Access Control
Access control consists of three modules: Application, Email, and QQ Whitelist, as shown in the following figure.
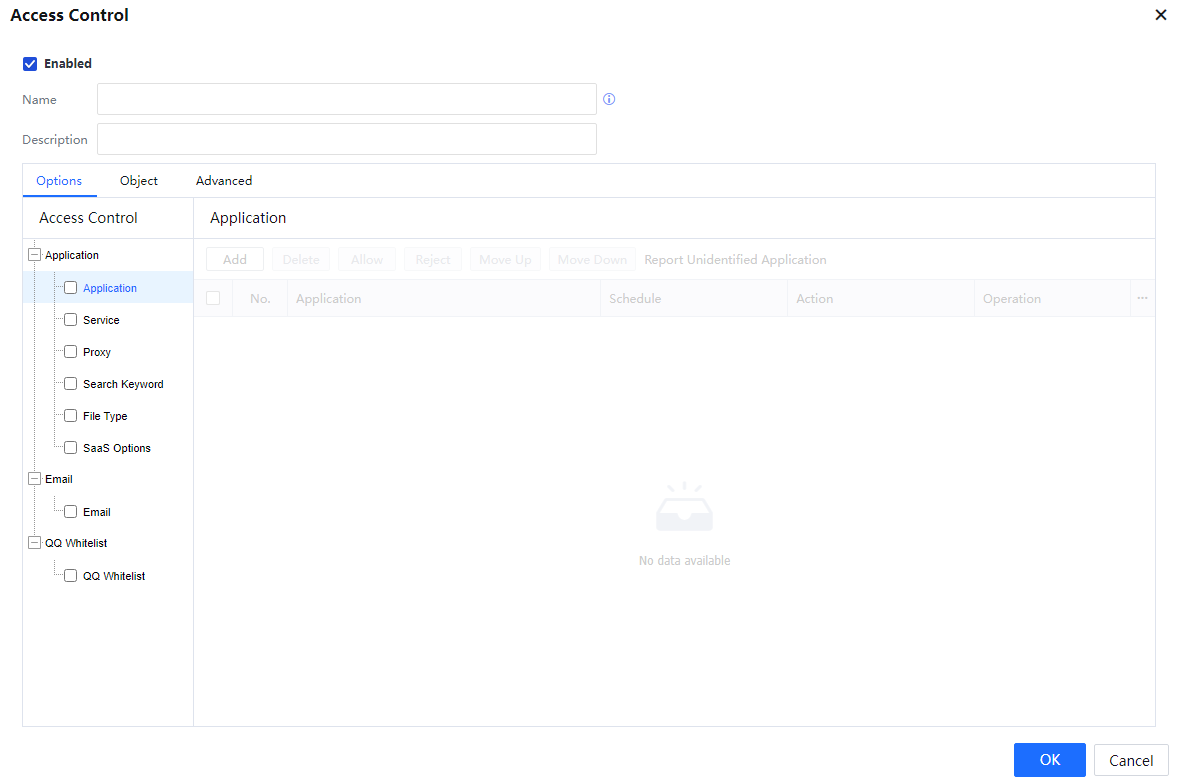

The Application includes Application, Service, Proxy, Search Keyword, File Type, and SaaS Options.
Application: The IAG has an application rule library set for all types of common network applications and a URL Database set for websites. The Application module references these rules to implement permission control on network applications and websites.
Access Control has four types: Website Browse, File Upload, Other Upload, and HTTPS.[LCH74][75]
In Access Control, the IAG detects the URLs of visited websites and controls website access behaviors. The URLs are referenced from the URL groups defined on the page displayed after choosing System > Objects > URL Database.
The IAG has embedded URL groups. Dedicated personnel collect and classify a large number of URLs. Embedded URL groups can be referenced. In addition, custom URL groups can be defined.
In control of file uploading and other uploading, the IAG filters behaviors of uploading files through HTTP POST or other contents based on URL groups.
HTTPS permission control is about filtering websites visited through HTTPS. Like access control, HTTPS permission control is also performed based on URL groups defined on the page displayed after choosing System > Objects > URL Database. They differ in the URL detection mode. Data is encrypted when a user visits a secure website through HTTPS, and the IAG cannot detect the URL. Generally, the URL of a secure website is the same as the address specified in Issued To of an SSL certificate. Therefore, the IAG can detect this value in the SSL certificate to obtain the URL of the visited security website. To define the URL of an HTTPS website, set the URL based on the value of Issued To in the certificate issued by the website.
Service involves detecting the IP address, protocol ID, and port number of packets to control Internet access data. You can choose System > Objects > URL Database, define target IP groups, and choose System > Objects > Service and define target protocols or ports. These defined objects are referenced in port control to control Internet access data.
Proxy includes whether to allow an external HTTP proxy and an external SOCK4/5 proxy and whether to detect sharing Internet access. To prevent applications from transmitting data using a standard HTTP port (TCP 80) or SSL port (TCP 443) to escape restrictions of the IAG, you can select the Not allow other protocols on standard HTTP or SSL port.
Search Keyword falls into two types: Search Keyword and HTTP Upload. In search keyword filtering, the IAG performs filtering or generates alarms based on search keywords. In HTTP uploading, the IAG performs filtering or generates alarms based on keywords in HTTP uploading. The referenced keywords are defined on the page displayed after choosing System > Objects > Keyword Group. The two types of filtering are aimed at all HTTP websites and cannot implement keyword-based filtering or alarming for specified URLs.
In File Type, the IAG can filter files Upload or Download through HTTP or FTP. The referenced file types are defined on the page displayed after choosing System > Objects > File Type Group.

SaaS Options: The configuration documents are provided on this device and are not repeated in this manual. The corresponding function post in the Sangfor community is as follows: http://bbs.Sangfor.com.cn/forum.php?mod=viewthread&tid=65956[LCH76][77]

The email involves filtering emails sent and received by clients on the intranet through SMTP or POP3. The IAG can filter mails by the sending address, recipient address, mail subject, or text keyword.

If a QQ Whitelist is defined, only QQ numbers in the whitelist can be used, and therefore no QQ blocking policy needs to be configured. The whitelist function is compatible with both the PC QQ client and the mobile QQ client.




