User binding management is usually used for password authentication and can also be used in scenarios where the administrator defines a username that does not require authentication. It mainly includes user binding, IP/MAC binding, and WeChat ID binding.
User binding: When you need to restrict a username to only log in on a specific IP or MAC address and require the bound IP or MAC to be used only by this user, you need to use the user binding function.
IP/MAC binding: Binding the user's IP address and MAC address can facilitate the administrator's unified management of intranet users and realize one-person, one-machine real-name management. In addition, the IP address and MAC address are bound in two directions. When the user is authenticated, it will verify whether the user's IP and MAC comply with the binding relationship. If one item is incorrect, the authentication will fail. To prevent users from modifying the IP at will on the intranet.
WeChat ID binding: As WeChat officially reclaimed open ID-related permissions, WeChat authentication cannot be used. The WeChat ID binding here also loses its original function. If there are updates in the future, the Sangfor team will notify you as soon as possible.
User Binding
User binding methods include automatic binding and manual binding.
Automatic binding: When the administrator configures the authentication policy, he can go to the action option to automatically bind the binding relationship between the user and IP/MAC, and you can choose to bind IP, MAC, or IP and MAC. The binding supports setting the validity period.
Manual binding: The administrator can bind the users when adding users in Access Mgt > User Management > Local Users. Please refer to the Add New User section. The user binding configuration instructions are as follows.
Step 1.In Access Mgt > User Management > User Binding Mgt > User Binding Mgt, and click Add. The Add dialog box appears.
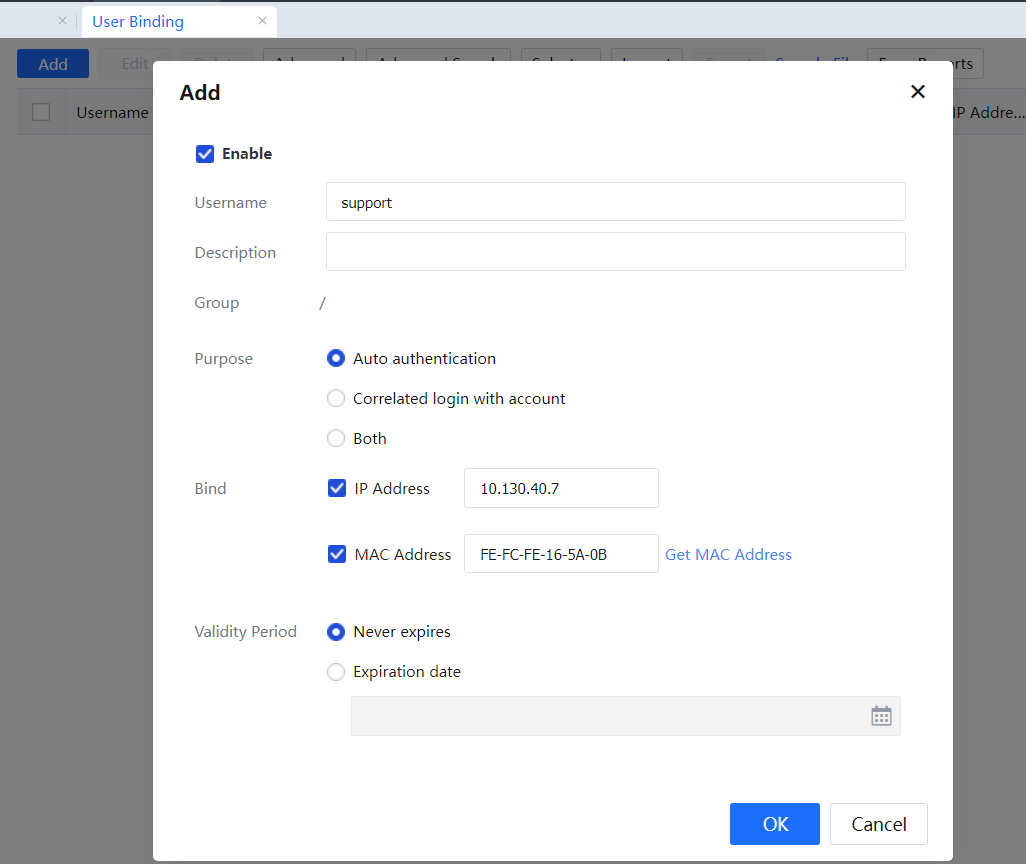
Step 2.Select Enable and set the Username and Description. The username can add binding relationships to users in the local IAG organizational structure and binding relationships to users authenticated by a third-party server. If these users are not added to the IAG's organizational structure, the binding relationship is still valid as long as the username is known.
Step 3.Select the binding purpose for auto authentication, including auto authentication, correlated login with an account, auto authentication, and correlated login with an account.
Step 4.Set binding object: select whether the user is bound to IP or MAC.

If the administrator does not know the MAC address of the endpoint used by the user when binding the MAC, click Auto assigned and enter the IP address of the user endpoint to obtain the MAC address automatically.
Step 5.Set the binding validity period. Specifically, select Never expires or Expiration date as needed. If you select Expiration date, specified the specific expiration date.
Step 6.Click OK. The user binding is successful.
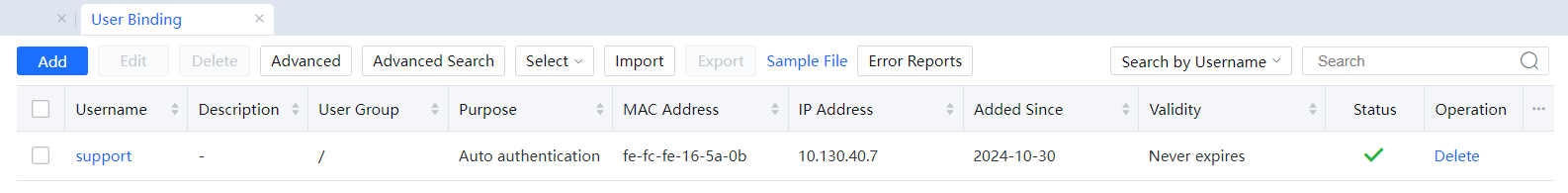
Administrators can add, batch edit, delete, advanced search, advanced settings, select, and import/export in user binding. You can also download the example file for reference.
Edit: Click Edit to configure the description information and auto authentication settings for multiple bound users at a time.
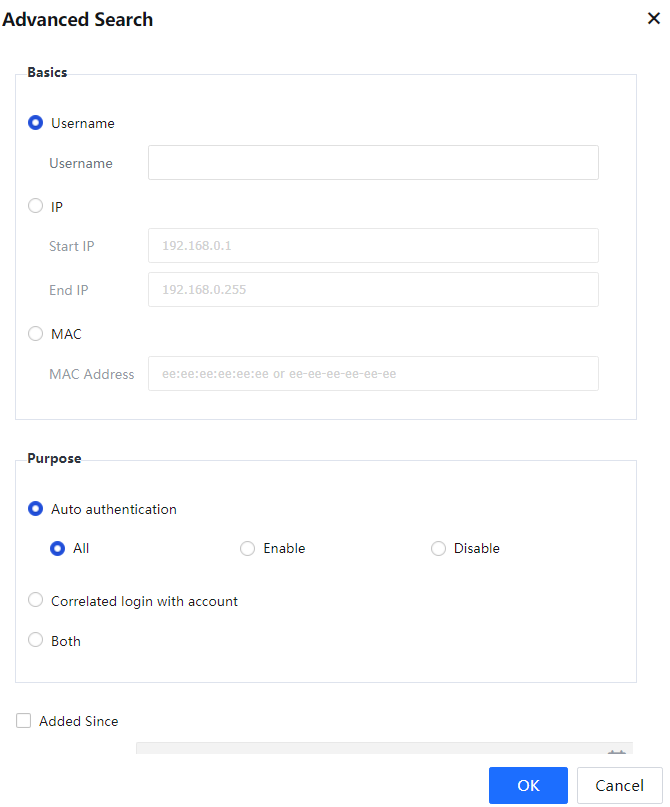
Advanced Search: Click Advanced Search to search for users based on basic conditions such as the username, IP address, or MAC address. According to the binding Purpose, you can filter the users in the list by the time since added and the account expiration time.
Example file: Click Example File to download the sample template and fill the template information as instructed.
Error Reports: Click Error Reports to view the user binding error report during authentication.
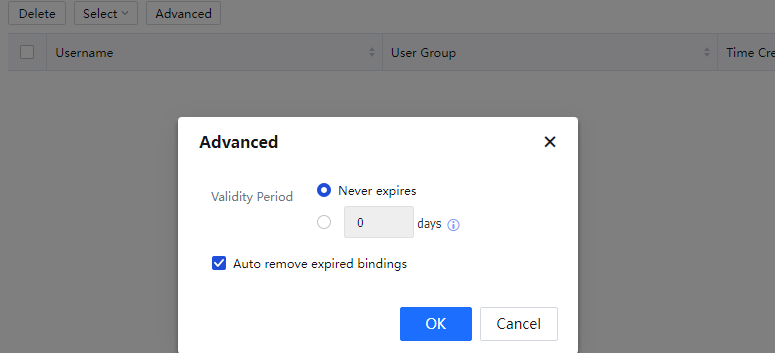
Advanced: Click Advanced to configure advanced settings. For more information about how to configure advanced settings, see the instructions in the advanced options.
IP/MAC Binding
IP/MAC binding function imports in batches and binds the IP address and MAC address in two directions. When the user is authenticated, it will verify whether the user's IP and MAC confirm the binding relationship. If one of them is wrong, it will not pass the authentication to prevent users from modifying the IP at will on the intranet.
The administrator can delete, import, and export the corresponding policy. When many policies are in the list, you can search based on IP/MAC, enter the description information, and press the Enter key to search.
Secret Key Binding
This module is used to manage the TOTP (Time-based One Time password) secret for Google Authenticator and Microsoft Authenticator usage.
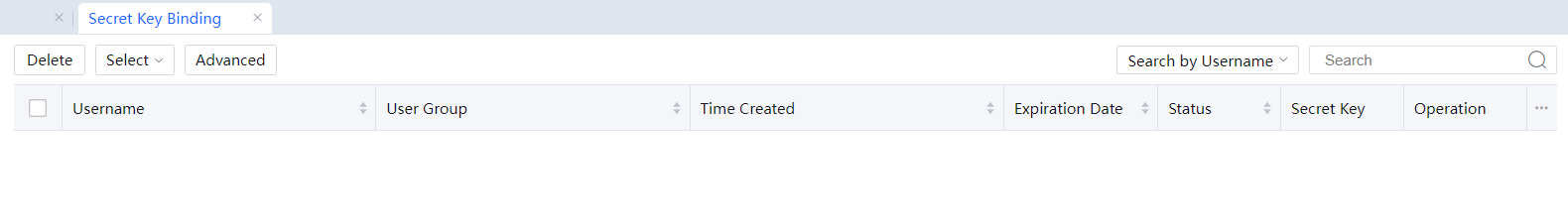
Navigate to Access Mgt > User Binding Mgt > Secret Key Binding, and click Advanced to set the Validity Period.