The role of the check policy is to check and control the compliance and illegal outreach of all endpoints. The policy configuration is first customized according to the settings of the check rules. The following are the steps to check the configuration of the policy.
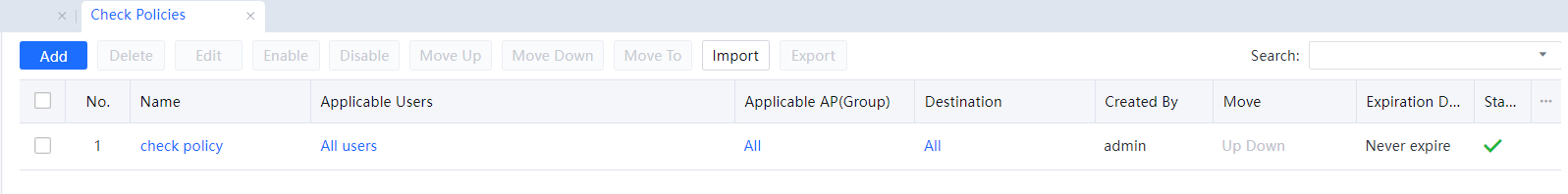
Step 1.After configuring the check rule settings, create a new policy in Access Mgt > Endpoint Check > Check Policies in the navigation menu, click to enable the policy, and enter the policy name and description information.
Step 2.In the policy settings, check the corresponding check rules that have been configured and click Add. Select the type of rule created before, select the effective time as needed, and click OK.
Step 3.On the Object page, select the users for which the policy takes effect. You can select the objects to be checked according to the user, location, endpoint type, and destination.
Step 4.On the Advanced page, you can set the expiration time of the policy, the viewing and editing permission settings of the same-level administrator, and whether to allow lower-level administrators to view it.
Step 5.Click OK to complete the configuration of the check policy function.
Check Policy Management
The administrator can delete, edit in batches, enable and disable, import/export, move up/down, etc.. All check policies can be filtered and selected.
Check Rules
Check rules are divided into ingress client-based checking. When implementing the ingress client-based rules, the endpoint needs to install the ingress plug-in.
Ingress Client Based
Step 1.In Access Mgt > Endpoint Check > Check Rules > Ingress Client Based, click Add to add the check rule to be configured.
Step 2.Fill in the rule name and description, select the rule type in the menu, or enter the custom rule type name in the dialog box to select the configuration and item to be checked according to the configured check rule.
Step 3.
| Ingress Client Based Rule Name |
Rule Description |
| Anti-Virus Software Rule |
The antivirus software checked mainly includes Sangfor Endpoint Secure, 360 Total Security, 360 Antivirus, Rising Antivirus, Kxetray, QQPCTray, 2345 MPC Safe, Rising Personal Firewall, Avira AntiVir, Kaspersky, Avast,Symantec, Trend Micro Antivirus, Norton Antivirus, McAfee, Windows Defender, Microsoft Security Essentials, Jiangmin Antivirus, Huorong Security, Panda Dome, Dr.Web Security Space, ESET Nod32, etc. |
| Login Domain Rule |
Must log in to the domain. Need to log in to the specified domain: it can be customized. |
| Operating System Rule |
Windows XP, Windows2003, Windows7, Windows8, Windows10, and Windows 11. Windows2012R2, Windows2016, Windows Vista, Windows2008R2. Windows2008. |
| Process Rule |
Process name, window name, program path. Process status: running and not running. Advanced conditions: The MD5 value and size of the matching program can be set. |
| File Rule |
File path: The storage path. File status: The file exists, or the file does not exist. Advanced conditions: Set the MD5 value, file size, and update date of the matching file by the number of days lagging behind the current date. |
| Registry Rule |
Registry entries, entry names, and entry data. Entry status: yes and no. |
| Task Rule |
execute program 1. Enter the program path or click to upload the file. 2. Configure the parameters required for the operation of the program, and use it with the above program |
| Scheduled Execution 1. Periodic operation: the minimum time interval is 40 seconds. 2. Run once: run when the access program is started on the computer. |
| Execution permission 1. The current user execution permission. 2. Execute with SYSTEM user authority. |
| Result check 1. The result is returned without inspection. 2. Check the returned result |
| Service patch Rule |
Detect according to the specified level; detect according to the specified patch; deal with violations when obtaining pc patch information and identification. |
| Internet Access Rule |
Dial-up behavior, wireless network port, dual network card behavior, 4g network card, connection to the external network, custom external connection, connection to illegal WIFI, use of an illegal gateway. |
| Access control rule |
Only the following address can be accessed. The following address cannot be accessed. |
| Device Control Rule |
Forbidden Device types Storage devices, network devices, Bluetooth devices, cameras, and printers. Access control U disk and mobile hard disk access: readable and writable, rejected, readable, alarm. Portable device access: allow, disable, alarm. Whitelist Whitelist the specific device ID. |
| Windows account-based rule |
It is forbidden to log in to the computer as the super administrator of the computer (an account belonging to the Administrators group). Otherwise, the computer is prohibited from accessing the Internet. |
| Anti-Defacement Rule |
It is to check the user to change their MAC address and the PC IP address. |
| Software Check Rule |
It is to check the software installed on the PC and select the action to be taken. |
| Desktop Watermark Rule |
It is to display the watermark on the PC to prevent data leakage. |
| Inbound Port |
Allow and block specific ports[ZY67]. |
| App Access Control |
Control application access permissions. The action includes Allow, Deny, Deny addresses below and Allow addresses below.[ZY68] |
Table 2: Rule name table
Step 4.Configure the violation action and select the corresponding violation action according to different check rules. Click OK to complete the configuration.
Step 5.
| Ingress Client Based Check Rule |
Violation[LCH69][ZY70] |
| Anti-Virus Software-Based Rule |
Including: Prohibiting Internet access and prompting users, prompting users, fixing violations, restricting user rights, and customizing prompt content. |
| Login Domain Based Rule |
Including: Prohibiting Internet access and prompting users, prompting users, only recording results, limiting user rights, and customizing the prompt content. |
| Operating System Based Rule |
Including: Prohibiting Internet access and prompting users, prompting users, only recording results, and customizing prompt content. |
| Process Based Rule |
Prohibit surfing the Internet and prompt the user, stop the process, prompt the user, only record the result, and customize the prompt content. |
| File Based Rule |
Prohibit surfing the Internet and prompt users, delete files, prompt users, only record results, and customize prompt content. |
| Task-Based Rule |
Prohibit surfing the Internet and prompt the user, delete this item, prompt the user, only record the result, and customize the prompt content. |
| Registry Based Rule |
Prohibit Internet access and prompt users, prompt users, and only record results. |
| Patch Based Rule |
Prompt the user and only record the result. |
| Access Check |
Send alert emails, disconnect the network, and customize the reminder content. |
| External Device Control |
Whitelist setting, the corresponding device should add the ID to the whitelist. |
| Desktop Watermark Rule |
Configuration: Default Text: including Username, Time, Alias, Department/Group, IP Address, MAC Address, Windows Username, and Host Name. Select at least one item. Custom Text: You can customize the display watermark content (optional). Opacity: Configure the watermark opacity range. The default value is 20. Density: Select between High, Medium, and Low. The default value is Medium[ZY71]. |
Table 3:Rule Table

1.When configuring the check policy, the added rule type is the name entered in the check rule type. Therefore, it is recommended that the rule type needs to be filled in to match the rule for subsequent calls.
2.Operating system check: The patch package requires SP2 or above for Windows XP and no other requirements.
3.File inspection: The rules are only used for files with conditions configured at the same time.
4.Patch package detection: This rule does not support Windows XP, Windows Server 2003, and the operating system versions below it; when checking at the specified level and detecting for the specified patch simultaneously, any violation detected by either method is a violation.
5.Access check rules: Among them, illegal WIFI and illegal gateways have whitelist settings.
6.External device control rules: Windows XP system and all family version systems have no group policy and do not support group policy management and control; refined control only supports Windows 7 and above, regardless of whether it is the home version; refined control is only for USB interface Storage device: U disk mobile hard disk portable device.
Combined Ingress Rule
Step 1.In Access Mgt > Endpoint Check > Check Rules > Ingress Client Based, click Combined Ingress Rule and Add to add a combination rule.
Step 2.Fill in the rule name and rule description. The rule type can be selected in the menu, or you can directly enter the name of the custom rule type in the dialog box. This rule type is to be called when adding a rule policy later. The establishment of the combination rule can choose: establish all and any of the rules.
Step 3.In the combination rule setting, select the rule to be set, and click Add to add it to the selected rules. If there is no rule to choose from, create an operating system rule, process rule, file rule, registry rule, scheduled task rule, patch package detection rule, or Windows account rule in the endpoint ingress client-based check rule.
Step 4.Operation after violation: Reject request and alert, give an alert or log event only. You can also click Prompt Text to customize the prompt content.
Step 5.Click OK, and the combination rule configuration is completed.

The combination rule function only supports operating system rules, process rules, file rules, registry rules, scheduled task rules, patch package detection rules, and Windows account rules. Other rules currently do not support the combined ingress rule.
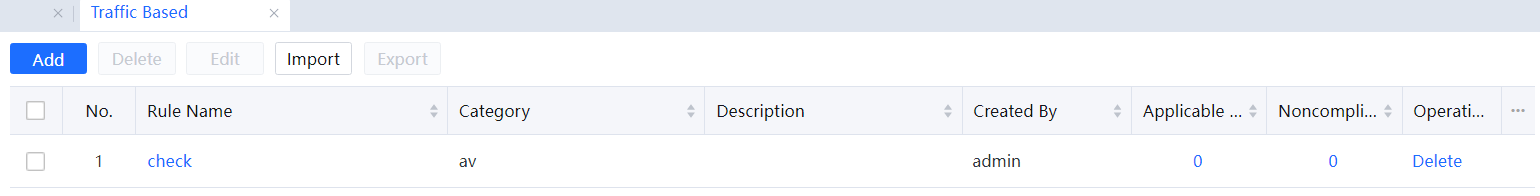
Check Rule Management
In Access Mgt > Endpoint Check > Check Rules, the administrator can delete, batch edit, and import/export ingress client-based check rules. Combined ingress rules only support the delete and edit operations.

1. When a rule that a check policy has referenced, you cannot delete it directly; if you need to delete it, you need to delete the rule referenced in the check policy first.
2. Cannot export the built-in check rules.
3. The imported rule file must be in zip format, and the imported file must include the IngressRuleExport.conf file, and the IngressRuleExport.conf file must be at the outermost level.
Traffic Based
Step 1. In Access Mgt > Endpoint Check > Check Rules > Traffic Based, click Add.
Step 2.Fill in the rule name and rule description. The rule type can be selected from the menu or enter a custom rule type name directly in the dialog box.
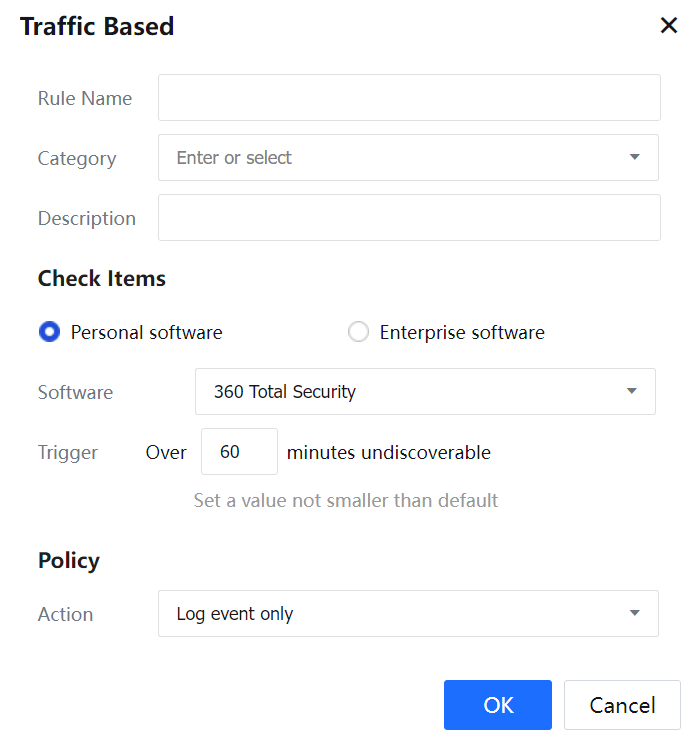
Step 3.Check items configuration can choose personal antivirus software or enterprise antivirus software. The personal version of antivirus software has defined traffic characteristics for the device. The enterprise version of the antivirus software will have a designated server address. It can be judged whether to install the antivirus software by checking whether the endpoint has traffic.
Personal Software
You can select the anti-software: 360 Total Security, Kingsoft Antivirus, Huorong Security, Tencent PC Manager, Avira AntiVir, Kaspersky, and Symantec.
Trigger & Action: According to the default time set by different anti-virus software, check whether the anti-virus software exists. The filling time cannot be less than the default value.
Enterprise Software
The anti-virus that can be selected for detection is Sangfor Endpoint Secure, QI-ANXIN Tianqing, Kaspersky, Symantec, and custom enterprise anti-virus.
Trigger & Action: need to be set according to the update frequency of the enterprise version of the anti-virus configuration (SANGFOR ENDPOINT SECURE defaults to fail to detect the anti-virus for more than 1 minute is a violation, and it is recommended to configure it for 5 minutes), each application has a different minimum default value, The user configuration must be greater than the default value.
Step 4.Deal with violations. You can select Log event only or Regularly redirect to specified site. If you choose to redirect to the specified URL, you need to configure the Redirection configuration: Redirect URL and Interval.
Step 5.Click OK to complete the configuration of traffic detection rules.