The advanced authentication options include Authentication Options and Managed Authentication.
Authentication Options
You can configure authentication options on the page shown in the following figure.
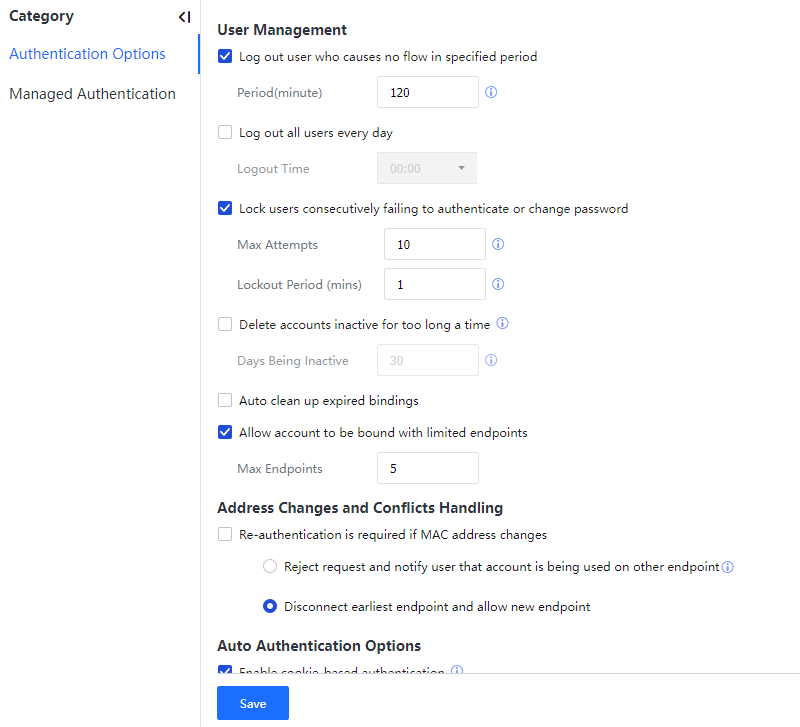
Select Log out users who causes no flow in specified period to set a timeout duration for the IAG to log out a user if the user has no traffic within the specified time. The login time is detected for users whose devices are automatically added to the organizational structure. If they have not logged in after the set time, IAG will automatically log out of these users.

Users created manually will not be logged out.
Select Log out all users every day to set a time for the IAG to log out all online users.
Select Lock users consecutively failing to authenticate or change password for the IAG to lock a user if the user fails authentication a specified number of times.
After Delete accounts inactive for too long a time is selected, the IAG will detect the login time of users that are automatically added to the local organization structure. If any user does not log in for a long time, the IAG will delete this user. Manually created users will not be deleted.
Auto clean up expired bindings: For authentication-free binding relationships automatically entered by the device, detect the login time. If the authentication-free binding time expires, these users will be automatically deleted.

The manually entered authentication-free users also will be deleted.
Allow account to be bound with limited endpoints: Set the number of endpoints corresponding to the account and limit the users logging in from several endpoints using the same account.
After selecting Re-authentication is required if MAC address changes, an authenticated user must perform authentication again if the MAC address changes. For example, user A with the IP address 192.168.1.1 adopts Password based. After getting offline, user A will remain logged in for some time. During this period, if another user preempts the IP address 192.168.1.1, the MAC address of user A will change. In this case, user A must authenticate again before accessing the Internet.
In Take action if user logs in on a second IP address with an account that does not allow concurrent login, set a policy for new endpoints by selecting Reject request and notify user that account is being used on another endpoint or Disconnect earliest endpoint and allow new endpoint. Multiple users can concurrently use a public account for login. You can choose Online Activities > Bandwidth Management > Quota Control [A63]and set the number of endpoints to use the public account for login. When you exceed the number of endpoints, you need to specify a policy for new endpoints.
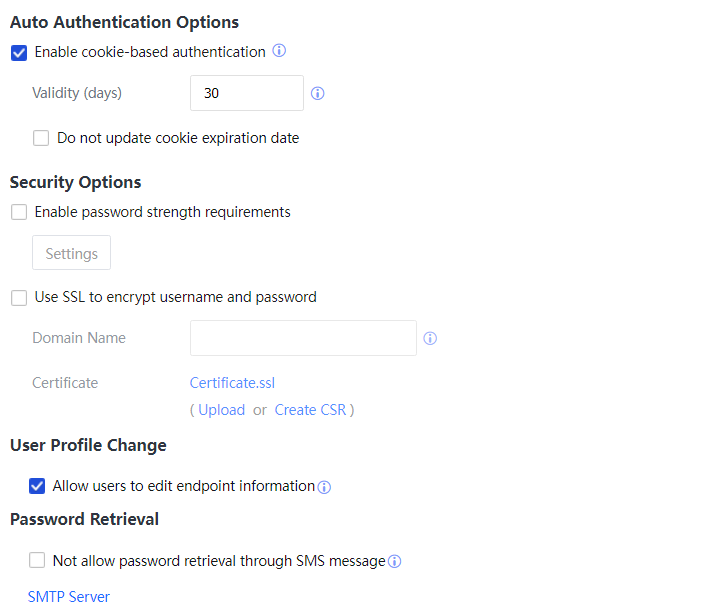
Enable cookie-based authentication: Set the Cookie-based authentication validity within 1-100 days.
Select Enable password strength requirements and click Settings to set the security requirements for user passwords. In the dialog box for setting security requirements, you can select Password and username must not be the same, New and the current password must not be the same, Password Strength, or Password must contain. After all four options are selected, a user can change the login password only if all the requirements are met.
By default, the password-based authentication page is an HTTP page. Information submitted on this page is in plaintext. Use SSL to encrypt username and password must be selected if SSL encryption is required.
Domain Name indicates the domain name of a page to which users are redirected. Click Certificate to import or create a CSR.
Allow user to edit endpoint information: If the endpoint user can change the information of bound endpoints by oneself, check this function.
Not allow password retrieval through SMS message: If you use the password retrieval function and do not want to retrieve the password using SMS message, check this function to use the Email account password function. You shall configure the SMTP server.
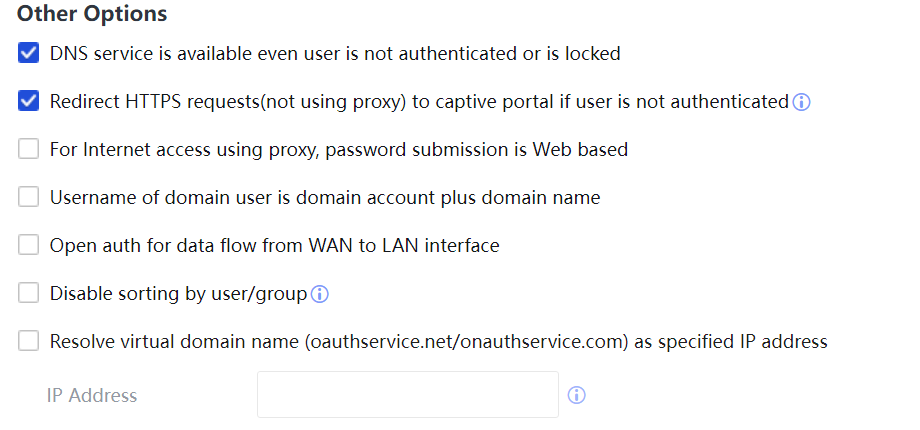
Select DNS service is available even user is not authenticated or is locked to allow users to access the DNS service before being authenticated or after being locked.
When users adopt Password-based open an HTTP web page, they will be redirected to an authentication page. However, they will not be redirected if they access an HTTPS webpage. To redirect users when they access an HTTPS webpage, select Redirect HTTPS request (not using proxy) to captive portal if user is not authenticated.
For Internet access using proxy, password submission is Web based: If this option is selected, the password submission is performed using the Web authentication page for the Internet access using the proxy. If it is not selected, 407 pop-ups are used to authenticate Internet access using the proxy.
Username of domain user is domain account plus domain name can be selected to identify users on different domain servers if there are multiple domains. The domain name is suffixed to the username on the Online Users and Status pages.
Suppose the proxy server is deployed in one-arm mode, and the IAG is deployed in bridge mode between the intranet and the proxy server. In that case, public network IP addresses will be added to the online user list. In this case, Open auth for data flow from WAN to LAN interface needs to be selected to avoid authenticating public network IP addresses.
Disable sorting by user/group: When the user/group query speed is too slow, the Disable sorting by user/group function can be enabled to accelerate the query.
Resolve virtual domain name (oauthservice.net/onauthservice.com) as specified IP address: It is recommended to configure this function because multiple IAG devices exist in the environment/Oauth authentication or QR code authentication is configured in the IAG scenario.
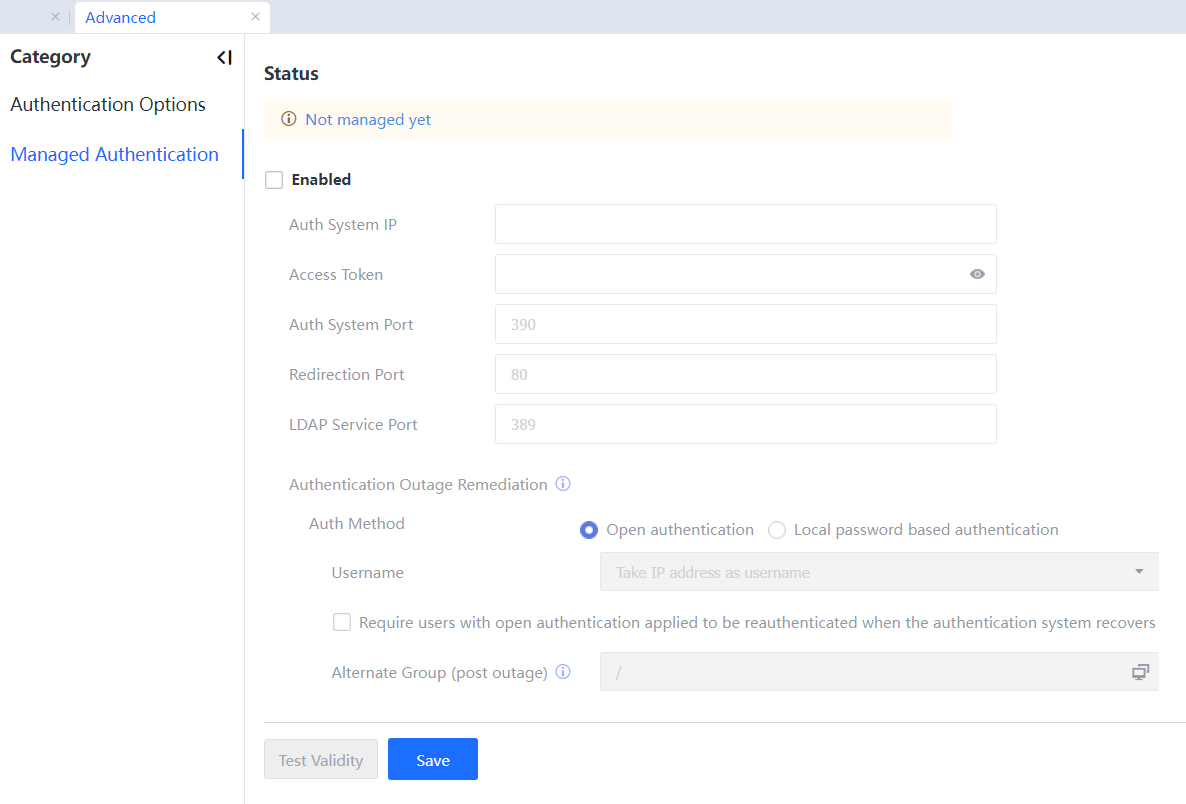
Managed Authentication
- Support configuring managed authentication functions on AC, SG, and IAG devices and implement the managed authentication of users in the authentication system. Enable Managed Authentication, and then the device will enter the managed authentication status.
- After Managed Authentication is enabled, authentication-related functions are implemented in the authentication system, and the following functions will be hidden on the controller device and will not take effect.
- Authentication policy
- User binding
- IP/MAC binding
- User automatic synchronization
- Single sign-on
- Authentication controller
- RADIUS Server
- After Managed Authentication is enabled, Authentication Outage Remediation is supported. When the authentication system is offline, the device is authenticated using the configuration policy of the outage policy to go online. The outage policy supports two methods, including open authentication and password-based authentication.
- Under the managed authentication status, the user going online on the controller does not support synchronously going online on the authentication system, but the user logged off on the controller can be synchronously logged off on the authentication system.
- The managed authentication supports four authentication policy methods: MAC authentication-free, open authentication, password authentication, and authentication not allowed.
- The managed authentication also supports the scenario taking the control device as the proxy server, HTTPS proxy, HTTP proxy, and SOCK5 proxy scenarios.
- The managed authentication supports docking with IPV6 addresses.
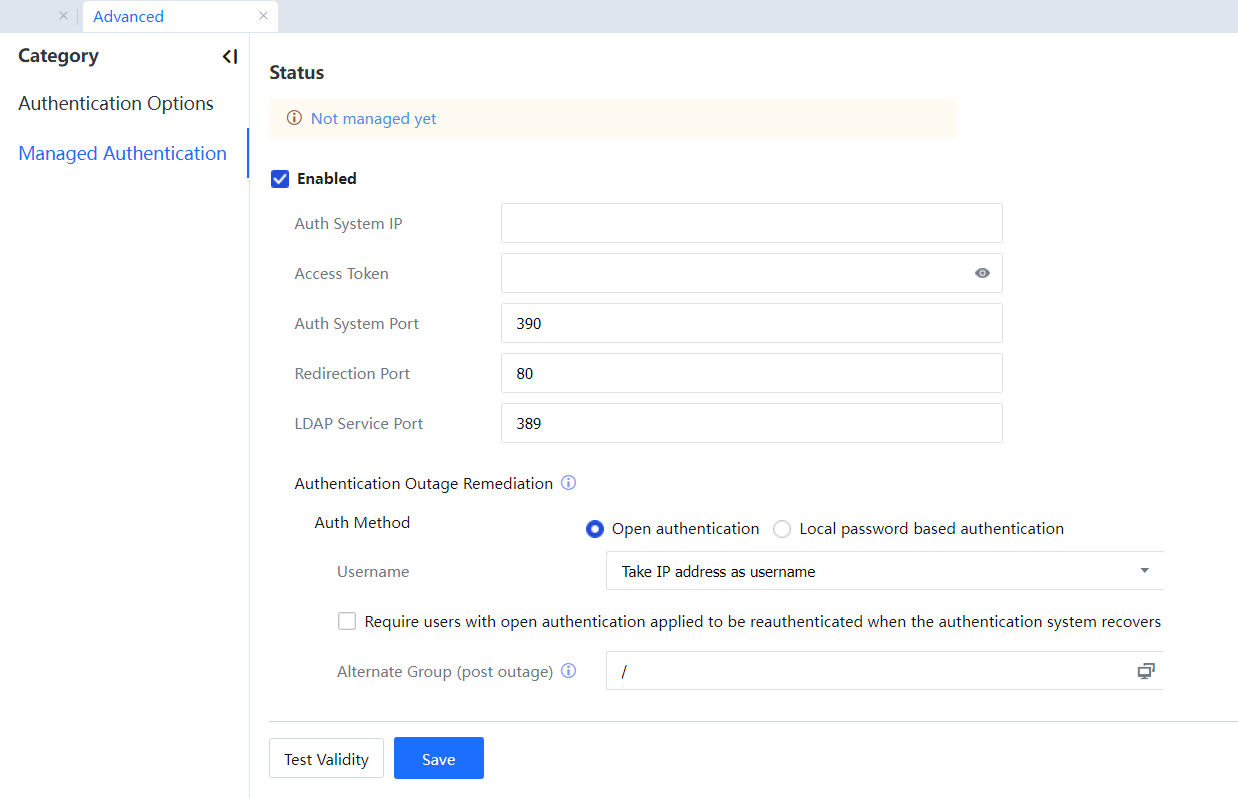
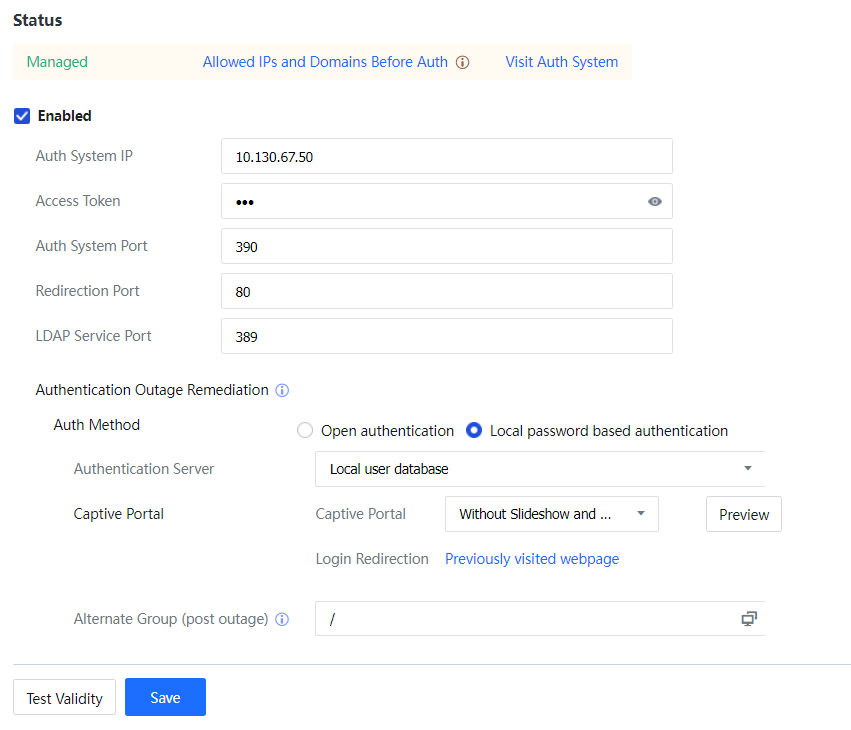
Check Enabled to enable the function.
Auth System IP: Fill in IP addresses from the unified authentication system to the authentication port, supporting IPV4 and IPV6.
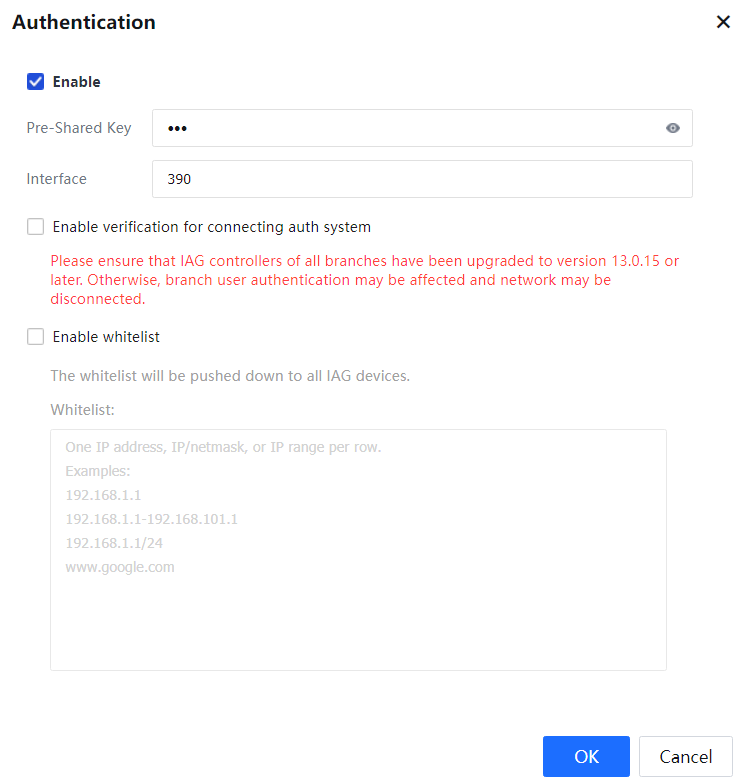
Access Token: It aligns with the secret key for the unified authentication system settings.
Auth System Port: It is a TCP390 port by default, which can be customized in the authentication system.
The configuration of Access Token and Auth System Port in the authentication system are defined in Access Mgt > Authentication > Correlation Connection > Controllers, as shown in the following figure.
Redirection Port: A port used in the authentication redirection page is a TCP80 port by default and can be customized.
LDAP Service Port: The unified authentication system can be used as an LDAP server and takes a TPC389 port as the default port.
Outage mechanism: After Managed Authentication is enabled, Authentication Outage Remediation is supported. When the authentication system is offline, the device is authenticated using the configuration policy of the outage policy to go online. The outage policy supports two methods, including Open authentication and Local password based authentication.
Open Authentication: IP address, MAC address, or hostname can be selected as username.
Local password based authentication: Select the authentication server, the captive portal, and the redirection page after authentication. For the configuration method, refer to the "Add Authentication Policy" section.
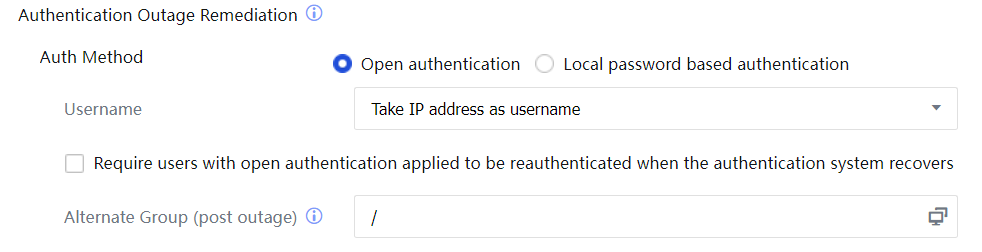
Alternate Group (post outage): Use the configuration policy of the outage policy to authenticate and go online on the user group.
Click Test Validity: This option tests the device's communication situations and unified authentication system.
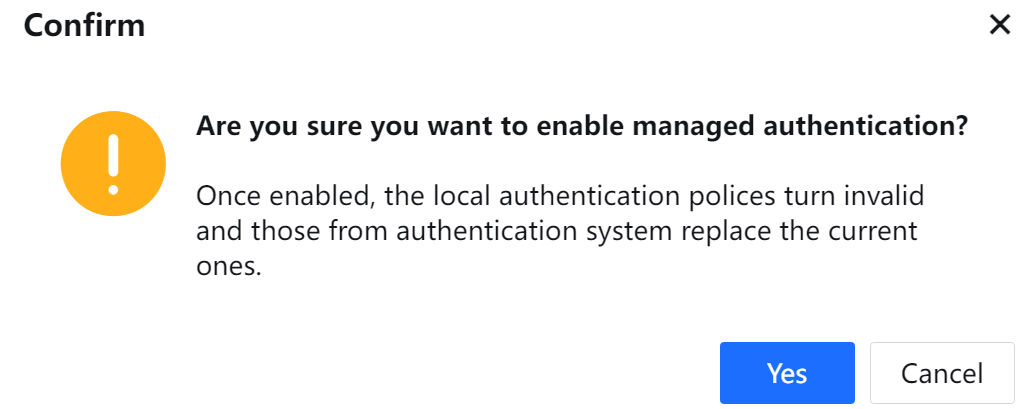
After configuration, click OK[A64] to prompt the following message:
After confirming and submitting, the display device is managed by the authentication system and can skip to the authentication system, as shown in the following figure.
Meanwhile, the unified authentication system displays the device access status: 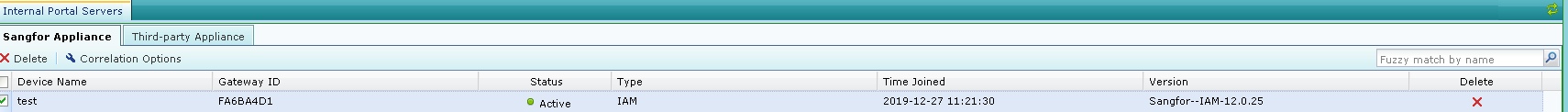
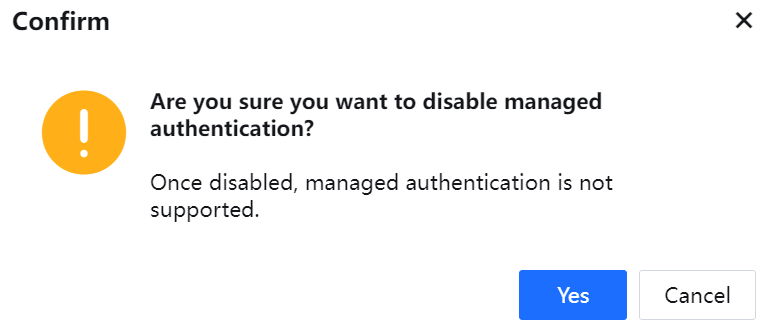
Cancel Enabled and click Yes[A65] to prompt the following message. Please operate carefully.