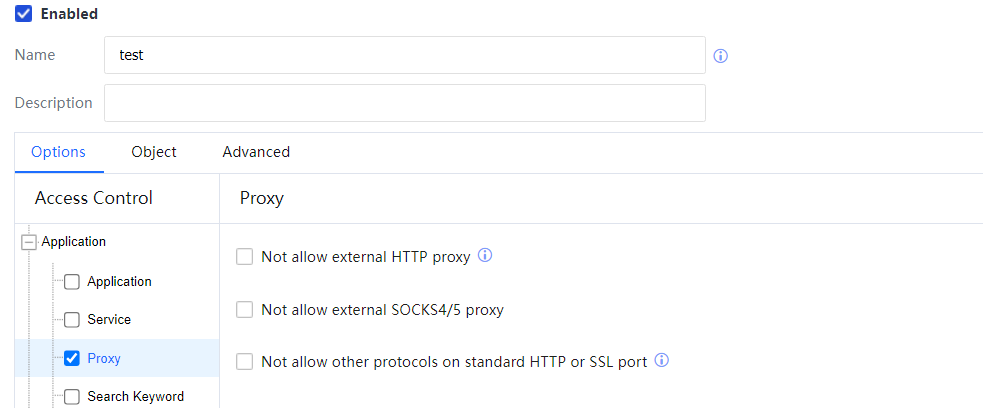
If Not allow external HTTP proxy is selected, the IAG will reject the requests sent by intranet users to access the Internet using an external HTTP proxy server.
If Not allow external SOCK4/5 proxy is selected, the IAG will reject the requests sent by intranet users to access the Internet using a SOCK proxy.
After Not allow other protocols on standard HTTP or SSL port is selected, if identified/unidentified software conducts communication over a well-known port (TCP 80 or TCP 443), and the communication contents are in private protocol format, the IAG will reject the communication information.
D.Search Keyword
Web keyword filtering comprises two parts: search keyword filtering and HTTP uploading filtering. The IAG filters or generates alarms when detecting specified search keywords in search keyword filtering. For example, the IAG can control behaviors of searching keywords by using search engines such as Baidu and Google. In HTTP uploading filtering, the IAG rejects access requests or sends an alarm mail when detecting keywords uploaded over HTTP. For example, the IAG can filter access requests or generate an alarm for keywords in posts on forums or the QQ Zone. Set Action to Give alert. When the uploaded contents include the specified keyword, the IAG will send an alarm mail to the specified mailbox.
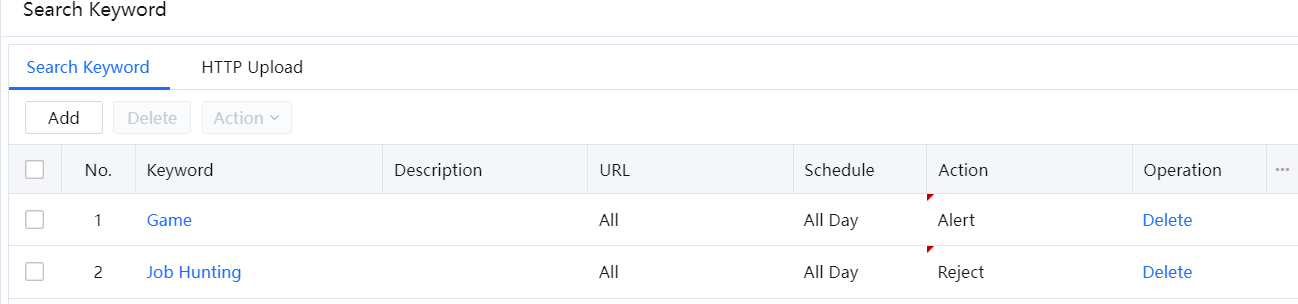
Example: Set a policy to reject search requests with the keyword Job Hunting and allow search requests with the keyword Game all day. When detecting search requests with the keyword Game, the IAG sends an alarm mail to example@example.com. [LCH86][87]The IAG prevents uploading data containing politically sensitive keywords through HTTP.
- Select Search Keyword. On the Search Keyword pane, click Add and set related parameters.
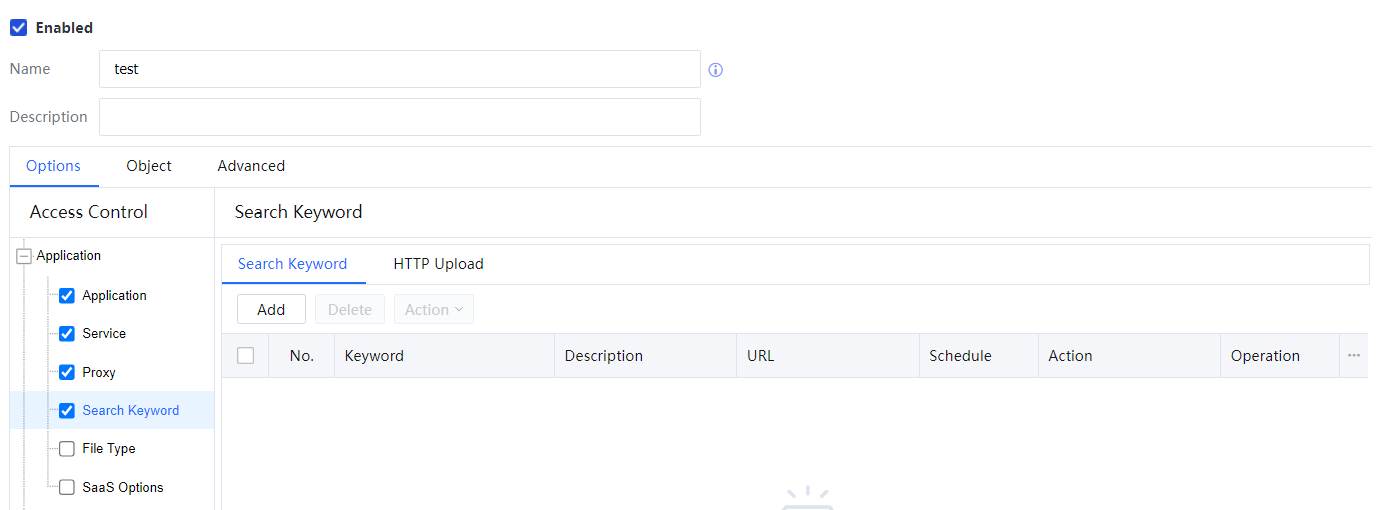
- In the Keyword drop-down list, select Job Hunting. If the required keyword is not included, select Add Keyword Group to create it.
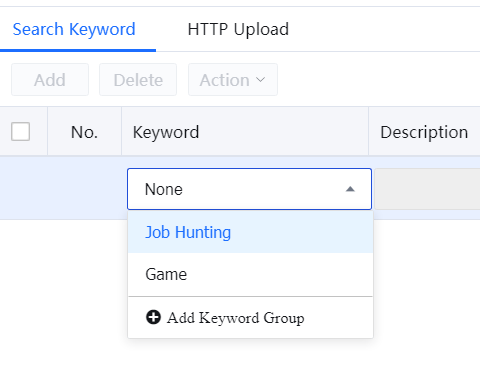
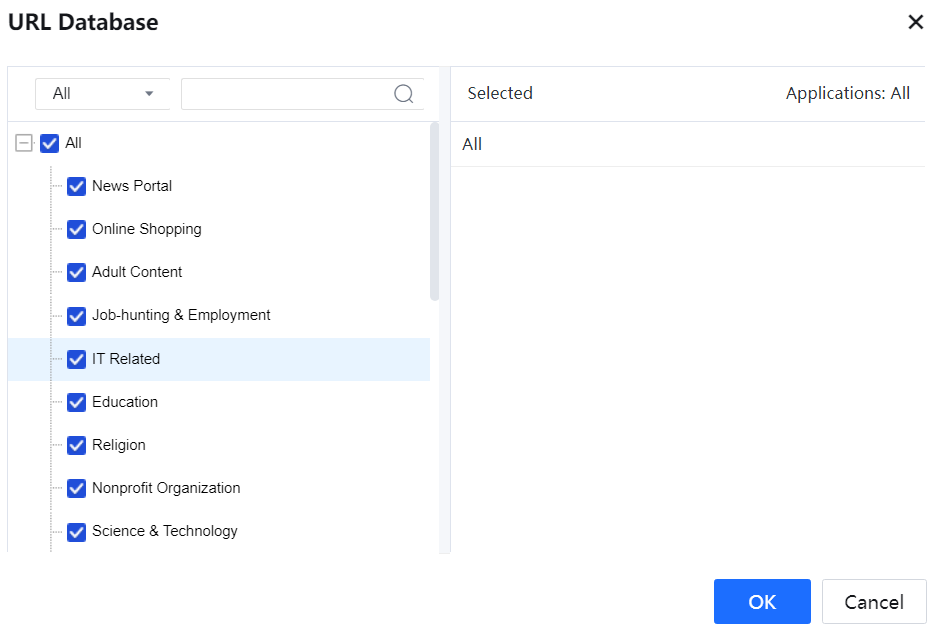
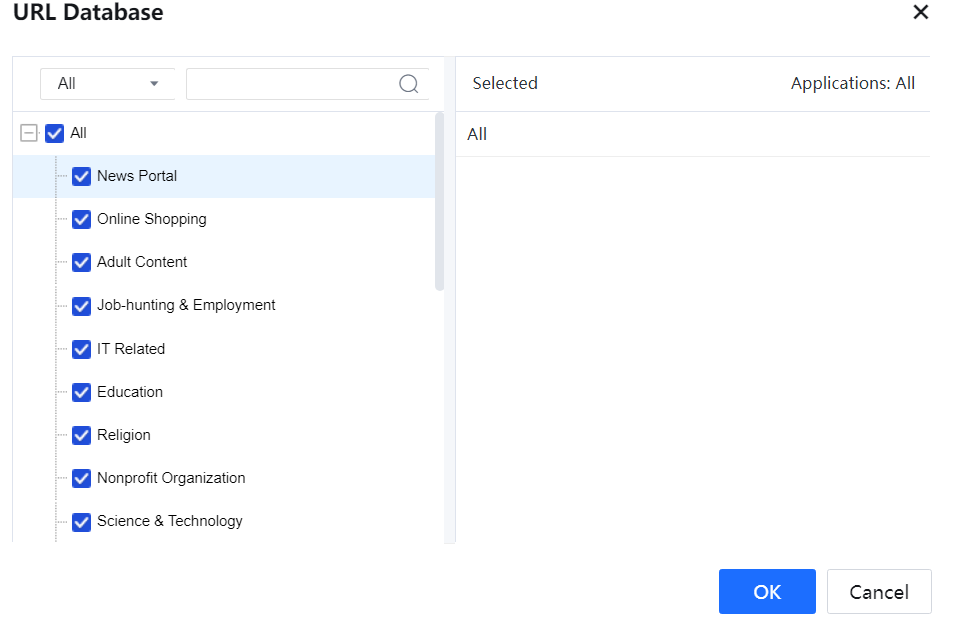
- Return to the configuration page, select all URL types, and click OK.
- Set Action to Reject and Schedule to All Day, and click OK. The policy of rejecting search requests for the keyword Job Hunting all day is set successfully. Repeat steps 1 to 4 to set a policy to generate alarms for search requests for the keyword Game.
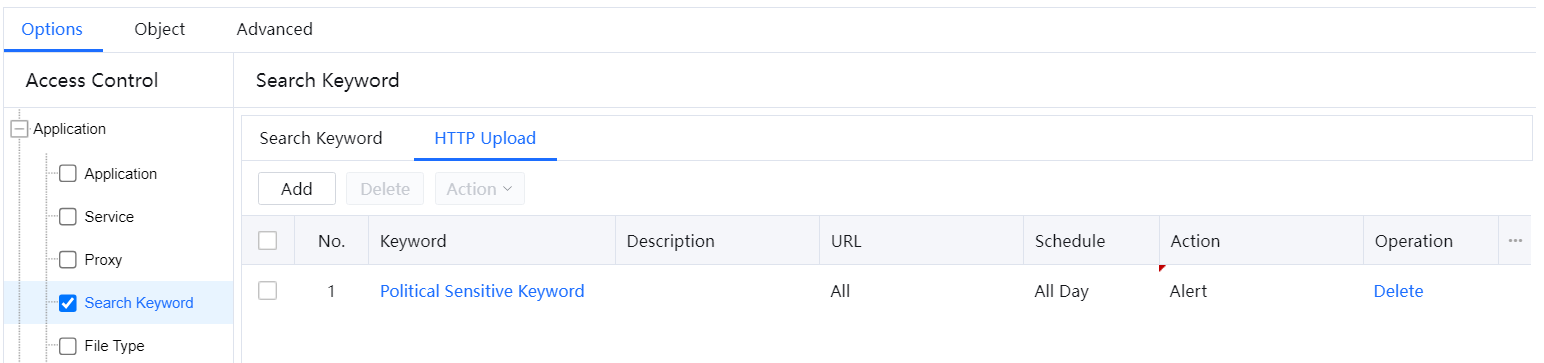
- On the HTTP Upload tab page, click Add. Click the drop-down button below Keyword to display the keyword group list.
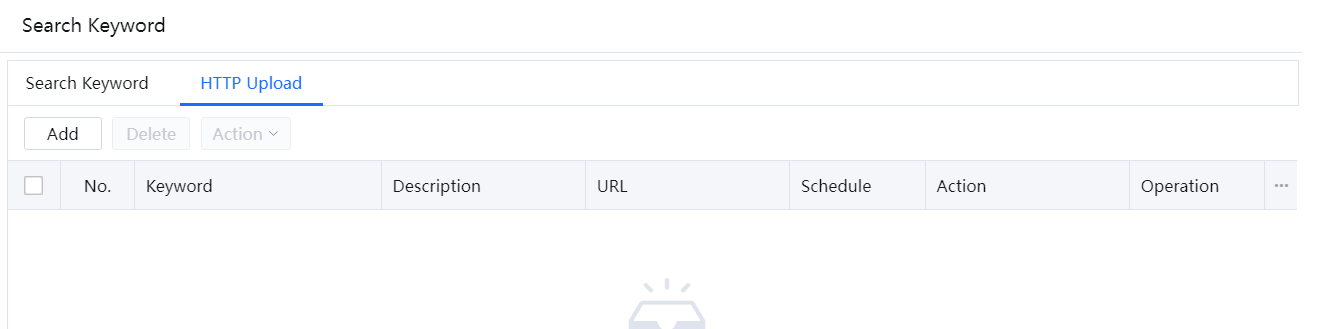
- In the Keyword drop-down list, select Political Sensitive Keyword. If the required keyword is not included, select Add Keyword Group to create it.
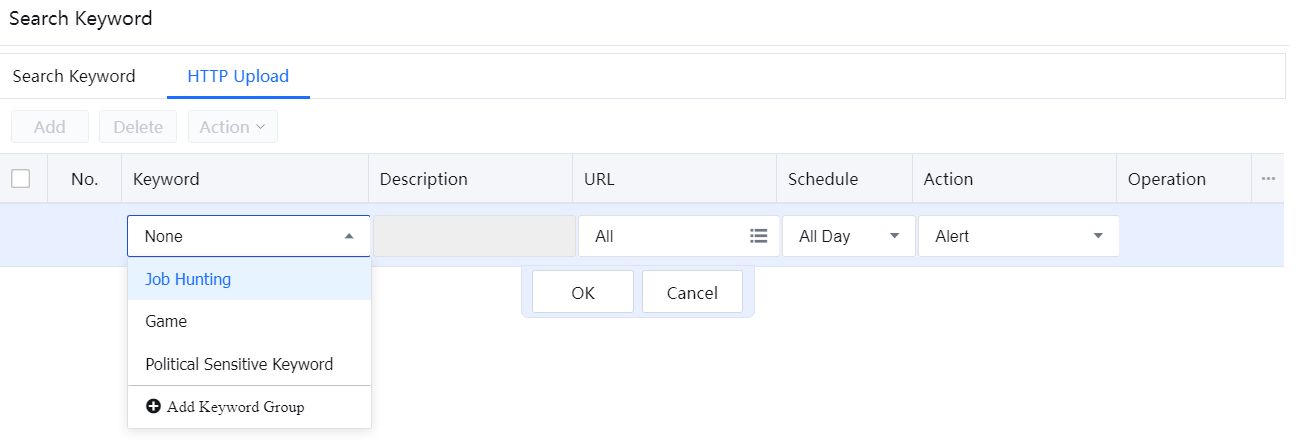
- Return to the configuration page, select all URL types, and click OK.
- Set Action to Reject and Schedule to All Day, and click OK. The policy of rejecting uploading requests with politically sensitive keywords all day is set successfully.
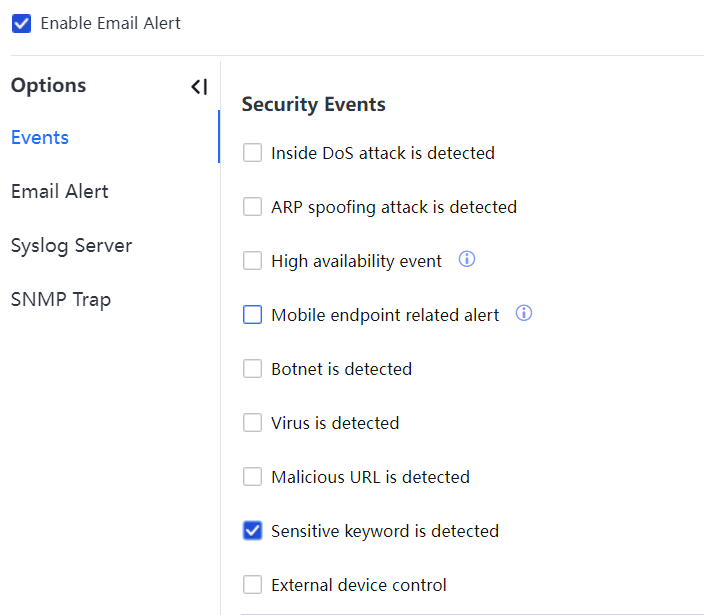
- If only keyword filtering is required, click OK. To enable Web keyword filtering alarms, choose System > General > Alert options > Events > Sensitive Keyword is detected, as shown in the following figure.
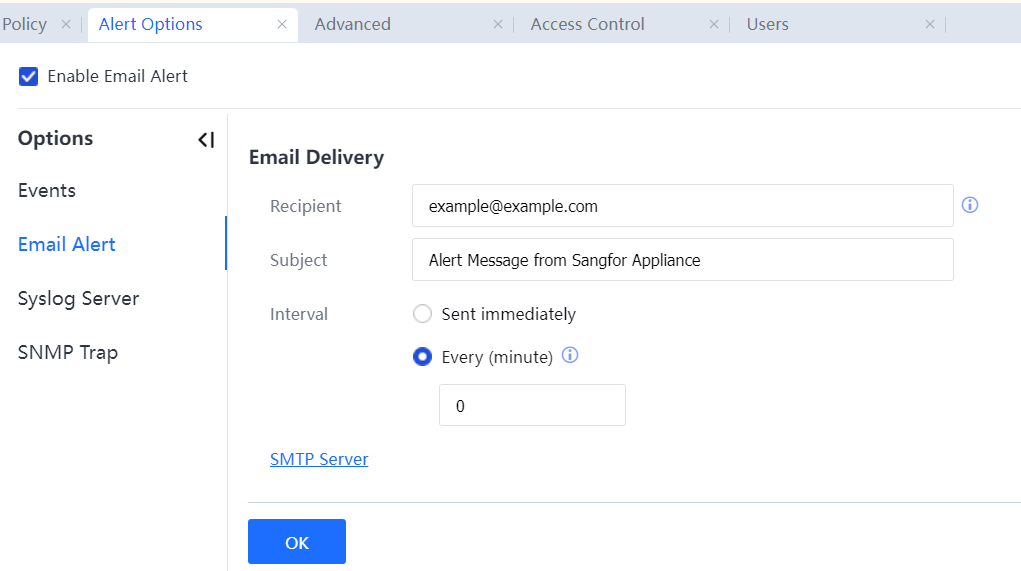
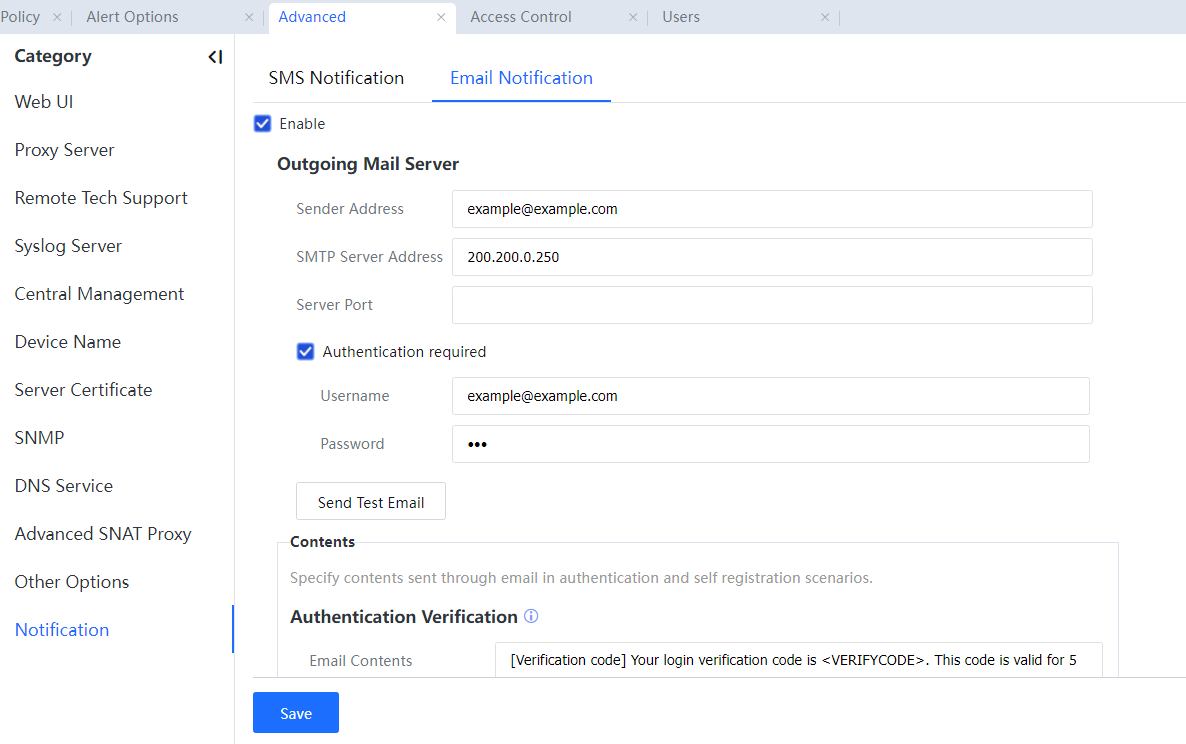
- To set the address of the mail server for sending alarm emails and the recipient mailbox, choose System > General > Alert options > Email Alert[A88] > SMTP Server.
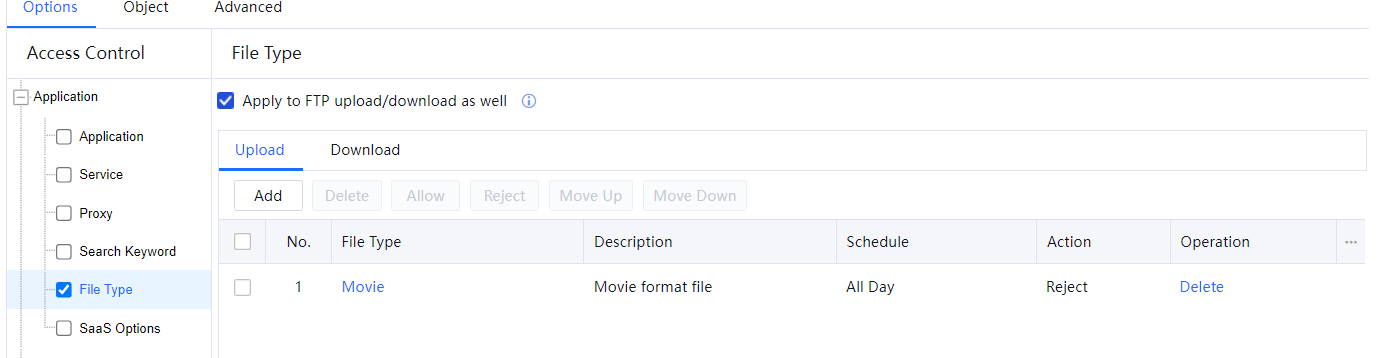
E. File Type
Web file type filtering comprises two parts: uploading and downloading. You can set the IAG to filter files uploaded or downloaded over HTTP or FTP.
The procedure for setting a policy to reject requests for downloading and uploading film files from websites or over FTP is as follows:
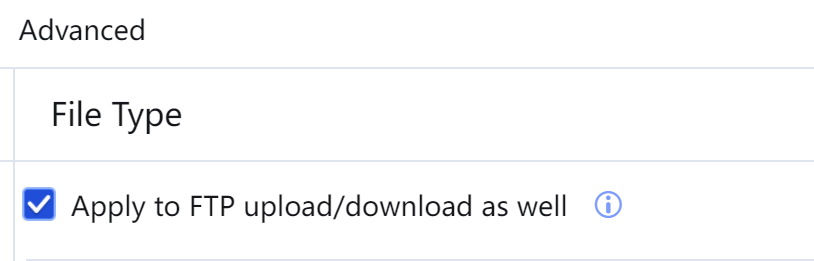
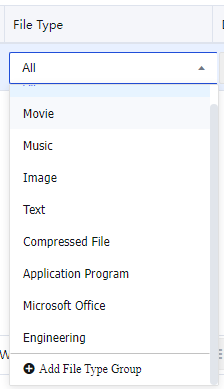
- Select File Type. On the File Type pane, click Add and set related parameters. Click the drop-down button below File Type and choose a keyword group. Select Apply to FTP upload/download as well.
- On the Upload tab page, click Add.
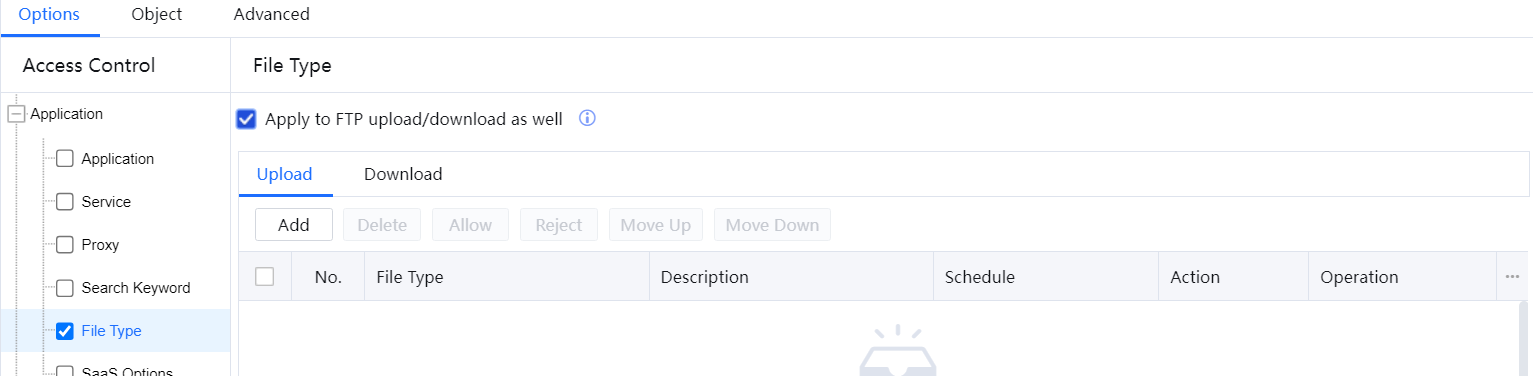
- In the File Type drop-down list, select Movie. If the required file type is not included, select Add File Type Group to create it.
- Return to the configuration page, set Action to Reject and Schedule to All Day, and click OK. The policy of rejecting requests to upload film files to websites or over FTP all day is set successfully.
- On the Download tab page, click Add.
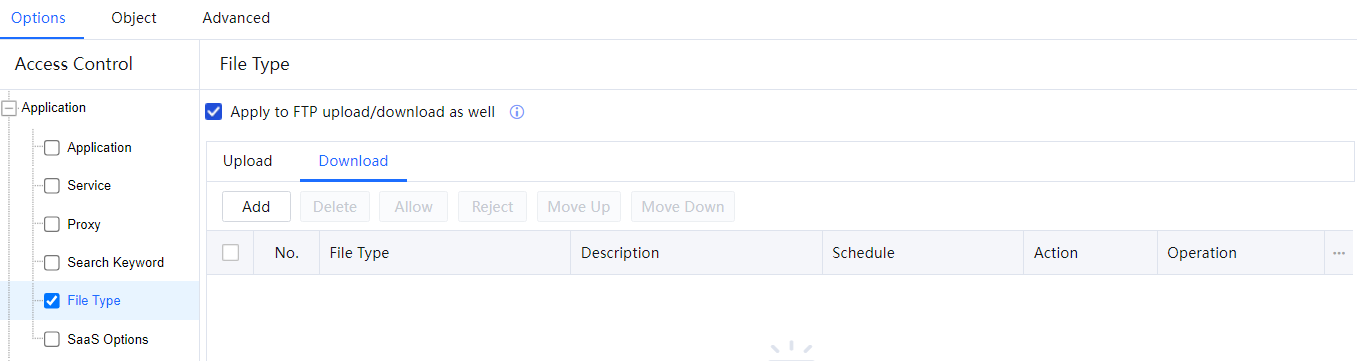
- In the Fill Type drop-down list, select Movie. If the required file type is not included, select Add File Type Group to create it.

- Return to the configuration page, set Action to Reject and Schedule to All Day, and click OK. The policy of rejecting requests to download film files from websites or over FTP all day is set successfully.
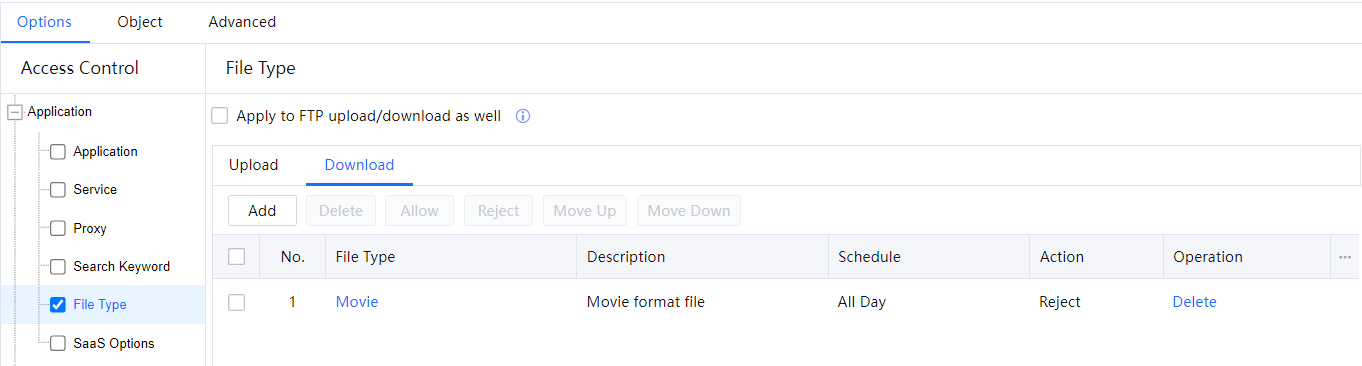
- To allow file uploading and downloading for some websites, add an exclusion URL. Select Excluded Website and select Excluded URL types.
- Click OK.
F. SaaS Options
Along with the rise of the Internet, more and more software providers offer SaaS services in the evolution process from Web 2.0 to HTML 5.0 to support the users' usage of the Internet, bringing convenience but causing the risks of Shadow IT.
Shadow IT: All applications not involving IT organizations and applications not covered by IT service management are all in the scope of Shadow IT.
Shadow IT brings in potential risks and costs. Hundreds of Cloud applications may be operated in the enterprise network, where most are shadow services. IT team does not supervise these services, which may cause significant risks and compliance issues of data for business. Therefore, handling Shadow IT becomes a problem to be solved in the aspect of enterprise information security:
• How to inspect and evaluate the usage of SaaS applications.
• How to discover and handle potential Shadow IT risks.
• How to manage SaaS applications.
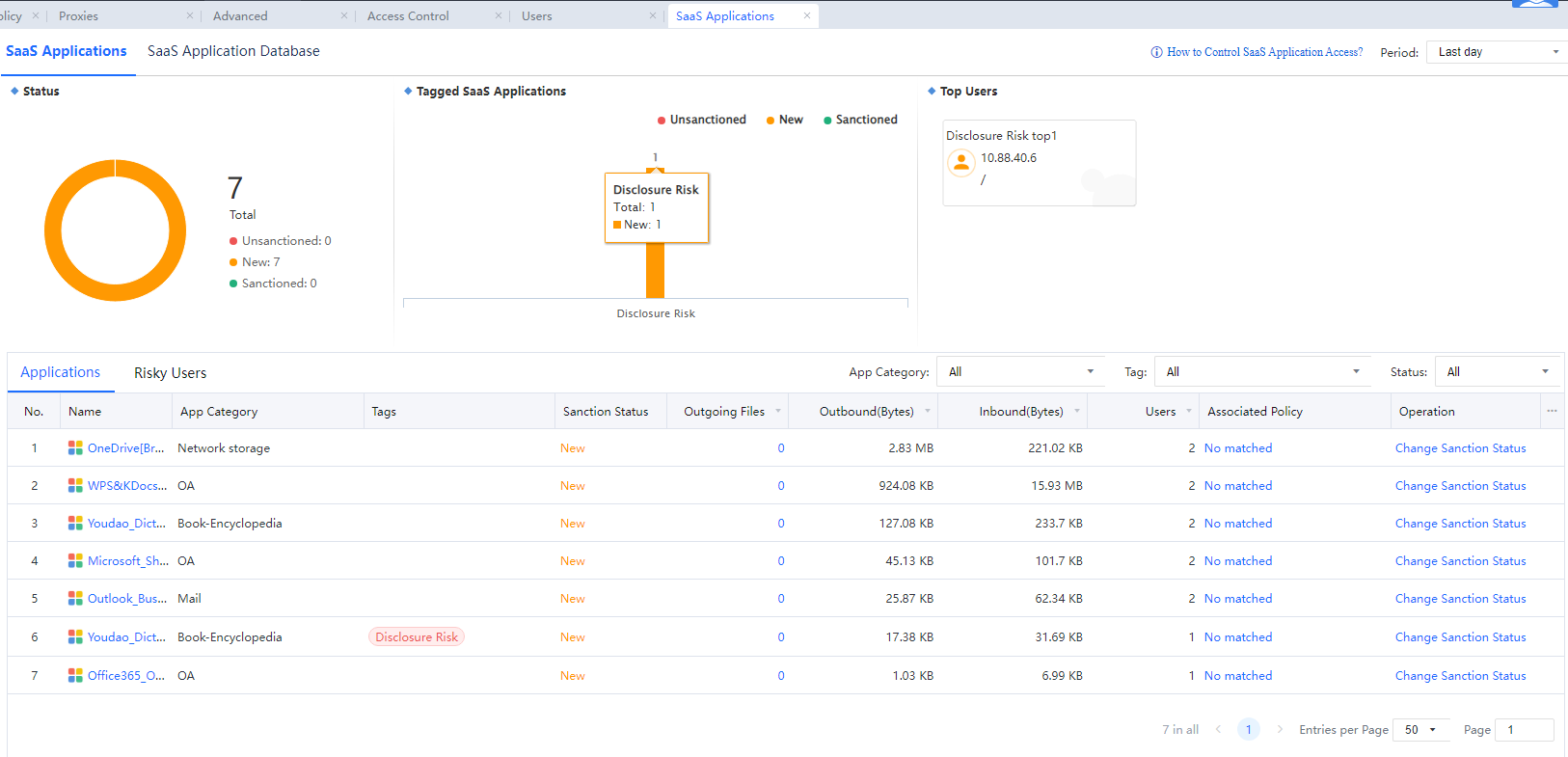
SaaS Options
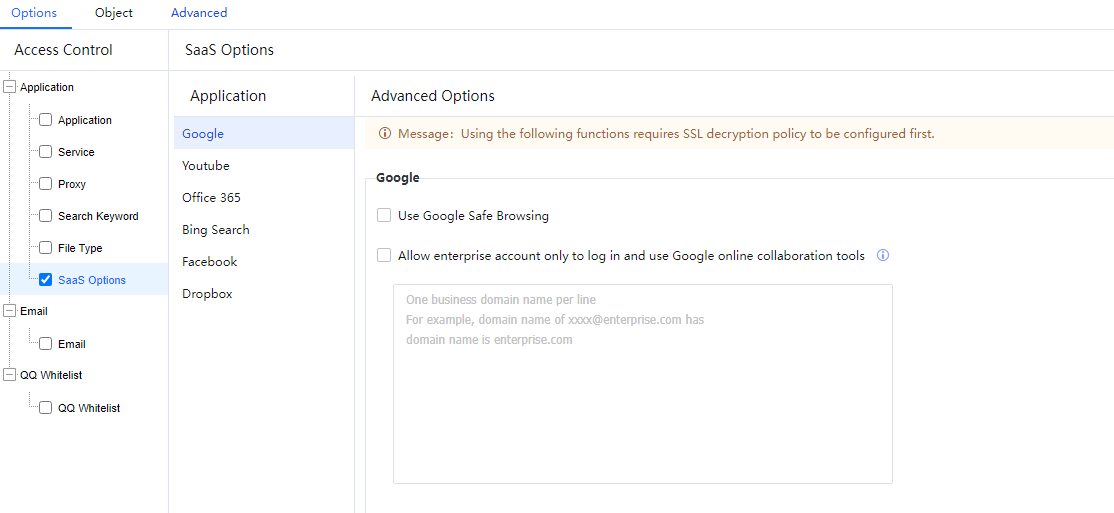
The configuration documents are provided on this device and are not repeated in this manual. The corresponding function post in the Sangfor community is as follows: https://community.Sangfor.com/forum.php?mod=viewthread&tid=1488&highlight=
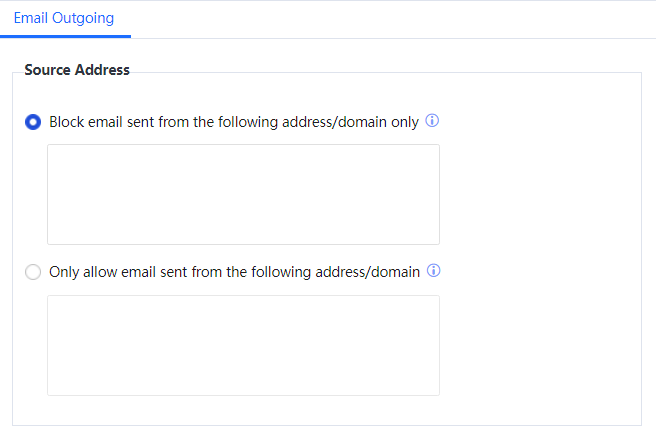
3.6.1.5.1.3 Email
Mail filtering involves filtering emails sent and received by clients on the intranet through SMTP or POP3. The IAG can filter mails by the sending address, recipient address, mail subject, or text keyword.
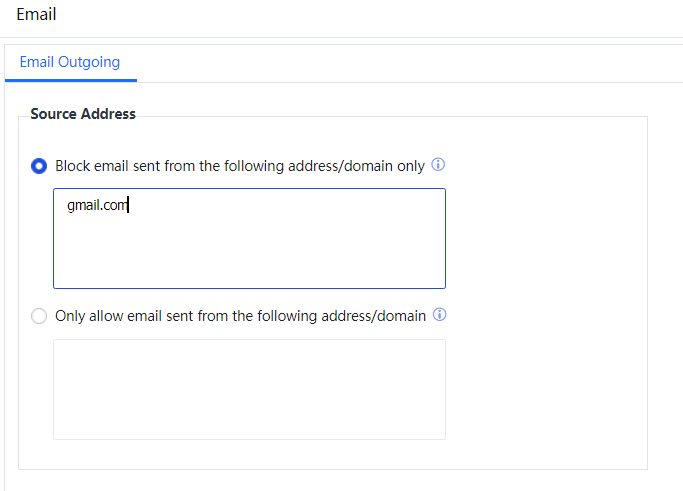
The following is an example of setting a policy to filter emails sent to a Gmail mailbox or emails with a .exe attachment.
Select Email and set a policy to filter emails sent to a Gmail mailbox or emails with a .exe attachment.
There are several methods of filtering sent and received emails:
Source Address: to filter sender addresses of mails. Select Block email sent from the following addresses/domain only and enter the mail addresses to be filtered. If the sender of any mail matches any of the listed mail addresses, the IAG blocks the mail. Select Only allow email sent from the following addresses/domain and enter the mail addresses to be allowed. If the sender of any mail matches any of the listed mail addresses, the IAG allows the mail. See the following figure.
Destination Address: to filter recipient addresses of mails. Select Block email sent to the following mail addresses/domain and enter the mail addresses to be filtered. If the recipient of any mail matches any of the listed mail addresses, the IAG blocks the mail. Select Only allow email sent to the following mail addresses/domain and enter the mail addresses to be allowed. If the recipient of any mail matches any of the listed mail addresses, the IAG allows the mail. In this example, emails sent to Gmail mailboxes are to be filtered. Therefore, enter @gmail.com in Block email sent to the following address/domain.
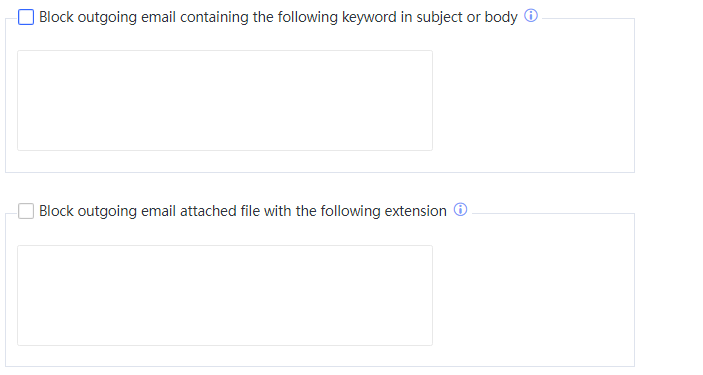
Block outgoing email containing the following keyword in subject or body: If this option is selected, the IAG detects whether the title and text of a mail to be sent contain the specified keywords. If yes, the IAG blocks the mail. For example, to filter mails whose title or text contains the keyword Job Hunting, enter Job Hunting.
Block outgoing email attached file with the following extension: If this option is selected, the IAG detects whether a mail to be sent contains an attachment of the specified type. If yes, the IAG blocks the mail. In this example, emails containing a .exe attachment are to be filtered. Therefore, enter .exe.
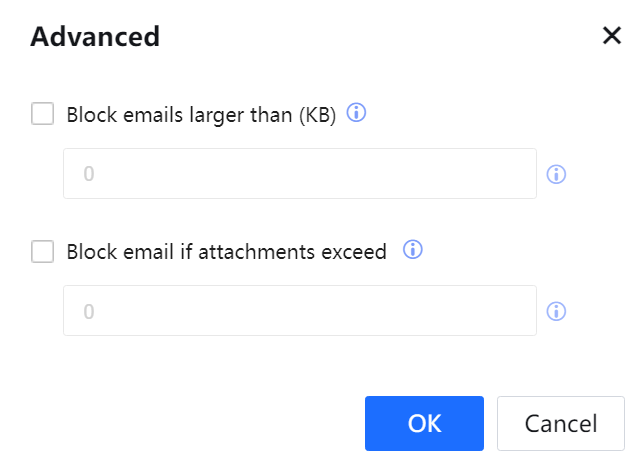
If Block emails larger than (KB) is selected in the Advanced dialog box, and the function of detecting mail size is enabled, the IAG will block emails whose size exceeds the specified value. If Block email if attachments exceed is selected and the function of detecting the number of attachments in emails is enabled, the IAG will block emails whose number of attachments exceeds the specified value.

The configured rules have the OR relationship and are matched from the top down. If any rule is matched, the IAG performs the specified action. For any conflicts, the first matched rule prevails.

- On the Email page, you can enter a complete mail address or a suffix, for example, xxx@abc.com, @abc.com, or abc.com. If abc.com is entered, emails with abc.com or abc.com.cn will be matched. Enter one mail address in each row.
On the Email page, you can enter a regular expression when setting keywords. For example, if key.*d is entered, and both key and keyword are matched.
If one keyword is entered in each row, keywords in different rows have the OR relationship. A rule will be matched if any keyword is matched.
- If multiple keywords separated with a comma (,) are entered in each row, the keywords have the AND relationship. A rule will be matched if all keywords in a row are matched.
3.Mail filtering involves filtering emails that are sent through SMTP. This function is invalid for webmail. To use this function, ensure that mail data passes the IAG. The standard SMTP port used for sending emails is TCP 25. The mail filtering function is invalid for emails that are sent over a non-standard port.
4.An SMTP authentication password must contain at least three characters. If the SMTP authentication password of a mail contains less than three characters, the mail will be blocked.
5.Before enabling mail filtering, ensure the IAG can connect to the mail server correctly. Otherwise, emails cannot be sent.
3.6.1.5.1.4 QQ Whitelist
You can configure a QQ number whitelist to allow specified QQ numbers and block other QQ numbers. The whitelist function is compatible with PC QQ client and mobile QQ clients.
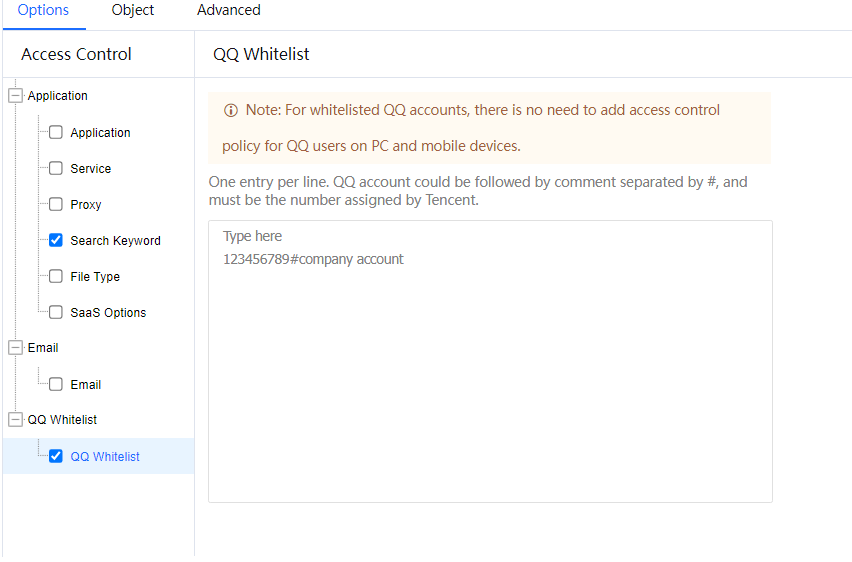
Click OK.

If a mobile phone number or a mailbox is used as the QQ account, you need to fill in the account automatically allocated by Tencent, which is a numeric string.
3.6.1.5.1.5 SSL Decryption
The role of the SSL decryption policy is to perform content audit identification for applications connected using SSL security protocols, including encrypted websites, webmail, web-bbs, POP3, IMCP, SNMP, etc., except for financial-related websites such as online banking and online payment.
Two decryption methods: IAG decryption and Ingress client decryption. Selecting ingress client decryption requires configuring an ingress policy to take effect.
| |
IAG decryption |
Ingress Client Decryption |
| Requirement |
No PC system requirements. Need to install the certificate. |
Windows system users need to install the ingress client, need to install the certificate. |
| Distribution Method |
1. AD domain, desktop management software, and ingress client distribution to install the certificate, users are not aware 2. Users who have not installed the certificate will be redirected to the certificate installation page when they visit the webpage, and they will be guided to download the certificate installation tool |
1. The ingress client will be installed silently, and the users are not aware 2. AD domain, desktop management software, and ingress client distribution to install the certificate, users are not aware 3. Users who have not installed the certificate will be redirected to the certificate installation page when they visit the webpage, and they will be guided to download the installation tool |
| Advantage |
No need to install the ingress client, no PC system requirements |
No need to consume IAG performance, richer audit content |
| Notes |
Decryption based on web page identification requires more CPU resources. Customizing the domain name for decryption is recommended to reduce performance degradation caused by excessive traffic decryption. For complete decryption requirements, you can use hardware model devices with hardware acceleration cards. The decryption performance of hardware acceleration cards is doubled compared with software decryption performance. For specific models, please contact Sangfor regional offices or Sangfor channel partners for details. |
| The HTTPS decryption function configuration does not support IP addresses in the domain name list when the domain name list is customized.[zyl89][U90] |
| When using the HTTPS decryption function, you need to install a device certificate on the endpoint to a trusted root certification authority. |
| HTTPS decryption does not support the QUIC protocol. It is recommended to check Reject data transmitted over QUIC protocol. |
| The HTTPS decryption function conflicts with the Easy Connect protocol of SSL VPN. When the HTTPS decryption function is enabled, if the endpoint needs to use Easy Connect to access the headquarters resources through SSL VPN, it needs to be excluded from the exclusion list of the SSL global decryption of the IAG device. Otherwise, the connection will be interrupted. |
| This function requires Multi-function license/SSL content Ident. |
| When IAG decryption and ingress client decryption are configured simultaneously, the policy list is matched from top to bottom, and only the first one that is matched takes effect. |
| Using an ingress client for decryption is not recommended if the endpoint is a virtual machine. You can use an IAG decryption to decrypt. |
| |
When the option of installing the ingress client on a PC is turned on, it only supports the Windows system (the XP system does not support it). MacOS and Linux systems can use IAG decryption for decryption. |
| |
The ingress client only decrypts port 443 by default. |
| |
The client's certificate and the SSL content recognition certificate are different certificates. |
| HTTPS decryption supports the scenario where the device acts as a proxy but only supports HTTPS proxy and does not support SOCKS proxy. The client decryption solution does not support use in proxy scenarios. |
|
| In two-way certificate verification, the HTTPS decryption function cannot be used. Otherwise, a connection error will be caused by a client verification failure. |
|
| If the endpoint’s DNS request data does not go through the device or the HTTPS website accessed by the endpoint is directly accessed with an IP address, the HTTPS decryption function is not supported. |
|
| |
|
|
|
Table 4:Decryption Comparison table
Configuration steps:
Step 1.In Online Activities > Access Control, click Add > SSL Decryption to enable the policy[LCH91][A92].
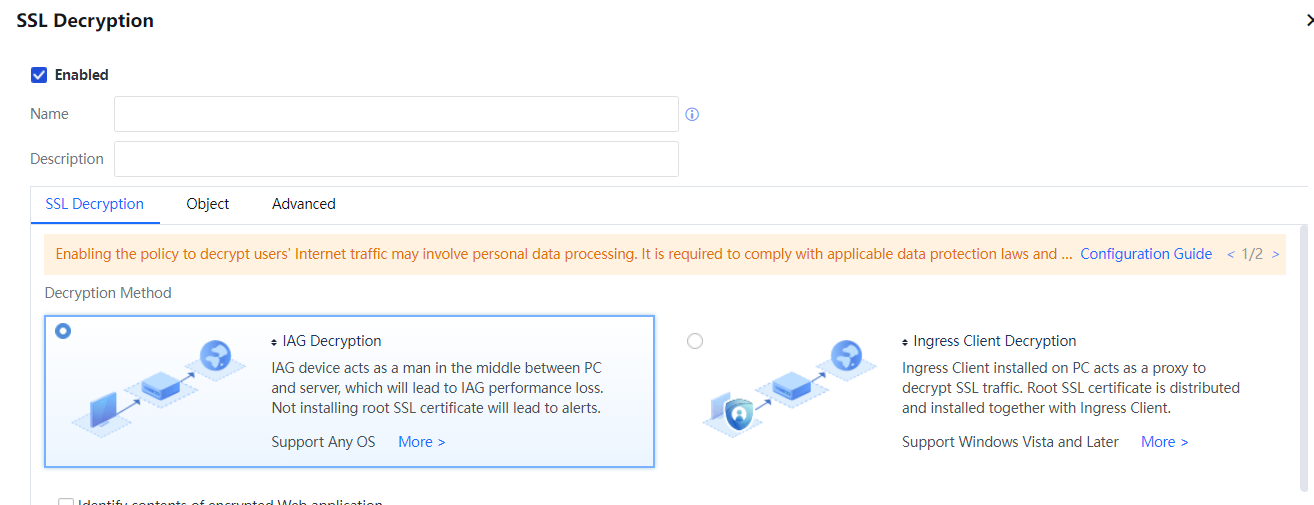
Step 2.Fill in the policy name and description. The policy name is the only required item, and the description information is not required.
Step 3.The decryption method can choose IAG decryption or ingress client decryption according to the actual situation. For more detail, you can click on More.
Step 4.Define the decryption range, and select Identify contents of encrypted Web application. You can choose All or Specified; web applications only support identification using port 443.
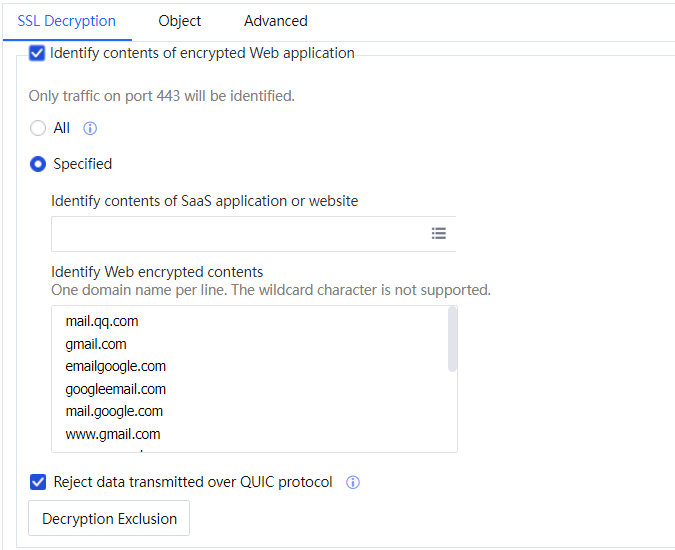
Step 5.Select SaaS applications or encrypted web content according to requirements when selecting specified identification.
Step 6.Check Reject data transmitted over QUIC protocol. SSL decryption will not affect QUIC protocol domain names.
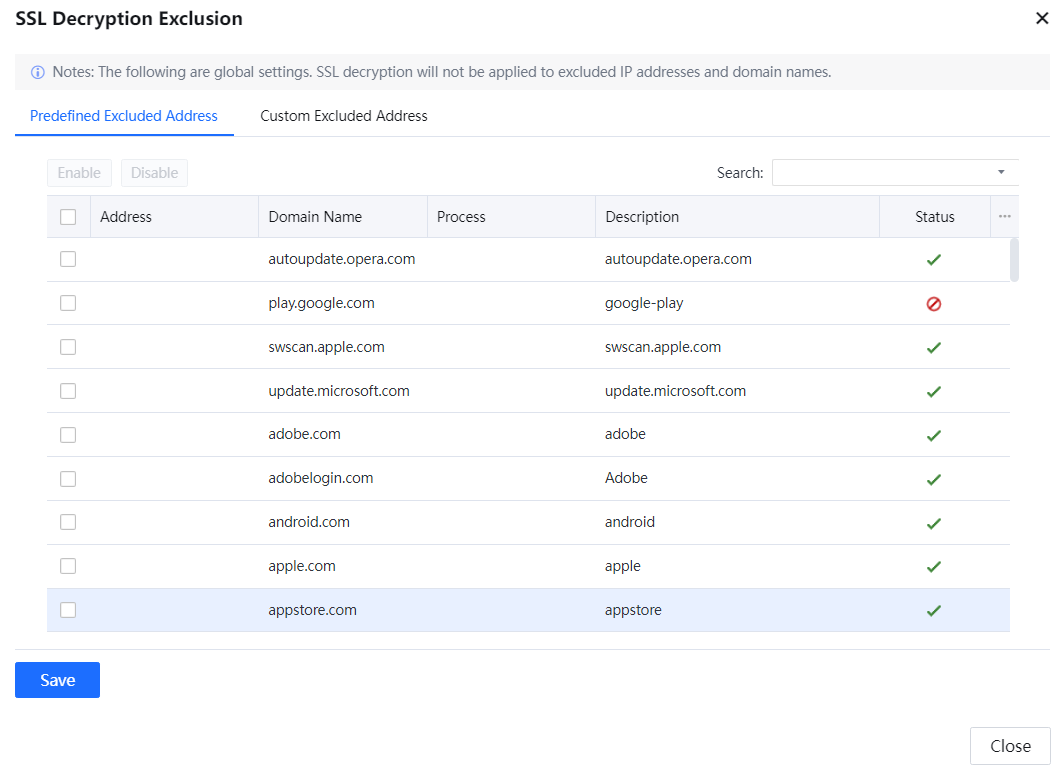
Step 7.Click Decryption Exclusion, configure the IP, domain name, and process that do not require SSL content identification. The three are related to each other and can be used flexibly.
Step 8.When you need to identify the content of ports 25, 465, 143, 993, and 587, you need to enable the Filter encrypted emails.
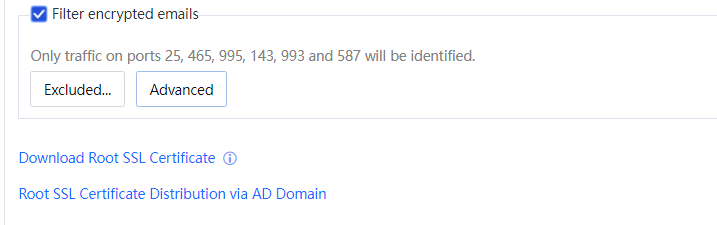
Step 9.Click Download Root SSL Certificate to download and install the downloaded root certificate on the computer and eliminate the browser security alarm caused by enabling SSL content recognition. If you need to stop the security alarm of the browser in the AD domain environment, click Root SSL Certificate Distribution via AD Domain, and refer to the configuration steps in the document for details.
Step 10.After the setting is completed, click OK. If you need to edit other types of policies, continue to select other control types for editing.

SSL content recognition is invalid for financial-related sites such as online banking and online payment to prevent sensitive financial information from being audited.
In the HTTPS scenario, we need to configure SSL content recognition.
Add a Policy Using a Template
You can use an available policy or a built-in policy as a template to add a policy. If a policy is added using a template, the settings for the template are applied to the new policy. It facilitates the addition of multiple Internet access policies that are identical to or similar to each other.
The configuration page is shown in the figure below:
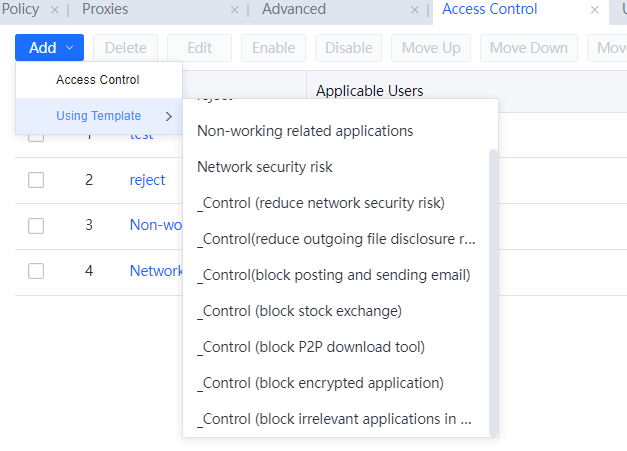
For example, if you use the Various Internet activities and traffic template to add a policy, all the settings included are copied to the new policy. You can modify the settings of Policy Name, Description, Policy Setup, Applicable Group and User, and Advanced Settings.

Suppose the Privilege of Admin in Same Role is not selected on the Advanced tab page. In that case, same role administrators cannot use this template to add a new policy after logging in to the console.




