Suppose a database system is deployed for storing and managing user authentication information and the organization structure. In that case, SQL statements can be configured on the Sangfor IAG to query the user list, authenticate users from the database system, and synchronize the information to the local organization structure and online user list by implementing SSO by working with the database system. After a user is authenticated in the database, the user is automatically authenticated on the IAG. When the user is logged out of the database, the user is also logged out of the IAG. Currently, the supported database types include Oracle, MS SQL Server, DB2, and MySQL. See the following figure.
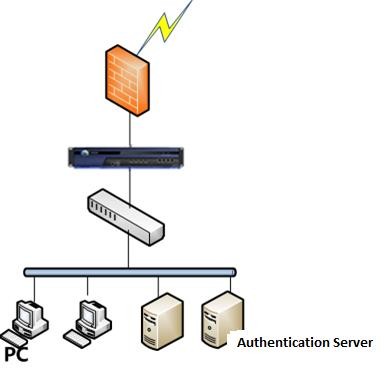
The data flow is as follows:
- The authentication server authenticates a PC, and the authentication information is updated to the database server.
- The IAG regularly queries the database server for online users and updates its online user list.
- The PC accesses the Internet as an online user whose information is obtained by the IAG. The procedure is as follows:
Step 1.Set the authentication policy. Navigate to Access Mgt > Authentication > Web Authentication > Authentication Policy and click Add to set the authentication policy according to the IP or MAC addresses of the users who require SSO.
Step 2.Navigate to Access Mgt > Authentication > Web Authentication > Auth Server and set the database server.
Step 3.Choose Users > Single Sign On SSO > Database and perform configuration.
Select Enable Database SSO, select the Database Server, and set SQL Statement for queries.
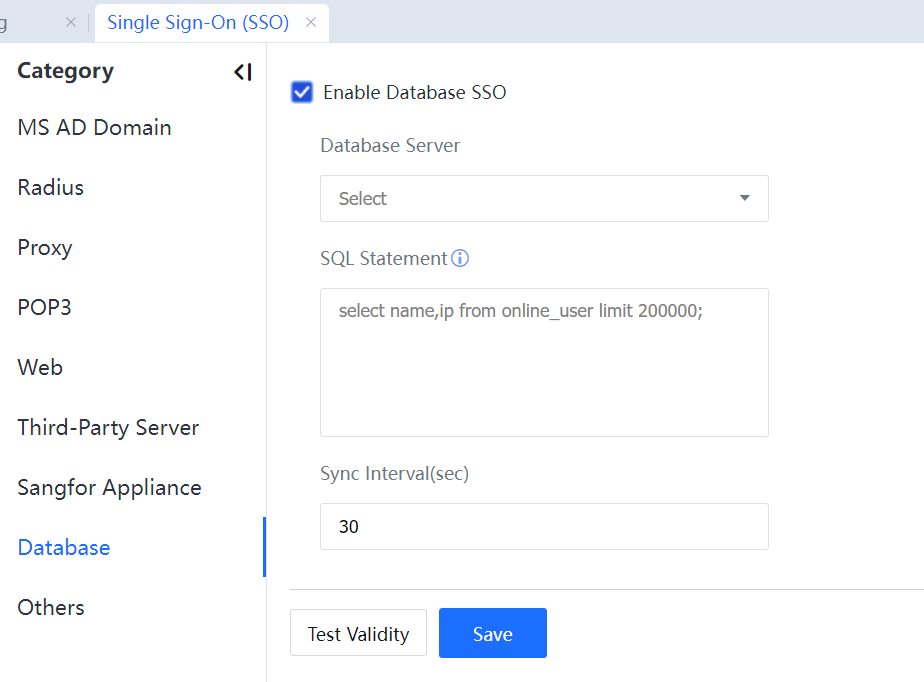
Set Database to the database server that was set in Step 1.
Set SQL Statement to the select statement that can query online users. The IAG runs this select statement to query online users in the user information table of the database. The result set returned by the SQL statement cannot contain more than two columns. The first column specifies usernames, and the second specifies IP addresses. The number of records found cannot exceed 200,000.
The default value of Sync Interval (sec) is the 30s. Generally, it indicates the maximum duration from when a user is authenticated on the authentication server to when the user is authenticated on the IAG.

1. The online user list consists of only the username and IP address columns. It does not support synchronization of other user attributes, such as the attributes indicating whether a user account is disabled or expired. By default, all the user accounts synchronized are enabled and never expire.
2. Database authentication allows automatic user information synchronization, which is set at Access Mgt > User Management > Users Sync.
3. In some cases, a user is authenticated by the IAG (depending on the settings of Sync Interval (sec) after being authenticated by the authentication server. Therefore, it is recommended that the authentication policy be configured not to require user authentication after an SSO failure.




