With antiproxy, users’ Internet access through proxy tools can be detected and blocked, as shown in the following figure.
To detect the use of proxy tools, enable proxy detection. However, proxy tools will not be blocked. To configure anti-proxy, click Settings:
To select proxy tools that you want to detect, restrict or block, click Select next to Proxy Tool, as shown in the following figure:
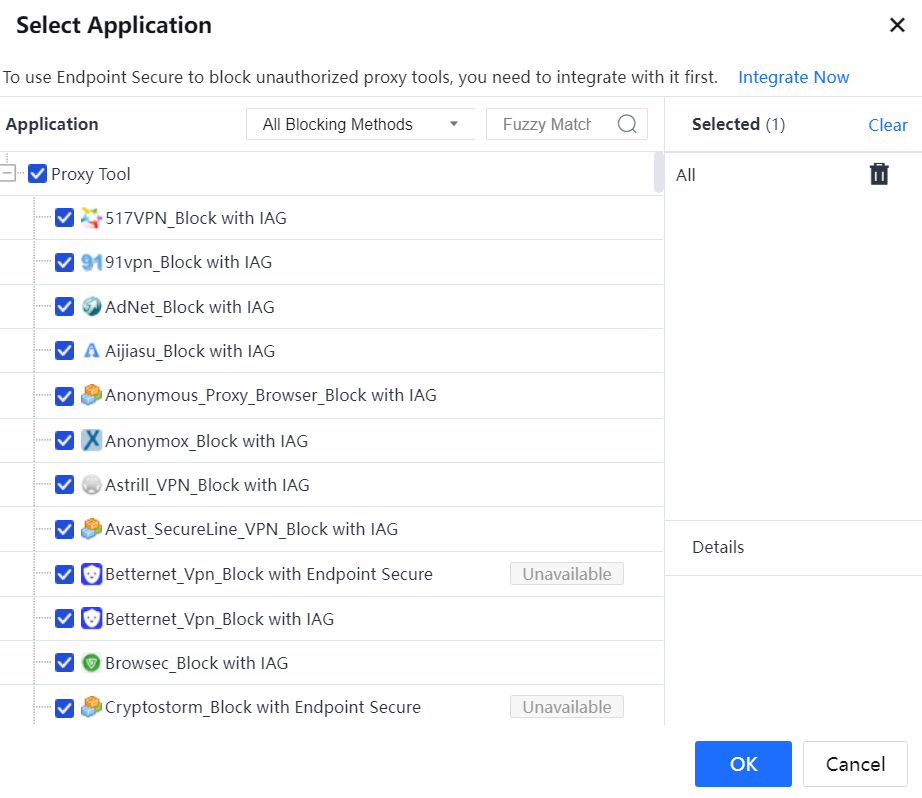
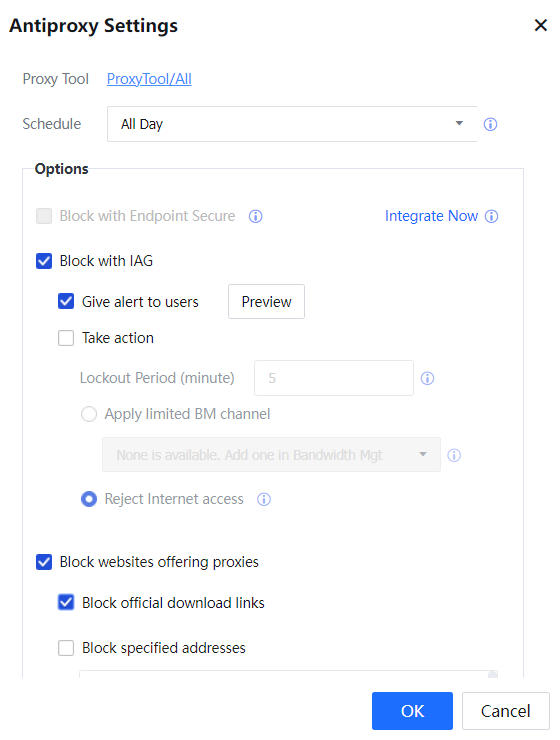
To block specified proxy tools, select With IAG or With Endpoint Secure from the All Blocking Methods dropdown list. The proxy tools application containing With IAG means the block is based on the network flow. The proxy tools application containing With Endpoint Secure means it is required to correlate with Endpoint Secure to block the application based on the process. If that option is not selected, proxy tools will be detected but not blocked.
The details for the correlation block with Endpoint secure can refer to the configuration guide IAG_v13.0.47_Sangfor anti-proxy IAG and ES correlation Configuration Guide.[LCH165][166]
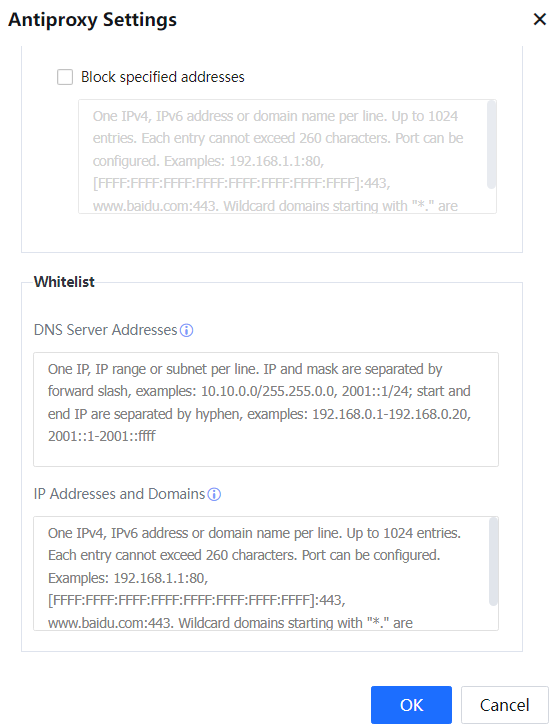
To block official websites that offer proxy tool download, select Block websites offering proxies. It can also add some of the specific URLs or IP addresses in Block specific addresses that offer the proxies services.
It also can add the Internal DNS server to the whitelist inside DNS Server address, to prevent misjudgment, and it also supports inserting the IP address or domain that detects the misjudgment into the IP address and domain whitelist.
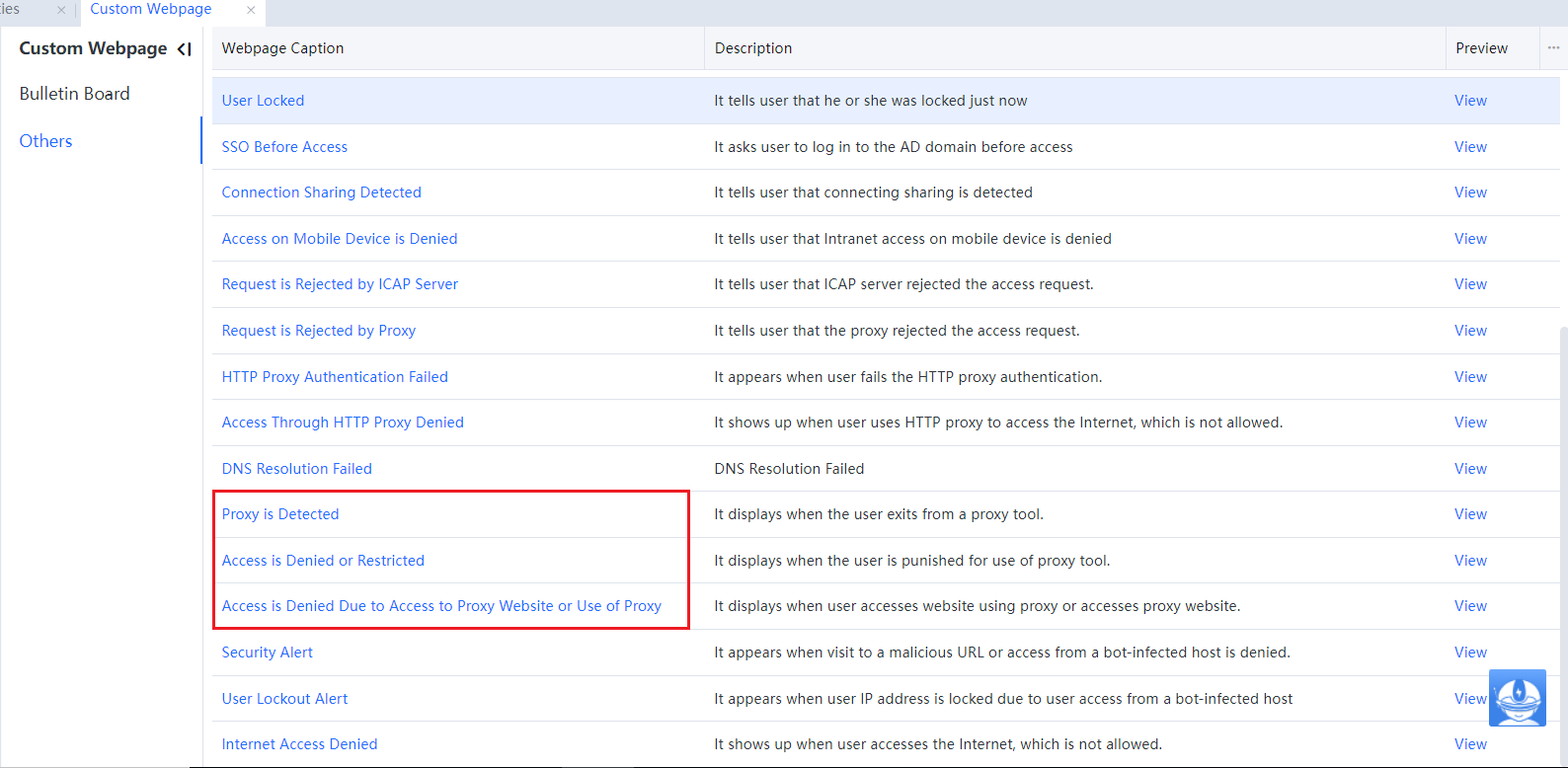
To alert the user when access is denied, select Give alert to user. By clicking Preview next to that option, you may view the webpage to which the user is redirected when Internet access is denied. To modify that webpage, go to System > General > Custom Webpage > Others, as shown in the following figure.
To lock the user when the proxy is detected, select Take action and specify Lockout Period (minute). Moreover, you can Apply limited BM channel or Reject Internet access.
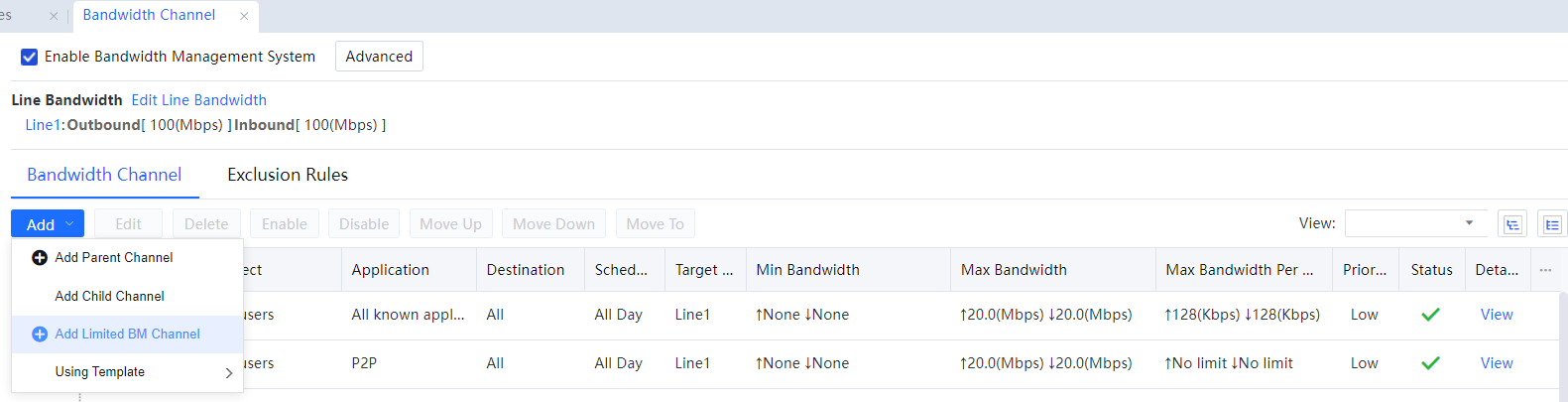
• Apply limited bandwidth management (BM) channel: If this option is selected, you need to select a limited BM channel. If there is no available limited BM channel, you need to add one in Bandwidth Management[A167] > Bandwidth Channel, as shown in the following figure.
• Reject Internet access: If this option is selected, Internet access will be denied when the use of the specified proxy tool is detected.
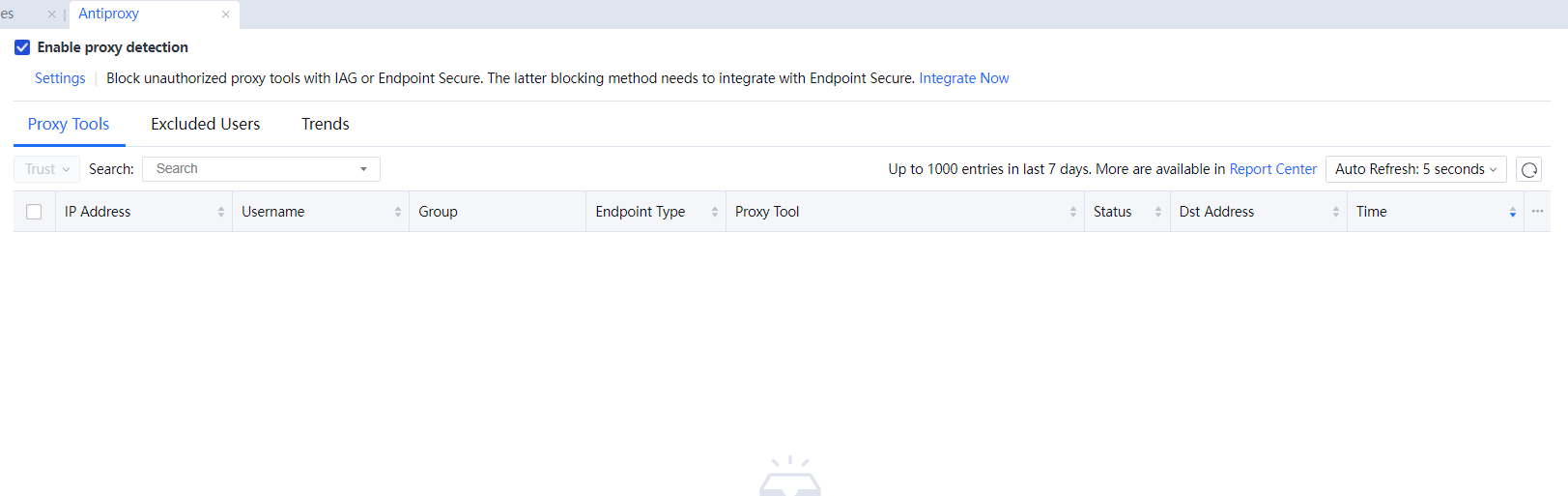
There are three tabs on the Anti-Proxy page: Proxy Tools, Excluded Users, and Trends.
The following information on the Proxy Tools tab: IP Address, Username, Group, Endpoint Device, Proxy Tool, Status and Time, etc., and up to 1000 entries in the last seven days can be displayed. You may log in to the report center for more entries by clicking on Report Center in the upper-right corner of that tab.
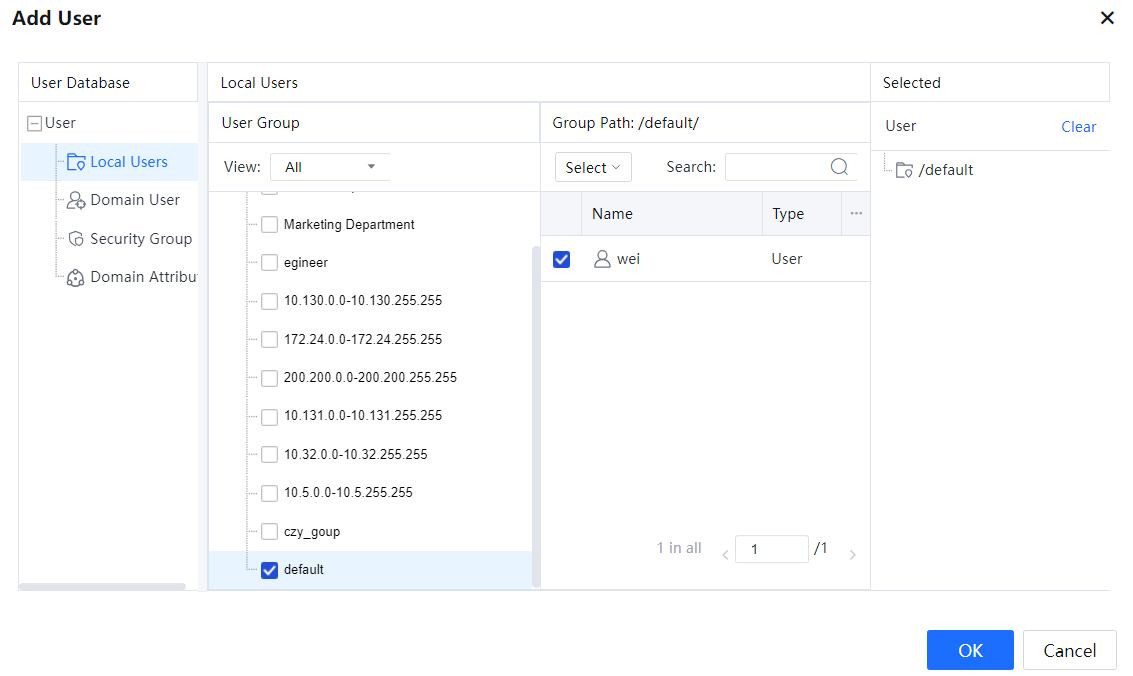
On the Excluded Users tab, you can add the user you want to use the proxy tool and specify the IP address to allow the use of the proxy tool on that address.
To select users or groups you want to exclude, click on Select user > group, as shown in the following figure. You can select local users, domain users, and security groups.
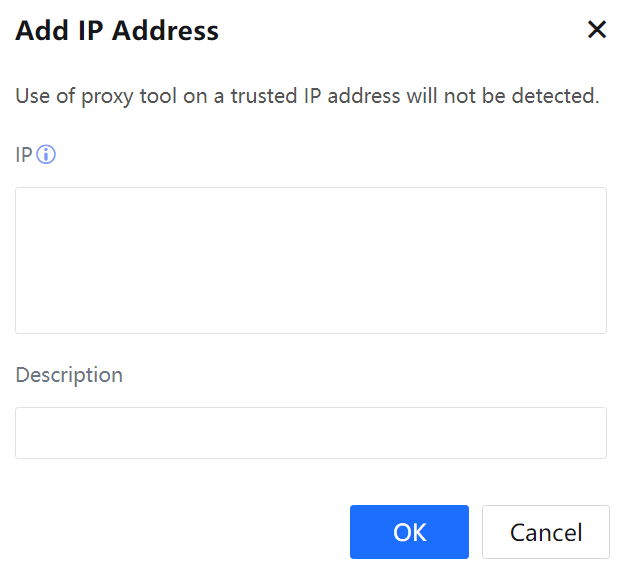
To add an IP address that you want to exclude, click Add in IP Addresses list and specify it on the following page:
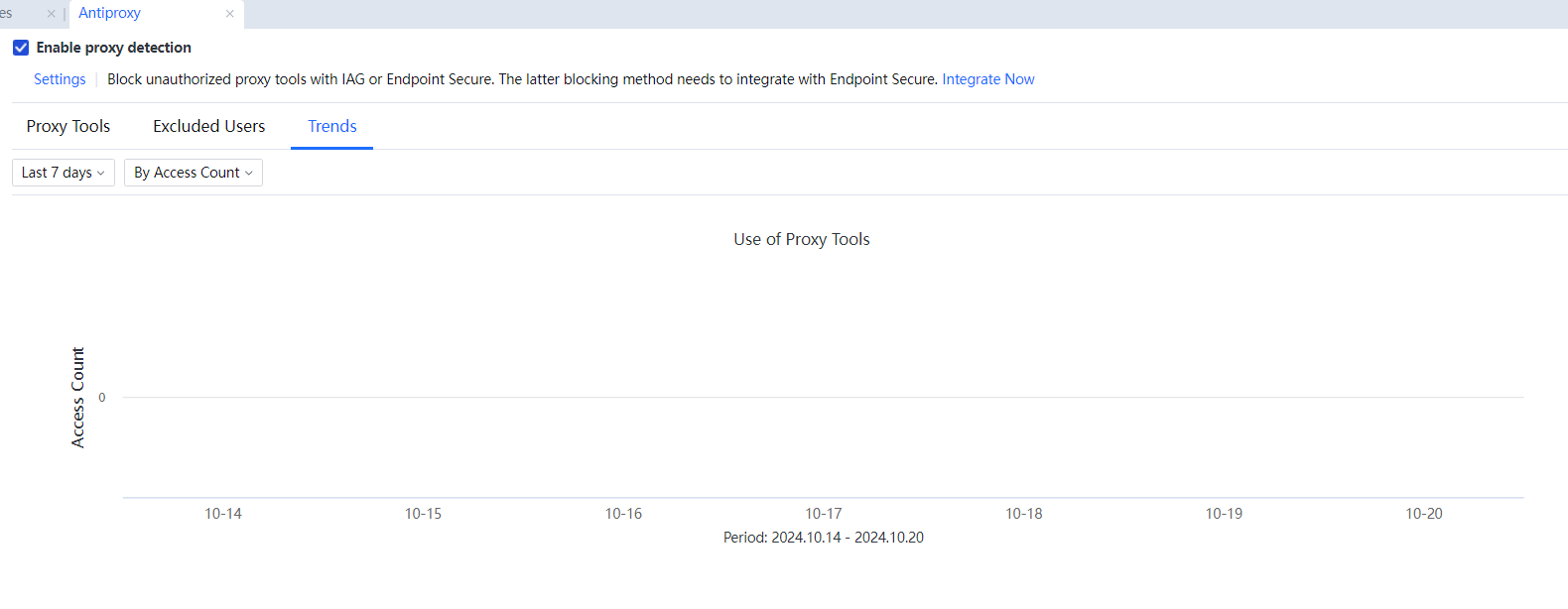
On the Trends tab, it displays the trend of the use of proxy tools over the last 7 or 30 days, as shown in the following figure.