Correlation connections are for docking with third-party devices, including controller docking, Radius authentication server, and MAC address acquisition across layer three networks.
Controllers
Controller docking includes Sangfor device docking and third-party controller docking, which is suitable for multi-branch scenarios. When Sangfor equipment is connected to the headquarters IAG as the authentication center, it combines the branch Sangfor equipment to do managed authentication to push the authentication page uniformly. Using the third-party controller as a unified authentication server for the IAG connects with the wireless controller to push the unified authentication page to realize unified authentication and the right to follow.
3.5.3.2.1.1 Sangfor Appliance
When IAG acts as an authentication center, it can connect with Sangfor equipment to complete the managed authentication function.
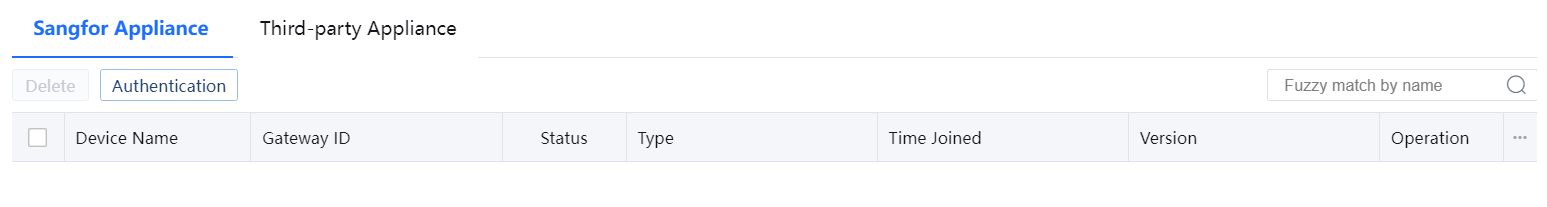
Authentication: Click Authentication to set the authentication center parameters.
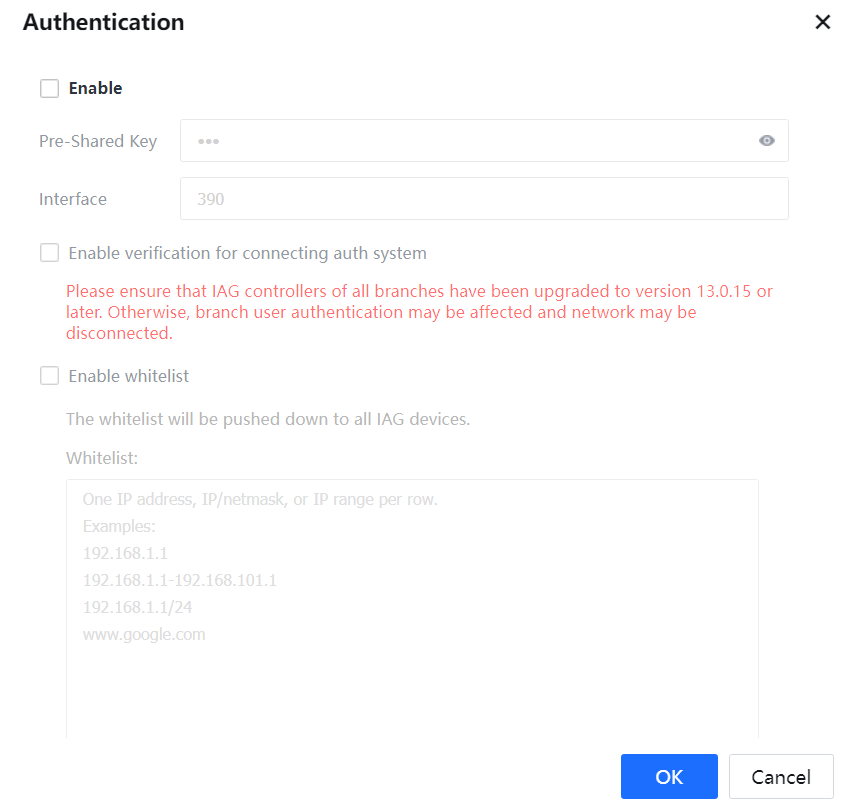
Pre-Shared key: The key used for branch IAG access must be consistent with the connection key of the branch Sangfor device.
Interface: The port used for communication between the IAG authentication center and the branch Sangfor equipment. The default is 390, which can be modified. However, it needs to be consistent with the branch Sangfor equipment authentication center port.

After the IAG authentication center has completed the configuration, it needs to go to the branch IAG equipment to configure the managed authentication. Please refer to the managed authentication chapter. Please refer to the chapter on multi-branch networking scenarios for BBC environment configuration.
3.5.3.2.1.2 Third-party Appliance
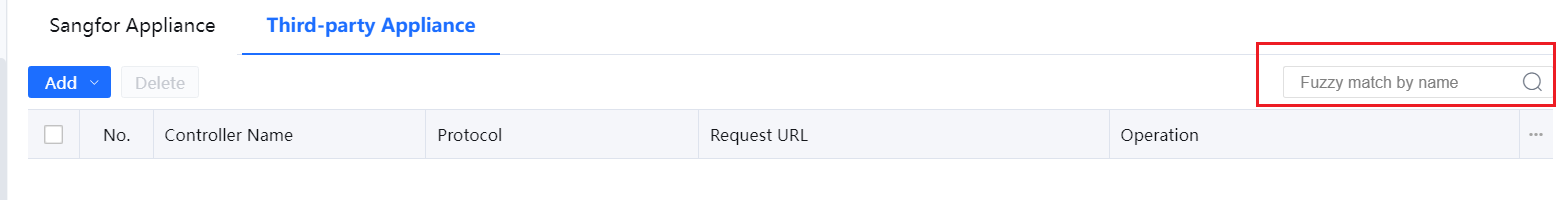
Go to Access Mgt > Authentication > Correlation Connection > Controllers page:
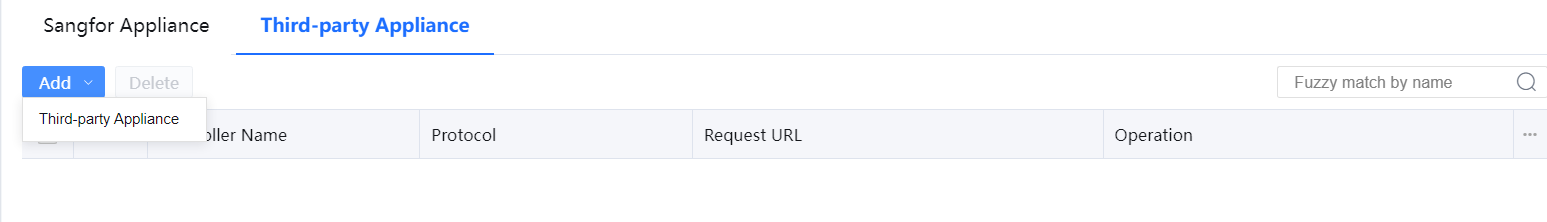
Click Add to add a Third-party Appliance interface as follows:
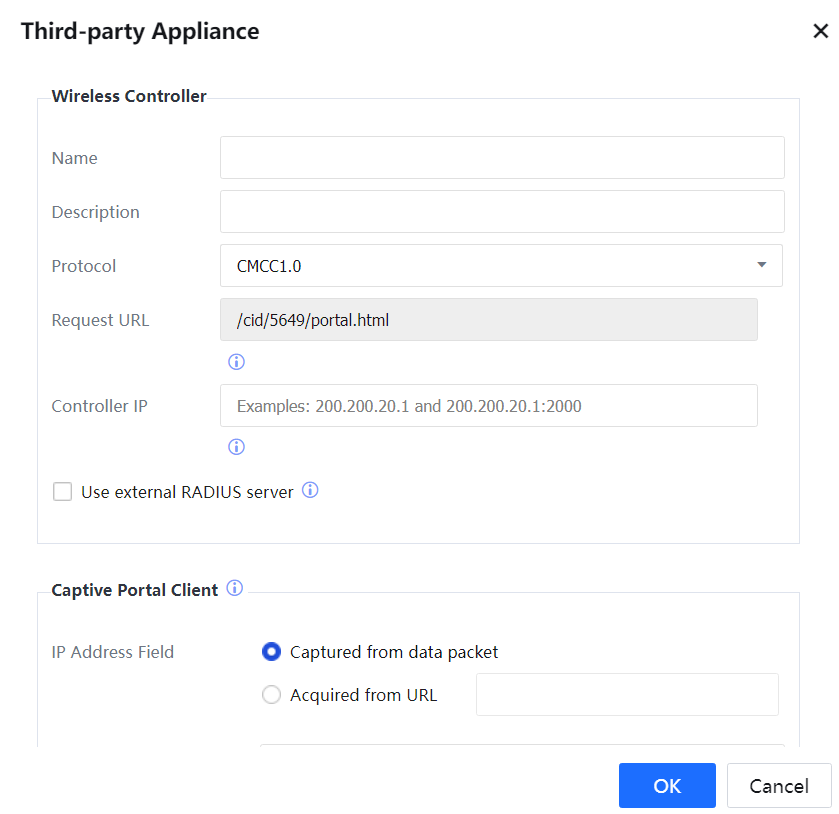
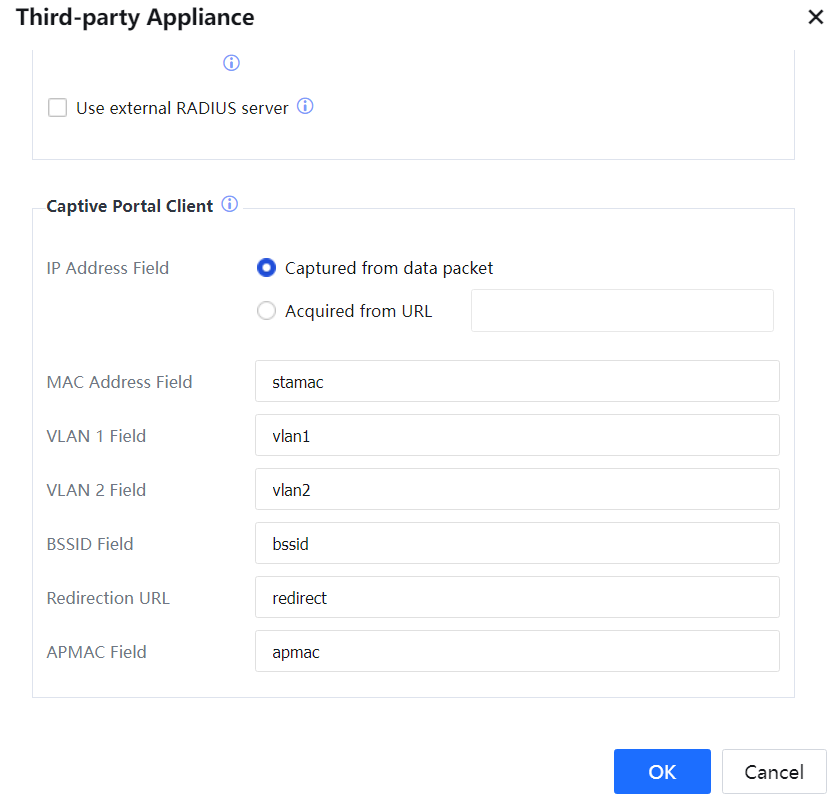
Name: Used to set up the name of the third-party portal server.
Description: The description information of the server.
Protocol: Supported types of portal protocols, currently supporting connection with standard CMCC 1.0, CMCC 2.0 and Huawei Portal 2.0/IMC, Cisco External Portal Web Authentication Protocol, and Aruba Protocol.
Request URL: A URL address will be automatically generated after selecting relevant protocols. When WeChat is enabled to connect to WiFi by QR code, the controller must support carrying AUTHURL and EXTEND parameters in configuring the request URL.
Controller IP: The IP address of the third-party portal controller can be entered with a port. If the port number is not entered, port 2000 will be used by default in connection with CA.
Use external RADIUS server: The authentication system combines the third-party controller for authentication; when the user information is maintained on the third-party RADIUS server, check this option; when the authentication system serves as the RADIUS server, do not check this option. Enable the configuration in Access Mgt > Authentication > Correlation Connection > RADIUS Server, set the port as 1812 and the key as RADIUS, consistent with the third-party controller.
Captive Portal Client:
IP Address Field: The way to obtain the IP address of the client. The field can be obtained from the data packet or the URL parameter.
MAC Address Field: MAC address information of the third-party controller.
VLAN 1 Field: Field information is contained in the data packet of the third-party controller.
VLAN 2 Field: Field information is contained in the data packet of the third-party controller.
BSSID Field: Consistent with the controller.
Redirection URL: Consistent with the controller.[LCH60]
[61][62]APMAC: MAC address of the wireless AP.
When there is more than one third-party controller's information configuration, you can use the search box in the upper right corner to search for relevant information by name.
RADIUS Server
The device can be regarded as the RADIUS server, and the accounting and authentication ports use mutually exclusive keys.
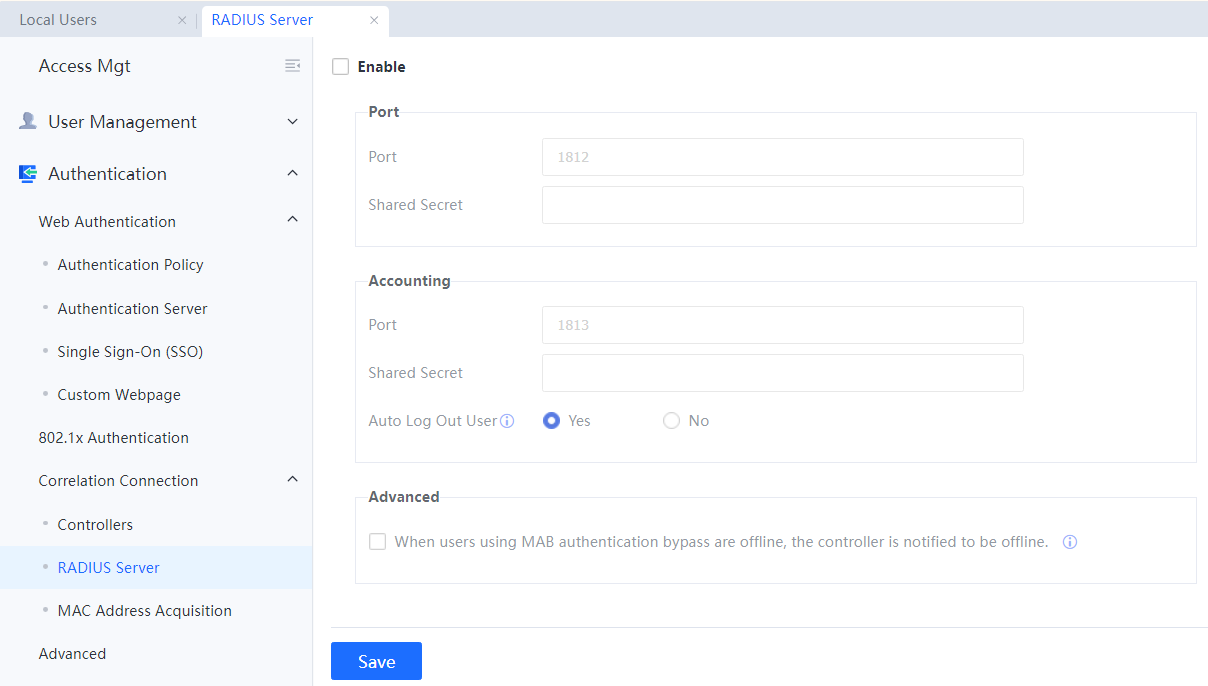
Enable: Select Enable to configure the IAG device as the RADIUS server, and only PAP is supported by default.
Port: Configure ports used by the RADIUS server.
Shared Secret: Configure the secret key of RADIUS.
MAC Address Acquisition
There are two ways to acquire MAC across L3. The setting method is as follows:
- Enable MAC acquisition across L3 network
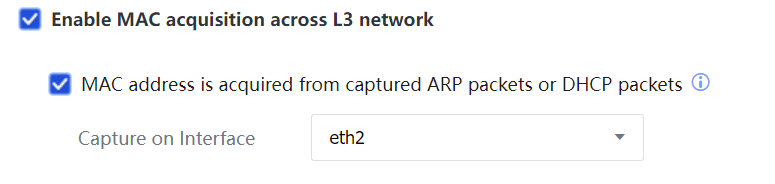
Select MAC address is acquired or from captured ARP packets or DHCP packets to connect any idle network port of IAG to the switch, enable mirror on the corresponding interface of the switch, and mirror relevant data packets to IAG. This method does not require enabling SNMP protocol by the switch.
- Get MAC by configuring across L3.
If intranet users are bound with MAC addresses or the MAC address range is limited, and the intranet covers L3, obtaining MAC addresses across L3 needs to be enabled for obtaining MAC addresses of intranet users. To use this function, ensure that the intranet switch supports SNMP so that the IAG can obtain the real MAC addresses of intranet users from the switch through SNMP.
Principle: The IAG periodically sends an SNMP request to the L3 switch to obtain the MAC address table and saves the table in the memory. Suppose a PC on another network segment accesses the Internet through the IAG. In that case, a PC with the IP address 192.168.1.2 (on a different network segment as the LAN interface of the IAG) accesses the Internet through the IAG will verify whether the MAC address of the packets is the L3 switch. If yes, the IAG will query and verify the actual MAC address based on the IP address 192.168.1.2.
The procedure is as follows:
Step 1.Enable SNMP on the L3 switch.
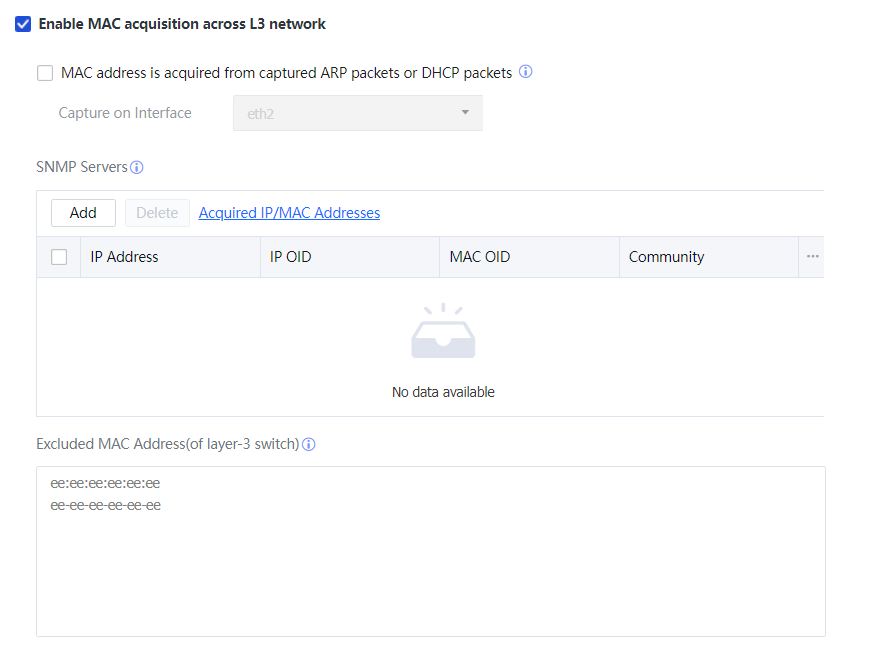
Step 2.Select Enable MAC acquisition across L3 network.
Step 3.In SNMP Servers, enter the information about the L3 switch from which the IAG obtains MAC addresses.
Enable SNMP for the L3 switch in advance.
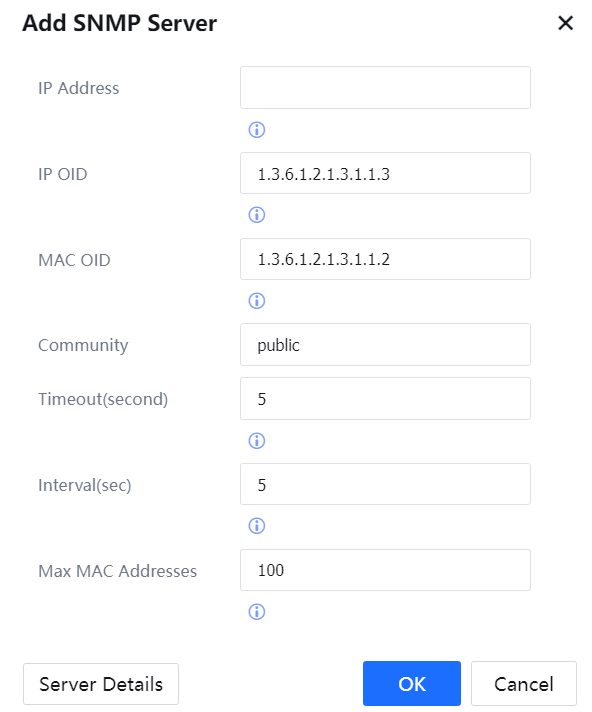
IP Address: IP address of the L3 switch.
IP OID: OID of the IP address in the SNMP information.
MAC OID: OID of the MAC address in the SNMP information.
Community: Key for SNMP negotiation.
Timeout (second): Timeout duration for the IAG to obtain SNMP information.
Interval (sec): Interval for the IAG to send an SNMP request for obtaining information.
Max MAC Addresses: Maximum number of SNMP entries obtained at a time. Click Server Details to view SNMP information on the SNMP server (switch). Click OK to save the settings.
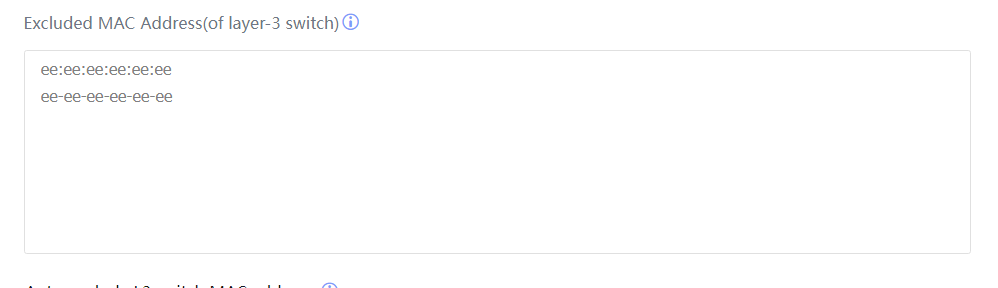
- Enter the MAC address of the intranet switch to avoid being bound with a user, as shown in the following figure.
In addition to the MAC address manually entered in the preceding step, the IAG can automatically discover the MAC address of the L3 switch. The IAG counts the number of IP addresses corresponding to each MAC address every 10 minutes. If a MAC address corresponds to multiple IP addresses, this MAC address is one of the L3 switches.
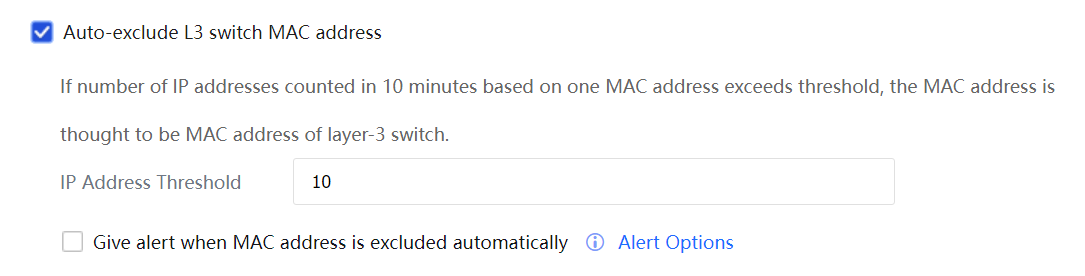
Click MAC Address Calculation.
If Auto-exclude L3 switch MAC address is selected, the IAG will add each MAC address whose count of IP addresses exceeds the specified value of IP Address Threshold to the exclusion MAC address list.
If Give alert when MAC address is excluded automatically is selected, the IAG will send an alarm mail to the administrator after adding a MAC address. Set alert options on the page displayed after you choose System > General > Alert options.




