Generally, it applies to customers who have their web servers, and the web servers store account information. A customer wants its web server and the device to authenticate users simultaneously before they access the Internet. It applies to scenarios where the web server is deployed within or outside the intranet.
Scenario 1: Web server deployed in the intranet
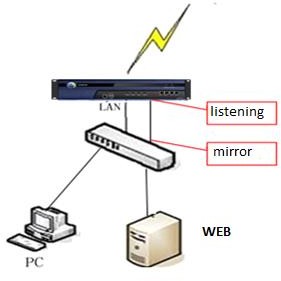
The data flow is as follows:
- A user logs in to the web server. The entire process uses plaintext data, and the device monitors the communication.
- The keywords contained in the feedback sent from the server after authentication are checked to determine whether the user is authenticated. If the user is authenticated, web SSO is successful.
The procedure is as follows:
Step 1.Set the authentication policy. Navigate to Access Mgt > Authentication > Web Authentication > Authentication Policy and click Add to set the authentication policy according to the IP or MAC addresses of the users who require SSO.
Step 2.Choose Access Mgt > Authentication > Web Authentication > Single Sign On SSO > Web and perform configuration. Select Enable Web SSO.
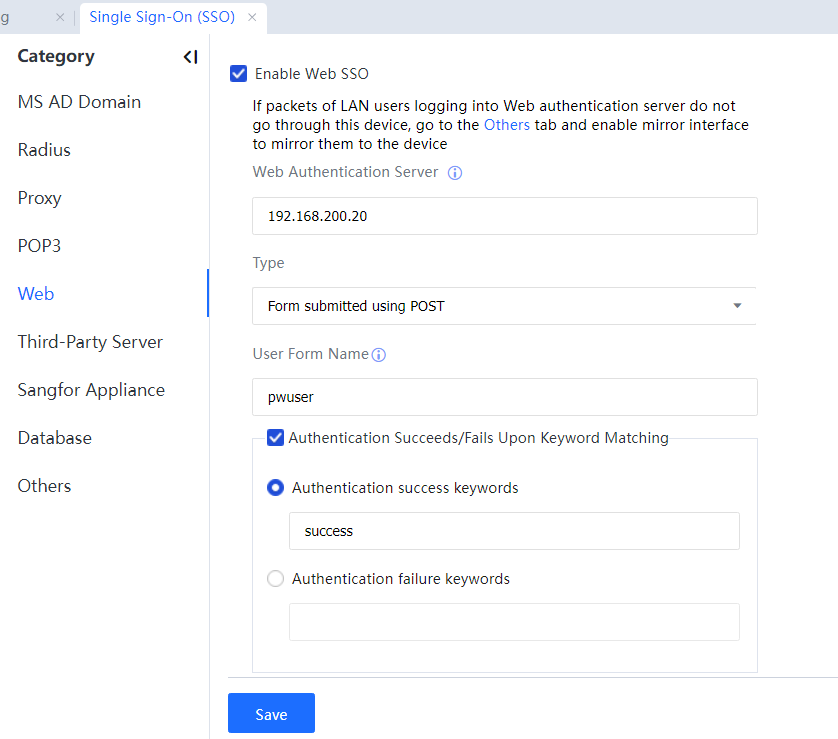
Set Web Authentication Server to the IP address of the web server.
Set User Form Name to the name of the username form submitted to the server during web authentication.
Set Authentication Success Keyword or Authentication Failure Keyword to identify whether web SSO is successful. For example, if you set Authentication Success Keyword and the keyword is contained in the result sent back using the POST method, web SSO is successful; If you set Authentication Failure Keyword and the keyword is included in the result sent back using the POST method, web SSO fails.
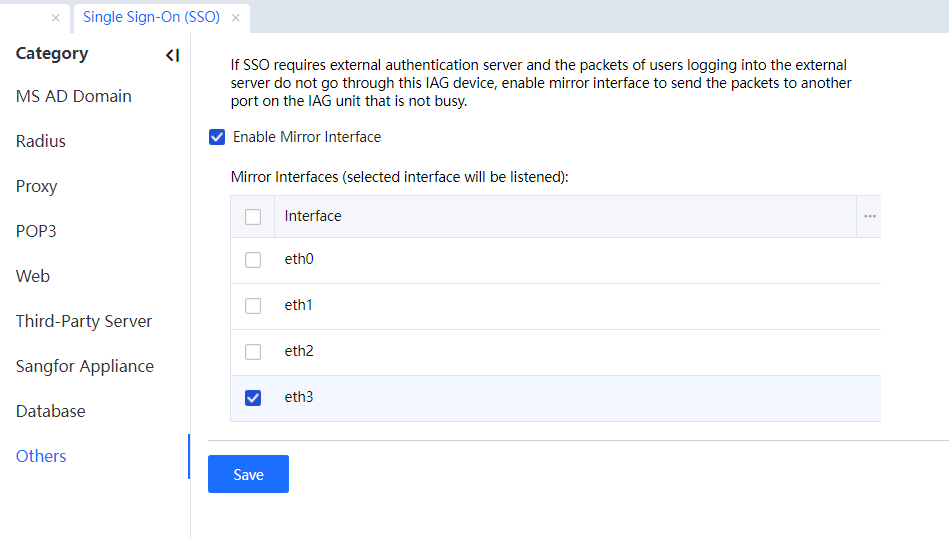
Step 3.In this example, if the login data does not pass through the device, set a mirroring port connected to the mirroring port on the switch forwarding login data packets. Click Others and set the mirroring port. The mirroring port must be an available one not in use.
Step 4.Log in to the specified website on a computer, such as the BBS website in the example. If the login is successful, you can access the Internet.
Scenario 2: Web server deployed out of the intranet.

The data flow is as follows:
- The packets of a PC logging into the web server pass through the device.
- The intranet interface of the device is used as a listening port. No more listening port is required. If the user successfully logs in to the web server, web SSO is successful.
The procedure is as follows:
Step 1.Set the authentication policy. Navigate to Access Mgt > Authentication > Web Authentication > Authentication Policy and click Add to set the authentication policy according to the IP or MAC addresses of the users who require SSO.
Step 2.Choose Access Mgt > Authentication > Web Authentication > Single Sign On SSO > Web and perform configuration. Select Enable Web SSO.
Step 3.Log in to the specified website on a computer, such as the BBS website in the example. If the login is successful, you can access the Internet.




