An enterprise has recently seen records of unidentified IPs that have not passed authentication accessing the intranet server to read confidential files. As a result, it is necessary to control the access endpoints of the intranet strictly. Before the access endpoints pass the authentication, they cannot access internal and external servers. Network resources, authentication using account password authentication. Ensure that endpoints pass authentication when accessing the network to improve the intranet's security.
Demand Analysis
This requirement is combined with IAG local users performing 802.1x authentication on the access endpoint, the switch enables 802.1x, and the endpoint enters the username and password locally created by IAG to complete the authentication and go online. Access endpoints without authentication are not allowed to access intranet resources.
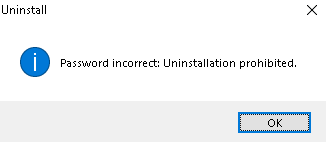
802.1x authentication must first enable the 802.1x network access control function of IAG, use IAG as the Radius server, and configure the corresponding port and server key.
Select user source, local user, and AD domain user are optional;
Finally, configure the policy for post-authentication processing, including the group to which the user belongs, whether to bind the user, restrict user login, and other configurations.
Configuration Steps:
Step 1.Enable 802.1x authentication on IAG. Navigate to Access Mgt > Authentication > 802.1x Authentication to configure. Enable the 802.1X network access control function, and configure the Radius authentication port as 1812, the accounting port as 1813, and the server key as 123. The authentication server enables local password authentication.

The configured Radius port cannot conflict with the Radius authentication server in the linkage interconnection settings.
IAG has two built-in Radius servers. Free Radius is for 802.1x authentication. The Radius in the correlation connection setting is used in the Portal connection. The two ports can be opened at the same time if there is no conflict.
If there is a conflict, please modify the port of the Radius authentication server in the linkage docking settings and configure it to another port.
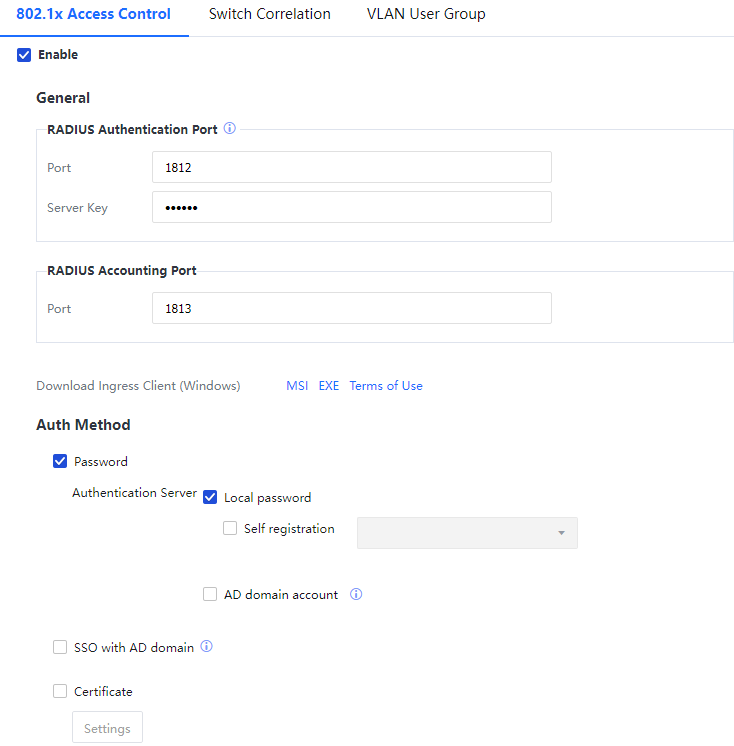
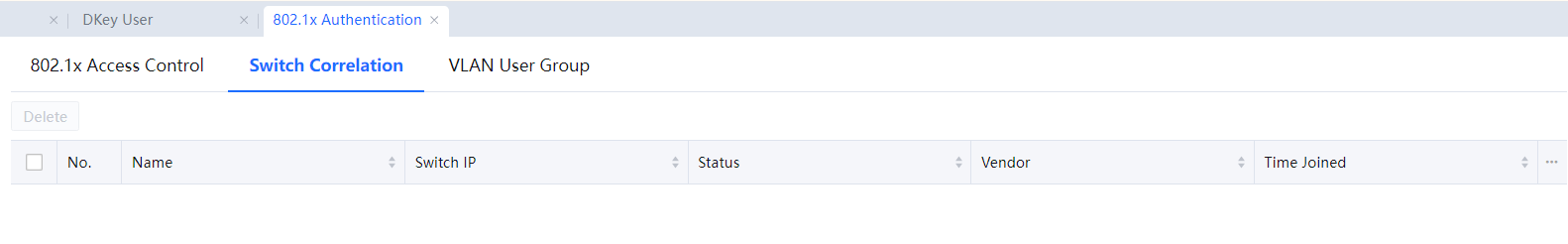
Step 2.Navigate to Access Mgt > Authentication > 802.1x Authentication > Switch Correlation to view the switch status when authentication data is sent to IAG.
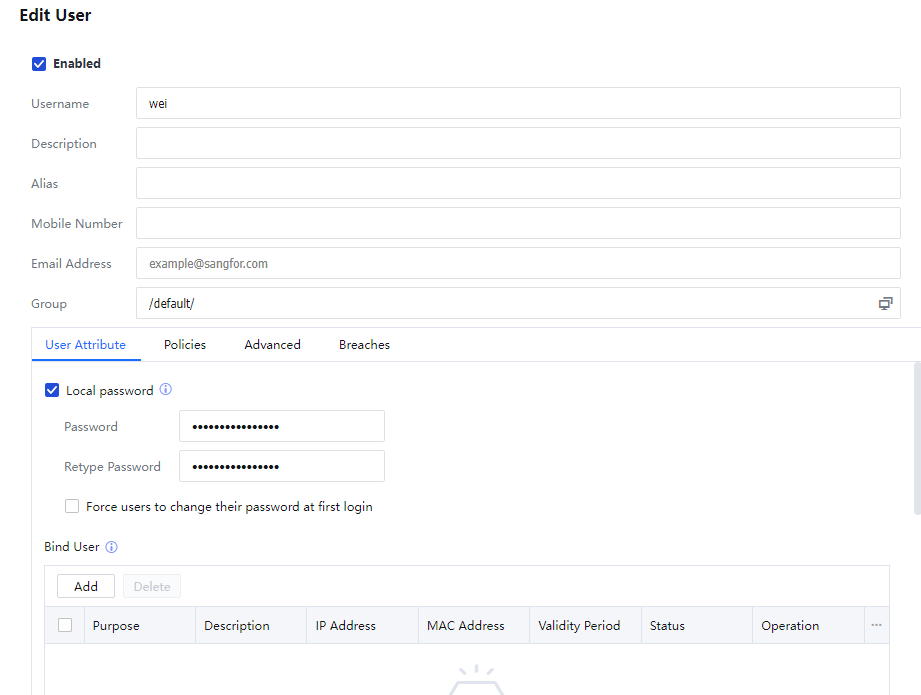
Step 3.Navigate to Access Mgt > User Management > Local Users, click Add > User, fill in the username and Local password, and click OK.
Step 4.Interconnect the switch with 802.1x configuration. Enable the 802.1x function on the corresponding switch, select Radius as the authentication server, and map the radius server to IAG.
Step 5. IAG needs to obtain the corresponding relationship between the endpoint's IP and MAC address for the user to go online. There are four ways to go online:
1. The Radius accounting message of the switch carries IP information and sends it to IAG (most of the manufacturer's accounting messages will carry IP information. If you find that it does not carry IP information, please contact the manufacturer's engineer to configure)
2. Switch configuration: The mirror port is connected to the IAG mirror port, and the traffic goes online;
3. Obtain the MAC address from ARP and DHCP messages, or obtain the MAC address across three layers through SNMP;
4. The endpoint that uses the authentication assistant to log in to 802.1x will report the IP and MAC address information to the IAG device. It is recommended to use accounting packets. (If the manufacturer's switch does not carry the IP in the accounting packet, please refer to the SNMP configuration chapter).[LCH41]
Step 6.Authentication Assistant Configuration.
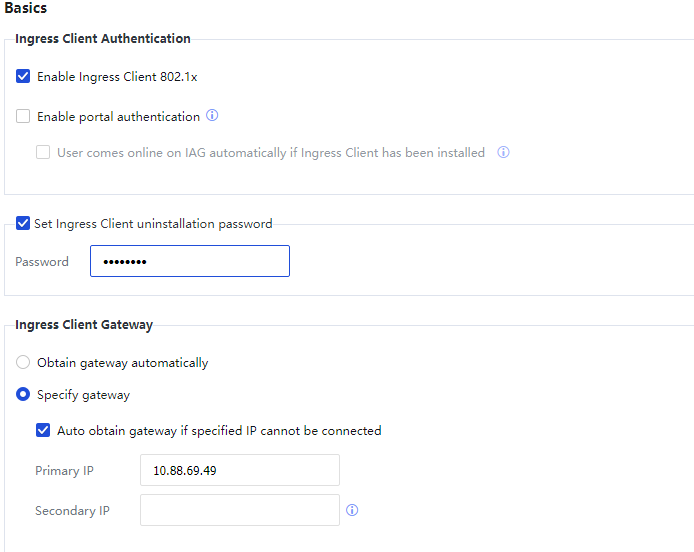
In Access Management > Ingress Client Settings, select Enable Ingress Client 802.1x and Set Ingress Client uninstallation password, and enter the password. Fill in the IAG device IP address in Specify gateway under Ingress Client Gateway address. Under Installation Reminder, select Remind users to install Ingress Client and Allow Internet access. The authentication assistant downloaded after selecting Enable Ingress Client 802.1x in the IAG console will generate an authentication assistant shortcut for entering the account password.
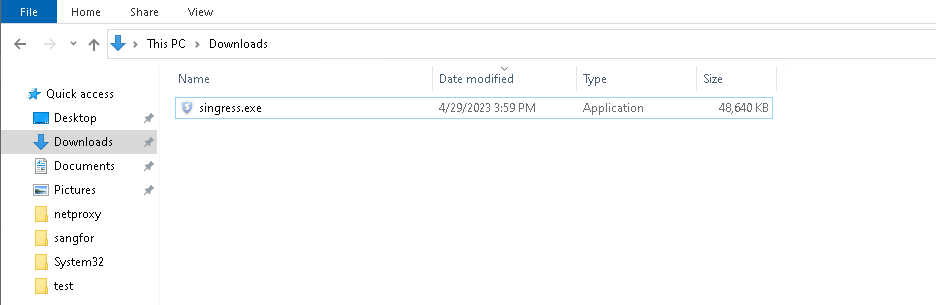
Step 7.Download the Ingress Client on the IAG device web console, and install singress.exe with administrator privileges. The download link shortcut will only be generated when the 802.1x Access Control is enabled.
Step 8.After the installation, a shortcut will be generated on the desktop. Double-click to run.
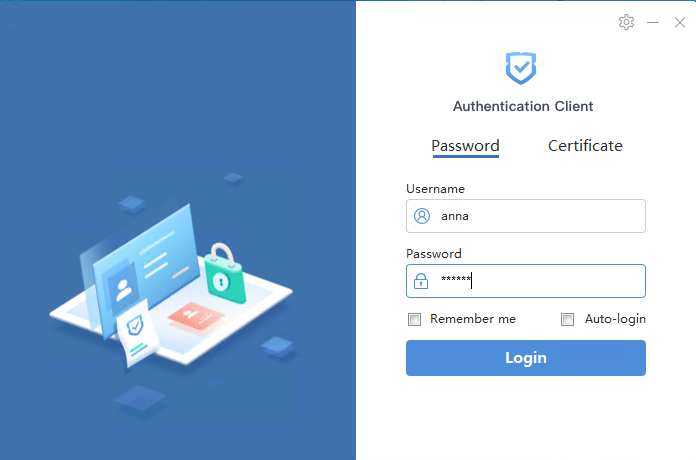
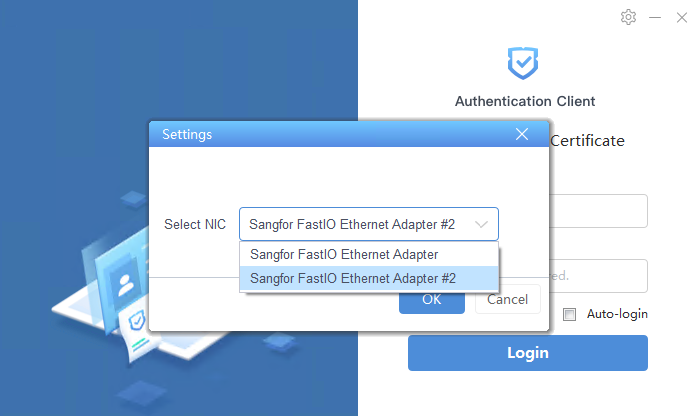
Step 9.When using the Authentication Client, select the correct NIC in the upper right corner and click Login.
Configuration results
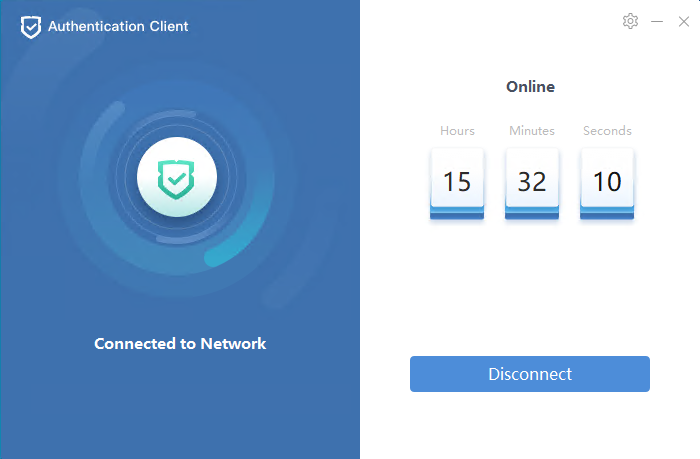
- The online time will be displayed after successfully logging in.
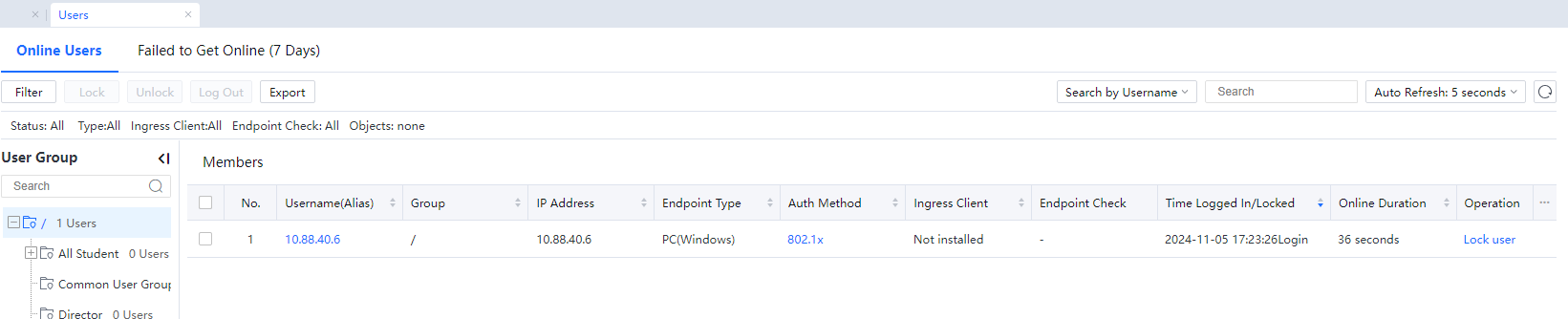
- Navigate to Status > Users, you can see the user's online status, and the authentication method is 802.1x.
 [A42]
[A42]
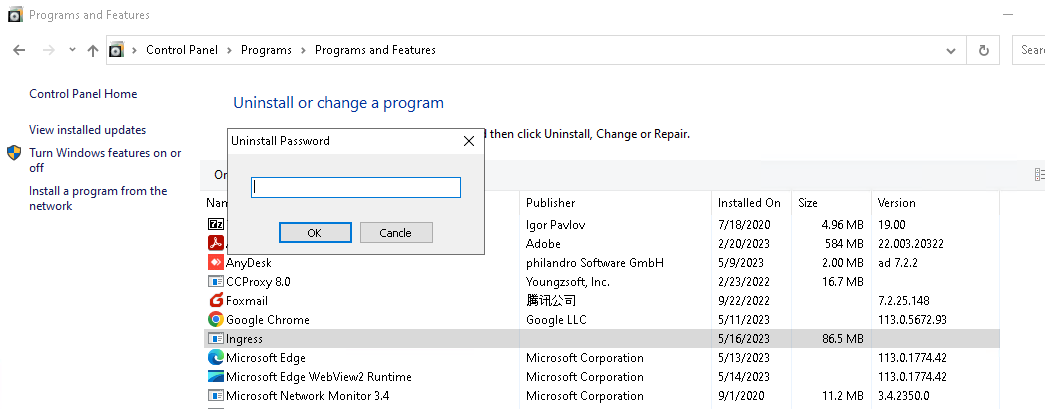
- Select the ingress program in PC Control Panel > Programs > Program and Features > Uninstall or change a program, and click Uninstall. You will be prompted to enter the Uninstall Password. You need to enter the correct uninstallation password (the Ingress client uninstallation password set in the Ingress Client Settings) to uninstall the program. Otherwise, it will prompt "Password incorrect: Uninstallation prohibited".