Operating system scenario introduction
When an enterprise only allows employees to use the XP operating system, the operating system of the access endpoint is checked for compliance, and the compliant operating system can normally access the Internet. There are three ways to deal with non-compliant endpoints: reject Internet access and alert, give alert, and log event only.
Configuration steps:
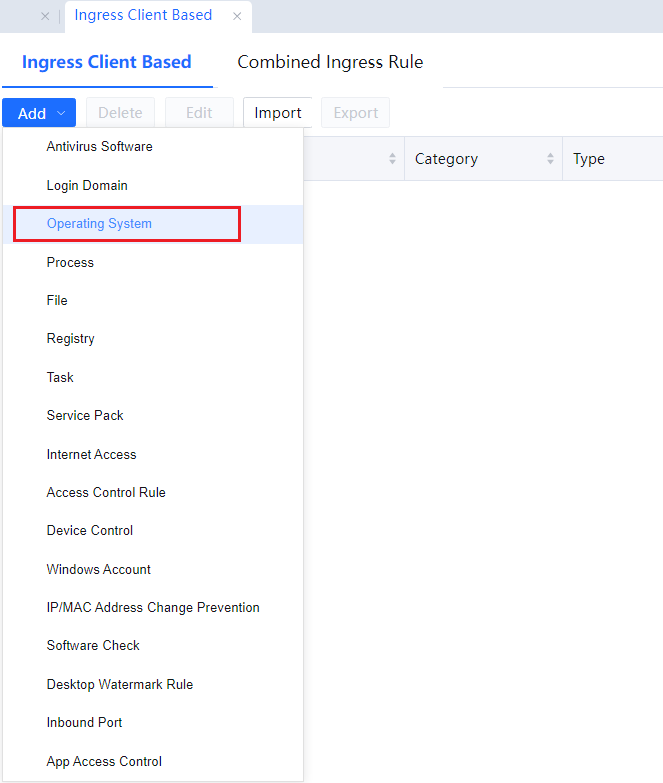
Step 1.In Access Mgt > Endpoint Check > Check Rules > Ingress Client Based, click Add, and select Operating System.
Step 2.Fill in the rule name, category, and description on the operating system rules page, and check the corresponding operating system. The operating system selected here is not in violation, and the operating system that is not selected is in violation. Take the XP system as an example, only the XP system is allowed, and the other unchecked systems are all violating systems.
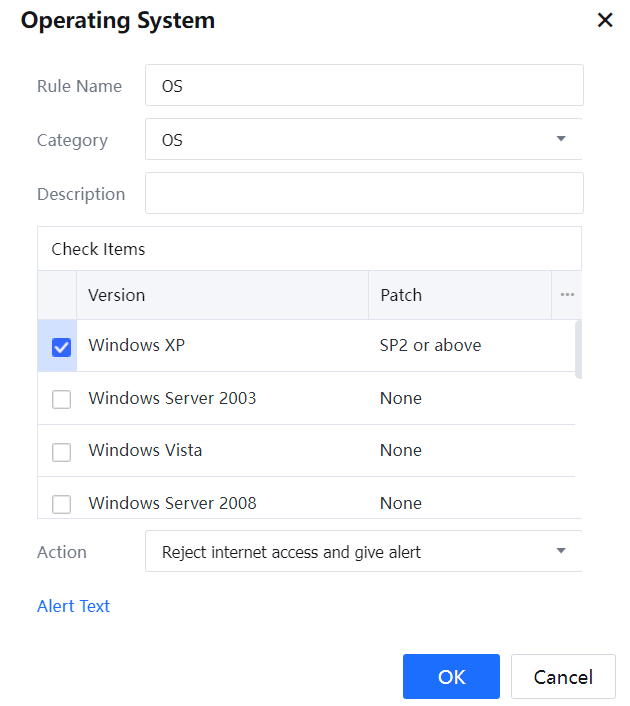
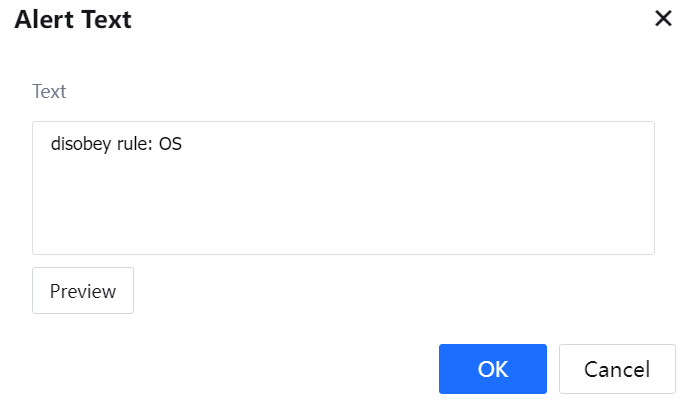
Step 3.Some methods for illegal operations include: Reject internet access and give alert, Give alert, and Log event only. At the same time, click Alert Text to customize the alert content[LCH72][A73].
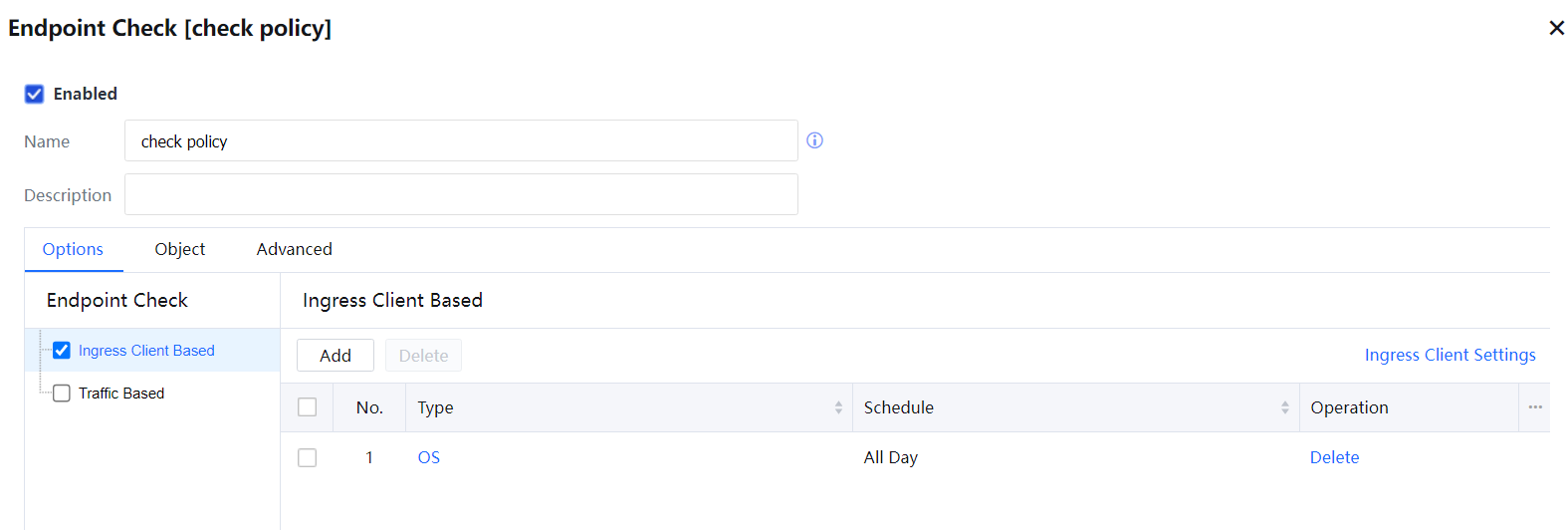
Step 4.After completing the check rule settings, create a new policy in Access Mgt > Endpoint Check > Check Policies in the navigation menu, enter the policy name and description information, check the ingress client-based, and click Add. Select the previously created operating system rule, select the effective time as needed, and click OK.
Step 5.On the Objects page, select the users for whom the policy takes effect. You can choose according to the user, location, endpoint type, and destination.
Step 6.On the Advanced page, you can set the expiration time of the policy, the viewing and editing permission settings of the same-level administrators, and whether to allow lower-level administrators to view it.
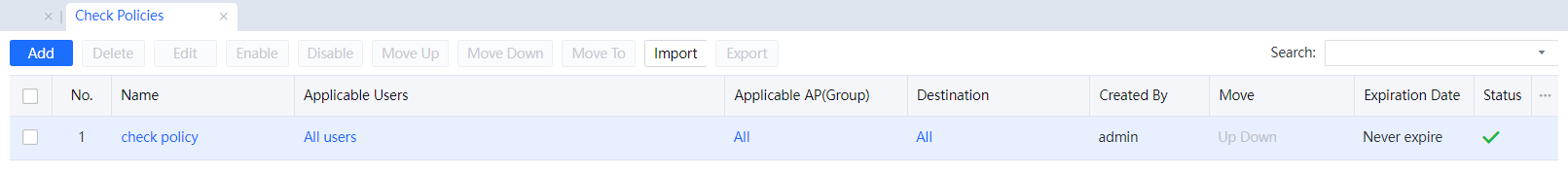
Step 7.Click OK to complete the configuration of the operating system detection function, and you can see the operating system check strategy in the check policy list.
Step 8.When the user is not using the specified operating system, access to the Internet will be prohibited.
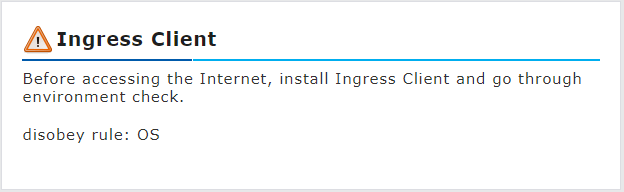
Step 9.The device will pop up a reminder of violation of disobey rules: OS.