802.1x authentication is mainly used in scenarios where the internal network is strictly controlled. The requirement in this scenario is that the internal network cannot be accessed (including Layer 2 networks) without authentication and cannot pass through Layer 2 switches. The advantage is to achieve strict network access control. If there is no authentication, the Layer 2 network cannot be accessed, preventing illegal users and endpoints from accessing the network, and they cannot access the intranet without authentication.
802.1x Authentication Bypass: This feature needs to be enabled on the switch at the same time. IAG will divide the bypass users into the bypass VLAN if this feature is enabled.
If this feature is not enabled and the bypass VLAN is configured on the switch, when the IAG is down or disconnected for a long time, the end user will automatically enter the bypass VLAN to ensure normal network access.

Please confirm that the escape function has been configured on the switch. If the switch is not configured with the escape function, enabling the 802.1x escape function will cause the endpoint to fail to access the network.
Basic Configuration:
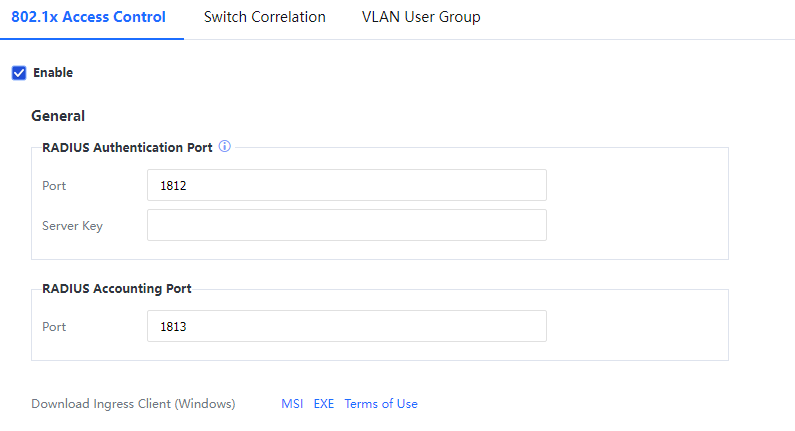
Configure the RADIUS Authentication Port and RADIUS Accounting Port. The authentication port is 1812 by default, the Server Key must be consistent with the key configured on the switch, and the accounting port is 1813 by default.
Ingress ClientDownload:
After updating the Ingress Client function configuration, please click Submit first and then Download. There are two ways to install the Client: MSI installation package and EXE installation package. (The built-in AD domain installation access configuration method document in the MSI compressed package).

1. The admission client installed by MSI cannot prevent uninstallation, and it is usually used in combination with the AD domain controller to push.
2. The EXE package prevents uninstallation of the accessing client and needs to be used in conjunction with Set Ingress Client uninstallation password in Access Mgt > Ingress Client Settings.
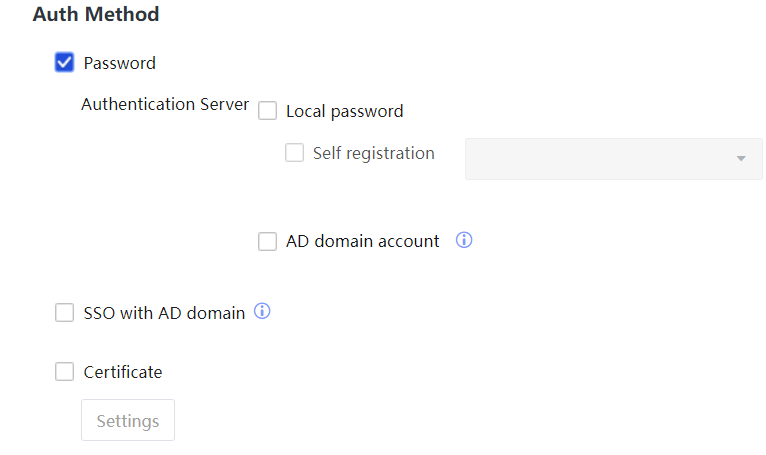
Auth Method:
• Password Authentication
There are two options:l local password and AD domain account. The user source of the local password is the local user that needs to be created in User Management. The source of the AD domain account is the AD domain, and the IAG device needs to join the domain. After the client submits the username and password, the IAG submits it to the AD domain for verification. After the AD domain returns the verification result, the IAG notifies the switch whether to allow access according to the result.
• Certificate Authentication
When the enterprise already has a CA certificate center and has issued a trusted personal certificate to the user, IAG combines the enterprise's CA certificate to enable 802.1X authentication on the access switch. The network access endpoint selects the certificate authentication on the accessing client and then imports the personal certificate issued by the enterprise to complete the authentication.
• SSO with AD Domain
It is suitable for seamless connection with the existing AD domain of the enterprise. After the user successfully logs in to the AD domain, it will automatically pass the 802.1X authentication between the IAG and the switch, and there is no need to enter the account password again for authentication.
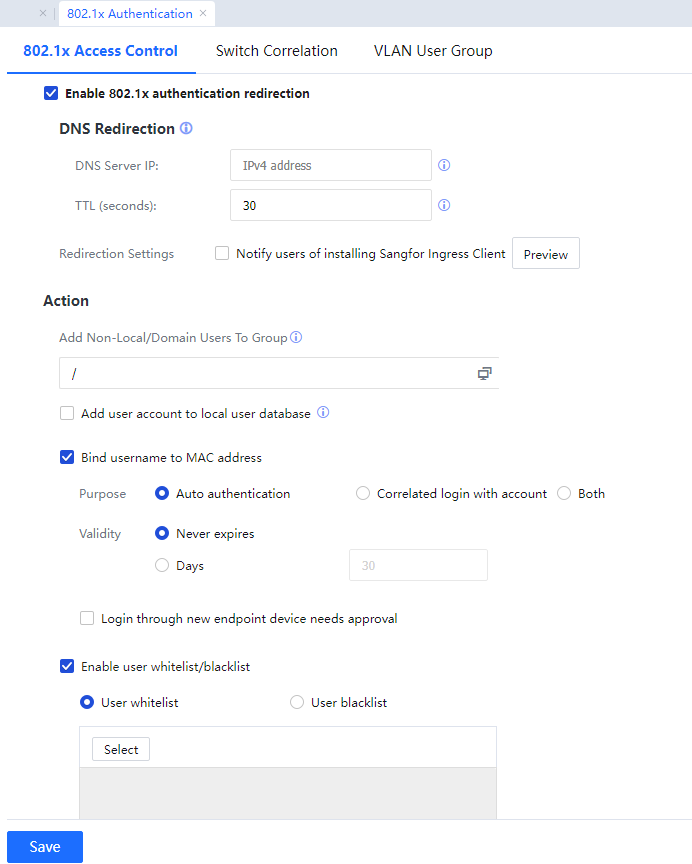
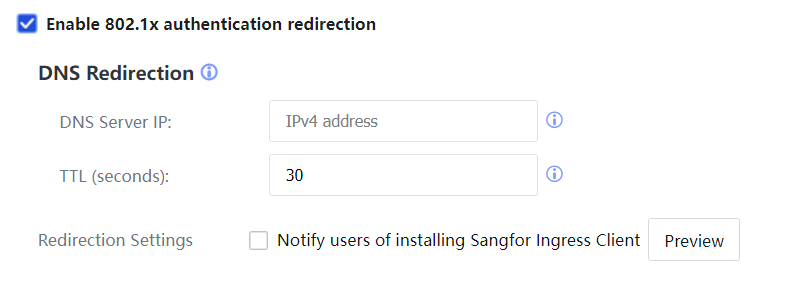
Enable 802.1x authentication redirection:
• DNS redirection: Configure the DNS redirection function to implement the redirection function before 802.1X authentication to push the admission client and self-registration functions before authentication.
• DNS Server IP: The server IP address used for DNS redirection must be on the same network segment as the DMZ management port address of IAG and cannot reuse the IP address of the management port.
• TTL (seconds): The default is 30 seconds, range: between 1 to 86400 seconds.
• Redirection Settings: Set the page to remind users to install and access the client.
Action
After completing the authentication, post-authentication processing is used to configure the user group to which the user belongs.
- Select Add Non-local/Domain Users to Group for online authentication. Users in the local group structure will go online with the local group, and non-local/non-domain users will go online with the specified group.
- Add user account to local user database, where the attribute value is optional: Allow multiple users to log in with one account concurrently, or Only one user logs in with an account.
- Bind username to MAC address. For detailed configuration, refer to the User Binding Management chapter. When the user changes to a new endpoint and requires approval, please enable Login through new endpoint device needs approvals.
- Enable user whitelist/blacklist: Add a custom whitelist or blacklist to allow or disallow specific users to log in.
Advanced
• Force user to log out: It forces 802.1X users to log out on the IAG. The RADIUS CoA/DM function needs to be configured on the switch to enable this function. (The CoA message dynamically changes the network user's attributes when the user is not offline, and the DM message interrupts the user connection.